Quote for the day:
“Leaders become great not because of their power, but because of their ability to empower others.” -- John C. Maxwell
🎧 Listen to this digest on YouTube Music
▶ Play Audio DigestDuration: 22 mins • Perfect for listening on the go.
API-First architecture: The backbone of modern enterprise innovation
 Pankaj Tripathi explains that API-first architecture has evolved from a
technical choice into a strategic leadership mandate essential for digital
survival and modern enterprise innovation. By prioritizing Application
Programming Interfaces as the core of strategic ecosystems, organizations can
achieve greater agility, seamless scaling, and faster time-to-market metrics.
This methodology effectively decouples front-end user experiences from
back-end logic, fostering a modular environment that allows for the
integration of sophisticated capabilities without the heavy burden of legacy
technical debt. In sectors like banking, travel, and retail, this approach
facilitates interoperability and unified digital experiences, as evidenced by
the massive success of India’s UPI and Open Government Data platforms.
Furthermore, API-first design is a critical prerequisite for deploying
advanced artificial intelligence at scale, as it eliminates data silos and
ensures that AI agents can consume the continuous flow of clean data required
for real-time insights. This architecture also supports operational
resilience, allowing individual microservices to scale independently during
demand surges without stressing the broader system. Transitioning to this
model requires a cultural shift toward managing product-centric digital
ecosystems that leverage third-party integrations as growth multipliers.
Ultimately, embracing an API-first framework provides the structural integrity
required to dismantle internal barriers and deliver the exceptional, connected
experiences that define modern market leadership in an increasingly complex
global economy.
Pankaj Tripathi explains that API-first architecture has evolved from a
technical choice into a strategic leadership mandate essential for digital
survival and modern enterprise innovation. By prioritizing Application
Programming Interfaces as the core of strategic ecosystems, organizations can
achieve greater agility, seamless scaling, and faster time-to-market metrics.
This methodology effectively decouples front-end user experiences from
back-end logic, fostering a modular environment that allows for the
integration of sophisticated capabilities without the heavy burden of legacy
technical debt. In sectors like banking, travel, and retail, this approach
facilitates interoperability and unified digital experiences, as evidenced by
the massive success of India’s UPI and Open Government Data platforms.
Furthermore, API-first design is a critical prerequisite for deploying
advanced artificial intelligence at scale, as it eliminates data silos and
ensures that AI agents can consume the continuous flow of clean data required
for real-time insights. This architecture also supports operational
resilience, allowing individual microservices to scale independently during
demand surges without stressing the broader system. Transitioning to this
model requires a cultural shift toward managing product-centric digital
ecosystems that leverage third-party integrations as growth multipliers.
Ultimately, embracing an API-first framework provides the structural integrity
required to dismantle internal barriers and deliver the exceptional, connected
experiences that define modern market leadership in an increasingly complex
global economy.5,000 vibe-coded apps just proved shadow AI is the new S3 bucket crisis
 The VentureBeat article details how "vibe coding"—the practice of using
natural language AI prompts to build applications—has sparked a significant
security crisis, drawing parallels to the notorious S3 bucket exposures of a
decade ago. Research by RedAccess and Escape.tech revealed that over 5,000
AI-generated applications are currently exposing sensitive corporate and
personal data, including medical records and financial details. This
vulnerability stems from popular platforms like Lovable and Replit having
public-by-default privacy settings, which allow search engines to index
internal tools created by non-technical "citizen developers" without proper
access controls. Gartner predicts that by 2028, these prompt-to-app approaches
will increase software defects by 2,500%, primarily through code that is
syntactically correct but contextually flawed. Shadow AI is identified as a
massive financial liability, with IBM reporting that breaches linked to
unsanctioned AI tools cost organizations an average of $4.63 million per
incident. To combat these risks, the article outlines a comprehensive
five-domain CISO audit framework focusing on discovery, authentication, code
scanning, data loss prevention, and governance. This strategy emphasizes
moving beyond mere gatekeeping to implementing automated inventorying and
strict identity management. CISOs are urged to adopt a structured remediation
plan to secure their AI environments, ensuring that rapid innovation does not
compromise fundamental security hygiene.
The VentureBeat article details how "vibe coding"—the practice of using
natural language AI prompts to build applications—has sparked a significant
security crisis, drawing parallels to the notorious S3 bucket exposures of a
decade ago. Research by RedAccess and Escape.tech revealed that over 5,000
AI-generated applications are currently exposing sensitive corporate and
personal data, including medical records and financial details. This
vulnerability stems from popular platforms like Lovable and Replit having
public-by-default privacy settings, which allow search engines to index
internal tools created by non-technical "citizen developers" without proper
access controls. Gartner predicts that by 2028, these prompt-to-app approaches
will increase software defects by 2,500%, primarily through code that is
syntactically correct but contextually flawed. Shadow AI is identified as a
massive financial liability, with IBM reporting that breaches linked to
unsanctioned AI tools cost organizations an average of $4.63 million per
incident. To combat these risks, the article outlines a comprehensive
five-domain CISO audit framework focusing on discovery, authentication, code
scanning, data loss prevention, and governance. This strategy emphasizes
moving beyond mere gatekeeping to implementing automated inventorying and
strict identity management. CISOs are urged to adopt a structured remediation
plan to secure their AI environments, ensuring that rapid innovation does not
compromise fundamental security hygiene.How Goldman Sachs, JPMorgan, AIG Are Actually Deploying AI
 The article details insights from leaders at Goldman Sachs, JPMorgan Chase,
and AIG regarding their strategic deployment of artificial intelligence,
particularly following Anthropic’s launch of specialized financial agents. At
an event in New York, Goldman Sachs CIO Marco Argenti outlined a three-wave
adoption strategy focusing on engineering productivity, operational redesign,
and enhanced risk decision-making. He notably described the shift as a
transition from purchasing infrastructure to "buying intelligence." JPMorgan
Chase CIO Lori Beer stressed that the primary hurdle is not the technology
itself but an organization’s capacity to absorb and integrate these tools
effectively. CEO Jamie Dimon highlighted Claude’s efficiency, noting it
completed accurate research tasks in twenty minutes that typically require
forty analyst hours. Meanwhile, AIG CEO Peter Zaffino revealed that AI
achieved eighty-eight percent accuracy in insurance claims processing,
emphasizing its role in supporting human expertise rather than replacing it.
The discussion coincided with Anthropic’s debut of ten pre-built agents
designed for high-value workflows like pitchbook creation and KYC screening.
Additionally, the article covers a one-point-five billion dollar joint venture
between Anthropic, Blackstone, and Goldman Sachs aimed at scaling AI for
mid-sized firms. Ultimately, these leaders view AI as a fundamental shift in
financial services, demanding both rigorous safety guardrails and profound
cultural transformation.
The article details insights from leaders at Goldman Sachs, JPMorgan Chase,
and AIG regarding their strategic deployment of artificial intelligence,
particularly following Anthropic’s launch of specialized financial agents. At
an event in New York, Goldman Sachs CIO Marco Argenti outlined a three-wave
adoption strategy focusing on engineering productivity, operational redesign,
and enhanced risk decision-making. He notably described the shift as a
transition from purchasing infrastructure to "buying intelligence." JPMorgan
Chase CIO Lori Beer stressed that the primary hurdle is not the technology
itself but an organization’s capacity to absorb and integrate these tools
effectively. CEO Jamie Dimon highlighted Claude’s efficiency, noting it
completed accurate research tasks in twenty minutes that typically require
forty analyst hours. Meanwhile, AIG CEO Peter Zaffino revealed that AI
achieved eighty-eight percent accuracy in insurance claims processing,
emphasizing its role in supporting human expertise rather than replacing it.
The discussion coincided with Anthropic’s debut of ten pre-built agents
designed for high-value workflows like pitchbook creation and KYC screening.
Additionally, the article covers a one-point-five billion dollar joint venture
between Anthropic, Blackstone, and Goldman Sachs aimed at scaling AI for
mid-sized firms. Ultimately, these leaders view AI as a fundamental shift in
financial services, demanding both rigorous safety guardrails and profound
cultural transformation.The agentic enterprise will be built on people, not just intelligence; here's how
 The shift toward the agentic enterprise signifies a transition where
artificial intelligence moves beyond generating insights to autonomous
execution and machine-led workflows. While this evolution sparks concerns
regarding employee relevance, the article emphasizes that the success of such
enterprises hinges more on human readiness than technological intelligence. As
AI assumes more execution-oriented tasks, uniquely human capabilities—such as
navigating ambiguity, exercising ethical judgment, and managing complex
relationships—become increasingly vital. India is positioned as a global
leader in this transition due to its high AI talent acquisition and literate
workforce. To thrive, organizations must prioritize building an agentic-ready
workforce by embedding transformation directly into technology adoption rather
than treating it as a separate initiative. This involves fostering a culture
of inquiry and psychological safety where experimentation is encouraged.
Training should focus on elevating judgment and discretion, particularly in
high-stakes areas like strategy and hiring. Ultimately, the most resilient
professionals will be those who develop versatile skills that transcend
specific tools, while the most successful companies will be those that empower
their people to lead alongside AI. By centering human intuition and
leadership, the agentic enterprise can effectively balance automated
efficiency with the critical oversight necessary for long-term organizational
trust and cultural integrity.
The shift toward the agentic enterprise signifies a transition where
artificial intelligence moves beyond generating insights to autonomous
execution and machine-led workflows. While this evolution sparks concerns
regarding employee relevance, the article emphasizes that the success of such
enterprises hinges more on human readiness than technological intelligence. As
AI assumes more execution-oriented tasks, uniquely human capabilities—such as
navigating ambiguity, exercising ethical judgment, and managing complex
relationships—become increasingly vital. India is positioned as a global
leader in this transition due to its high AI talent acquisition and literate
workforce. To thrive, organizations must prioritize building an agentic-ready
workforce by embedding transformation directly into technology adoption rather
than treating it as a separate initiative. This involves fostering a culture
of inquiry and psychological safety where experimentation is encouraged.
Training should focus on elevating judgment and discretion, particularly in
high-stakes areas like strategy and hiring. Ultimately, the most resilient
professionals will be those who develop versatile skills that transcend
specific tools, while the most successful companies will be those that empower
their people to lead alongside AI. By centering human intuition and
leadership, the agentic enterprise can effectively balance automated
efficiency with the critical oversight necessary for long-term organizational
trust and cultural integrity.AI on trial: The Workday case that CIOs can't ignore
 The article "AI on Trial: The Workday Case That CIOs Can’t Ignore" explores
the legal battle in Mobley v. Workday Inc., where over 14,000 job applicants
over age 40 allege that Workday’s AI-driven recruitment tools caused
systematic discrimination. The lawsuit challenges how antidiscrimination laws
apply to algorithms that score and rank candidates, placing the vendor’s
liability under intense scrutiny. Workday maintains that employers, not the
software provider, remain in control of hiring decisions and that their
technology focuses strictly on qualifications. However, the case highlights a
critical technical dispute over bias detection mathematics, specifically
comparing the “four-fifths rule” against standard-deviation analysis. This
conflict underscores why Chief Information Officers (CIOs) can no longer rely
solely on vendor-provided audits, which may suffer from “drift” or lack
independent criteria. The article advises CIOs to establish robust internal
oversight committees comprising technical, legal, and ethics experts to
independently validate AI outputs. As political environments shift and legal
risks surrounding "disparate impact" theories grow, the Workday case serves as
a landmark warning. Organizations must move beyond passive trust in AI
vendors, adopting proactive governance strategies to ensure their automated
hiring processes remain fair, transparent, and legally defensible in an
increasingly litigious landscape.
The article "AI on Trial: The Workday Case That CIOs Can’t Ignore" explores
the legal battle in Mobley v. Workday Inc., where over 14,000 job applicants
over age 40 allege that Workday’s AI-driven recruitment tools caused
systematic discrimination. The lawsuit challenges how antidiscrimination laws
apply to algorithms that score and rank candidates, placing the vendor’s
liability under intense scrutiny. Workday maintains that employers, not the
software provider, remain in control of hiring decisions and that their
technology focuses strictly on qualifications. However, the case highlights a
critical technical dispute over bias detection mathematics, specifically
comparing the “four-fifths rule” against standard-deviation analysis. This
conflict underscores why Chief Information Officers (CIOs) can no longer rely
solely on vendor-provided audits, which may suffer from “drift” or lack
independent criteria. The article advises CIOs to establish robust internal
oversight committees comprising technical, legal, and ethics experts to
independently validate AI outputs. As political environments shift and legal
risks surrounding "disparate impact" theories grow, the Workday case serves as
a landmark warning. Organizations must move beyond passive trust in AI
vendors, adopting proactive governance strategies to ensure their automated
hiring processes remain fair, transparent, and legally defensible in an
increasingly litigious landscape.The “Context Poisoning” Crisis: Why Metadata Is the New Security Perimeter
The article "The ‘Context Poisoning’ Crisis: Why Metadata Is the New Security
Perimeter" by Sriramprabhu Rajendran explores the emerging threat of context
poisoning within agentic AI and retrieval-augmented generation (RAG)
pipelines. Context poisoning occurs when AI agents utilize information that is
technically valid but semantically incorrect, often due to stale data vectors,
recursive hallucinations from agent-generated content, or amplified semantic
bias. Unlike traditional cybersecurity, which focuses on access controls and
encryption at the network perimeter, this crisis targets the metadata layer
where AI systems consume their grounding context. To mitigate these risks, the
author proposes a "metadata firebreak" rooted in zero-trust principles. This
architecture serves as a critical verification layer that validates every
piece of retrieved context before it enters the AI agent’s processing window.
The framework is built on four essential pillars: never trusting retrieved
chunks by default, continuously verifying data freshness against original
source timestamps, enforcing lineage tracking to prevent recursive feedback
loops, and applying semantic checksums to maintain truth. Ultimately, as AI
agents become integral to enterprise operations, the security focus must shift
from merely controlling access to ensuring data veracity. By establishing
metadata as the new security perimeter, organizations can ensure that
AI-driven decisions remain accurate, compliant, and trustworthy in a complex
digital environment.
Three skills that matter when AI handles the coding
 In the rapidly evolving landscape where artificial intelligence increasingly
manages the mechanical aspects of software development, the value of a
developer's expertise is shifting toward higher-level strategic functions.
This InfoWorld article argues that as large language models take over the
heavy lifting of code generation, three specific "upstream" skills are
becoming indispensable for modern engineers. First, developers must master the
art of providing precise context; this involves crystallizing complex
requirements, architectural designs, and functional constraints into detailed
prompts that guide the AI effectively. Second, the ability to critically
evaluate and verify model outputs remains crucial. Since AI can produce
confident yet incorrect solutions, developers need the technical depth to
review generated code against rigorous performance standards and existing
frameworks. Finally, deep problem understanding is essential to ensure that
the developer is not misled by plausible hallucinations or "confident but
wrong" answers. By focusing on these core competencies, teams can leverage AI
to accelerate iterative lifecycles, such as spiral development and
evolutionary prototyping, while maintaining absolute control over system
complexity. Ultimately, those who transition from manual coding to high-level
system design and rigorous evaluation will achieve significantly higher
productivity, while those failing to adapt risk being left behind in an
increasingly competitive AI-driven industry.
In the rapidly evolving landscape where artificial intelligence increasingly
manages the mechanical aspects of software development, the value of a
developer's expertise is shifting toward higher-level strategic functions.
This InfoWorld article argues that as large language models take over the
heavy lifting of code generation, three specific "upstream" skills are
becoming indispensable for modern engineers. First, developers must master the
art of providing precise context; this involves crystallizing complex
requirements, architectural designs, and functional constraints into detailed
prompts that guide the AI effectively. Second, the ability to critically
evaluate and verify model outputs remains crucial. Since AI can produce
confident yet incorrect solutions, developers need the technical depth to
review generated code against rigorous performance standards and existing
frameworks. Finally, deep problem understanding is essential to ensure that
the developer is not misled by plausible hallucinations or "confident but
wrong" answers. By focusing on these core competencies, teams can leverage AI
to accelerate iterative lifecycles, such as spiral development and
evolutionary prototyping, while maintaining absolute control over system
complexity. Ultimately, those who transition from manual coding to high-level
system design and rigorous evaluation will achieve significantly higher
productivity, while those failing to adapt risk being left behind in an
increasingly competitive AI-driven industry.Implementing the Sidecar Pattern in Microservices-based ASP.NET Core Applications
/articles/asp-net-core-side-car/en/smallimage/Implementing-the-Sidecar-Pattern-in-Microservices-based-ASP-NET-Core-Applications-thumb-1778079284259.jpg) In the article "Implementing the Sidecar Pattern in Microservices-based
ASP.NET Core Applications," author Joydip Kanjilal explores how the sidecar
design pattern effectively addresses cross-cutting concerns like logging,
monitoring, and security. By deploying these auxiliary tasks into a separate
container or process that runs alongside the primary application, developers
can decouple business logic from infrastructure requirements, thereby
significantly reducing complexity and enhancing overall maintainability. The
author provides a practical implementation walkthrough using an inventory
management system where a Transactions API offloads log persistence to a
shared file system. A dedicated Sidecar API then monitors this shared storage,
processes the incoming logs, and transmits them to Elasticsearch for analysis.
This architectural approach facilitates language-agnostic components and
allows for the independent scaling of auxiliary services without requiring
modifications to the core application code. However, the article highlights
significant trade-offs, such as increased resource overhead and potential
latency resulting from additional network hops, which may make it less
suitable for ultra-latency-sensitive workloads. Furthermore, Kanjilal
discusses modern alternatives like the Distributed Application Runtime (Dapr)
and potential enhancements through structured logging with Serilog or
observability via OpenTelemetry. Ultimately, the sidecar pattern emerges as a
robust solution for building modular and resilient microservices in the
ASP.NET Core ecosystem while keeping individual services lightweight.
In the article "Implementing the Sidecar Pattern in Microservices-based
ASP.NET Core Applications," author Joydip Kanjilal explores how the sidecar
design pattern effectively addresses cross-cutting concerns like logging,
monitoring, and security. By deploying these auxiliary tasks into a separate
container or process that runs alongside the primary application, developers
can decouple business logic from infrastructure requirements, thereby
significantly reducing complexity and enhancing overall maintainability. The
author provides a practical implementation walkthrough using an inventory
management system where a Transactions API offloads log persistence to a
shared file system. A dedicated Sidecar API then monitors this shared storage,
processes the incoming logs, and transmits them to Elasticsearch for analysis.
This architectural approach facilitates language-agnostic components and
allows for the independent scaling of auxiliary services without requiring
modifications to the core application code. However, the article highlights
significant trade-offs, such as increased resource overhead and potential
latency resulting from additional network hops, which may make it less
suitable for ultra-latency-sensitive workloads. Furthermore, Kanjilal
discusses modern alternatives like the Distributed Application Runtime (Dapr)
and potential enhancements through structured logging with Serilog or
observability via OpenTelemetry. Ultimately, the sidecar pattern emerges as a
robust solution for building modular and resilient microservices in the
ASP.NET Core ecosystem while keeping individual services lightweight.What is Quantum Machine Learning (QML)?
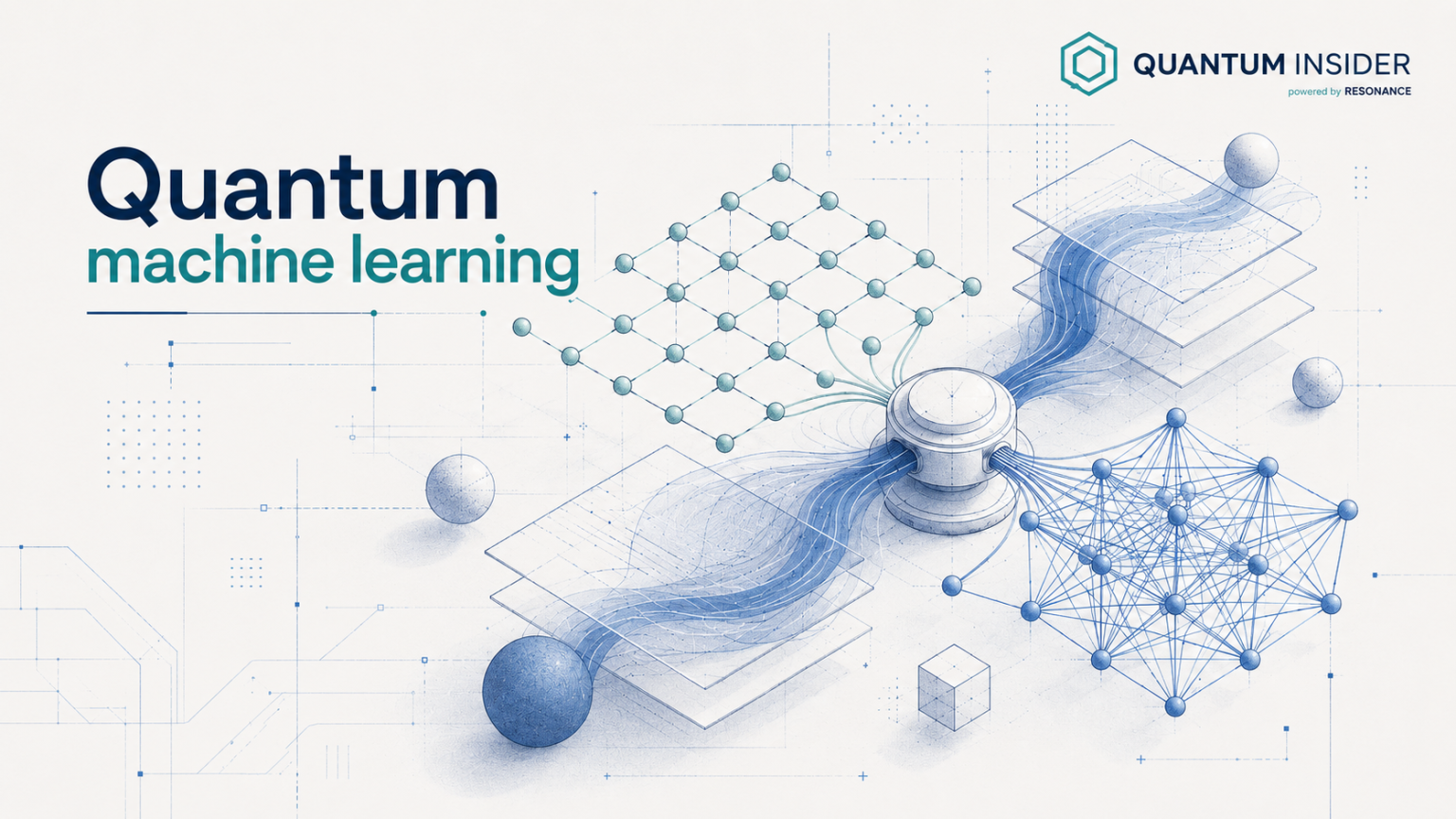 Quantum Machine Learning (QML) represents a transformative convergence of
quantum computing and artificial intelligence, leveraging quantum mechanical
phenomena to solve complex data-driven problems. The article explores how QML
utilizes qubits, which exist in superpositions of states, and entanglement to
achieve computational parallelism beyond the reach of classical bits. As of
May 2026, the field is firmly rooted in the "Noisy Intermediate-Scale Quantum"
(NISQ) era, where advanced hardware like IBM’s Nighthawk and Google’s Willow
processors facilitate hybrid workflows. In these systems, classical computers
handle data preprocessing and optimization while quantum circuits perform the
most computationally intensive subroutines, such as feature mapping in
high-dimensional spaces. This synergy is particularly potent for Variational
Quantum Algorithms (VQAs) and Quantum Neural Networks (QNNs), which are
currently being piloted for drug discovery, financial risk modeling, and
advanced materials science. Despite the promise of exponential speedups, the
article notes significant hurdles, including qubit decoherence, extreme
cooling requirements, and the necessity for more robust error correction.
Nevertheless, the transition from theoretical research to early commercial
pilots suggests that QML is poised to revolutionize industries by identifying
patterns and correlations that remain invisible to traditional machine
learning models, eventually paving the way for full-scale fault-tolerant
systems by the end of the decade.
Quantum Machine Learning (QML) represents a transformative convergence of
quantum computing and artificial intelligence, leveraging quantum mechanical
phenomena to solve complex data-driven problems. The article explores how QML
utilizes qubits, which exist in superpositions of states, and entanglement to
achieve computational parallelism beyond the reach of classical bits. As of
May 2026, the field is firmly rooted in the "Noisy Intermediate-Scale Quantum"
(NISQ) era, where advanced hardware like IBM’s Nighthawk and Google’s Willow
processors facilitate hybrid workflows. In these systems, classical computers
handle data preprocessing and optimization while quantum circuits perform the
most computationally intensive subroutines, such as feature mapping in
high-dimensional spaces. This synergy is particularly potent for Variational
Quantum Algorithms (VQAs) and Quantum Neural Networks (QNNs), which are
currently being piloted for drug discovery, financial risk modeling, and
advanced materials science. Despite the promise of exponential speedups, the
article notes significant hurdles, including qubit decoherence, extreme
cooling requirements, and the necessity for more robust error correction.
Nevertheless, the transition from theoretical research to early commercial
pilots suggests that QML is poised to revolutionize industries by identifying
patterns and correlations that remain invisible to traditional machine
learning models, eventually paving the way for full-scale fault-tolerant
systems by the end of the decade.











/articles/friction-fix/en/smallimage/friction-fix-thumbnail-1769156177973.jpg)