Driving digital transformation: The power of blockchain

While the BFSI sector is at the forefront of blockchain adoption, industries
like healthcare can also benefit from DLT. Tech Mahindra recently partnered
with StaTwig to manage the traceability of the global COVID-19 vaccine supply
through blockchain technology. In addition to improving transparency across
the supply chain, the VaccineLedger solution also helps prevent issues such as
expired vaccines being mistakenly distributed and used. With blockchain
technology, health institutions have complete traceability of the
vaccination’s journey from sourcing to the hospital floor. ... Sectors like
manufacturing are also finding value in blockchain technology. With
blockchain, manufacturers and suppliers can trace components and raw materials
through the entire remanufacturing process, ensuring that parts can be traced
back to a point of origin in case of a product recall or malfunction.
TradeLens, for example, a blockchain network for global shipments, has been
adopted by dozens of global carriers, customs authorities, freight forwarders,
and port authorities.

Meet Cadence: Workflow Engine for Taming Complex Processes

Cadence is an open source fault-oblivious stateful code platform and
workflow engine specifically designed to solve this development challenge.
Originally developed and open-sourced by Uber — and now adopted and
developed by an increasing number of companies including Uber and
Instaclustr — Cadence can abstract away the most difficult complexities
associated with developing high-scale distributed applications. Cadence
preserves the entire state of an application in durable virtual memory not
associated with any specific process. The stored application state includes
all call parameters and returned results for user-defined activities. It
then uses that information to catch up and replay workflows that get
interrupted. Cadence has libraries that enable developers to create and
coordinate workflows using popular languages such as Java, Go, Python and
Ruby. Cadence services, such as workers, are largely stateless and leverage
a data store for task/workflow persistence. Supported storage options
include open source Cassandra and MySQL/PostgreSQL, and an adapter is
available for any database featuring multi-row single shard
transactions.


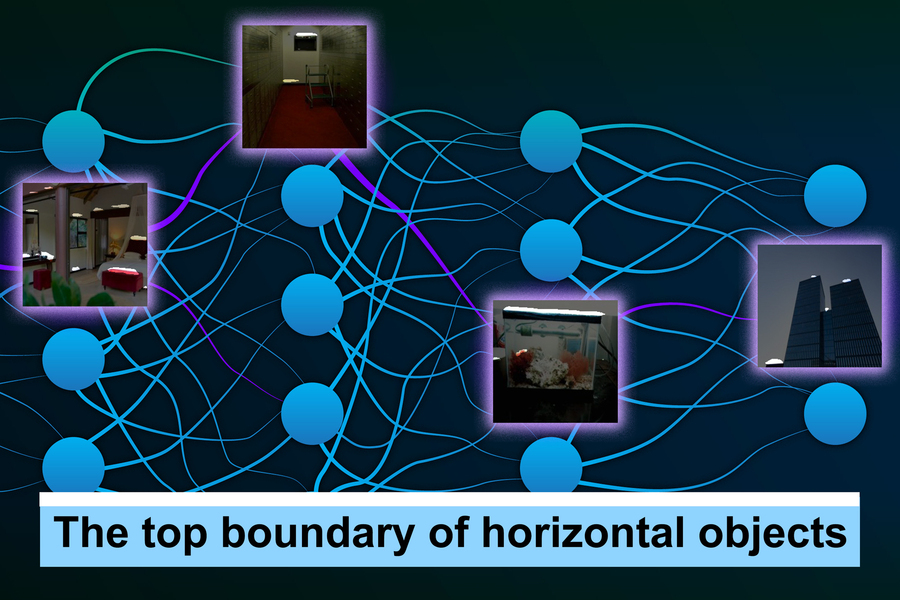
Extracting value from unstructured data with intelligent data management

The explosion of data is predicted to reach 175 zettabytes by 2025 and is
increasingly stored across disparate, hard-to-access, silos. Visibility in
the current ecosystem is poor. This growth of data has been fueled by
market forces that look to capitalise on the value that can be extracted
from the valuable resource. This is mirrored by the dramatic shift to the
cloud and edge. An estimated 90% of this data is unstructured information,
like text, video, audio, web server logs, social media and more. And, all
this data can’t be moved to a central data store or processed in its
entirety. Now, unstructured data management, for data-heavy organisations,
is an enterprise IT priority. They need to identify, index, tag and
monetise this information. Komprise, an intelligent data management
and mobility company, says it’s offering can solve this challenge: “We
dramatically save our customers money by tiering cold data to the cloud,
in a transparent, native AI/ML ready solution that doesn’t sit in front of
the hot data,” said Kumar Goswami, CEO and co-founder.
How to Create a Network Proxy Using Stream Processor Pipy
Every pipeline gets access to the same set of variables across a Pipy instance. In other words, contexts have the same shape. When you start a Pipy instance, the first thing you do is to define the shape of the context by defining variable(s) and their initial values. Every root pipeline clones the initial context you define at the start. When a sub-pipeline starts, it either shares or clones its parent’s context, depending on which joint filter you use. For instance, a link filter shares its parent’s context while a demux filter clones it. To the scripts embedded in a pipeline, these context variables are their global variables, which means that these variables are always accessible to scripts from anywhere as long as they live in the same script file. This might seem odd to a seasoned programmer because global variables usually mean they are globally unique. You have only one set of these variables, whereas in Pipy we can have many sets of them (aka contexts) depending on how many root pipelines are open for incoming network connections and how many sub-pipelines clone their parents’ contexts.More Security Flaws Found in Apple's OS Technologies

Apple said it has implemented an improved validation mechanism in macOS
Monterey 12.2 to address the issue. The company has credited two other
researchers — one from Trend Micro and another anonymous individual —
for reporting the flaw to the company. Meanwhile, one of the two
zero-day flaws (CVE-2022-22587) that Apple fixed this week involved
IOMobileFrameBuffer, a kernel extension related to a device's frame
buffer. The memory corruption bug allows attackers to run arbitrary code
at the kernel level and is likely being actively exploited in the wild
already, Apple said. The bug impacts macOS Monterey, iPhone 6 and later,
all iPad Pro models, and several other Apple mobile devices.
"CVE-2022-22587 targets the macOS kernel, and compromising it can give
the attacker root privileges," Levin says. "However, SIP comes into play
exactly for this kind of exploit." The flaw is one of several serious
vulnerabilities that researchers have uncovered in IOMobileFrameBuffer
recently. Other examples include CVE-2021-30883, a zero-day code
execution bug that Apple patched last October amid active exploit
activity, and CVE-2021-30807, which Apple fixed last July.


Why vulnerability scanners aren’t enough to prevent a ransomware attack on your business

Vulnerability scanners are needed in most security toolkits. However,
reactively detecting and alerting organizations to the presence of
vulnerabilities means companies cannot keep up. Vulnerability scanners
are akin to equipping security teams with an alarm system that’s
constantly flashing lights and sounding sirens everywhere – so many
alerts at once that it overwhelms security operations. Given the
significant transitions many organizations’ digital infrastructures
are undergoing, along with the complex and quickly evolving threat
landscape, a scan-and-patch approach reliant on vulnerability scanners
as a first line of defense is simply insufficient to protect
organizations from current and future threats. As such, relying on
vulnerability scanners is a dangerous strategy in the modern era, when
vulnerabilities are actively and regularly weaponized for successful
ransomware attacks. The dynamic shift in the threat landscape requires
an equally dynamic shift in how organizations approach their
cybersecurity programs.
Shipment-Delivery Scams Become the Favored Way to Spread Malware

Researchers attributed a couple of factors behind the ramp-up in
scams related to package delivery. Spoofing DHL certainly made sense
in the fourth quarter of last year during the busy holiday-shopping
season, noted Jeremey Fuchs, cybersecurity researcher and analyst
from Avanan, in a report on the latest DHL-related scam, published
Thursday. “Now, hackers are taking advantage of this, by attaching
malware to a DHL spoof,” which will likely attract attention from a
recipient in part because of its use of a trusted company, he wrote
in the report. Moreover, shipping delays and supply-chain issues
have become commonplace during the pandemic, which also has spurred
a massive increase in people working remotely from home. Attaching a
malicious invoice link to a fake USPS missed-delivery notification,
then – as threat actors did in the recently discovered Trickbot
campaign – would be an attractive lure for potential victims
accustomed to receiving these types of emails, according to Cofense.
“With the supply-chain delays, receiving a notification that a
delivery attempt was missed can lead to frustration and entice the
recipient to open the invoice link to further investigate,” Cofense
PDC researchers Andy Mann and Schyler Gallant wrote in the
report.

Do machines feel pain?

“Do machines feel pain?” is a very philosophical question, says
Anuj Gupta, Head of AI, Vahan. “Some robots react when hit. Does
it mean they ‘feel’ pain – no. Their reaction is a combination of
sensors and software. It is like a toy that reacts to one’s hand
gestures. Currently, machines can’t feel anything. They can be
programmed to trick humans by simulating human emotions, including
pain.” Few years ago, scientists from Nanyang Technological
University, Singapore, developed ‘mini-brains’ to help robots
recognise pain and activate self-repair. The approach embeds AI
into the sensor nodes, connected to multiple small, less-powerful
processing units that act like ‘mini-brains’ on the robotic skin.
Then, combining the system with self-healing ion gel material,
robots, when damaged, can recover their mechanical functions
without human intervention. Explaining the ‘mini-brains’,
co-author of the study, Associate Professor Arindam Basu, from the
School of Electrical & Electronic Engineering of the
university, says, “If robots have to work with humans, there is a
concern if they would interact safely. To ensure a safe
environment, scientists worldwide have been finding ways to bring
a sense of awareness to robots, including feeling pain, reacting
to it, and withstanding harsh operating conditions.

AI storage: a new requirement for the shift in computing and analytics

Traditionally, DDN Storage has focused on traditional data
storage for unstructured data and big data in enterprise,
government and academic sectors. Now, it is redefining the
imperatives that are driving it as a company, focusing on AI
storage, with its solution, AI, which is at the heart of its
growth strategy. In action, over the last two years DDN has
acted as the core backend storage system for NVIDIA to increase
performance & scale and flexibility to drive innovation.
NVIDIA commands “nearly 100%” of the market for training AI
algorithms and has multiple AI clusters, according to Karl
Freund, analyst at Cambrian AI Research. Following this success,
DDN is powering the UK’s most powerful supercomputer, Cambridge
1, which went live in 2021 and is focused on transforming
AI-based healthcare research. The AI storage vendor is also
working with Recursion, the drug discovery company. “Our
at-scale data needs require fast ingest, optimised processing
and reduced application run times,” said Kris Howard, Systems
Engineer at Recursion. Working with DDN, the drug discovery
company achieved up to 20x less costs and raised the
possibilities for accelerating the drug discovery pipeline with
new levels of AI capability.
Quote for the day:
"Leaders must see the dream in their mind before they will accomplish the dream with their team." -- Orrin Woodward
Chaos Engineering Has Evolved Since Netflix's Chaos Monkey Days
Chaos engineering or failure injection does not necessarily need to kill things or break services. Jason mentioned introducing latency and seeing how your application will behave. It's a normal situation when the database becomes slow because either there may be saturation of network because someone else all of a sudden starts using the same channel to your database. Or maybe it becomes slower because the indexes in this database are not optimized and things like that. When we develop a certain feature, we often think under the condition that everything will be, you know, nice and green and that it would be sunny with unicorns and things like that. However, simply looking at how your system will behave by increasing the latency between components already would be like a big eye-opener. This is especially true regarding how certain things are configured in your system or some of the requests you think need to be synchronous. And when you're testing this on a unit or integration test, you see the response time would be very quick.Quote for the day:
"Leaders must see the dream in their mind before they will accomplish the dream with their team." -- Orrin Woodward