Vetting an Open Source Database? 5 Green Flags to Look for

There’s an important difference between offerings that are legitimate open
source versus open source-compatible. “Captive” open source solutions pose as
the original open source solution from which they originated, but in reality,
they are merely branches of the original code. This can result in compromised
functionality or the inability to access features introduced in newer versions
of the true open source solution, as the branching occurred prior to the
introduction of those features. “Fake” open source can feature restrictive
licensing, a lack of source code availability and a non-transparent development
process. Despite this, these solutions are sometimes still marketed as open
source because, technically, the code is open to inspection and contributions
are possible. But when it comes down to it, the license is held by a single
company, so the degree of freedom is minute compared to that of actual open
source. The key is to minimize the gap between the core database and its open
source origins.
Zero trust and cloud capabilities essential for data management in enterprises
The challenge, however, lies in implementing a complete solution guided by the
seven pillars of Zero Trust. No company can do this alone. To help private and
public sector organizations simplify adoption, Dell is building a Zero Trust
ecosystem. It brings together more than thirty leading technology and security
companies to create a unified solution across infrastructure platforms,
applications, clouds, and services. PowerStore has always had a strong “security
DNA,” safeguarding data with advanced capabilities like hardware root of trust,
data-at-rest encryption and AIOps security analytics. As with everything about
the platform, the focus is simplicity and automation – delivering “always on”
protection without increasing management complexity or relying on human
vigilance to be effective. In 2023, the newest PowerStoreOS release adds even
more cybersecurity features to meet the stringent requirements, while also
enabling an authentic Zero Trust experience for business solutions.
Expecting Too Much From CISOs Can Drive Them Out The Door
“The CISO is there to raise the risk, to shine light on it, to offer solutions,
to differentiate and prioritize what needs to be fixed,” he explained. “You
can’t ask the CISO to do everything and everything; you need to give them the
support — and give them a team that can really make sure the cybersecurity and
risk management program is well-functioning.” Expecting too much from CISOs — as
so many company boards still do — continues to drive attrition from the security
function at a brisk pace, with burnout and the desire for greener pastures
pushing 24 percent of Fortune 500 CISOs to switch roles within a year of
starting. ... The increasing complexity of the modern cybersecurity defense has
dovetailed with the rapid expansion of managed service providers like eSentire,
whose ability to offer the full breadth of security capabilities — and to do so
confidently enough to offer guarantees like four-hour response times for remote
threat suppression — puts them well ahead of anything the average corporate
information security department can provide.
SRE Brings Modern Enterprise Architectures into Focus
If the business commitment is that users will reliably have enough light to
see what they are doing (service level), an SLO could be that one brightly lit
lamp (availability) is maintained for every 10 square feet of space. ... In
application delivery systems these could look like CPU utilization, API call
and database query time, etc. It’s up to the site reliability engineers to
define the SLI measures that impact the business SLOs and what responses will
be taken when they fall below specific thresholds by adjusting operating
policies and configuration. ... The measures, thresholds, and responses are
the intersection of SRE with the other domains of a modern enterprise
architecture designed for the application delivery of a digital business.
Operational data—telemetry—feeds the observability of the defined measures and
thresholds set by SRE. Automation is the combined application of tools,
technologies, and practices to enable site reliability engineers to scale
defined responses with less toil, thus enabling the efficient satisfaction of
the SLOs of a digital service.
What LOB leaders really think about IT: IDC study

For many IT leaders, turning that tide may require a new approach. CIOs can
demonstrate their value to the business and earn that seat at the table by
tying what they do to business goals, Thomson suggested. “One of the biggest
challenges that IT people have is being able to communicate their business
value in a language that the business understands,” she said. “Talking in
business outcomes is the currency that enables IT to gain trust and show the
value that they’re delivering.” In addition to mastering business concepts and
taking steps to prove the value of IT, CIOs who are succeeding at this are
putting in place seamless teams where there’s no wall between IT and the
business, she said. “It’s just seen as one cross-functional team where
everybody understands the common goal that is driving all the business
decisions.” Such strategic maneuvers are essential to becoming a digital
business, one where value creation is based on and dependent on the use of
digital technologies, from how processes are run to the products, services,
and experiences it provides, Thomson said.
Microsoft commits to supporting customers on their responsible AI journeys

The commitments include sharing Microsoft's expertise while teaching others to
develop AI safely, establishing a program to ensure AI applications are
created to follow legal regulations, and pledging to support the company's
customers in implementing Microsoft's AI systems responsibly within its
partner ecosystem. "Ultimately, we know that these commitments are only the
start, and we will have to build on them as both the technology and regulatory
conditions evolve," Cook wrote in the statement shared by Microsoft. Though
the company only recently developed its Bing Chat generative AI tool,
Microsoft will start by sharing key documents and methods that detail the
company's expertise and knowledge gained since beginning its journey into AI
years ago. The company will also share training curriculums and invest in
resources to teach others how to create a culture of responsible AI use within
organizations working with the technology. Microsoft will establish an "AI
Assurance Program" to leverage its own experiences and apply the financial
services concept called "Know your customer" to AI development.
Data Privacy Standard Contractual Clauses Called Into Question After Meta Ireland Fine

Although this decision deals a particularly large blow to Meta, all entities
relying upon SCCs to complete data transfers from the EU to the U.S. are now
affected. Due to the continued and wide-reaching effects of the U.S.’s
strategy on surveillance, we’ve now entered yet another period of uncertainty,
and the ability to lawfully transfer personal data into the U.S. from the EU
and United Kingdom is again in question. ... As a remedy, the DPC has given
Meta five months to suspend all transfers of personal data to the U.S., bring
its processing activities into compliance with EU law, and delete any EU
personal data that been transferred unlawfully under this decision. The EU has
long struggled with how to regulate EU personal data transfers to the U.S.
After the invalidation of the U.S.-EU Safe Harbor Agreement and the U.S.-EU
Privacy Shield in the Schrems I & Schrems II decisions, entities including
Meta have mostly relied on SCCs to lawfully transfer EU personal data into the
U.S. where U.S. laws are considered to provide substantially less protection.
5 Critical Data Governance Truths Every Data Leader Should Be Aware Of
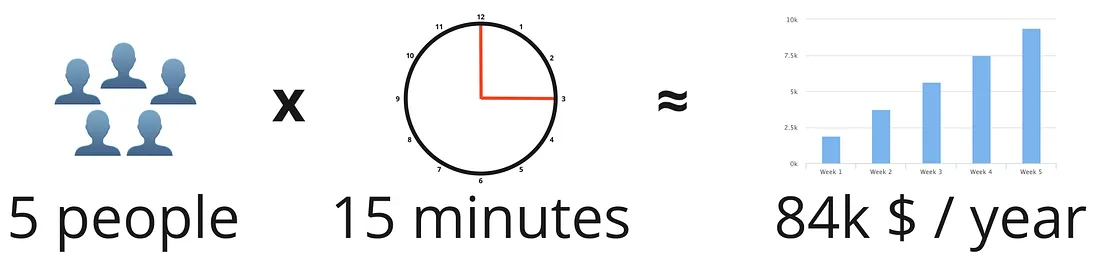
Implementing a comprehensive data governance program comes with a significant
price tag. As a result, firms can easily spend over US$1 million annually just
on resources to maintain data integrity. However, the risks associated with
poor data governance are many, for instance, reputational damage, lost
revenue, and more. Therefore, making decisions based on inaccurate data is
costly, leading to poor business outcomes. ... Data governance is
misunderstood to be solely about data. However, it's vital to understand data
governance is about components, each playing a crucial role in ensuring data
is managed effectively and efficiently. ... A good data governance program is
one with KPIs. The KPIs should be specific, measurable, and understandable by
everyone in the organization. By measuring these KPIs regularly and providing
timely feedback, managers can determine whether their efforts are paying off
or not. They can also communicate value metrics to key executives.
CDEI publishes portfolio of AI assurance techniques

The "portfolio of AI assurance techniques" was created to help anyone involved
in designing, developing, deploying or otherwise procuring AI systems do so in
a trustworthy way, by giving examples of real-world auditing and assurance
techniques. “AI assurance is about building confidence in AI systems by
measuring, evaluating and communicating whether an AI system meets relevant
criteria,” said the CDEI, adding these criteria could include regulations,
industry standards or ethical guidelines. “Assurance can also play an
important role in identifying and managing the potential risks associated with
AI. To assure AI systems effectively we need a range of assurance techniques
for assessing different types of AI systems, across a wide variety of
contexts, against a range of relevant criteria.” The portfolio specifically
contains case studies from multiple sectors and a range of technical,
procedural and educational approaches, to show how different techniques can
combine to promote responsible AI.
Consolidating your cyber security strategy
From a security perspective, consolidating threat defence into one system
means that all devices and endpoints can be set to one standard, minimising
the opportunity for weak spots and gaps to appear. In the event of a breach,
such as a member of staff clicking a malicious link, an XDR system can isolate
the threat to stop it spreading and roll-back the endpoint to a safe state.
Although changing cyber security tactics should not be viewed as a cost
cutting solution, vendor consolidation can certainly save money. By replacing
multiple products that may overlap, reducing the man hours spent monitoring
different systems and avoiding the consequences of a successful breach,
businesses can get a better return on their investment. Not all XDR systems
are the same, and it is important to choose one that best suits the needs of a
business. XDR has traditionally only been available for large enterprises.
However, finding the right partnership can allow small and medium sized
companies to customise the solution to fit their requirements without
unnecessary extras.
Quote for the day:
"Leadership does not always wear the
harness of compromise." -- Woodrow Wilson



































/filters:no_upscale()/articles/eda-mediator/en/resources/27figure-1-1685547198564.jpg)

