Quote for the day:
"If you automate chaos, you simply get faster chaos. Governance is the art of organizing the 'why' before the 'how'." — Adapted from Digital Transformation principles
🎧 Listen to this digest on YouTube Music
▶ Play Audio DigestDuration: 21 mins • Perfect for listening on the go.
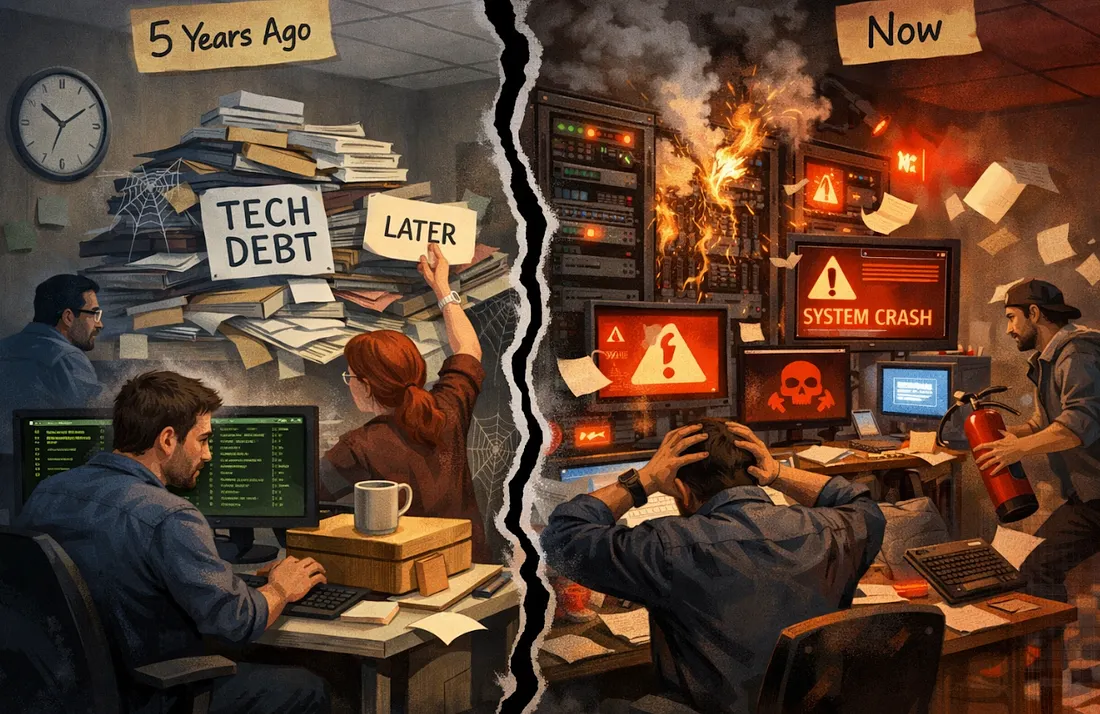
Why Culture Cracks During Digital Transformation
 Digital transformation is frequently heralded as a panacea for modern business
efficiency, yet Adrian Gostick argues that these initiatives often falter
because leaders prioritize technological implementation over cultural
integrity. When organizations undergo rapid digital shifts, the "cracks" in
culture emerge from a fundamental misalignment between new tools and the human
experience. Employees often face heightened anxiety regarding job security and
skill relevance, leading to a pervasive sense of uncertainty that stifles
productivity. Gostick emphasizes that the failure is rarely technical;
instead, it stems from a lack of transparent communication and psychological
safety. Leaders who focus solely on ROI and software integration neglect the
emotional toll of change, resulting in disengagement and burnout. To prevent
cultural collapse, management must actively bridge the gap by fostering an
environment of gratitude and clear purpose. This necessitates involving team
members in the transition process and ensuring that digital tools enhance,
rather than replace, human connection. Ultimately, the article posits that
culture acts as the essential operating system for any technological upgrade.
Without a resilient foundation of trust and recognition, even the most
sophisticated digital strategy is destined to fail, proving that people remain
the most critical component of successful corporate evolution.
Digital transformation is frequently heralded as a panacea for modern business
efficiency, yet Adrian Gostick argues that these initiatives often falter
because leaders prioritize technological implementation over cultural
integrity. When organizations undergo rapid digital shifts, the "cracks" in
culture emerge from a fundamental misalignment between new tools and the human
experience. Employees often face heightened anxiety regarding job security and
skill relevance, leading to a pervasive sense of uncertainty that stifles
productivity. Gostick emphasizes that the failure is rarely technical;
instead, it stems from a lack of transparent communication and psychological
safety. Leaders who focus solely on ROI and software integration neglect the
emotional toll of change, resulting in disengagement and burnout. To prevent
cultural collapse, management must actively bridge the gap by fostering an
environment of gratitude and clear purpose. This necessitates involving team
members in the transition process and ensuring that digital tools enhance,
rather than replace, human connection. Ultimately, the article posits that
culture acts as the essential operating system for any technological upgrade.
Without a resilient foundation of trust and recognition, even the most
sophisticated digital strategy is destined to fail, proving that people remain
the most critical component of successful corporate evolution.Most AI strategies will collapse without infrastructure discipline: Sesh Tirumala
In an interview with Express Computer, Sesh Tirumala, CIO of Western Digital,
warns that most enterprise AI strategies are destined for failure without
rigorous infrastructure discipline and alignment with business outcomes.
Rather than focusing solely on advanced models, Tirumala emphasizes that AI
readiness depends on a foundational architecture encompassing security,
resilience, full-stack observability, scalable compute platforms, and a
trusted data backbone. He argues that AI essentially acts as an amplifier;
therefore, applying it to a weak foundation only industrializes existing
inconsistencies. To achieve scalable value, organizations must shift from
fragmented experimentation to disciplined execution, ensuring that data is
connected and governed end-to-end. Beyond technical requirements, Tirumala
highlights that the true challenge lies in organizational readiness and change
management. Leaders must be willing to redesign workflows and invest in human
capital, as AI transformation is fundamentally a people-centric evolution
supported by technology. The evolving role of the CIO is thus to transition
from a technical manager to a transformation leader who integrates
intelligence into every business decision. Ultimately, infrastructure
discipline separates successful enterprise-scale deployments from those stuck
in perpetual pilot phases, making a robust foundation the most critical
determinant of whether AI delivers real, sustained value.
IoT Device Management: Provisioning, Monitoring and Lifecycle Control
 IoT Device Management serves as the critical operational backbone for
large-scale connected ecosystems, ensuring that devices remain secure,
functional, and efficient from initial deployment through decommissioning. As
projects scale from limited pilots to millions of endpoints, organizations
utilize these processes to centralize control over distributed assets,
bridging the gap between physical hardware and cloud services. The management
lifecycle encompasses four primary stages: secure provisioning to establish
device identity, continuous monitoring for telemetry and health diagnostics,
remote maintenance via over-the-air (OTA) updates, and responsible retirement.
These capabilities offer significant benefits, including enhanced security
through credential management, reduced operational costs via remote
troubleshooting, and accelerated innovation cycles. However, the field faces
substantial challenges, such as maintaining interoperability across
heterogeneous hardware, managing power-constrained battery devices, and
supporting hardware over extended lifespans often exceeding a decade. Looking
forward, the industry is evolving with the adoption of eSIM and iSIM
technologies for more flexible connectivity, alongside a shift toward
zero-trust security architectures and AI-driven predictive maintenance.
Ultimately, robust device management is indispensable for mitigating security
risks and ensuring the long-term reliability of IoT investments across diverse
sectors, including smart utilities, industrial manufacturing, and
mission-critical healthcare systems.
IoT Device Management serves as the critical operational backbone for
large-scale connected ecosystems, ensuring that devices remain secure,
functional, and efficient from initial deployment through decommissioning. As
projects scale from limited pilots to millions of endpoints, organizations
utilize these processes to centralize control over distributed assets,
bridging the gap between physical hardware and cloud services. The management
lifecycle encompasses four primary stages: secure provisioning to establish
device identity, continuous monitoring for telemetry and health diagnostics,
remote maintenance via over-the-air (OTA) updates, and responsible retirement.
These capabilities offer significant benefits, including enhanced security
through credential management, reduced operational costs via remote
troubleshooting, and accelerated innovation cycles. However, the field faces
substantial challenges, such as maintaining interoperability across
heterogeneous hardware, managing power-constrained battery devices, and
supporting hardware over extended lifespans often exceeding a decade. Looking
forward, the industry is evolving with the adoption of eSIM and iSIM
technologies for more flexible connectivity, alongside a shift toward
zero-trust security architectures and AI-driven predictive maintenance.
Ultimately, robust device management is indispensable for mitigating security
risks and ensuring the long-term reliability of IoT investments across diverse
sectors, including smart utilities, industrial manufacturing, and
mission-critical healthcare systems.Enterprises demand cloud value
 According to David Linthicum’s analysis of the Flexera 2026 State of the Cloud
Report, enterprise cloud strategies are undergoing a fundamental shift from
simple cost-cutting toward a focus on measurable business value and ROI. After
years of grappling with unpredictable billing and wasted resources—estimated
at 29% of current spending—organizations are maturing by establishing Cloud
Centers of Excellence (CCOEs) and dedicated FinOps teams to ensure centralized
accountability. This trend is further accelerated by the rapid adoption of
generative AI, which has seen extensive usage grow to 45% of organizations.
While AI offers immense opportunities for innovation, it introduces complex,
usage-based pricing models that demand early and rigorous governance to
prevent financial sprawl. To maximize cloud investments, the article
recommends doubling down on centralized governance, integrating AI oversight
into existing frameworks, and treating FinOps as a continuous operational
discipline rather than a one-time project. Ultimately, the industry is moving
past the chaotic early days of cloud adoption into an era where every dollar
spent must demonstrate a tangible return. By aligning technical innovation
with strategic business goals, mature enterprises are finally extracting the
true value that cloud and AI technologies originally promised, turning
potential liabilities into competitive advantages.
According to David Linthicum’s analysis of the Flexera 2026 State of the Cloud
Report, enterprise cloud strategies are undergoing a fundamental shift from
simple cost-cutting toward a focus on measurable business value and ROI. After
years of grappling with unpredictable billing and wasted resources—estimated
at 29% of current spending—organizations are maturing by establishing Cloud
Centers of Excellence (CCOEs) and dedicated FinOps teams to ensure centralized
accountability. This trend is further accelerated by the rapid adoption of
generative AI, which has seen extensive usage grow to 45% of organizations.
While AI offers immense opportunities for innovation, it introduces complex,
usage-based pricing models that demand early and rigorous governance to
prevent financial sprawl. To maximize cloud investments, the article
recommends doubling down on centralized governance, integrating AI oversight
into existing frameworks, and treating FinOps as a continuous operational
discipline rather than a one-time project. Ultimately, the industry is moving
past the chaotic early days of cloud adoption into an era where every dollar
spent must demonstrate a tangible return. By aligning technical innovation
with strategic business goals, mature enterprises are finally extracting the
true value that cloud and AI technologies originally promised, turning
potential liabilities into competitive advantages.The external pressures redefining cybersecurity risk
 In his analysis of the evolving threat landscape, John Bruggeman identifies
three external pressures fundamentally redefining modern cybersecurity risk:
geopolitical instability, the rapid advancement of artificial intelligence,
and systemic third-party vulnerabilities. Geopolitical tensions are no longer
localized; instead, battle-tested techniques from conflict zones frequently
spill over into global networks, particularly endangering operational
technology (OT) and critical infrastructure. Simultaneously, AI has triggered
a high-stakes arms race, lowering entry barriers for attackers while expanding
organizational attack surfaces through internal tool adoption and potential
data leakage. Finally, the concept of "cyber inequity" highlights that an
organization’s security is often only as robust as its weakest vendor, with
over 35% of breaches originating within partner networks. To navigate these
challenges, Bruggeman advocates for elevating OT security to board-level
oversight and establishing dedicated AI Risk Councils to govern internal
innovation. Rather than aiming for absolute prevention, successful leaders
must prioritize resilience and proactive incident response planning, operating
under the assumption that external partners will eventually be compromised. By
integrating these strategies, organizations can better withstand pressures
that originate far beyond their immediate control, shifting from a reactive
posture to one of coordinated defense and long-term business continuity.
In his analysis of the evolving threat landscape, John Bruggeman identifies
three external pressures fundamentally redefining modern cybersecurity risk:
geopolitical instability, the rapid advancement of artificial intelligence,
and systemic third-party vulnerabilities. Geopolitical tensions are no longer
localized; instead, battle-tested techniques from conflict zones frequently
spill over into global networks, particularly endangering operational
technology (OT) and critical infrastructure. Simultaneously, AI has triggered
a high-stakes arms race, lowering entry barriers for attackers while expanding
organizational attack surfaces through internal tool adoption and potential
data leakage. Finally, the concept of "cyber inequity" highlights that an
organization’s security is often only as robust as its weakest vendor, with
over 35% of breaches originating within partner networks. To navigate these
challenges, Bruggeman advocates for elevating OT security to board-level
oversight and establishing dedicated AI Risk Councils to govern internal
innovation. Rather than aiming for absolute prevention, successful leaders
must prioritize resilience and proactive incident response planning, operating
under the assumption that external partners will eventually be compromised. By
integrating these strategies, organizations can better withstand pressures
that originate far beyond their immediate control, shifting from a reactive
posture to one of coordinated defense and long-term business continuity.
Failure As a Means to Build Resilient Software Systems: A Conversation with Lorin Hochstein
In this InfoQ podcast, host Michael Stiefel interviews reliability expert Lorin Hochstein to explore how software failures serve as critical learning tools for architects. Hochstein distinguishes between "robustness," which targets anticipated failure patterns, and "resilience," the ability of a system to adapt to "unknown unknowns." A central theme is "Lorin’s Law," which posits that as systems become more reliable, they inevitably grow more complex, often leading to failure modes triggered by the very mechanisms intended to protect them. Hochstein argues that synthetic testing tools like Chaos Monkey are useful but cannot replicate the unpredictable confluence of events found in real-world outages. He emphasizes a "no-blame" culture, asserting that operators are rational actors who make the best possible decisions with available information. Therefore, humans are not the "weak link" but the primary source of resilience, constantly adjusting to maintain stability in evolving socio-technical systems. The discussion highlights that because software is never truly static, architects must embrace storytelling and incident reviews to understand the "drift" between original design assumptions and current operational realities. Ultimately, building resilient systems requires moving beyond binary uptime metrics to cultivate an organizational capacity for handling the inevitable surprises of modern, complex computing environments.How AI has suddenly become much more useful to open-source developers
 The ZDNET article "Maybe open source needs AI" explores the growing necessity
of artificial intelligence in managing the vast landscape of open-source
software. With millions of critical projects relying on a single maintainer,
the ecosystem faces significant risks from burnout or loss of leadership.
Fortunately, AI coding tools have evolved from producing unreliable "slop" to
generating high-quality security reports and sophisticated code improvements.
Industry leaders, including Linux kernel maintainer Greg Kroah-Hartman,
highlight a recent shift where AI-generated contributions have become
genuinely useful for triaging vulnerabilities and modernizing legacy
codebases. However, this transition is not without friction. Legal
complexities regarding copyright and derivative works are emerging,
exemplified by disputes over AI-driven library rewrites. Furthermore,
maintainers are often overwhelmed by a flood of low-quality, AI-generated pull
requests that can paradoxically increase their workload or even force projects
to shut down. Despite these hurdles, organizations like the Linux Foundation
are deploying AI resources to assist overworked developers. The article
concludes that while AI offers a potential lifeline for neglected projects and
a productivity boost for experts, careful implementation and oversight are
essential to navigate the legal and technical challenges inherent in this new
era of software development.
The ZDNET article "Maybe open source needs AI" explores the growing necessity
of artificial intelligence in managing the vast landscape of open-source
software. With millions of critical projects relying on a single maintainer,
the ecosystem faces significant risks from burnout or loss of leadership.
Fortunately, AI coding tools have evolved from producing unreliable "slop" to
generating high-quality security reports and sophisticated code improvements.
Industry leaders, including Linux kernel maintainer Greg Kroah-Hartman,
highlight a recent shift where AI-generated contributions have become
genuinely useful for triaging vulnerabilities and modernizing legacy
codebases. However, this transition is not without friction. Legal
complexities regarding copyright and derivative works are emerging,
exemplified by disputes over AI-driven library rewrites. Furthermore,
maintainers are often overwhelmed by a flood of low-quality, AI-generated pull
requests that can paradoxically increase their workload or even force projects
to shut down. Despite these hurdles, organizations like the Linux Foundation
are deploying AI resources to assist overworked developers. The article
concludes that while AI offers a potential lifeline for neglected projects and
a productivity boost for experts, careful implementation and oversight are
essential to navigate the legal and technical challenges inherent in this new
era of software development.
Axios NPM Package Compromised in Precision Attack
 The Axios npm package, a cornerstone of the JavaScript ecosystem with over 400
million monthly downloads, recently fell victim to a highly sophisticated
"precision attack" that underscores the evolving threats to the software
supply chain. Security researchers identified malicious versions—specifically
1.14.1 and 0.30.4—which were published following the compromise of a lead
maintainer’s account. These versions introduced a malicious dependency called
"plain-crypto-js," which stealthily installed a cross-platform remote-access
Trojan (RAT) capable of targeting Windows, Linux, and macOS environments.
Attributed by Google to the North Korean threat actor UNC1069, the campaign
exhibited remarkable operational tradecraft, including pre-staged dependencies
and advanced anti-forensic techniques where the malware deleted itself and
restored original configuration files to evade detection. Unlike typical
broad-spectrum attacks, this incident focused on machine profiling and
environment fingerprinting, suggesting a strategic goal of initial access
brokerage or targeted espionage. Although the malicious versions were active
for only a few hours before being removed by NPM, the breach highlights a
significant escalation in supply chain exploitation, marking the first time a
top-ten npm package has been successfully compromised by North Korean actors.
Organizations are urged to verify dependencies immediately as the silent,
traceless nature of the infection poses a fundamental risk to developer
environments.
The Axios npm package, a cornerstone of the JavaScript ecosystem with over 400
million monthly downloads, recently fell victim to a highly sophisticated
"precision attack" that underscores the evolving threats to the software
supply chain. Security researchers identified malicious versions—specifically
1.14.1 and 0.30.4—which were published following the compromise of a lead
maintainer’s account. These versions introduced a malicious dependency called
"plain-crypto-js," which stealthily installed a cross-platform remote-access
Trojan (RAT) capable of targeting Windows, Linux, and macOS environments.
Attributed by Google to the North Korean threat actor UNC1069, the campaign
exhibited remarkable operational tradecraft, including pre-staged dependencies
and advanced anti-forensic techniques where the malware deleted itself and
restored original configuration files to evade detection. Unlike typical
broad-spectrum attacks, this incident focused on machine profiling and
environment fingerprinting, suggesting a strategic goal of initial access
brokerage or targeted espionage. Although the malicious versions were active
for only a few hours before being removed by NPM, the breach highlights a
significant escalation in supply chain exploitation, marking the first time a
top-ten npm package has been successfully compromised by North Korean actors.
Organizations are urged to verify dependencies immediately as the silent,
traceless nature of the infection poses a fundamental risk to developer
environments.Financial groups lay out a plan to fight AI identity attacks
 The rapid advancement of generative AI has significantly lowered the cost of
creating deepfakes, leading to a dramatic surge in sophisticated identity
fraud targeting financial institutions. A joint report from the American
Bankers Association, the Better Identity Coalition, and the Financial Services
Sector Coordinating Council highlights that deepfake incidents in the fintech
sector rose by 700% in 2023, with projected annual losses reaching $40 billion
by 2027. To combat these AI-driven threats, the groups have proposed a
comprehensive plan focused on four primary initiatives. First, they advocate
for improved identity verification through the adoption of mobile driver's
licenses and expanding access to government databases like the Social Security
Administration's eCBSV system. Second, the report urges a shift toward
phishing-resistant authentication methods, such as FIDO security keys and
passkeys, to replace vulnerable legacy systems. Third, it emphasizes the
necessity of international cooperation to establish unified standards for
digital identity and wallet interoperability. Finally, the plan calls for
robust public education campaigns to raise awareness about deepfake risks and
modern security tools. By modernizing identity infrastructure and fostering
collaboration between government and industry, policymakers can better protect
the national economy from the escalating dangers posed by automated AI
exploitation.
The rapid advancement of generative AI has significantly lowered the cost of
creating deepfakes, leading to a dramatic surge in sophisticated identity
fraud targeting financial institutions. A joint report from the American
Bankers Association, the Better Identity Coalition, and the Financial Services
Sector Coordinating Council highlights that deepfake incidents in the fintech
sector rose by 700% in 2023, with projected annual losses reaching $40 billion
by 2027. To combat these AI-driven threats, the groups have proposed a
comprehensive plan focused on four primary initiatives. First, they advocate
for improved identity verification through the adoption of mobile driver's
licenses and expanding access to government databases like the Social Security
Administration's eCBSV system. Second, the report urges a shift toward
phishing-resistant authentication methods, such as FIDO security keys and
passkeys, to replace vulnerable legacy systems. Third, it emphasizes the
necessity of international cooperation to establish unified standards for
digital identity and wallet interoperability. Finally, the plan calls for
robust public education campaigns to raise awareness about deepfake risks and
modern security tools. By modernizing identity infrastructure and fostering
collaboration between government and industry, policymakers can better protect
the national economy from the escalating dangers posed by automated AI
exploitation.
/dq/media/media_files/2026/02/25/is-ai-killing-sustainability-2026-02-25-16-14-35.jpg)