How Is AI Helping To Commercialize Space?

The power of deep learning and AI-enabled recognition provides significant power in analyzing images and providing ability to review the millions of images produced by spacecraft. Artificial intelligence on the other end can analyze the images as they are being taken and determine if there are any issues with the images. Unlike humans, AI does not need to sleep or take breaks so it can rapidly process a lot of data. Using AI to capture images of Earth also prevents the need for large amounts of communication to and from Earth to analyze photos and determine whether a new photo needs to be taken. By cutting back on communication, the AI is saving processing power, reducing battery usage, and speeding up the image gathering process. Satellites are also being used to analyze natural disasters from space. Detailed imagery from a satellite can help those on the ground to see victims, determine the course of the disaster, and more. Artificial intelligence is being used to help speed up the response of satellites to natural disasters. With the help of the onboard AI, satellites are able to determine where a natural disaster is located and navigate to that location.
COVID-19: How to Adjust Business Continuity Plans
The COVID-19 pandemic present new challenges to healthcare IT and security teams, including the need to reassess and adjust business continuity plans, says Christopher Frenz, who leads information security at New York's Interfaith Medical Center. He's chair of an industry committee that has developed new guidance for dealing with those challenges. ... "Business continuity is something organizations should constantly test, particularly in healthcare," he says in an interview with Information Security Media Group. "Testing your backup and disaster recovery plans is something we should always be doing. But at a time like this where we're seeing an upswing in malware attacks against hospitals related to coronavirus, and you're going to have influxes of patients ... that puts additional stresses on systems. So it's definitely a good idea to test and verify that all this stuff works ahead of time," he says.
Once hailed as unhackable, blockchains are now getting hacked
Susceptibility to 51% attacks is inherent to most cryptocurrencies. That’s because most are based on blockchains that use proof of work as their protocol for verifying transactions. In this process, also known as mining, nodes spend vast amounts of computing power to prove themselves trustworthy enough to add information about new transactions to the database. A miner who somehow gains control of a majority of the network's mining power can defraud other users by sending them payments and then creating an alternative version of the blockchain in which the payments never happened. This new version is called a fork. The attacker, who controls most of the mining power, can make the fork the authoritative version of the chain and proceed to spend the same cryptocurrency again. For popular blockchains, attempting this sort of heist is likely to be extremely expensive. According to the website Crypto51, renting enough mining power to attack Bitcoin would currently cost more than $260,000 per hour. But it gets much cheaper quickly as you move down the list of the more than 1,500 cryptocurrencies out there.
Cyber crooks continue to exploit COVID-19 for their malicious schemes
“BEC attacks are often delivered in stages. The first email sent is typically innocuous, meaning that they do not contain the attacker’s end goal. The attackers craft plausible scenarios in hopes the recipient will reply. Once they’re on the hook, the attacker will send their true ask. (I need you to buy gift cards, wire transfer funds, etc.),” the researchers explained. “These coronavirus-themed BEC attacks often come with spoofed display names, which are likely real people known to the recipient. In the body of this message, the actor attempts to eliminate the possibility of voice-verification, in hopes of ensuring a higher success rate, by saying their phone is ‘faulty at the moment.'” They’ve also spotted an assortment of fake notices impersonating doctors and local health agencies and institutions (aimed at the general population), as well as more targeted emails aimed at enterprises (employees), such as fake internal emails for credential phishing attacks impersonating the organization’s president, IT staff, risk manager, and so on.
CIOs say personal disruption comes before digital disruption

CIOs suggest personal disruption should be part and parcel to the overall disruptions that their organizations are making. At the same time, they say transformation needs to happen at many levels these days including the personal level. With this said, if an organization has been comfortable with the status quo for too time, CIOs say they need to start by driving the organizational change needed to be receptive to change and to perceive changes the organization needs. A key part of this, CIOs say is that IT leaders should resolve to be open to new ideas and ways of thinking this year and in the coming decade. Part of this involves getting out of the natural comfort zone and being open to thinking differently about how to impact the organization. CIOs suggest in 2020 IT leaders need to have increased awareness of the social and cultural impacts occurring from technology. CIOs say, for this reason, it makes sense to encourage the entire team to self-disrupt itself. To fix businesses, CIOs should get the business out of its comfort zone too.
4 Reasons Central Banks Should Launch Retail Digital Currencies
While domestic retail payments in many OECD countries are now free, cross border payments remain a minefield of pain, cost and delays for consumers. If I send money to my mum in India, she has no digital identity in the UK and I have no digital identity in India. So my bank in the UK verifies that I sent the money, my mum’s bank verifies that she’s the person the money is for and both the banks verify (or at least hope) that neither I nor my mum is a nefarious character. Then the banks wait until they have compared their respective spreadsheets and make me wait for this reconciliation. Only after that, both the banks take a nice cut on the FX and send the rest to my mum. If the bank was in rural Ghana instead of Delhi, there’d probably be two more banks in this bank-chain, which’d quadruple the delay and the pain. This whole process of cross border payments is not only a pain for consumers, it also makes the global AML regime ineffective and unenforceable. Instead, if the Bank of England and the Reserve Bank of India both were to rely on a shared set of data standards for their respective digital currencies and for the corresponding digital identity infrastructure
Exploring the risky behavior of IT security professionals

Almost 65% of the nearly 300 international cybersecurity professionals canvased by Gurucul at RSA Conference 2020 said they access documents that have nothing to do with their jobs. Meanwhile, nearly 40% of respondents who experienced bad performance reviews also admitted to abusing their privileged access, which is double the overall rate (19%). “We knew insider privilege abuse was rampant in most enterprises, but these survey results demonstrate that the infosecurity department is not immune to this practice,” said Saryu Nayyar, CEO of Gurucul. “Detecting impermissible access to resources by authorized users, whether it is malicious or not, is virtually impossible with traditional monitoring tools. That’s why many organizations are turning to security and risk analytics that look at both employee and entity behaviors to identify anomalies indicative of insider threats.” ... This showcases the problems organizations have with employees behaving outside of the bounds of practical and published security policies.
Covid-19: NHS tackles coronavirus crisis with the help of tech
NHS Digital’s website states: “Patients should be enabled to get advice and care without attending the practice unless in-person care is clinically required.” But although phone appointments are great, they won’t cover everything. This is where video appointments are invaluable – not just for patients who may be displaying coronavirus symptoms, but for anyone who needs to be seen by a GP. Some GPs already have online systems and video consultations in place, but many of those who have the service available have not yet begun to use it. EMIS is one of the biggest GP IT system providers in England, with nearly 4,000 GP practices using its EMIS Web service. In 2017, it launched its Video Consult service, but uptake has been limited. This echoes throughout GP practices in the UK – suppliers often offer the service, but few GP practices use it. EMIS, which normally charges GPs for the use of video consultations, has now decided to offer it free for the next few months.
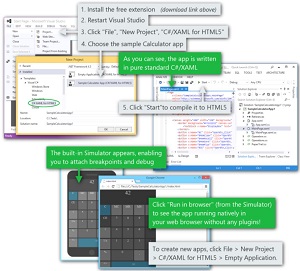
To succeed in DevOps these days, go hybrid

DevOps is not just a technical undertaking, it's a business proposition. This calls for hybrid skills that enable a more holistic view of the entire software development and deployment process. With a majority of enterprises (52%) intending to ramp up their recruiting of DevOps skills. close to two-thirds, 65%, reported having difficulties with finding these combinations of skills. DevOps is not just a technical undertaking, it's a business proposition. This calls for hybrid skills that enable a more holistic view of the entire software development and deployment process. With a majority of enterprises (52%) intending to ramp up their recruiting of DevOps skills. close to two-thirds, 65%, reported having difficulties with finding these combinations of skills. The DevOps journey is still very difficult for more than 50% of respondents. "DevOps is a fundamental change in the traditional structure of IT. It not only represents the adoption of new technology, but also an organizational transformation challenge with all that it implies with the 'evangelization of the existing responsibility silos.
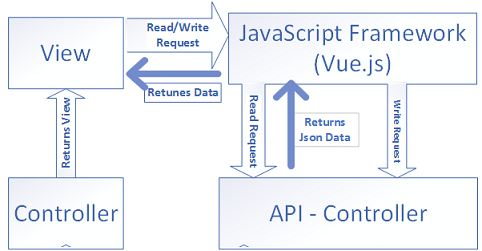
The Anatomy of a Microservice, One Service, Multiple Servers
In addition to supporting multiple transport mechanisms that can improve performance and efficiency, when providing more than one API Server, there’s an architectural benefit. That is helping to enforce separation of concerns. While the high-level architecture diagram presented in Microservice Definition and Architecture depicts a clear separation of concerns, like any other development effort, implementing this pattern does require diligence. In a previous article in this series, I stated that I believe developers have the best intentions in mind. Of course, there are exceptions, but individuals do want to do a good job. The problem comes in when deadlines loom. Things start to get thrown off the back of the truck. Shortcuts are taken. Non-functional requirements such as metrics gathering and reporting are missed. The more an architecture helps guide a team, the less likely these things will happen. Specifically, in the case of having two API Servers, business logic remains where it’s supposed to remain: in the business service.
Quote for the day:
"Leadership is the other side of the coin of loneliness, and he who is a leader must always act alone. And acting alone, accept everything alone." -- Ferdinand Marcos