What is tokenization?

Tokenization is the process of issuing a digital representation of an asset on a
(typically private) blockchain. These assets can include physical assets like
real estate or art, financial assets like equities or bonds, nontangible assets
like intellectual property, or even identity and data. Tokenization can create
several types of tokens. Stablecoins, a type of cryptocurrency pegged to
real-world money designed to be fungible, or replicable, are one example.
Another type of token is an NFT—a nonfungible token, or a token that can’t be
replicated—which is a digital proof of ownership people can buy and sell.
Tokenization is potentially a big deal. Industry experts have forecast up to $5
trillion in tokenized digital-securities trade volume by 2030. There’s been hype
around digital-asset tokenization for years, since its introduction back in
2017. But despite the big predictions, it hasn’t yet caught on in a meaningful
way. We are seeing slow movement: US-based fintech infrastructure firm
Broadridge now facilitates more than $1 trillion monthly on its distributed
ledger platform.
MVP or TVP? Why Your Internal Developer Platform Needs Both

“TVP is about ‘thinness’ to try and avoid a massive platform. TVP is something
that remains throughout an organizational evolution — it should always be the
thinnest viable — whereas MVP is normally the first stage of something larger.”
This shift toward investment in long-term thinness is extremely important.
Gregor Hohpe calls this a “sinking platform” in his 2022 PlatformCon talk “The
Magic of Platforms.” ... You can leave your platform the same because you
invested all this kind of money, and we call this a sinking platform as the
water level rises, right; it might be justified from investment, but you are
kind of duplicating things that are now available in the base platform.” Hohpe
goes on to describe how platform teams need to intentionally decide on their
philosophy when it comes to supporting their platform: “Or you build a ‘floating
platform’ where, when the base platform gains the capabilities you have built,
you say ‘Oh, perfect! I don’t need my part anymore. I can let the base platform
handle that, and I can innovate further on top. I build new things.'”
7 Blockchain Technology Mistakes You Should Watch Out For
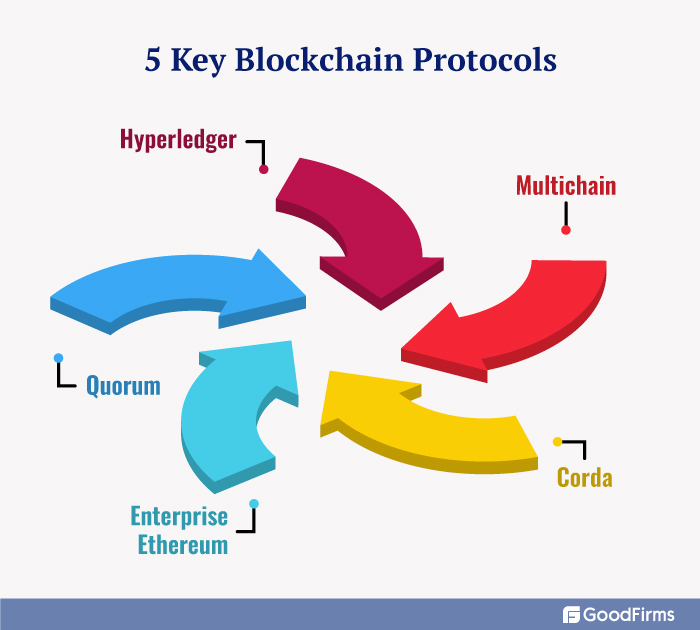
The application of Blockchain for secure information exchange and storing
records leads to many wrong beliefs. CIOs get confused between Data Base
Management Systems (DBMS) and blockchain. The existing blockchain platforms
cannot provide support for complex data models and do not provide assurance of
high throughput or low latency. They were built to provide an immutable,
authoritative, and trusted record of events among a dynamic assortment of
unrelated stakeholders. ... Smart Contract is a code that automatically
executes legally relevant events and actions that are part of the agreement.
The main utility of Smart Contracts is to reduce the need for trusted
intermediaries, prevent fraud and reduce arbitration costs. They are commonly
associated with cryptocurrencies like Bitcoin and are fundamental building
blocks of Decentralized Finance (DeFi) applications. Although, at present
Smart Contracts are not necessarily an agreement that has been approved by
law, with some countries being an exception.
Practicing Good Green Governance Leads to Profits

Let’s begin by defining green governance. It refers to a set of principles and
practices aimed at promoting environmental sustainability and responsible
management of natural resources within a clear governance and decision-making
framework. A green-minded corporation should integrate environmental
considerations into policies, regulations, and actions throughout all
divisions of its business. Green governance aims to balance economic and
environmental practices to create a profitable and sustainable future. ...
Practicing green governance requires a holistic approach that considers the
interconnectedness of environmental, operational, and economic systems to
balance human needs and the health of the planet with the company’s bottom
line and valuation. That balance is what helps ensure a sustainable and
prosperous future for all stakeholders. ... Many companies want to showcase
their greenness in a credible and trustworthy way but find the current system
of backward-looking, voluntary standards and the myriad of ESG metrics to be
daunting, arduous, and costly.
The Future is Now: IoT and the Evolution of Business Computing

The proliferation of IoT devices and sensors is generating massive amounts of
data that provides invaluable insights for business decision-making. However,
organizations need talent to properly analyze and derive meaning from these
huge IoT datasets. A business management and accounting online degree is
valuable in helping to develop the analytics skills needed to fully capitalize
on IoT capabilities. These programs prepare the next generation of data-driven
business leaders who will drive transformative change through IoT adoption.
With access to real-time data from across the enterprise, managers can gain
unprecedented visibility into operations. Marketers can analyze IoT data to
understand customer behavior patterns and rapidly adjust campaigns. Supply
chain personnel can identify and resolve bottlenecks as they occur. Executives
can track core business metrics in real time to guide strategic decisions. The
sheer volume of IoT data brings a paradigm shift in business computing where
decisions are proactive, not reactive.
Psychological safety at the workplace
People show up at work with different states of mental well-being. So, empathy
is absolutely non-negotiable. A meaningful way to be empathetic is to be
mindful of our language and its impact on the other person. For instance,
instead of the confrontational approach where one might say, “Your code is
quite bad and not what I expected” say, “I know that you are capable of
writing great code. Let’s figure out what happened this time.” This manner of
checking in with each other on their state of mind and creating a space for
team members to discuss their mental health without fear of judgment is a move
in the right direction. ... Welcome different perspectives, and when people
offer them, disagree with respect. People tend to cushion their ideas when
they fear judgment. For instance, they might say, “this is probably a silly
idea,” or “this may be a dumb question.” Reassure them that all ideas are
welcome. Watch out for groupthink — the tendency of the minority to stay
silent in order not to upset the majority. Invite opinions from
everyone.
The future of augmented reality is AI

Whenever we in the tech media or tech industry think or talk about AR, we tend
to focus on what kind of holographic imagery we might see superimposed on the
real world through our AR glasses. We imagine hands-free Pokémon Go, or
radically better versions of Google Glass. But since the generative
AI/LLM-based chatbot revolution struck late last year, it has become
increasingly clear that of all the pieces that make up an AR experience,
holographic digital virtual objects is the least important. The glasses are
necessary. Android phones and iPhones have had “augmented reality”
capabilities for years, and nobody cares because looking at your phone doesn’t
compare to just seeing the world hands-free through glasses. The cameras and
other sensors are necessary. It’s impossible to augment reality if your device
has no way to perceive reality. The AI is necessary. We need AI to interpret
and make sense of arbitrary people, objects, and activity in our fields of
view.
How to maintain a harmonious workplace atmosphere in multigenerational firms

Ensuring the well-being of a multigenerational workforce is crucial for any
organisation. HR can play a key role in this by implementing policies and
programs that cater to the unique needs and preferences of different
generations. For instance, offering flexible work arrangements, mentoring
programs, and personalised professional development opportunities can help
employees of all ages feel valued and supported. Additionally, providing
access to resources and benefits that address specific health and wellness
concerns can help ensure that employees stay healthy and productive throughout
their careers. “By prioritising the well-being of all employees, regardless of
age or background, organisations can create a more inclusive and supportive
workplace environment that promotes work-life balance. Creating a diverse,
equitable, and inclusive workplace is essential for fostering a positive and
productive work environment.
Oh No, the Software Consultants Are Coming!

Sadly, consultants are still used to back up a decision that has already been
made by management. So a sudden presence of consultants is often viewed as
positively as the arrival of sharks around a stalled boat. But in most cases,
consultants are just hired to see why an area is not performing in some way.
It is perfectly common for them to tell management that they are the problem.
That might shorten the engagement, but you can do that sort of thing when you
are not an employee. More realistically, consultants might need to explain to
staff why systematic changes will improve the company’s prospects, which still
leaves the unspoken threat about what happens if things don’t change. And yet,
many developers do fall into ruts and moving on may truly be the best thing to
do. And of course, escaping a death march project is not always the worst
thing that can happen. By the way, if you are staff, always ask consultants
for career advice. Not only is it free, but it won’t be biased by your
background or colored by employer motives.
CBDC and stablecoins: Early coexistence on an uncertain road
It is too early to confidently forecast the trajectory and endgame for CBDCs
and stablecoins, given the multitude of unresolved design factors still in
play. For instance, will central banks focus first on retail or wholesale use
cases, and emphasize domestic or cross-border applications? And how rapidly
will national agencies pursue regulation of stablecoins prior to issuing their
own CBDCs? To begin to understand some of the potential scenarios, we need to
appreciate the variety and applications of CBDCs and stablecoins. There is no
single CBDC issuance model, but rather a continuum of approaches being piloted
in various countries. ... At the opposite end of the spectrum, China’s CBDC
pilot relies on private-sector banks to distribute and maintain eCNY (digital
yuan) accounts for their customers. The ECB approach under consideration
involves licensed financial institutions each operating a permissioned node of
the blockchain network as a conduit for distribution of a digital euro.
Quote for the day:
"Anything is possible when you have
the right people there to support you." -- Misty Copeland