What You Need to Know About Securing 5G Networks and Communication

IoT devices have exploded over the past several years, and this growth shows
no signs of slowing down. And all of these devices have one thing in common:
Remote connectivity via a public 4G or 5G network, or, increasingly, a private
5G network. This explosion of connected devices creates an expanded attack
surface, since the entire network is only as secure as its weakest link.
Specifically, just because a network is secure, any devices attached to it
that are not secure in how they communicate or receive updates create a breach
opportunity. As a result, it’s essential that every device has an identity and
each identity is managed. This might sound daunting, but it’s not as complex
as it seems at first – it goes back to the building blocks of PKI. Much of the
security industry has a handle on running PKI for enterprise networks in their
organization (think laptops, mobile devices, and so on). Therefore, security
teams are also enabled to do PKI for these smart devices — it’s the same
approach for a different endpoint.
To AI Hell and Back: Finding Salvation Through Empathy
Iannopollo said the guides assisting in AI Hell could come from IT, marketing,
or the executive team. “All of them understand the incredible opportunity of
generative AI and the unparalleled transformative power of the new technology.
And they know that without adequate security, privacy, and risk governance.”
According to Forrester’s research, 36% of respondents in those groups said
privacy and security are the greatest barriers to generative AI adoption,
while another 31% said governance and risk were the biggest hurdle. Another
61% cited concerns that GenAI could violate privacy and data protection laws
like the EU’s GDPR. “So, concerns exist,” she said. “But remember, Hell is a
place of confusion.” As more frameworks come online -- more regulations, there
may be less confusion and the guides will help businesses assess their AI
adoption. ... Once you are out of AI Hell, like Dante, your story is not
complete. Dante had to first stop in purgatory. And after spending time in AI
Hell dealing with the questions of risk and threats, businesses will need to
figure out a compliance strategy.
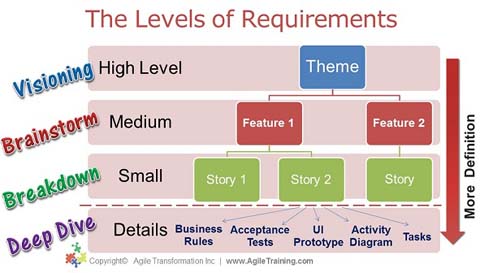
Conceptual vs. Logical vs. Physical Data Modeling

“Companies need to do Data Modeling to solve a specific business problem or
answer a business question,” summarized Aiken. IT and businesses need to share
goals and understanding to get to a data solution. Moreover, there needs to be
a common language between systems for data to flow smoothly. However, slapping
together any model or a big overarching enterprise architecture will not be
helpful. A data model needs to achieve a particular purpose, and getting there
requires a systematic process. Aiken’s three-dimensional model evolution
framework provides resources for an improved data platform. It considers the
existing architecture and the evolution needed to meet business needs and
validates that stakeholders and builders are on the same page. A combination
of conceptual, logical, and physical data models promises meaningful and
useful results, especially where business and IT need to achieve a common
objective. Doing the data modeling correctly and understanding requirements
frees up 20% time and money for corporations to leverage their data
capabilities and get more value from them.
AI: The indispensable ally in the information age
The implementation of AI in data centers must be viewed through a dual lens:
risk mitigation and knowledge preservation. As we face a generational turnover
in expertise within the industry, with a significant proportion of seasoned
professionals retiring, there's an urgent need to capture and transfer this
wealth of knowledge. AI and machine learning algorithms, when correctly
trained and utilized, can play a crucial role in bridging this knowledge gap.
By learning from clean data, and benchmarking and decisions made by
experienced personnel, AI systems can emulate, and eventually, enhance these
expert-driven processes. This transfer of knowledge is vital not just for
maintaining current operational standards, but also for paving the way for
more advanced, efficient, and resilient data center architectures. Moreover,
AI's potential in managing and reducing operational risks in data centers is
monumental. Advanced predictive analytics can foresee and mitigate potential
failures, while continuous monitoring AI systems can identify anomalies that
hint at future problems, allowing for preemptive maintenance and risk
aversion.
Shadowy Hack-for-Hire Group Behind Sprawling Web of Global Cyberattacks

The cybersecurity firm's exhaustive analysis of data that Reuters journalists
collected showed near-conclusive links between Appin and numerous data theft
incidents. These included theft of email and other data by Appin from
Pakistani and Chinese government officials. SentinelOne also found evidence of
Appin carrying out defacement attacks on sites associated with the Sikh
religious minority community in India and of at least one request to hack into
a Gmail account belonging to a Sikh individual suspected of being a terrorist.
"The current state of the organization significantly differs from its status a
decade ago," says Tom Hegel, principal threat researcher at SentinelLabs. "The
initial entity, 'Appin,' featured in our research, no longer exists but can be
regarded as the progenitor from which several present-day hack-for-hire
enterprises have emerged," he says. Factors such as rebranding, employee
transitions, and the widespread dissemination of skills contribute to Appin
being recognized as the pioneering hack-for-hire group in India, he
says.
Security Firm COO Hacked Hospitals to Drum Up Business

According to the plea agreement, Singla on Sept. 27, 2018, knowingly
transmitted a command that resulted in an unauthorized modification to the
configuration template for the ASCOM phone system at Gwinnett Medical Center's
Duluth hospital campus. As a result, all of the Duluth hospital's ASCOM phones
that were connected to the phone system during Singla's transmission were
rendered inoperable, and more than 200 ASCOM handset devices were taken
offline, the court document says. Those phones were used by Duluth hospital
staff, including doctors and nurses, for internal communication, including for
"code blue" emergencies. The ASCOM phones were used to place calls outside of
the hospital, the court document says. On that same day, Singla - without
authorization - obtained information including names, birthdates and the sex
of more than 300 patients from a Hologic R2 Digitizer connected to a mammogram
machine at Gwinnett's Lawrenceville hospital campus, the document says. The
digitizer, which was accessible through Gwinnett's virtual private network,
was protected by a password.
How to Structure and Build a Team For Long-Term Success
Leaders have to be careful not to get caught in a situation where somebody
could misconstrue their kindness or attention, but being in leadership doesn't
have to mean sacrificing gaining friendships. Balance being too friendly with
being able to offer necessary corrections. By nature, I tend to be a people
pleaser, so I must work on being tougher — especially early in relationships.
After my collegiate basketball career ended, I became a high school basketball
referee. I found that the whole game went smoother if I was tough in the first
quarter of a game. It is important to establish a sense of control when they
first hire a new team member, and then they can infuse the second, third and
fourth quarters with more friendship. Leaders can have situations that test
the relationships they're working to build. Let's say someone has two people
on their team, and they have to decide which one gets promoted. The one who
didn't get promoted might feel like the leader let them down. Leaders must
maintain enough professional distance so that an employee knows it was not due
to favoritism in this situation.
Data is Everybody’s Business: The Fundamentals of Data Monetization

Companies get better at data monetization by practicing it. “Rather than wait
for the right set of capabilities to magically appear,” Owens says,
“businesses should start engaging in monetization activities. The learning and
the returns come from doing, not from talking about doing. For starters,
organizations could choose one process or product to improve or a single
business challenge to solve with data.” Creating data assets also means
creating organizational governance so that the right people use the data in
the right ways. Data assets can be monetized only after data is properly
cleaned, permissioned with the right security, and made accessible to
authorized users. “If you aren’t purposely managing and monetizing your data,
it won’t pay off,” says Wixom. A big problem with data is that everybody is
starting from scratch all the time, says Wixom. “There isn’t enough attention
to accumulating knowledge and skills for the future benefit of the
organization. But if you create data assets and establish enterprise
capabilities to manage them properly, data can be reused limitlessly for all
kinds of value-creating reasons across an organization.”
Blockchain could save AI by cracking open the black box
Blockchain is finally being unchained from crypto, and many now see its
potential as a foundation of support and validation for another emerging
technology -- AI. Blockchain -- and other distributed ledger technologies --
could even help solve AI's black box problem "by providing a transparent,
immutable ledger to monitor model training and trace decision-making
processes," according to the authors of a new report. "This gives
organizations the ability to audit the data and algorithms used, enabling
greater security and trust in AI systems." ... "As AI operations go
mainstream -- and as people raise concerns about the technology -- leaders
are recognizing the need for a more responsible AI that prioritizes data
security and transparency," the survey's authors point out. "Ensuring
trustworthiness and reliability of their AI tools is a top priority for
businesses, and blockchain is the turnkey solution for addressing the risks
that come with AI implementation." Executives have developed a greater level
of understanding of blockchain. Seventy-seven percent say they fully
understand blockchain and can explain the value of it to their teams -- up
five percentage points over last year's survey.
FinOps Debuts Cloud Transparency Standards
Given that the project is backed by the largest players in the multi-billion
dollar cloud market, several large enterprise-level users such as Goldman
Sachs and Walmart, have also backed this initiative. “We are establishing
FOCUS as the cornerstone lexicon of FinOps by providing an open source,
vendor-agnostic specification featuring a unified schema and language,” says
Mike Fuller CTO at the FinOps Foundation. “With this release, we are paving
the way for FOCUS to foster collaboration among major cloud providers,
FinOps vendors, leading SaaS providers and forward-thinking FinOps
enterprises to establish a unified, serviceable framework for cloud billing
data, increasing trust in the data and making it easier to understand the
value of cloud spend,” Fuller said in a statement. As readers would know,
cloud operators provide customers with billing data providing the costs of
services they use, which also includes granular details around individual
product costs, and discounts, if any. Businesses use this billing data from
the service providers to track their spends, forecast future costs and build
their SaaS budgets.
Quote for the day:
"Pursue one great decisive aim with force and determination." --
Carl Von Clause Witz