Quote for the day:
“Everything you’ve ever wanted is on the other side of fear.” -- George Addair
🎧 Listen to this digest on YouTube Music
▶ Play Audio DigestDuration: 22 mins • Perfect for listening on the go.
How enterprises can manage LLM costs: A practical guide
 Managing large language model (LLM) costs has become a critical priority for
enterprises as generative and agentic AI deployments scale. According to the
InformationWeek guide, LLM expenses are primarily driven by token pricing and
consumption, factors that remain notoriously difficult to forecast due to the
iterative nature of AI workflows. This unpredictability is exacerbated by
dynamic vendor pricing, a lack of specialized FinOps tools, and limited user
awareness regarding how complex queries impact the bottom line. To mitigate
these financial risks, the article recommends a multi-pronged approach: matching
task complexity to model capability by using lower-cost LLMs for routine work,
and implementing technical optimizations like response caching and prompt
compression to reduce token usage. Furthermore, enterprises should utilize
prompt libraries of validated, efficient inputs and leverage query batching for
non-urgent tasks to access vendor discounts. While self-hosting models
eliminates third-party token fees, the guide warns of significant underlying
costs in infrastructure and energy. Ultimately, successful cost management
requires a strategic balance where the productivity gains of AI clearly outweigh
the operational expenditures. By proactively setting token allowances and
comparing vendor rates, CIOs can prevent AI budgets from spiraling while still
fostering innovation across the organization.
Managing large language model (LLM) costs has become a critical priority for
enterprises as generative and agentic AI deployments scale. According to the
InformationWeek guide, LLM expenses are primarily driven by token pricing and
consumption, factors that remain notoriously difficult to forecast due to the
iterative nature of AI workflows. This unpredictability is exacerbated by
dynamic vendor pricing, a lack of specialized FinOps tools, and limited user
awareness regarding how complex queries impact the bottom line. To mitigate
these financial risks, the article recommends a multi-pronged approach: matching
task complexity to model capability by using lower-cost LLMs for routine work,
and implementing technical optimizations like response caching and prompt
compression to reduce token usage. Furthermore, enterprises should utilize
prompt libraries of validated, efficient inputs and leverage query batching for
non-urgent tasks to access vendor discounts. While self-hosting models
eliminates third-party token fees, the guide warns of significant underlying
costs in infrastructure and energy. Ultimately, successful cost management
requires a strategic balance where the productivity gains of AI clearly outweigh
the operational expenditures. By proactively setting token allowances and
comparing vendor rates, CIOs can prevent AI budgets from spiraling while still
fostering innovation across the organization.The Death of the Firewall
The article "The Death of the Firewall" by Chandrodaya Prasad explores why the
firewall has survived decades of premature obituaries to remain a cornerstone
of modern cybersecurity. Rather than becoming obsolete, the technology has
successfully transitioned from a standalone perimeter appliance into a
versatile, integrated architecture. The global firewall market continues to
expand, currently valued at approximately $6 billion, as organizations face
complex security challenges that identity-centric models alone cannot solve.
The firewall has evolved through critical phases, including convergence with
SD-WAN for simplified networking and integration with cloud-based Security
Service Edge (SSE) frameworks. Crucially, it serves as a necessary enforcement
point for inspecting encrypted traffic and implementing post-quantum
cryptography. It remains indispensable in Operational Technology (OT) sectors,
such as manufacturing and healthcare, where legacy systems and IoT devices
cannot support endpoint agents or tolerate cloud-based latency. For these
heavily regulated industries, the firewall is not merely an architectural
choice but a fundamental requirement for regulatory compliance. Ultimately,
the firewall’s endurance is attributed to its ongoing adaptation, offloading
intelligence to the cloud while maintaining essential local execution. As
cyber threats grow more sophisticated due to AI, the firewall is evolving into
a vital, persistent component of a unified security fabric.
 The Computerworld article "AI clones: The good, the bad, and the ugly"
examines the dual-edged nature of digital personas, categorizing their
applications into three distinct ethical spheres. Under "the good," the author
highlights authorized use cases where public figures like Imran Khan and Eric
Adams employ AI voice clones to transcend physical or linguistic barriers,
amplifying their reach and accessibility. However, "the bad" introduces the
problematic rise of nonconsensual professional cloning. Tools like "Colleague
Skill" enable individuals to replicate the expertise and communication styles
of coworkers or supervisors, often to retain institutional knowledge or
manipulate workplace dynamics. This section also underscores the threat of
sophisticated financial fraud perpetrated through voice impersonation.
Finally, "the ugly" explores the deeply controversial territory of "Ex-Partner
Skill" and "digital resurrection." These tools allow users to simulate
interactions with former or deceased loved ones by mimicking subtle nuances
and shared memories, raising profound ethical concerns regarding consent and
emotional health. Ultimately, the piece argues that as AI cloning technology
becomes more accessible, society must navigate the erosion of reality and
establish clear boundaries to protect individual identity and privacy in an
increasingly synthetic world.
The Computerworld article "AI clones: The good, the bad, and the ugly"
examines the dual-edged nature of digital personas, categorizing their
applications into three distinct ethical spheres. Under "the good," the author
highlights authorized use cases where public figures like Imran Khan and Eric
Adams employ AI voice clones to transcend physical or linguistic barriers,
amplifying their reach and accessibility. However, "the bad" introduces the
problematic rise of nonconsensual professional cloning. Tools like "Colleague
Skill" enable individuals to replicate the expertise and communication styles
of coworkers or supervisors, often to retain institutional knowledge or
manipulate workplace dynamics. This section also underscores the threat of
sophisticated financial fraud perpetrated through voice impersonation.
Finally, "the ugly" explores the deeply controversial territory of "Ex-Partner
Skill" and "digital resurrection." These tools allow users to simulate
interactions with former or deceased loved ones by mimicking subtle nuances
and shared memories, raising profound ethical concerns regarding consent and
emotional health. Ultimately, the piece argues that as AI cloning technology
becomes more accessible, society must navigate the erosion of reality and
establish clear boundaries to protect individual identity and privacy in an
increasingly synthetic world.
 On May 7, 2026, a significant fire erupted at the NorthC data center in
Almere, Netherlands, triggering a regional emergency response and
demonstrating the fragility of modern digital infrastructure. The blaze, which
originated in the technical compartment housing critical power systems, forced
emergency services to order a total power shutdown. Although the server rooms
remained largely protected by fire-resistant separations, the resulting outage
caused widespread, often bizarre, secondary consequences. Beyond standard
digital disruptions, the failure crippled physical security at Utrecht
University, where students and staff were locked out of buildings and even
restrooms because electronic access card systems failed completely. Public
transit in Utrecht faced communication breakdowns, while healthcare billing
services and numerous pharmacies across the country saw their operations grind
to a halt. This incident serves as a stark wake-up call, proving that even
ISO-certified facilities with redundant backups are susceptible to
catastrophic failure when authorities prioritize safety over continuity. It
underscores a critical lesson for organizations: business continuity plans
must account for the unpredictable ripple effects of physical infrastructure
loss. The event highlights the inherent risks of centralized digital
dependencies, revealing that a localized technical fire can effectively
paralyze diverse sectors of society far beyond the immediate flames.
On May 7, 2026, a significant fire erupted at the NorthC data center in
Almere, Netherlands, triggering a regional emergency response and
demonstrating the fragility of modern digital infrastructure. The blaze, which
originated in the technical compartment housing critical power systems, forced
emergency services to order a total power shutdown. Although the server rooms
remained largely protected by fire-resistant separations, the resulting outage
caused widespread, often bizarre, secondary consequences. Beyond standard
digital disruptions, the failure crippled physical security at Utrecht
University, where students and staff were locked out of buildings and even
restrooms because electronic access card systems failed completely. Public
transit in Utrecht faced communication breakdowns, while healthcare billing
services and numerous pharmacies across the country saw their operations grind
to a halt. This incident serves as a stark wake-up call, proving that even
ISO-certified facilities with redundant backups are susceptible to
catastrophic failure when authorities prioritize safety over continuity. It
underscores a critical lesson for organizations: business continuity plans
must account for the unpredictable ripple effects of physical infrastructure
loss. The event highlights the inherent risks of centralized digital
dependencies, revealing that a localized technical fire can effectively
paralyze diverse sectors of society far beyond the immediate flames.
AI clones: the good, the bad, and the ugly
 The Computerworld article "AI clones: The good, the bad, and the ugly"
examines the dual-edged nature of digital personas, categorizing their
applications into three distinct ethical spheres. Under "the good," the author
highlights authorized use cases where public figures like Imran Khan and Eric
Adams employ AI voice clones to transcend physical or linguistic barriers,
amplifying their reach and accessibility. However, "the bad" introduces the
problematic rise of nonconsensual professional cloning. Tools like "Colleague
Skill" enable individuals to replicate the expertise and communication styles
of coworkers or supervisors, often to retain institutional knowledge or
manipulate workplace dynamics. This section also underscores the threat of
sophisticated financial fraud perpetrated through voice impersonation.
Finally, "the ugly" explores the deeply controversial territory of "Ex-Partner
Skill" and "digital resurrection." These tools allow users to simulate
interactions with former or deceased loved ones by mimicking subtle nuances
and shared memories, raising profound ethical concerns regarding consent and
emotional health. Ultimately, the piece argues that as AI cloning technology
becomes more accessible, society must navigate the erosion of reality and
establish clear boundaries to protect individual identity and privacy in an
increasingly synthetic world.
The Computerworld article "AI clones: The good, the bad, and the ugly"
examines the dual-edged nature of digital personas, categorizing their
applications into three distinct ethical spheres. Under "the good," the author
highlights authorized use cases where public figures like Imran Khan and Eric
Adams employ AI voice clones to transcend physical or linguistic barriers,
amplifying their reach and accessibility. However, "the bad" introduces the
problematic rise of nonconsensual professional cloning. Tools like "Colleague
Skill" enable individuals to replicate the expertise and communication styles
of coworkers or supervisors, often to retain institutional knowledge or
manipulate workplace dynamics. This section also underscores the threat of
sophisticated financial fraud perpetrated through voice impersonation.
Finally, "the ugly" explores the deeply controversial territory of "Ex-Partner
Skill" and "digital resurrection." These tools allow users to simulate
interactions with former or deceased loved ones by mimicking subtle nuances
and shared memories, raising profound ethical concerns regarding consent and
emotional health. Ultimately, the piece argues that as AI cloning technology
becomes more accessible, society must navigate the erosion of reality and
establish clear boundaries to protect individual identity and privacy in an
increasingly synthetic world.
Fire at Dutch data center has many unintended consequences
 On May 7, 2026, a significant fire erupted at the NorthC data center in
Almere, Netherlands, triggering a regional emergency response and
demonstrating the fragility of modern digital infrastructure. The blaze, which
originated in the technical compartment housing critical power systems, forced
emergency services to order a total power shutdown. Although the server rooms
remained largely protected by fire-resistant separations, the resulting outage
caused widespread, often bizarre, secondary consequences. Beyond standard
digital disruptions, the failure crippled physical security at Utrecht
University, where students and staff were locked out of buildings and even
restrooms because electronic access card systems failed completely. Public
transit in Utrecht faced communication breakdowns, while healthcare billing
services and numerous pharmacies across the country saw their operations grind
to a halt. This incident serves as a stark wake-up call, proving that even
ISO-certified facilities with redundant backups are susceptible to
catastrophic failure when authorities prioritize safety over continuity. It
underscores a critical lesson for organizations: business continuity plans
must account for the unpredictable ripple effects of physical infrastructure
loss. The event highlights the inherent risks of centralized digital
dependencies, revealing that a localized technical fire can effectively
paralyze diverse sectors of society far beyond the immediate flames.
On May 7, 2026, a significant fire erupted at the NorthC data center in
Almere, Netherlands, triggering a regional emergency response and
demonstrating the fragility of modern digital infrastructure. The blaze, which
originated in the technical compartment housing critical power systems, forced
emergency services to order a total power shutdown. Although the server rooms
remained largely protected by fire-resistant separations, the resulting outage
caused widespread, often bizarre, secondary consequences. Beyond standard
digital disruptions, the failure crippled physical security at Utrecht
University, where students and staff were locked out of buildings and even
restrooms because electronic access card systems failed completely. Public
transit in Utrecht faced communication breakdowns, while healthcare billing
services and numerous pharmacies across the country saw their operations grind
to a halt. This incident serves as a stark wake-up call, proving that even
ISO-certified facilities with redundant backups are susceptible to
catastrophic failure when authorities prioritize safety over continuity. It
underscores a critical lesson for organizations: business continuity plans
must account for the unpredictable ripple effects of physical infrastructure
loss. The event highlights the inherent risks of centralized digital
dependencies, revealing that a localized technical fire can effectively
paralyze diverse sectors of society far beyond the immediate flames.The hidden cost of front-end complexity
 The article "The Hidden Cost of Front-End Complexity" explores how modern web
development has transitioned from solving rendering challenges to facing
profound system design issues. While current frameworks have optimized UI
performance and component modularity, complexity has not disappeared; instead,
it has shifted "up the stack" into application logic and state coordination.
Modern front-end engineers now shoulder responsibilities once reserved for
multiple infrastructure layers, managing distributed APIs, CI/CD pipelines,
and intricate data flows that reside within the browser. The author argues
that the true "hidden cost" of this evolution is the significantly increased
cognitive load required for developers to navigate a dense web of invisible
dependencies and reactive chains. Consequently, development cycles slow down
and maintainability suffers when state relationships remain opaque or poorly
defined. To address these architectural failures, the industry must pivot from
debating framework syntax or rendering speed to prioritizing a "state-first"
architecture. In this paradigm, the UI is treated as a simple projection of a
clearly modeled state. By shifting the focus toward explicit state
representation and observable system design, engineering teams can manage the
inherent complexity of large-scale applications more effectively. Ultimately,
the future of the front-end lies in building systems that are fundamentally
easier to reason about.
The article "The Hidden Cost of Front-End Complexity" explores how modern web
development has transitioned from solving rendering challenges to facing
profound system design issues. While current frameworks have optimized UI
performance and component modularity, complexity has not disappeared; instead,
it has shifted "up the stack" into application logic and state coordination.
Modern front-end engineers now shoulder responsibilities once reserved for
multiple infrastructure layers, managing distributed APIs, CI/CD pipelines,
and intricate data flows that reside within the browser. The author argues
that the true "hidden cost" of this evolution is the significantly increased
cognitive load required for developers to navigate a dense web of invisible
dependencies and reactive chains. Consequently, development cycles slow down
and maintainability suffers when state relationships remain opaque or poorly
defined. To address these architectural failures, the industry must pivot from
debating framework syntax or rendering speed to prioritizing a "state-first"
architecture. In this paradigm, the UI is treated as a simple projection of a
clearly modeled state. By shifting the focus toward explicit state
representation and observable system design, engineering teams can manage the
inherent complexity of large-scale applications more effectively. Ultimately,
the future of the front-end lies in building systems that are fundamentally
easier to reason about.How Federated Identity and Cross-Cloud Authentication Actually Work at Scale
This article discusses the critical shift from traditional, secrets-based authentication to Federated Identity and Workload Identity Federation (WIF) within modern DevOps and multi-cloud environments. Historically, integrating services across clouds (such as Azure, AWS, or GCP) required storing long-lived service principal keys or static credentials, which posed significant security risks including credential leakage and management overhead. To solve this, Federated Identity utilizes OpenID Connect (OIDC) to establish a trust relationship between an external identity provider and a cloud resource. Instead of using persistent secrets, a workload—such as a GitHub Action or an Azure DevOps pipeline—requests a short-lived, ephemeral token from its identity provider. This token is then exchanged for a temporary access token from the target cloud service, which automatically expires after the task is completed. This approach eliminates the need for manual secret rotation and significantly reduces the attack surface by ensuring no permanent credentials exist to be stolen. By leveraging Managed Identities and structured OIDC exchanges, organizations can achieve a "zero-trust" authentication model that scales across diverse cloud providers, providing a more secure, automated, and maintainable framework for cross-cloud resource management and CI/CD workflows.Ten years later, has the GDPR fulfilled its purpose?
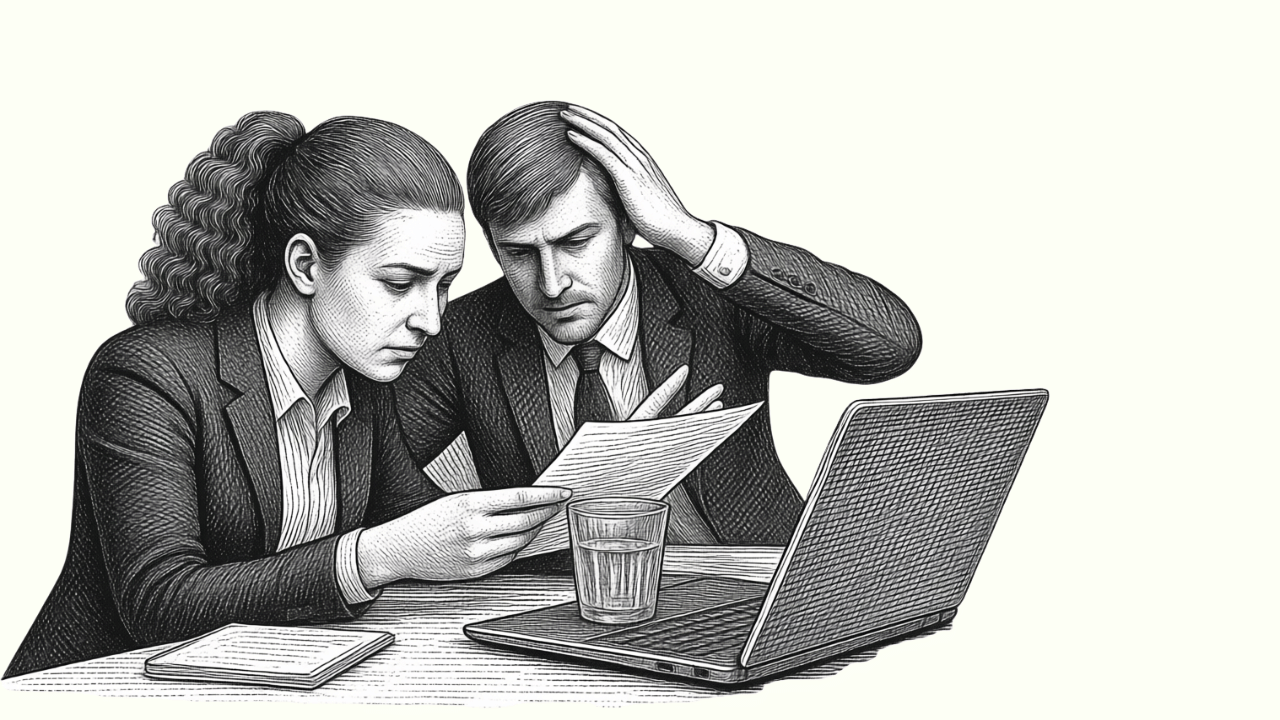
 A decade after its adoption, the General Data Protection Regulation (GDPR)
presents a bittersweet legacy, having fundamentally reshaped global corporate
culture while facing significant modern hurdles. The regulation successfully
elevated privacy from a legal footnote to a core management priority,
institutionalizing principles like "privacy by design" and establishing a gold
standard for international digital governance. However, experts highlight a
growing disconnect between regulatory intent and practical application. While
the GDPR empowered citizens with theoretical rights, the reality often
manifests as "consent fatigue" through ubiquitous cookie pop-ups rather than
providing meaningful control. Furthermore, the enforcement landscape reveals a
stark gap; despite billions in issued fines, the actual collection rate
remains remarkably low due to protracted legal appeals and the complexity of
the "one-stop-shop" mechanism. International data transfers also remain a
legal Achilles' heel, plagued by ongoing uncertainty across borders. The
emergence of generative AI further complicates this framework, as massive
training datasets and opaque algorithms challenge core tenets like data
minimization and transparency. Additionally, the proliferation of overlapping
EU regulations has created a "regulatory avalanche," making compliance
increasingly difficult for smaller organizations. Ultimately, the article
suggests that while the GDPR fulfilled its primary purpose, it now requires
urgent refinement to remain relevant in a complex, AI-driven digital
economy.
A decade after its adoption, the General Data Protection Regulation (GDPR)
presents a bittersweet legacy, having fundamentally reshaped global corporate
culture while facing significant modern hurdles. The regulation successfully
elevated privacy from a legal footnote to a core management priority,
institutionalizing principles like "privacy by design" and establishing a gold
standard for international digital governance. However, experts highlight a
growing disconnect between regulatory intent and practical application. While
the GDPR empowered citizens with theoretical rights, the reality often
manifests as "consent fatigue" through ubiquitous cookie pop-ups rather than
providing meaningful control. Furthermore, the enforcement landscape reveals a
stark gap; despite billions in issued fines, the actual collection rate
remains remarkably low due to protracted legal appeals and the complexity of
the "one-stop-shop" mechanism. International data transfers also remain a
legal Achilles' heel, plagued by ongoing uncertainty across borders. The
emergence of generative AI further complicates this framework, as massive
training datasets and opaque algorithms challenge core tenets like data
minimization and transparency. Additionally, the proliferation of overlapping
EU regulations has created a "regulatory avalanche," making compliance
increasingly difficult for smaller organizations. Ultimately, the article
suggests that while the GDPR fulfilled its primary purpose, it now requires
urgent refinement to remain relevant in a complex, AI-driven digital
economy.Bunkers, Mines, and Caverns: The World of Underground Data Centers
 The article "Bunkers, Mines, and Caverns: The World of Underground Data
Centers" by Nathan Eddy explores the growing strategic niche of subterranean
infrastructure through the adaptive reuse of retired mines and Cold War-era
bunkers. Predominantly found in North America and Northern Europe, these
facilities offer a unique "underground advantage" centered on unparalleled
physical security, environmental resilience, and inherent cooling efficiency.
By repurposing sites like Iron Mountain’s Pennsylvania campus or Norway’s
Lefdal Mine, operators benefit from a natural, impenetrable shield against
extreme weather and external threats, making them ideal for high-security or
mission-critical workloads. Furthermore, underground locations often bypass
local "NIMBY" resistance because they are invisible to surrounding
communities. However, the article notes that subterranean deployments present
significant engineering and logistical hurdles. Managing humidity,
ventilation, and heat dissipation requires complex systems, and retrofitting
older structures can be costly. Site selection is also intricate, requiring
rigorous assessments of structural stability and risks like water ingress or
geological faults. Despite these challenges, underground data centers are no
longer a novelty but a proven, permanent fixture in the industry. They are
increasingly attractive in land-constrained hubs like Singapore and for highly
regulated sectors, providing a sustainable and secure alternative to
traditional above-ground facilities.
The article "Bunkers, Mines, and Caverns: The World of Underground Data
Centers" by Nathan Eddy explores the growing strategic niche of subterranean
infrastructure through the adaptive reuse of retired mines and Cold War-era
bunkers. Predominantly found in North America and Northern Europe, these
facilities offer a unique "underground advantage" centered on unparalleled
physical security, environmental resilience, and inherent cooling efficiency.
By repurposing sites like Iron Mountain’s Pennsylvania campus or Norway’s
Lefdal Mine, operators benefit from a natural, impenetrable shield against
extreme weather and external threats, making them ideal for high-security or
mission-critical workloads. Furthermore, underground locations often bypass
local "NIMBY" resistance because they are invisible to surrounding
communities. However, the article notes that subterranean deployments present
significant engineering and logistical hurdles. Managing humidity,
ventilation, and heat dissipation requires complex systems, and retrofitting
older structures can be costly. Site selection is also intricate, requiring
rigorous assessments of structural stability and risks like water ingress or
geological faults. Despite these challenges, underground data centers are no
longer a novelty but a proven, permanent fixture in the industry. They are
increasingly attractive in land-constrained hubs like Singapore and for highly
regulated sectors, providing a sustainable and secure alternative to
traditional above-ground facilities.Why the future of software is no longer written — it is architected, governed and continuously learned
 The article argues that software development is undergoing a fundamental
structural shift, moving from manual coding to a paradigm defined by
architecture, governance, and continuous learning. As generative AI and
agentic systems take over the heavy lifting of building code, the role of the
developer is evolving into that of an "intelligence orchestrator" who curates
intent rather than writing lines of syntax. For CIOs, this transition
represents a critical leadership inflection point where software is no longer
just a business enabler but the primary engine for scaling enterprise
intelligence. The focus is shifting from development speed to the strategic
design of decision systems. This new era necessitates the rise of roles like
the Chief AI Officer (CAIO) to govern AI as a strategic asset, ensuring
security through zero-trust principles and navigating complex regulatory
landscapes like the EU AI Act. While productivity gains are significant,
organizations must proactively manage risks such as code hallucinations, model
bias, and intellectual property concerns. Ultimately, the future of digital
economies will be shaped by leaders who prioritize "intelligence
orchestration" over traditional application building, fostering adaptive
systems that learn and evolve. Success in 2026 requires a focus on three core
mandates: architecting intelligence, governing AI assets, and aligning
technology ecosystems with overarching corporate strategy.
The article argues that software development is undergoing a fundamental
structural shift, moving from manual coding to a paradigm defined by
architecture, governance, and continuous learning. As generative AI and
agentic systems take over the heavy lifting of building code, the role of the
developer is evolving into that of an "intelligence orchestrator" who curates
intent rather than writing lines of syntax. For CIOs, this transition
represents a critical leadership inflection point where software is no longer
just a business enabler but the primary engine for scaling enterprise
intelligence. The focus is shifting from development speed to the strategic
design of decision systems. This new era necessitates the rise of roles like
the Chief AI Officer (CAIO) to govern AI as a strategic asset, ensuring
security through zero-trust principles and navigating complex regulatory
landscapes like the EU AI Act. While productivity gains are significant,
organizations must proactively manage risks such as code hallucinations, model
bias, and intellectual property concerns. Ultimately, the future of digital
economies will be shaped by leaders who prioritize "intelligence
orchestration" over traditional application building, fostering adaptive
systems that learn and evolve. Success in 2026 requires a focus on three core
mandates: architecting intelligence, governing AI assets, and aligning
technology ecosystems with overarching corporate strategy.Maximizing Impact Amid Constraints: The Role of Automation and Orchestration in Federal IT Modernization
Federal IT leaders currently face a challenging landscape where they must
fortify complex digital environments against persistent threats while
navigating significant fiscal uncertainty and budget constraints. According to
a recent report, over sixty percent of these leaders struggle with monitoring
tools across diverse hybrid environments, largely due to the persistence of
legacy, multi-vendor systems that create integration gaps and increase
operational costs. To overcome these hurdles, federal agencies must
strategically embrace automation and orchestration as foundational components
of a modern zero-trust architecture. By integrating AI-driven technologies for
routine tasks like alert analysis and anomaly detection, IT teams can
transition from a reactive posture to a proactive defense, effectively
reducing monitoring complexity through single-pane-of-glass solutions. This
methodical approach allows organizations to maximize the value of their
existing investments while freeing up personnel for mission-critical
initiatives. The success of such incremental improvements can be clearly
measured through enhanced metrics like mean time to detection (MTTD) and mean
time to resolution (MTTR). Ultimately, a disciplined, phased implementation of
these technologies ensures that federal agencies maintain operational
resilience and mission readiness. By focusing on strategic automation, IT
leaders can deliver maximum impact for every budget dollar, ensuring that
modernization efforts continue to advance despite the ongoing challenges of a
resource-constrained environment.






















/articles/agent-assisted-intelligent-observability/en/smallimage/agent-assisted-intelligent-thumbnail-1769595476571.jpg)

