Quote for the day:
“Happiness is a butterfly, which when pursued, is always beyond your grasp, but which, if you will sit down quietly, may alight upon you.” -- Nathaniel Hawthorne
Deep dive into Agentic AI stack

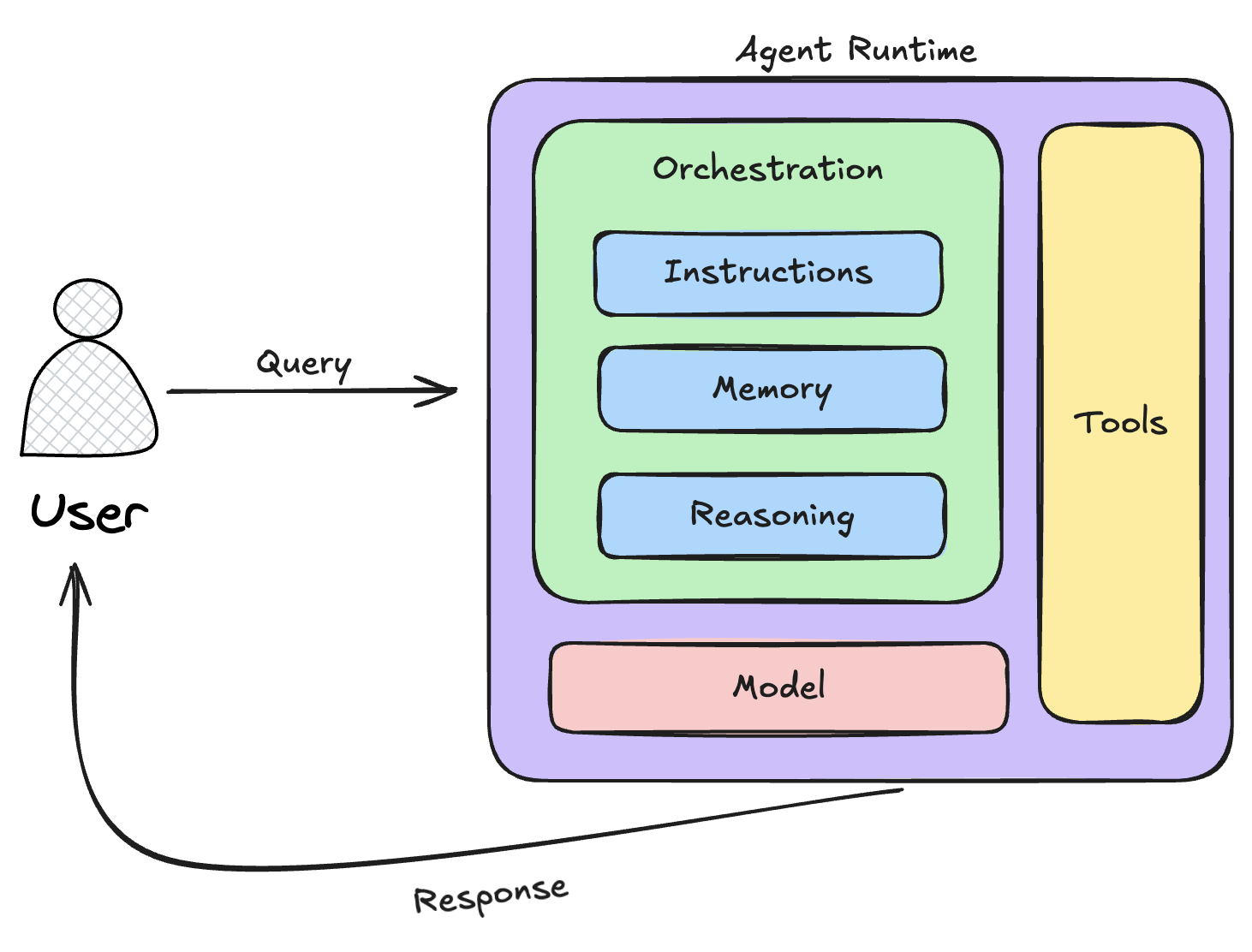
The Tool / Retrieval Layer forms the backbone of an intelligent agent’s ability
to gather, process, and apply knowledge. It enables the agent to retrieve
relevant information from diverse data sources, ensuring it has the necessary
context to make informed decisions and execute tasks effectively. By integrating
various databases, APIs, and knowledge structures, this layer acts as a bridge
between raw data and actionable intelligence, equipping the agent with a robust
understanding of its environment. ... The Action / Orchestration Layer is a
critical component in an intelligent agent’s architecture, responsible for
transforming insights and understanding into concrete, executable actions. It
serves as the bridge between perception and execution, ensuring that workflows
are effectively managed, tasks are executed efficiently, and system interactions
remain seamless. This layer must handle the complexity of decision-making,
automation, and resource coordination while maintaining adaptability to dynamic
conditions. ... The Reasoning Layer is where the agent’s cognitive processes
take place, enabling it to analyse data, understand context, draw inferences,
and make informed decisions. This layer bridges raw data retrieval and
actionable execution by leveraging advanced AI models and structured reasoning
techniques.
AI Hijacked: New Jailbreak Exploits Chain-of-Thought

Several current AI models use chain-of-thought reasoning, an AI technique that
helps large language models solve problems by breaking them down into a series
of logical steps. The process aims to improve performance and safety by enabling
the AI to verify its outputs. But "reasoning" also exposes a new attack surface,
allowing adversaries to manipulate the AI's safety mechanisms. A research team
comprising experts from Duke University, Accenture and Taiwan's National Tsing
Hua University, found a vulnerability in how the models processed and displayed
their reasoning. They developed a dataset called Malicious-Educator to test the
vulnerability, designing prompts that tricked the models into overriding their
built-in safety checks. These adversarial prompts exploited the AI's
intermediate reasoning process, which is often displayed in user interfaces. ...
The researchers acknowledged that they could be facilitating further
jailbreaking attacks by publishing the Malicious-Educator dataset but argued
that studying these vulnerabilities openly is necessary to develop stronger AI
safety measures. A key distinction in this research is its focus on cloud-based
models. AI models running in the cloud often include hidden safety filters that
block harmful input prompts and moderate output in real-time. Local models lack
these automatic safeguards unless users implement them manually.
What CISOs need from the board: Mutual respect on expectations

The CISO requires specific and sustained support from the board to effectively
protect the organization from cyber threats. A strong partnership between the
CISO and board is essential for establishing and maintaining robust
cybersecurity practices. My favourite saying one that CISO Robert Veres relayed
to me: The board should support the “Red” and challenge the “Green.” This
support is exactly what the CISO requires as a foundation. The board must help
set the overall strategic direction that aligns with the organization’s risk
appetite. This high-level guidance provides the framework within which the CISO
can develop and implement security programs. While the CISO establishes the
cyber risk culture, they need the board to reinforce this by setting the
appropriate tone from the top and ensuring cybersecurity compliance is
prioritized across all levels of management and business units. This is a
difficult task for some boards as they may lack a good understanding of business
and integration of the technology strategy. A critical requirement is for the
CISO to have a strong mandate to operate with clear accountability. They need
the authority to act and defend the enterprise without excessive interference,
allowing them to respond quickly and effectively to emerging threats.
AI-Powered Ransomware Attacks
Consolidating artificial consciousness (simulated intelligence) into
cyberattacks is, in a general sense, changing the dangerous scene, creating
difficulties for all people and organizations. Generally, digital dangers have
been, to a great extent, manual, depending on the inventiveness and flexibility
of the aggressor. The idea of these dangers has developed as artificial
brainpower has become more computerized, versatile, and practical. AI-based
assaults can dissect immense measures of information to recognize weaknesses and
send off profoundly designated phishing efforts to spread the most recent
malware with negligible human intercession. The speed and execution of
computer-based intelligence-fueled assaults imply that dangers can arise more
suddenly than at any time in recent memory. For instance, simulated intelligence
can mechanize the surveillance and observation stages and guide targets rapidly
and precisely. This fast weakness, recognizable proof permits aggressors to take
advantage of weaknesses before they are fixed, giving organizations less chance
to respond. Additionally, AI can create modified malware that constantly evolves
to evade detection using traditional security frameworks, making it more
difficult to defend against.
AI Factories: Separating Hype From Reality

While the concept is compelling, will we see this wave of AI factories that
Jensen is promising? Probably not at scale. AI hardware is not only costly to
acquire and operate, but it also doesn’t run continuously like a database
server. Once a model is trained, it may not need updates for months, leaving
this expensive infrastructure sitting idle. For that reason, Alan Howard, senior
analyst at Omdia specializing in infrastructure and data centers, believes most
AI hardware deployments will occur in multipurpose data centers. ... AI tech
advances rapidly, and keeping up with the competition is prohibitively
expensive, Palaniappan added. “When you start looking at how much each of these
GPUs cost, and it gets outdated quite pretty quickly, that becomes bottleneck,”
he said. “If you are trying to leverage a data center, you’re always looking for
the latest chip in the in the facility, so many of these data centers are losing
money because of these efforts.” ... In addition to the cost of the GPUs,
significant investment is required for networking hardware, as all the GPUs need
to communicate with each other efficiently. Tom Traugott, senior vice president
of strategy at EdgeCore Digital Infrastructure, explains that in a typical
eight-GPU Nvidia DGX system, the GPUs communicate via NVlink.
Overcoming Challenges of IT Integration in Cross-Border M&As

When companies agree to combine, things get complicated, particularly when
blending their IT and digital operations. To that end, organizations must
carefully outline how they plan to merge their IT departments to overcome
associated challenges and avoid expensive disruptions. ... IT is the cornerstone
of most multinational corporations. Determining how each merger participant will
mesh its systems with the other is significant, particularly because 47% of
M&A deals fail because of IT problems. IT due diligence is paramount. Not
only does the process help identify priorities and risks beforehand, but it also
lets the acquiring company properly evaluate the technical capabilities of the
firm it intends to purchase. ... Cross-border M&As are subject to data
privacy and compliance regulations that vary significantly across jurisdictions.
When assessing an international merger, ensure there aren't any non-compliance
risks and that the firm being acquired operates legitimately. Be aware of
complex international data and privacy laws. Address any irregularities with a
strong compliance strategy and retain expert legal counsel before signing the
deal. ... In fact, cultural mismatch is one of the top reasons why M&As
fail.
10 machine learning mistakes and how to avoid them

Addressing biases is crucial to success in the modern AI landscape, Swita says.
“Best practices include implementing continuous surveillance, alerting
mechanisms, and content filtering to help proactively identify and rectify
biased content,” he says. “Through these methodologies, organizations can
develop AI frameworks that prioritize validated content.” To resolve bias,
organizations need to embrace a dynamic approach that includes continually
refining systems to keep pace with rapidly evolving models, Swita says.
“Strategies need to be meticulously tailored for combating bias,” he says. ...
Machine learning comes with certain legal and ethical risks. Legal risks include
discrimination due to model bias, data privacy violations, security leaks, and
intellectual property violations. These and other risks can have repercussions
for developers and users of machine learning systems. Ethical risks include the
potential for harm or exploitation, misuse of data, lack of transparency, and
lack of accountability. Decisions based on machine learning algorithms can
negatively affect individuals, even if that was not the intent. Swita reiterates
the need to anchor models and output on trusted, validated, and regulated data.
“By adhering to regulations and standards governing data usage and privacy,
organizations can reduce the legal and ethical risks associated with machine
learning,” he said.
Beyond the Buzz: What 2025's Tech Trends Mean for CIOs

Stemming from the large-scale deployment of AI is the issue of governance.
Organizations need to use AI securely, responsibly and with accountability. A
DLA Piper survey showed that 96% of firms using AI find governing AI systems a
challenge. Some companies are already at the forefront of providing AI
governance solutions. For instance, IBM Watsonx provides AI life cycle
governance, risk management and regulatory compliance. Cisco AI Defense offers
AI visibility, automated vulnerability scanning and real-time protections for AI
assets. ... The rise of deepfakes and countless AI-generated misinformation
campaigns have made disinformation security a crucial, non-negotiable imperative
for enterprises. Although AI-based detection systems and blockchain-backed
verification systems are evolving, they still lag behind the sophistication of
adversarial tactics, pushing organizations toward adopting robust detection
mechanisms and resilience strategies. ... Application of ambient intelligence in
healthcare monitoring and for improving customer experience is already in the
works. For instance, in early 2024, Texas-based Houston Methodist forged a
partnership with Apella, a startup that uses ambient sensor technology and AI to
improve surgical processes in operating rooms.
AI, automation spur efforts to upskill network pros

By developing skills in networking monitoring, performance management, and cost
optimization through automation and AI-powered tools, networking pros can become
more adept at troubleshooting while offloading repetitive tasks such as
copy-pasting configurations. Over time, they can gain the skills to better
understand which behaviors and patterns to automate. According to Skillsoft’s
Stanger, networking professionals can be challenged in finding the appropriate
tasks and workflows to automate. ... “The continuous growth in cloud
technologies ensures that cloud computing skills remain in high demand. This
includes a thorough understanding of cloud infrastructure and services, which is
becoming crucial,” Randstad’s Heins says. “Particularly challenging for
companies to find are skills related to cloud service management, especially
when combined with AI competencies.” Designing the appropriate network
infrastructure, especially for cloud-first and hybrid environments, will be
critical for networking pros looking to support sophisticated cloud
environments. According to Greg Fuller, chief evangelist and vice president of
Skillsoft/Codecademy, cloud computing, in some cases, can lead to complacency in
networking as it allows more flexibility to spin up networks quickly.
The future of data security and governance: Why organizations must rethink their strategy

AI is transforming industries, but it’s also introducing new risks. Businesses
are racing to integrate AI-powered applications, often without fully
understanding the implications for data security and compliance. AI models
require vast amounts of data, much of it sensitive, and without proper
governance, they can become a significant liability. ... Regulatory bodies
worldwide are tightening their grip on data privacy and security. From GDPR and
CCPA to emerging AI regulations, the compliance landscape is becoming
increasingly complex. Businesses can no longer afford to treat compliance as an
afterthought — it must be embedded into every aspect of data management. ...
Enterprises now manage data across multiple cloud environments, SaaS
applications and third-party vendors. The result? A complex web of data assets,
many of which are unprotected and difficult to track. Security teams struggle
with: Lack of visibility into where sensitive data resides; Data access
governance challenges; Increased vulnerability to cyber threats and insider
risks ... The time to act is now. Security, AI, risk and governance leaders must
take a proactive approach to data security and governance, ensuring that their
organizations are not just reacting to threats but staying ahead of them.





/articles/prompt-engineering/en/smallimage/prompt-engineering-thumbnail-1739797104596.jpg)







_Science_Photo_Library_Alamy.jpg?width=1280&auto=webp&quality=95&format=jpg&disable=upscale)