Quote for the day:
"A tough hide with a tender heart is a goal that all leaders must have." -- Wayde Goodall
A smarter approach to training AI models

AI models are beginning to hit the limits of compute. Model size is far
outpacing Moore’s Law and the advances in AI training chips. Training runs for
large models can cost tens of millions of dollars due to the cost of chips.
This issue has been acknowledged by prominent AI engineers including Ilya
Sutskever. The costs have become so high that Anthropic has estimated that it
could cost as much to update Claude as it did to develop it in the first
place. Companies like Amazon are spending billions to erect new AI data
centers in an effort to keep up with the demands of building new frontier
models. ... With a better foundational understanding of how AI works, we can
approach AI model training and deployment in new ways that require a fraction
of the energy and compute, bringing the rigor of other sciences to AI with a
principles-first approach. ... By eschewing the inefficiencies and less
theoretically justified parts of deep learning, we create a path forward to
the next generation of truly intelligent AI, that we’ve seen surpasses the
wall deep learning has hit. We have to understand how learning works and build
models with interpretability and efficiency in mind from the ground up,
especially as high-risk applications of AI in sectors like finance and
healthcare demand more than the nondeterministic behavior we’ve become
accustomed to.
Strategic? Functional? Tactical? Which type of CISO are you?

Various factors influence what type of CISO a company may need, says Patton, a
former CISO now working as a cybersecurity executive advisor at Cisco. A
large, older company with a big, complicated tech stack will need someone with
different skills, experience, and leadership qualities than a cloud-native
startup that’s rapidly growing and changing. A heavily regulated industry such
as financial services, healthcare, or utilities needs someone steeped in how
to navigate all the compliance requirements. ... The path professionals take
to the CISO seat also influences what type or types of CISOs they tend to be,
adds Matt Stamper, CEO, CISO, and executive advisor with Executive Advisors
Group as well as a board member with the ISACA San Diego chapter. Different
career paths forge different types of executives, he says. Those who advanced
through technical roles typically retain a technology bent, while those who
came up through governance and risk functions usually gravitate toward
compliance-focused roles. ... “CISOs should and tend to lean into where
they’re gifted,” says Jenai Marinkovic, vCISO and CTO with Tiro Security and a
member of the Emerging Trends Working Group with the IT governance association
ISACA.
Becoming Ransomware Ready: Why Continuous Validation Is Your Best Defense

With the nature of IOCs being subtle and intentionally difficult to detect,
how do you know that your XDR is effectively knipping them all in the bud? You
hope that it is, but security leaders are using continuous ransomware
validation to get a lot more certainty than that. By safely emulating the full
ransomware kill chain - from initial access and privilege escalation to
encryption attempts - tools like Pentera validate whether security controls,
including EDR and XDR solutions, trigger the necessary alerts and responses.
If key IOCs like shadow copy deletion, and process injection go undetected,
then that's a crucial flag to prompt security teams to fine-tune detection
rules and response workflows. ... Here's the reality: testing your defenses
once a year leaves you exposed the other 364 days. Ransomware is constantly
evolving, and so are the Indicators of Compromise (IOCs) used in attacks. Can
you say with certainty that your EDR is detecting every IOC it should? The
last thing you need to stress about is how threats are constantly changing
into something your security tools will fail to recognize and aren't prepared
to handle. That's why continuous ransomware validation is essential. With an
automated process, you can continuously test your defenses to ensure they
stand up against the latest threats.
US intensifies scrutiny of the EU’s Digital Markets Act

The DMA introduced unprecedented restrictions and requirements for companies
designated as “gatekeepers” in the digital market. These companies must comply
with a strict set of rules designed to prevent unfair business practices and
ensure market accessibility for smaller competitors. The Act mandates various
requirements including interoperability for core platform services,
restrictions on personal data combination across services, and prohibition of
self-preferencing practices in rankings and search results. “Big tech’s
designated platforms can no longer unfairly promote their own products or
services above yours (EU-based companies) in search results or ads,” one of
the clauses of the DMA says pertaining to offering level playing. ...
Meanwhile, the European Commission — where Ribera serves as the second-highest
ranking official under President Ursula von der Leyen — maintains that these
regulations are not targeted at US companies, according to the report. The
Commission argued that the DMA is designed to ensure fair competition and
consumer choice in digital markets, regardless of companies’ national origin.
However, the predominance of US firms among those affected has intensified
transatlantic tensions over digital policy.
The Technology Blueprint for CIOs: Expectations and Concerns

"Security sits at the front and center of business innovations, especially in
sectors like banking and finance, where protecting user data and privacy is
paramount. Every sector has its own unique challenges and opportunities, making
a sector-driven approach essential," said Sachin Tayal, managing director at
Protiviti member firm for India. AI-powered fraud detection systems are now
integral, using behavior biometrics and facial recognition to detect and
mitigate threats such as UPI frauds. Decentralized finance is also gaining
traction, with blockchain-based solutions modernizing core banking functions and
facilitating secure, transparent digital transactions, the report found. ... The
industrial manufacturing sector is embracing Industry 4.0, characterized by the
convergence of AI, IoT and cloud technologies. The market is seeing a shift
toward digital twins and real-time analytics to optimize production processes.
The integration of autonomous mobile robots and collaborative robots, cobots, is
enhancing efficiency and safety on the production floor, the report said. ...
CIOs have their work cut out - innovate or risk getting redundant. "Technology
is driving businesses today, and the transformative role of the CIO amid the
rapid rise of AI and digital innovations has never been more critical. The CIO
now wears many hats - CTO, CISO and even CEO - as roles evolve to meet the
demands of a digital-first world," Gupta said.
Man vs. machine: Striking the perfect balance in threat intelligence
One of the key things you must be aware of is your unconscious biases. Because
we all have them. But being able to understand that and implement practices
that challenge your assumptions, analysis and hypotheses is key to providing
the best intelligence product. I think it’s a fascinating problem,
particularly as it’s not necessarily something a SOC analyst or a
vulnerability manager may consider, because it’s not really a part of their
job to think that way, right? Fortunately, when it comes to working with the
AI data, we can apply things like system prompts, we can be explicit in what
we want to see as the output, and we can ask it to demonstrate where and why
findings are identified, and their possible impact. Alongside that, I think
the question also demonstrates the importance on why we as humans can’t forego
things like training or maintaining skills. ... It’s also important that
security continues to be a business enabler. There are times we interact with
websites in countries that may have questionable points of view or human
rights records. Does the AI block those countries because the training data
indicates it shouldn’t support or provide access? Now some organisations will
do domain blocking to an extreme level and require processes and approvals to
access a website, it’s archaic and ridiculous in my opinion. Can AI help in
that space? Almost certainly.
AI and the Future of Software Testing: Will Human Testers Become Obsolete?
With generative AI tools, it has become possible to produce software testing
code automatically. QA engineers can simply describe what they want to test
and specify a testing framework, tool, or language, then let generative AI do
the tedious work of writing out the code. Test engineers often need to
validate and tweak the AI-generated code, just as software developers most
often rework some parts of application code produced by AI. But by writing
unit tests and other software tests automatically, AI can dramatically reduce
the time that QA engineers spend creating tests. ... AI tools can also assist
in evaluating test results. This is important because, in the past, a test
failure typically meant that a QA engineer had to sit down with developers,
figure out why the test failed, and formulate a plan for fixing whichever
flaw triggered the issue. AI can automate this process in many cases by
evaluating test results and corresponding application code and then making
recommendations about how to fix an issue. Although it's not realistic to
expect AI to be capable of entirely automating all software test assessments,
it can do much of the tedious work. ... At the same time, though, AI will
almost certainly reduce the need for human software testers, which could lead
to some job losses in this area.
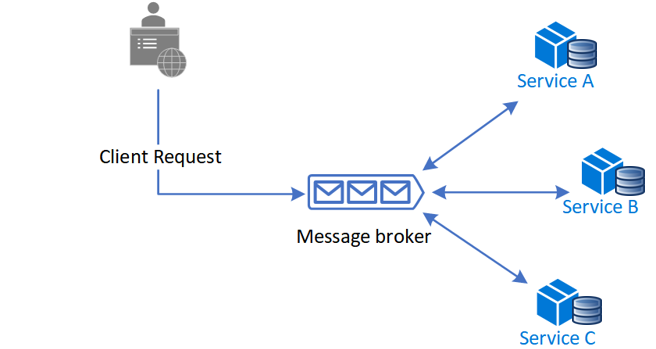
From Convenience to Vulnerability: The Dual Role of APIs in Modern Services
Recently, a non-exploited vulnerability was discovered within a popular Travel
Service that could have enabled attackers to take over victim accounts with a
single click. Such an attack is called an "API Supply Chain Attack," in which
an attacker chooses to attack a weaker link in the service's API ecosystem.
While the takeover could occur within the integrated service, it likely would
have provided attackers full access to the user's personally identifiable
information (PII) from the main account, including all mileage and rewards
data. Beyond mere data exposure, attackers could perform actions on behalf of
the user, such as creating orders or modifying account details. This critical
risk highlights the vulnerabilities in third-party integrations and the
importance of stringent security protocols to protect users from unauthorized
account access and manipulation. Vigilance, governance, and explicit control
of APIs are essential for safeguarding against security gaps and
vulnerabilities within API ecosystems. Organizations must prioritize investing
in comprehensive API tools and software that support the entire API lifecycle.
This includes identifying and cataloging all APIs in use to ensure visibility
and control, continuously assessing and improving the security posture of APIs
to mitigate risks, and implementing robust security measures to detect and
respond to potential threats targeting APIs.
Scientists Tested AI For Cognitive Decline. The Results Were a Shock.
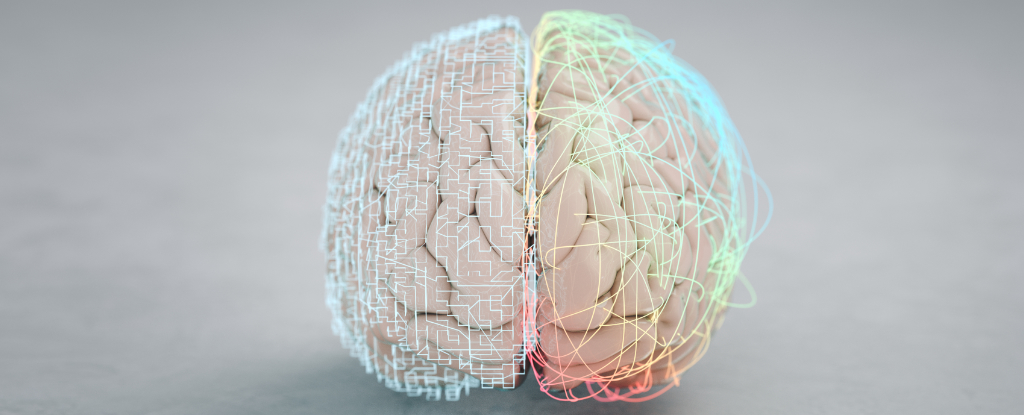
Today, the famous large language model (LLM) is just one of several leading
programs that appear convincingly human in their responses to basic queries.
That uncanny resemblance may extend further than intended, with researchers
from Israel now finding LLMs suffer a form of cognitive impairment similar to
decline in humans, one that is more severe among earlier models. The team
applied a battery of cognitive assessments to publicly available 'chatbots':
versions 4 and 4o of ChatGPT, two versions of Alphabet's Gemini, and version
3.5 of Anthropic's Claude. Were the LLMs truly intelligent, the results would
be concerning. In their published paper, neurologists Roy Dayan and Benjamin
Uliel from Hadassah Medical Center and Gal Koplewitz, a data scientist at Tel
Aviv University, describe a level of "cognitive decline that seems comparable
to neurodegenerative processes in the human brain." For all of their
personality, LLMs have more in common with the predictive text on your phone
than the principles that generate knowledge using the squishy grey matter
inside our heads. What this statistical approach to text and image generation
gains in speed and personability, it loses in gullibility, building code
according to algorithms that struggle to sort meaningful snippets of text from
fiction and nonsense.
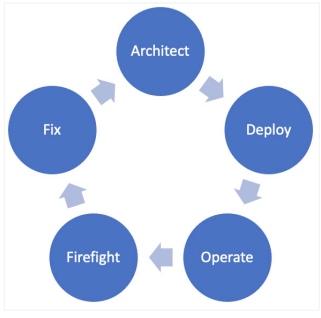
6 reasons so many IT orgs fail to exceed expectations today

“CIOs at large organizations know what they’ve got to hit. They know what they
have to do to exceed expectations. But it’s more common that CIOs at smaller
and less mature organizations have unclear objectives,” says Mark Taylor, CEO
of the Society for Information Management (SIM). ... Doing all that work
around expectation setting may still not be enough, as CIOs frequently find
that the expectations set for them and their teams can shift suddenly. “Those
moving targets happen all the time, especially when it comes to innovation,”
says Peter Kreutter, WHU Otto Beisheim School of Management’s CIO Leadership
Excellence Program faculty director and a member of the board of trustees for
CIO Stiftung. ... “Fundamental challenges, such as legacy technology
infrastructure and rigid operating cost structures, were at the core of
failure rates,” the report reads. “These frequently limited the effectiveness
of margin improvement initiatives and their impact on the bottom line.
Unfortunately, this may only get worse, with uncertainty as a constant and the
push for gen AI and data across enterprises.” ... Confusion about
accountability — that is, who is really accountable for what results — is
another obstacle for CIOs and IT teams as they aim high, according to Swartz.