5 Questions to Ask About DDoS Pricing

As DDoS attacks grow more frequent, more powerful, and more sophisticated, many organizations turn to DDoS mitigation services to protect themselves against attack. DDoS protection vendors range in all shapes and sizes, from dedicated DDoS mitigation providers to CDN vendors who add website DDoS protection, to ISPs who resell DDoS protection as an add-on. As a result, the quality and cost of such service can vary wildly, and many customers end up purchasing protection packages that are either inadequate, or too big for their needs, resulting in unnecessary costs. ... Paying for attack traffic is particularly a concern if you rely on your CDN provider, your ISP, or your public cloud host for DDoS protection, because these providers charge customers according to the amount of traffic. In such cases you will essentially be paying your provider to be attacked, which can quickly escalate to tens of thousands of dollars (or more) per attack.
Millennials could change ‘hero’ mentality in IT departments, says Gartner
“Maybe new recruits have some skills, they have some capabilities they can bring to your organisation in terms of new thinking, in terms of how they collaborate,” he said. Tiny Haynes, Gartner research director of infrastructure, said organisations can benefit from the “experience versus enthusiasm” of young recruits to create a more collaborative working environment. Entrepreneur Margaret Heffernan, also speaking at the Gartner event, said an individualistic environment in the workplace can have an adverse effect. “For decades, we used to believe the best way to manage people at work is you get the high performers and you put them all into fantastic departments and projects and you get them to compete furiously for recognition, for bonuses, for promotions,” she said. “We found that instead you create huge amounts of dysfunction, huge amounts of aggression and huge amounts of waste.”
How to ensure IT works on the right projects

The first step in improving IT’s impact on your business is to understand whether the business’s perception of IT is reality and then position your IT organization to leverage their knowledge to support the business. It’s all about developing a strong partnership with the business and empowering your IT team to do more. Once you have your team aligned, you need to paint the vision for all that IT can be. In the digital era, IT can do more than put in systems; we can develop new products and services. That’s a greater level of influence than IT has had before, and your team needs to know that. There is a journey of taking IT from a liability to an asset and then to an enabler of value capture, and finally to being a value creator itself. Your whole team needs to understand the journey and that it doesn’t happen overnight.
Why Your Board Is Critical To Digital Transformation Results

The survey which looked across four pillars of digital transformation maturity, including strategy and vision, people and culture, process and governance, and technology and capabilities, found the majority of companies were still in the early stages of their digital maturity based on a scale of early (1.0), developing (2.0) and maturing (3.0). ... One of the most surprising findings of the survey was the correlation between board-level priority for digital transformation and the achievement of transformational results. The results when digital was a top 3 board-level priority were surprisingly higher than when digital was simply a top 3 CEO-level priority ... Board-level prioritization of digital transformation is needed to create the impetus for change and to fuel investments; perennial skills such as leadership, culture and change management are needed to promote understanding and buy-in
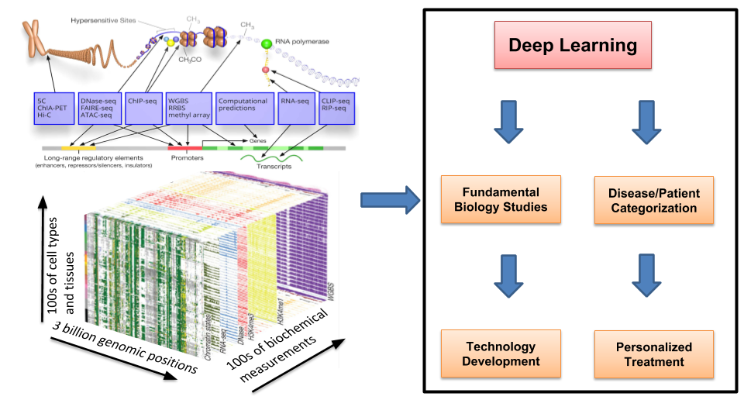
The importance of data mining
With the help of data warehouses, information is extracted from a wide range of systems, converted into an ordinary format and uploaded into the data warehouse. Extract, transform and load or ETL is the name given to this sophisticated process. When the obtained info is merged and converted, experts can work with the data. In the past, the consolidation of information was conducted within a specific time frame like – once a day, once a week, bi-weekly or monthly. One of the main reasons why intervals were used was the fact that databases had to be offline while the data was processed. As you are probably aware, the business that is open 24 hours a day, 7 days a week can’t be down simply because data must be updated. As a result of that, many businesses and organisations had old, obsolete and/or irrelevant data. Even with irregularly updated data, organisations in the 1990s were operating fine, but today it’s impossible to run a business in this way.
What is two-factor authentication (2FA)? How to enable it and why you should

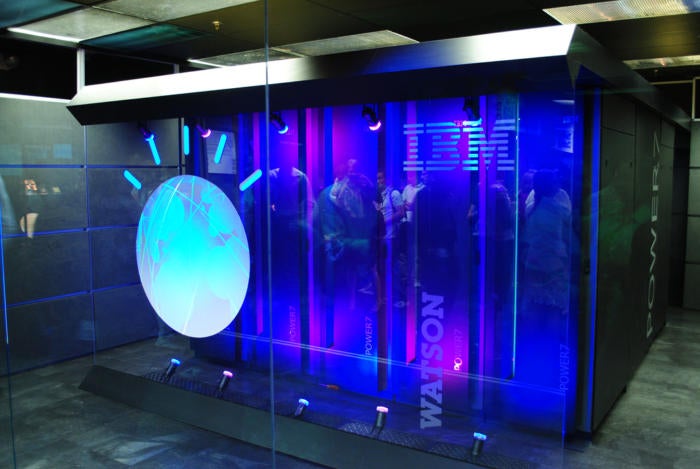
The notion of 2FA as a best security practice is no longer even remotely new. Google brought the advanced form of online security into the mainstream conscience with the launch of multilayered protection for enterprise customers in 2010 and then for all Google users in 2011. Facebook followed soon after. Yet, according to a recent report by the Pew Research Center, only 10 percent of American adults can correctly identify a two-factor-enabled login screen from a set of four choices. Another report, from Duo Labs, estimates a measly 28 percent of Americans actually use 2FA on a regular basis. More than half of those surveyed by the firm had never even heard of it. That, to put it mildly, is troubling. "People should all be looking at 2FA, even for minor things — if they're just buying toothpaste at a shopping site," says Patrick Wardrop, chief product architect of IBM's Identity and Access Management division.
Machine Learning and Big Data Know It Wasn’t You Who Just Swiped Your Credit Card
The algorithm knows right away if your card is being used at the restaurant you go to every Saturday morning — or at a gas station two time zones away at an odd time such as 3:00 a.m. It also checks if your transaction sequence is out of the ordinary. If the card is suddenly used for cash-advance services twice on the same day when the historic data show no such use, this behavior is going to up the fraud probability score. If the transaction’s fraud score is above a certain threshold, often after a quick human review, the algorithm will communicate with the point-of-sale system and ask it to reject the transaction. Online purchases go through the same process. In this type of system, heavy human interventions are becoming a thing of the past. In fact, they could actually be in the way since the reaction time will be much longer if a human being is too heavily involved in the fraud-detection cycle.
Adversarial machine learning tops McAfee’s 2018 security forecast

Serverless apps enable greater granularity, such as faster billing for services, but they are vulnerable to attacks exploiting privilege escalation and application dependencies. They are also vulnerable to attacks on data in transit across a network, and potentially to brute-force denial of service attacks, in which the serverless architecture fails to scale and incurs expensive service disruptions. “Serverless apps that are quickly implemented or rapidly deployed can use an inappropriate privilege level, leaving the environment open to a privilege escalation attack,” said Samani. “Similarly, the speed of deployment can result in a function depending on packages pulled from external repositories that are not under the organisation’s control and have not been properly evaluated.” There are also new risks, according to Samani. “By looking at the URL, we can tell if the request is going to a serverless environment.
Wi-Fi in 2018: What will the future look like?
![smart city - wireless network - internet of things edge [IoT] - edge computing](https://images.idgesg.net/images/article/2017/09/smart_city_wireless_network_iot_internet_of_things_edge_computing_thinkstock_540226428_3x2_1200x800-100736486-large.jpg)
802.11ax's key technology is something called orthogonal frequency-division multiplexing, or OFDM. This is a transmission technique that, in essence, allows multiple devices to share not only the same access point, but the same Wi-Fi channel at the same time. Previous-generation Wi-Fi can’t do that, so OFDM means that 802.11ax has a substantial leg up on current technology, particularly in terms of large numbers of devices sharing the same access point. But experts don’t think that 2018 will see widespread deployment of the new standard. For one thing, it has yet to be formally ratified by the IEEE, although that won’t stop large vendors from releasing 802.11ax gear before the standard is official. But beyond standardization issues, there’s also the simple fact that enterprise Wi-Fi is only just beginning to deploy 802.11ac wave 2
Making an effective case for increasing the data security budget
A variety of factors affect the affordability issue, but the lack of availability with the cybersecurity professional community also compounds the problem. One source, the Global Information Security Workforce Study, released in June 2017, that found the cybersecurity workforce gap is on pace to hit 1.8 million in 2022, a 20 percent increase since 2015. The lack of cybersecurity funding combined with too few trained cybersecurity analysts and engineers adds up to an IT security disaster. This assumption is shared by 56 of those surveyed who said their companies are underprepared to identify and respond to a security incident, while 45 percent believed their organization suffered a breach in the past year. Educating stakeholders of the tremendous risks that exploits and breaches pose to the health and success of the business is one of the greatest challenges CIOs and CEOs face when allocating resources to meaningful and effective security initiatives.
Quote for the day:
"It is better to fail in originality than to succeed in imitation." -- Herman Melville