At CES 2019, there are a few examples of what I'll call design mashups. These mashups are created by companies with expertise in disparate areas coming together to collaborate. These companies are going for design collaborations to better digitize their businesses. Panasonic refers to its approach to design with its brand as "comfortable disruption." The general idea is that you can take devices and technologies that are already comfortable -- and even retro -- and update them to reflect modern reality. Panasonic is taking this comfortable disruption approach with its portfolio of products. Exhibit A in this comfortable disruption concept is Procter & Gamble, which outlined how it is integrating technology into everyday products. Yes kids, AI is coming to a toothbrush near you. The catch is that the line between evolving concepts and disrupting existing products is delicate.
The 9 Cybersecurity Practices All Firms Should Follow in 2019
An entry window is also an exit window. The human being is curious by nature, and as soon as he sees something that is not his placed at his disposal, the most probable thing is that, at least out of curiosity, he makes use of that gift of becoming. This usually happens in cybercafés, in work offices and in all the places where computers are shared. If you open Facebook, Gmail or any other service, get used to closing the session before getting out of the chair to leave. With this you will avoid entering the immense rate of users who lose data by leaving their sessions open there. A good exercise to generate the habit is to do it at home too, every time you get up from the computer; close the session ... This means comfort, but also possibilities for sniffing to take shape and bank, social, mail, etc. accounts. In a blink of an eye. To avoid this, you should avoid connecting, and that’s like telling you to cut the light of your home so you never get electrocuted.
Rust programming language: Seven reasons why you should learn it in 2019
Born out of a personal project by then Mozilla developer Graydon Hoare in 2006, the language, like the Rust fungus it is named after, is starting to spread, and today is used to build software for the web, embedded computers, distributed services, and the command line. "The biggest strength of Rust is that it's an empowering technology," says Carol Nichols, from the Rust programming language core team and co-author of The Rust Programming Language book. "To write extremely fast code with a low memory footprint previously meant using C or C++. However, using those languages in production code requires you to manage memory manually and know all the ways you might cause undefined behavior." Nichols points out that the ever-expanding CVE database of code vulnerabilities is evidence that "even the best programmers" can struggle with this level of freedom.
Feds Urge Private Sector 'Shields Up' Against Hackers
"Make no mistake, American companies are squarely in the cross-hairs of well-financed nation-state actors, who are routinely breaching private sector networks, stealing proprietary data and compromising supply chains," Evanina says. "The attacks are persistent, aggressive, and cost our nation jobs, economic advantage, and hundreds of billions of dollars." Last year, Director of National Intelligence Dan Coats told Congress that in the online realm, Russia poses the top online attack threat to United States, while China, North Korea and Iran are also top threats, "although many countries and some non-state actors are exploring ways to use influence operations, both domestically and abroad." Indeed, the former head of the U.K.'s signals intelligence agency, GCHQ, last year warned that it was becoming increasingly difficult to tell cybercriminals and nation-state actors apart
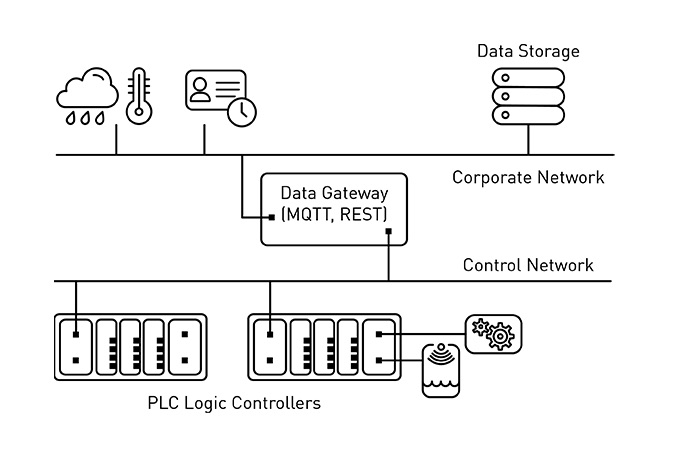
How AI and automation will impact cybersecurity strategies
My real first experience with data security came in 2000 when my personal information was exposed on a website where a disgruntled employee was able to steal an HR spreadsheet that had hundreds of people’s names, DOB, SS#, addresses and how much they earned. Even though we have moved PII to a “more secure” storage method, those storage solutions and access to them are still insecure. And this has been largely proven in the massive breaches of 2018. We need to become better stewards of data that impacts people. I read an article introducing an InfoSec Color Wheel, and they discuss involving and integrating red teams with DevOps. I think that is a great idea to move quicker towards a more secure application development process that will ultimately impact the safety of our data. I had one potential customer tell me, “thank you for not saying that this product uses AI.” I found that to be interesting. More and more applications in several different verticals are gravitating towards AI.
Never mind killer robots—here are six real AI dangers to watch out for in 2019

Carmakers like Ford and General Motors, newcomers like Uber, and a horde of startups are hurrying to commercialize a technology that, despite its immaturity, has already seen billions of dollars in investment. Waymo, a subsidiary of Alphabet, has made the most progress; it rolled out the first fully autonomous taxi service in Arizona last year. But even Waymo’s technology is limited, and autonomous cars cannot drive everywhere in all conditions. ... Last year, an AI peace movement took shape when Google employees learned that their employer was supplying technology to the US Air Force for classifying drone imagery. The workers feared this could be a fateful step towards supplying technology for automating deadly drone strikes. In response, the company abandoned Project Maven, as it was called, and created an AI code of ethics. Academics and industry heavyweights have backed a campaign to ban the use of autonomous weapons.
ODFMA should alleviate much of the unpredictability users experience in highly congested areas. Consider a case where a person arrives several hours early to an airport gate and is one of only a few people in a small area. The user connects, watches something on Netflix, and sends out Tweets to their followers. Over time, the gate area gets crowded and the network becomes unusable. The most likely cause of this isn’t bandwidth, but congestion from too many users. ODFMA will take care of this problem by enabling more clients to connect to a single AP simultaneously. Technically what’s happening is that the channels are dividing up into subcarriers through some fancy mathematical functions. The spacing of these subcarriers is orthogonal (hence the O in ODFMA) preventing interference with subcarriers. With Wi-Fi 5, a 20 MHz channel consists of 64 312.5 kHz subcarriers with all of them being used to transmit data to a single client. Wi-Fi 6 operates differently and lets the space shrink from 312.5 kHz to 78.125 kHz, allowing for the number of subcarriers to increase to 256.
How to automate machine learning on SQL Server 2019 big data clusters
H2O provides popular open source software for data science and machine learning on big data, including Apache SparkTM integration. It provides two open source python AutoML classes: h2o.automl.H2OAutoML and pysparkling.ml.H2OAutoML. Both APIs use the same underlying algorithm implementations, however, the latter follows the conventions of Apache Spark’s MLlib library and allows you to build machine learning pipelines that include MLlib transformers. We will focus on the latter API in this post. H2OAutoML supports classification and regression. The ML models built and tuned by H2OAutoML include Random Forests, Gradient Boosting Machines, Deep Neural Nets, Generalized Linear Models, and Stacked Ensembles.H2OAutoML can automatically split training data into training, validation, and leaderboard frames. The h2o.automl.H2OAutoML API also allows these frames to be specified manually, which is useful when the task is to predict the future using a model trained on historical data.
Encryption: Avoiding the Pitfalls That Can Lead to Breaches

In its revised findings about a mega-breach that it now says affected 327 million customers, Marriott notes that 25.6 million passport numbers were exposed in the breach, of which 5.25 million were unencrypted. "There is no evidence that the unauthorized third party accessed the master encryption key needed to decrypt the encrypted passport numbers," Marriott says. But that doesn't mean that the attackers couldn't later brute-force decrypt the numbers. Also exposed in the breach were approximately 8.6 million encrypted payment cards that were being stored by Marriott. By the time the breach was discovered in late 2018, however, Marriott says most of the payment cards had already expired. As with the passport data, "there is no evidence that the unauthorized third party accessed either of the components needed to decrypt the encrypted payment card numbers," Marriott says. U.S. Sen. Mark Warner, D-Virginia, says the breach highlights a failure by many organizations to minimize the amount of data they routinely store on consumers.
How Chrome extensions are making organisations vulnerable to attack

Application developers can create Chrome extensions to provide a richer experience for their users. Chrome extensions can perform a variety of tasks, from showing the Alexa ranking of websites to blocking ads to processing cryptocurrency payments on-site, and much more. However, to perform these tasks, extensions require permission to access various data, such as the content of visited pages, bookmarks, browser history, clipboards, list of installed apps and even a user’s geographical location. Some extensions might request access to a microphone or webcam, and others might require permission to modify web page content. Chrome extensions are complex applications in their own right. And complex apps can easily hide malicious behaviour. Chrome has a Web Store where developers can publish extensions and users can install them on their browsers. This is the equivalent of Google’s App Store for Android devices. And while Google does its best to keep its marketplace free of malware, cybercriminals are finding new ways to publish and distribute their malicious Chrome extensions and conduct man-in-the-browser attacks.
Quote for the day:
"Your first and foremost job as a leader is to take charge of your own energy and then help to orchestrate the energy of those around you." -- Peter F. Drucker