Heated Seats? Advanced Telematics? Software-Defined Cars Drive Risk

The main issue is that this next generation of cars has fewer platforms and SKUs but more advanced telematics and software interfaces. This results in less retooling of assembly lines at factories, but a bigger code base also means more exploitable vulnerabilities. And with the over-the-air (OTA) capabilities that these cars offer, those attacks could potentially be carried out remotely. ... "In some ways, software-defined vehicles increase the opportunity for you to make a mistake," says Liz James, a senior security consultant at NCC Group, a cybersecurity consultancy that does assessments of vehicle cybersecurity. "The more complex your software stack gets, the more likely you are to have implementation bugs, and now you also have software installed that might never be run, which runs counter to traditional embedded system advice." It's not just traditional vulnerabilities at issue. With the move to SDVs, cars increasingly resemble cloud infrastructure with virtual machines, hypervisors, and application programming interfaces (APIs), and with the increased complexity comes greater risk of failure, says John Sheehy
Cloud Native Companies Are Overspending on CVE Management

One major factor is software consumers are voracious, demanding new features built rapidly. This means software engineers with tight timelines are begrudgingly accepting the cloud native default — containers with CVEs. If the functionality works, scanning for CVEs (much less fixing them) is an afterthought. Another key factor is the software application developers who usually select a container image — often through making a few edits to a Dockerfile — are often not the ones bearing the downstream costs of vulnerability management. Finally, creating software that is easy to update is difficult. While it’s at the core of the DevOps philosophy, it’s hard to do in practice. Changing a piece of software, even to fix a CVE, often risks product downtime and frustrated customers. Consequently, many software organizations find it painful to make even minor changes to their software. ... For the particularly unfortunate, the debt comes due all at once as a consequence of hackers exploiting a CVE to access a system. That cost may be millions of dollars in reputational loss, lawsuits and ransomware.
CISO Role Shifts from Fear to Growth

“The results underscore the importance of strategic collaboration between CISOs
and CIOs, highlighting the need for a unified approach to cybersecurity that
aligns with broader business objectives,” says Frank Dickson, Group Vice
President of Security and Trust at IDC. “Check Point's commitment to pioneering
cybersecurity solutions supports this evolution, enabling organisations to
navigate these challenges successfully.” ... As organisations are looking to
modernise IT infrastructures as a foundation for digital transformation, Check
Point and IDC found there is a need for security strategies that support, rather
than hinder, progress. Despite such fast-paced growth, a trust gap remains in
the cybersecurity landscape, with a majority of businesses and customers
expressing concerns about technology being used unethically. With this in mind,
Check Point and IDC cite in their survey a transformation towards security as a
business enabler - shifting away from fear-based security postures towards
growth-oriented strategies. This evolution is supported by Check Point's
emphasis on simplifying and consolidating security solutions to address cost and
management inefficiencies effectively.
How AI has already changed coding forever

Seven says he sees both bottom-up approaches (a developer or team has success
and spreads the word) and top-down approaches (executive mandate) to adoption.
What he’s not seeing is any sort of slowdown to generative AI innovation. Today
we use things like CodeWhisperer almost as tools—like a calculator, he suggests.
But a few years from now, he continues, we’ll see more of “a partnership between
a software engineering team and the AI that is integrated at all parts of the
software development life cycle.” In this near future, “Humans start to shift
into more of a [director’s] role…, providing the ideas and the direction to go
do things and the oversight to make sure that what’s coming back to us is what
we expected or what we wanted.” As exciting as that future promises to be for
developers, the present is pretty darn good, too. Developers of any level of
experience can benefit from tools like Amazon CodeWhisperer. How developers use
them will vary based on their level of experience, but whether they should use
them is a settled question, and the answer is yes.
How can you ensure your Zero Trust Network Access rollout is a success?

As with any large project, buy-in from the board is essential for a successful
ZTNA rollout. Getting senior leadership on side from the outset will make it far
easier to secure the budget and resources required and enable the project to
proceed smoothly. To achieve this, it's best to focus on the value in terms of
outcomes for the business including security benefits and other advantages, such
as regulatory compliance. Consider starting with a small pilot project first
when it’s time to start implementation. Small but high-risk groups such as
contractors and seasonal workers are a good starting point. A successful rollout
here will showcase the benefits of Zero Trust to secure further leadership
support and highlight any issues to work out ahead of larger implementations.
It's also worth noting that, while it can be highly modular, ZTNA is still a
complex endeavour that takes time and expertise. Bringing in project managers
and consultants can help provide more specialist experience alongside your
in-house IT and security personnel.
A Call to Action via Modular Collaboration

The transition towards Modular Open Systems Approaches (MOSA) necessitates a
collaborative ecosystem where government entities, industry partners, and
academic institutions converge. Consortia embody this spirit of cooperation by
pooling resources, knowledge, and expertise to drive shared innovation and
standardization. This collective approach not only accelerates the development
of interoperable and modular technologies but also fosters a culture of
continuous improvement, critical for adapting to the ever-evolving landscape of
defense technology. Modular contracting offers a practical framework for
implementing the principles of action and collaboration. By decomposing large
projects into smaller efforts, just as we decompose complex systems to
manageable components, we achieve an approach that is modular and allows for
greater flexibility, risk mitigation, and the inclusion of innovative solutions
from a broader range of contributors. Modular contracting supports agile
acquisition processes, facilitating rapid iteration, and deployment of new
technologies, thereby enhancing the defense sector’s capability to respond to
emerging threats and opportunities.
Akamai, Neural Magic team to bolster AI at the network edge

The combination of technologies could solve a dilemma that AI poses: whether
it’s worth it to put computationally intensive AI at the edge—in this case,
Akamai’s own network of edge devices. Generally, network experts feel that it
doesn’t make sense to invest in substantial infrastructure at the edge if it’s
only going to be used part of the time. Delivering AI models efficiently at the
edge also “is a bigger challenge than most people realize,” said John O’Hara,
senior vice president of engineering and COO at Neural Magic, in a press
statement. “Specialized or expensive hardware and associated power and delivery
requirements are not always available or feasible, leaving organizations to
effectively miss out on leveraging the benefits of running AI inference at the
edge.” ... “As we observe attacks shifting over time from not only exploiting
very specific vulnerabilities but increasingly including more nuanced
application-level abuse, having AI-aided anomaly detection capabilities can be
helpful,” he said. “If partnerships such as this one open the door for increased
use of deep learning and generative AI by more developers, I view this as
positive.”
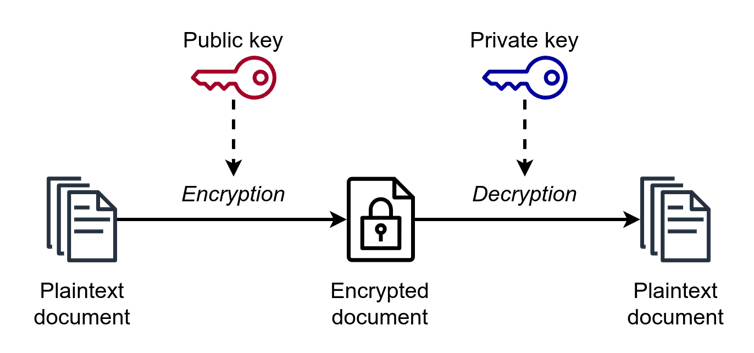
Foundations of Data in the Cloud
With the structure of data management in the cloud laid out, it's time to talk
about security. After all, what good is a skyscraper if it's not safe? Data
security in the cloud is a multifaceted challenge that involves protecting data
at rest, in transit, and during processing. Encryption is the steel-reinforced
door of our data house. It ensures that even if someone gets past the perimeter
defenses, they can't make sense of the data without the right key. Cloud
providers offer various encryption options, from server-side encryption for data
at rest to SSL/TLS for data in transit. In this article, we spoke about
encryption options for your data at rest. But security doesn't stop at
encryption. It also involves identity and access management (IAM), ensuring that
only authorized personnel can access certain data or applications. Think of IAM
as the security guard at the entrance, checking IDs before letting anyone in.
Moreover, regular security audits and compliance checks are like routine
maintenance checks for a building. As we continue to build and innovate in the
cloud, these practices must evolve to counter new threats and meet changing
regulations.
A call for digital-privacy regulation 'with teeth' at the federal level
The US government and Americans in general are letting big tech companies get
away with infringing the online privacy of millions of citizens who use "free"
services in the form of apps and websites. Big tech's goal is to connect
advertisers with an ideal customer, who, because of some online interaction, is
perceived as being more likely to buy products like the ones the advertiser is
selling. These tech companies collect information including search data,
purchase history, payment information, facial recognition data, documents,
photos, videos, locations, Wi-Fi location, IP address, birth date, mailing
address, email address, phone number, activities or interactions such as videos
watched, app use, emails sent and received, activity on your device, phone calls
— and a lot more. ... It should come as no surprise that the companies tracking
users employ cryptic legal language to explain what they do with your data. And
whatever privacy controls users might have been provided tend to be incomplete,
spread out, difficult to find, ambiguous, or needlessly complex. Plus, both the
legalese and privacy settings can change without notice.
Demonstrating the Value of Data Governance

According to Hook, quantifying cost savings “is the easiest and most effective
way to show value.” He advises turning intangible wins into tangible ones. For
example, a data scientist spends less time cleaning data due to better Data
Quality serviced by the Data Governance program and adds a testimonial. A DG
manager can interview the data scientist to determine the time saved and use
Glassdoor PayScale, a popular platform to research salary costs freed up for
that person to do more impactful work. Although this approach does not include
revenue generated by Data Governance, “it remains the most popular way to get
the hard dollars,” Hook observed. ... The second-most impactful way to show the
value of Governance calls attention to tangible wins. Examples include product
optimization, speed to market, effective decision-making, or revenue-generating
opportunities. Hook noted that people generally do not expect to realize
profitable value from DG services. However, these results indicate that the DG
program has value and can be sustained as a pro. On the con side, sticking with
only tangible wins limits evidence to the past or present and does not provide
information on future capabilities.
Quote for the day:
“There is only one thing that makes a
dream impossible to achieve: the fear of failure.” --
Paulo Coelho



/filters:no_upscale()/articles/technical-decision-buy-in/en/resources/15Picture1-1710153443158.jpg)








:format(webp)/cdn.vox-cdn.com/uploads/chorus_asset/file/13292777/acastro_181017_1777_brain_ai_0001.jpg)


















/dq/media/post_banners/wp-content/uploads/2023/08/cyber-4610993-1280.jpg)

:format(webp)/cdn.vox-cdn.com/uploads/chorus_asset/file/24347780/STK095_Microsoft_04.jpg)