How AI can help find new employees

AI-based recruitment platforms can find "more diverse talent pools, and [offer]
a more accurate approach to qualifying candidates by matching skills rather than
on a job title match or other signal,” said Forrester Principal Analyst Betsy
Summers. Some of the use cases for talent acquisition platforms are
efficiency-oriented, since they’re used for interview scheduling, managing the
candidate application process, assisting recruiters with follow-ups, and
managing the applicant pipeline. Other platforms also focus on bias mitigation
such as adjusting language in job descriptions and candidate communications to
be more inclusive. Still others include remote video capabilities that automate
early interviews. ... Chatbots are typically employed by recruitment platforms
to engage job seekers and ask them about their interests and skills; the bots
can then present candidates with open positions for which they’re most qualified
to apply.
The EU digital strategy: The impact of data privacy on global business
First, companies may need to assess the impact of the EU digital strategy on
their business and their business model and need to identify where changes are
required and where additional care needs to be taken with respect to current
processes. This specifically applies to the four acts concerning data
governance, digital services, AI, and data. Second, companies may need to
investigate the possibilities for the applicability of the acts within their
organization. This includes possible access to markets that other competitors
led in the past through their access to end-user data. Finally, as the EU
digital strategy continues to evolve, organizations may be able to further
collaborate with governing bodies on the interpretation of the regulations.
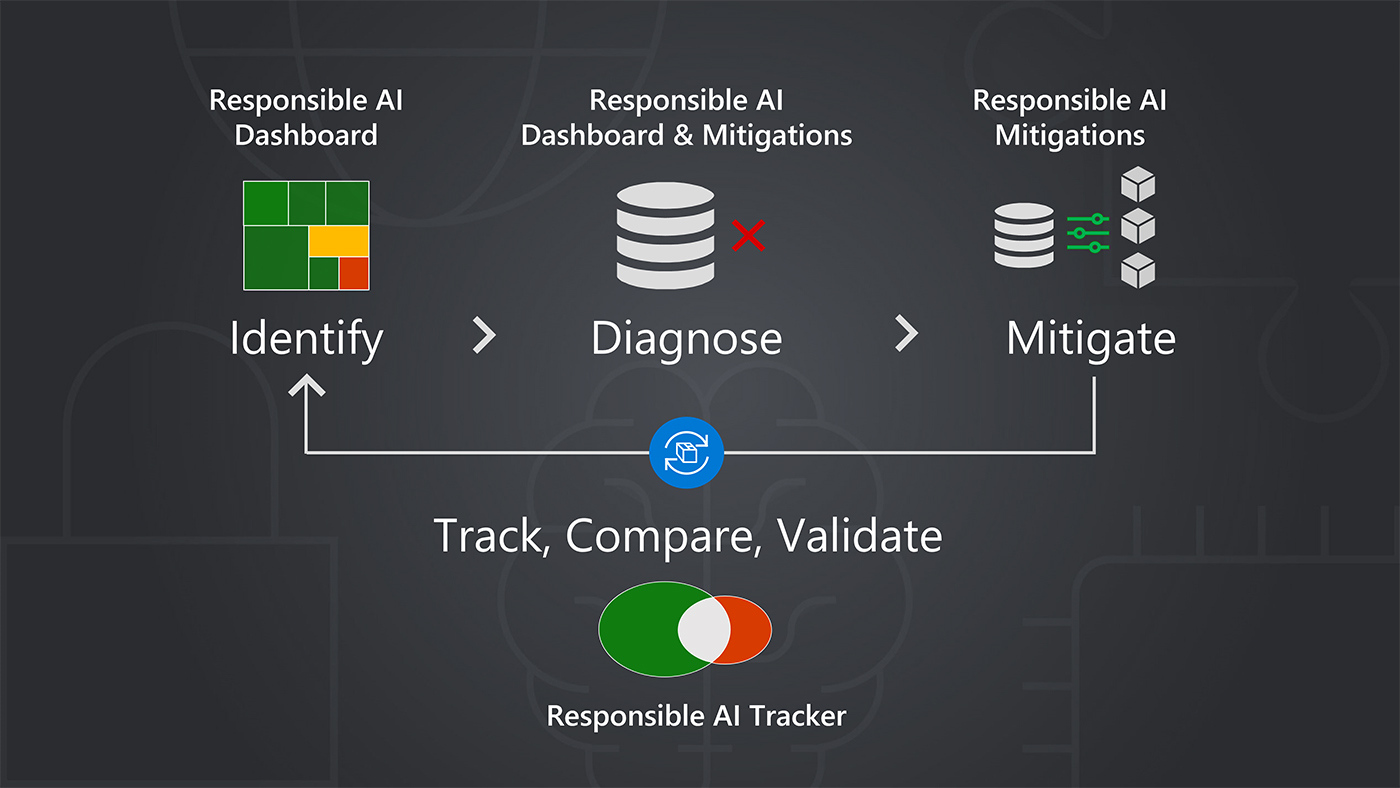
Specifically, in the case of AI, there are several companies that may find it
very challenging to work with their current model in the new guidance.
... Additionally, companies should revisit their current processes for data
collection and AI.
5 best practices for scaling AI in the enterprise

One of the most important challenges of implementing AI is defining the business
problem the enterprise is trying to solve. As the saying goes, don’t end up with
an answer that’s looking for a question. Simply deploying new forms of
technology isn’t the right approach. Next, examine the issues and determine if
AI is the best way to tackle the problem. There are other digital technologies
well adapted to simple problems. To help ensure success, define the business
issue clearly and determine what course to take at the outset — some may not
need AI. In automation, the end-to-end process is disaggregated and divided into
smaller parts. Each part is then digitized, and the parts are then reaggregated
into the value chain. ... So, AI-based transformation is as much about designing
a new operating model, cross-skilling the workforce and integrating it into
upstream and downstream processes as it is about neural nets and model
management. It’s important to note that AI in the enterprise is 20% about
technology and 80% about people, processes and data.
Data Privacy: A Public Policy Challenge
In today’s world, improved computational capabilities have enabled businesses
and public and private organizations to better structure their data in the form
of huge databases and leverage analytics to generate business intelligence and
contribute value creation. With these computational and analytical capabilities,
there are increasing avenues to develop profiles of humans’ behavior around
their purchasing, spending and consumption habits, their genetic profiling,
their travel history, medical history, etc. While these capabilities add value
to the human society, they also come with risks of intruding into individuals’
privacy. Unfortunately, the discourse around personal data is only centered
around its protection from leakage or prevention from breach. However, the
primary objective to safeguard the personal data is to ensure that such data are
not processed to create a more inequitable society and bring about unfair
outcomes. The amount of discrete data available today allows us to bring more
nuance and innovations into public policy, therefore aiding in ironing out any
imbalances within the society.
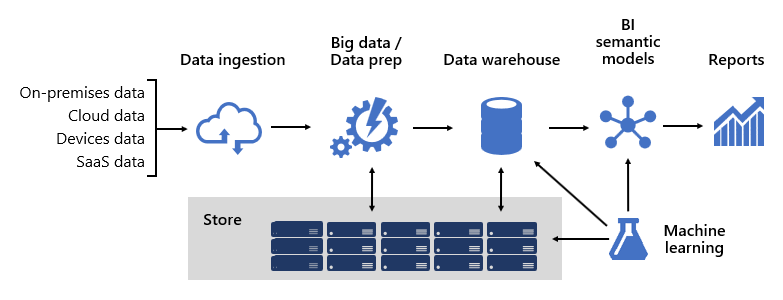
Why Database Administrators Are Rising in Prominence

“Currently, there’s a very disjointed relationship between DBAs and the business
problem they are solving for customers,” Neiweem says. He points out DBAs are
often the last touch point for customers, but this is changing as business and
marketing leaders glean deeper insights from customer data and look to achieve
personalization at scale. “It’s no longer effective to go through this
disconnected channel to get answers about customer data,” he says. “DBAs are now
moving into a consulting role where they can take data, analyze and action it,
enabling marketing and other internal teams to build stronger relationships with
customers through those data insights.” Arun Chandrasekaran, product manager for
ManageEngine, adds DBAs are often the first link in the chain of acquiring IT
tools. “While the decision-makers decide on what to buy, DBAs can influence
their decision,” he says. “Since the responsibility of managing the data
warehouse falls on DBAs, they work with the stakeholders to understand the
business requirements.
Designing For Data Flow
Put simply, the bottlenecks in designs are being defined by the type and volume
of data, and the speed at which it needs to be processed. “SoCs are getting
bigger and more complex, fitting everything in the actual chip,” he said. “So
data exchange, which used to happen at a system level, is now happening within
the IC. This means efficient circuit design for data transfer is required to
achieve the overall expected performance. The data flow design at the logic
level is quite abstract. In the past, the chips were smaller and mostly driven
by specific functionality, so there were only a few stages required to plan for
data flow. With bigger chips, this has changed, and more effort is needed to
understand the data sampling and placement of the appropriate functional modules
next to each other, to achieve optimal data flow.” Data integrity also is
becoming a challenge. In addition to crosstalk and various types of noise, which
are prevalent at advanced nodes, there are a variety of aging effects that can
appear over longer lifetimes, thermal mismatch between increasingly
heterogeneous components, and latent defects that can become real defects as the
amount of processing required on a chip or in a package increases.
Interacting with Machines through IoT and AI: A Revolution in Home and Workplace Technology

The seamless integration of IoT and AI has completely revolutionized the way we
interact with machines, offering novel and innovative solutions for both homes
and workplaces alike. With the aid of cutting-edge technologies like machine
learning, deep learning algorithms, gesture control, and wearable devices, the
potential of IoT and AI to create value across a range of applications is
colossal. As these technologies continue to advance, the potential for further
groundbreaking advancements in the future is undeniable. It is my sincere hope
that this blog has been informative and engaging, offering you valuable insight
into the current and future state of these two fields. That said, it is also
important to remain cognizant of the potential ethical and privacy concerns that
come with their widespread adoption. As with any rapidly-evolving technology, it
is essential that we consider and address these concerns to ensure that the
development and application of these technologies align with our societal values
and principles.
How Skyscanner Embedded a Team Metrics Culture for Continuous Improvement
Changing Culture was probably the part that we put the most effort into, because
we recognised that any mis-steps could be misinterpreted as us peering over
folks’ shoulders, or even worse, using these metrics intended to signal
improvement opportunities to measure individual performance. Either of those
would be strongly against the way that we work in Skyscanner, and would have
stopped the project in its tracks, maybe even causing irreversible damage to the
project’s reputation. To that end we created a plan that focused on developing a
deep understanding of the intent with our engineering managers before
introducing the tool. This plan focused on a bottom-up rollout approach, based
on small cohorts of squad leads. Each cohort was designed to be around 6 or 7
leads, with a mix of people from different tribes, different offices, and
different levels of experiences, covering all our squads. The smaller groups
would increase accountability, because it’s harder to disengage in a small
group, and also create a safe place where people can share their ideas,
learnings, and concerns.
Managing data is the key to better citizen services

As important as cyber-resilience is, there are also other issues associated
with the unchecked growth of a data estate. Top of mind for public sector CIOs
is keeping an eye of the purse-strings and being accountable to taxpayers for
the money they spend. Massive amounts of data cost a similarly large amount of
funding to maintain, says Mr Hatchuel. “You have to put data somewhere and
managing the cost is very challenging for CIOs.” A modern data protection and
management solution allows CIOs to manage their data estates in a
cost-effective way, as well as keep it secure. The solution should also
protect and manage external data sources which, in a contemporary environment,
could be a new public cloud service. “Data can pop up anywhere, so you need a
holistic solution able to look across the whole data estate and manage and
understand different data sources. CIO’s are also advised to understand the
Shared Responsibility model of most public cloud services; for the majority of
providers, that burden falls to the customer.”
4 ways for CIOs to strike a balance between operation and innovation
“Striking the right balance between innovation and operations is essential for
any organization to succeed and stay competitive. Innovation is about
exploring new ideas, embracing change, and striving for progress. On the other
hand, operations consist of taking those ideas and making them a reality,
efficiently utilizing resources, and ensuring that all the necessary steps are
in place to deliver the desired result. ... “The load that IT organizations
carry with snowballing technical debt has a direct and tangible drain on IT
innovation. While it’s obvious on the surface, every dollar spent on technical
debt is a dollar that IT cannot invest in innovation and transformation.
Maintaining, securing, and operating critical but aging applications and
infrastructure is a boat anchor that drags down innovation and must be
addressed continuously by IT leadership, architects, and CTOs before it blows
up in a disaster. Start by eliminating the 'kick the can down the road'
strategy of ignoring technical debt; instead, prioritize actual application
modernization investments that can break the pattern and open up innovation
cycles as part of a continuous modernization strategy.”
Quote for the day:
"Great leaders go forward without
stopping, remain firm without tiring and remain enthusiastic while growing"
-- Reed Markham