Quote for the day:
"Your life does not get better by chance, it gets better by change." -- Jim Rohn
Two AI developer strategies: Hire engineers or let AI do the work

Philip Walsh, director analyst in Gartner’s software engineering practice,
said that from his vantage point he sees “two contrasting signals: some
leaders, like Marc Benioff at Salesforce, suggest they may not need as many
engineers due to AI’s impact, while others — Alibaba being a prime example —
are actively scaling their technical teams and specifically hiring for
AI-oriented roles.” In practice, he said, Gartner believes AI is far more
likely to expand the need for software engineering talent. “AI adoption in
software development is early and uneven,” he said, “and most large
enterprises are still early in deploying AI for software development —
especially beyond pilots or small-scale trials.” Walsh noted that, while
there is a lot of interest in AI-based coding assistants (Gartner sees roughly
80% of large enterprises piloting or deploying them), actual active usage
among developers is often much lower. “Many organizations report usage rates
of 30% or less among those who have access to these tools,” he said, adding
that the most common tools are not yet generating sufficient productivity
gains to generate cost savings or headcount reductions. He said, “current
solutions often require strong human supervision to avoid errors or endless
loops. Even as these technologies mature over the next two to three years,
human expertise will remain critical.”
The Great AI shift: The rise of ‘services as software’
Today, AI is pushing the envelope by turning services built to be used by humans
as ‘self-serve’ utilities into automatically-running software solutions that
execute autonomously—a paradigm shift the venture capital world, in particular,
has termed ‘Services as Software’ ... The shift is already conspicuous across
industries. AI tools like Harvey AI are transforming the legal and compliance
sector by analysing case law and generating legal briefs, essentially replacing
human research assistants. The customer support ecosystem that once required
large human teams in call centres now handles significant query volumes daily
with AI chatbots and virtual agents. ... The AI-driven shift brings into
question the traditional notion of availing an ‘expert service’. Software
development,legal, and financial services are all coveted industries where
workers are considered ‘experts’ delivering specialised services. The human role
will undergo tremendous redefinition and will require calibrated re-skilling.
... Businesses won't simply replace SaaS with AI-powered tools; they will build
the company's processes and systems around these new systems. Instead of hiring
marketing agencies, companies will use AI to generate dynamic marketing and
advertising campaigns. Businesses will rely on AI-driven quality assurance and
control instead of outsourcing software testing, Quality Assurance, and Quality
Control.
Resilience, Observability and Unintended Consequences of Automation
Instead of thinking of replacing work that humans might make or do, it's
augmenting that work. And how do we make it easier for us to do these kinds of
jobs? And that might be writing code, that might be deploying it, that might be
tackling incidents when they come up, but understanding what the fancy, nerdy
academic jargon for this is joint cognitive systems. But thinking instead of
replacement or our functional allocation, another good nerdy academic term,
we'll give you this piece, we'll give the humans those pieces. How do we have a
joint system where that automation is really supporting the work of the humans
in this complex system? And in particular, how do you allow them to troubleshoot
that, to introspect that, to actually understand and to have even maybe the very
nerdy versions of this research lay out possible ways of thinking about what can
these computers do to help us? ... We could go monolith to microservices, we
could go pick your digital transformation. How long did that take you? And how
much care did you put into that? Maybe some of it was too long or too
bureaucratic or what have you, but I would argue that we tend to YOLO internal
developer technology way faster and way looser than we do with the things that
actually make us money as that is the perception, the things that actually make
us money.
The Modern CDN Means Complex Decisions for Developers

“Developers should not have to be experts on how to scale an application; that
should just be automatic. But equally, they should not have to be experts on
where to serve an application to stay compliant with all these different
patchworks of requirements; that should be more or less automatic,” Engates
argues. “You should be able to flip a few switches and say ‘I need to be XYZ
compliant in these countries,’ and the policy should then flow across that
network and orchestrate where traffic is encrypted and where it’s served and
where it’s delivered and what constraints are around it.” ... Along with the
physical constraint of the speed of light and the rise of data protection and
compliance regimes, Alexander also highlights the challenge of costs as
something developers want modern CDNs to help them with. “Egress fees between
clouds are one of the artificial barriers put in place,” he claims. That can
be 10%, 20% or even 30% of overall cloud spend. “People can’t build the
application that they want, they can’t optimize, because of some of these
taxes that are added on moving data around.” Update patterns aren’t always
straightforward either. Take a wiki like Fandom, where Fastly founder and CTO
Artur Bergman was previously CTO.
A Comprehensive Look at OSINT
Cybersecurity professionals within corporations rely on public data to
identify emerging phishing campaigns, data breaches, or malicious activity
targeting their brand. Investigative journalists and academic researchers turn
to OSINT for fact-checking, identifying new leads, and gathering reliable
support for their reporting or studies. ... Avoiding OSINT or downplaying its
value can leave organizations unaware of threats and opportunities that are
readily discoverable to others. By failing to gather open-source data,
businesses and government agencies could remain in the dark about malicious
activities, negative brand impersonations, or stolen credentials circulating
on forums and dark web marketplaces. In the event of a security breach or
public scandal, stakeholders may view the lack of proper OSINT measures as a
failure of due diligence, eroding trust and tarnishing the organization’s
image. ... The primary driver behind OSINT’s growth is the vast reservoir of
information generated daily by digital platforms, databases, and news outlets.
This public data can be invaluable for enhancing security, improving
transparency, and making more informed decisions. Security professionals, for
instance, can preemptively identify threats and vulnerabilities posted openly
by malicious actors.
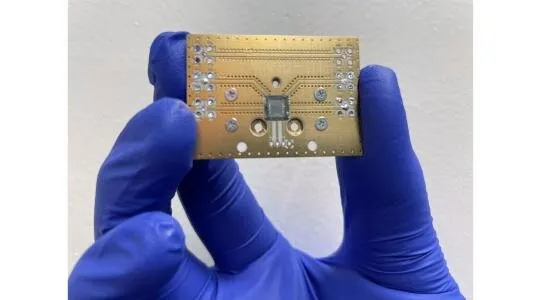
OT/ICS cyber threats escalate as geopolitical conflicts intensify

A persistent lack of visibility into OT environments continues to obscure the
full scale of these attacks. These insights come from Dragos’ 2025 OT/ICS
Cybersecurity Report, its eighth annual Year in Review, which analyzes
industrial organizations’ cyber threats. .., VOLTZITE is arguably the most
crucial threat group to track in critical infrastructure. Due to its dedicated
focus on OT data, the group is a capable threat to ICS asset owners and
operators. This group shares extensive technical overlaps with the Volt
Typhoon threat group tracked by other organizations. It utilizes the same
techniques as in previous years, setting up complex chains of network
infrastructure to target, compromise, and steal compromising OT-relevant
data—GIS data, OT network diagrams, OT operating instructions, etc.—from
victim ICS organizations. ... Increasing collaboration between hacktivist
groups and state-backed cyber actors has led to a hybrid threat model where
hacktivists amplify state objectives, either directly or through shared
infrastructure and intelligence. State actors increasingly look to exploit
hacktivist groups as proxies to conduct deniable cyber operations, allowing
for more aggressive attacks with reduced attribution risks.
Leveraging AR & VR for Remote Maintenance in Industrial IoT

AR tools like Microsoft’s HoloLens 2 are enabling workers on-site to receive
real-time guidance from experts located anywhere in the world. Using AR
glasses or headsets, on-site personnel can share their view with remote
technicians, who can then overlay instructions, schematics, or step-by-step
troubleshooting guidance directly onto the worker’s field of vision. This
allows maintenance teams to resolve issues faster and more accurately, without
the need for travel, reducing downtime and operational costs. ... By using VR
simulations, workers can familiarize themselves with equipment, troubleshoot
issues, and practice responses to emergencies, all in a virtual setting. This
hands-on experience builds confidence and competence, ultimately improving
safety and efficiency when dealing with real equipment. As IIoT systems become
more sophisticated, VR training can play a key role in ensuring that the
workforce is well-prepared to handle advanced technologies without risking
costly mistakes or accidents. ... In the future, we can expect even more
seamless integration between AR/VR systems and IIoT platforms, where real-time
data from sensors and machines is directly fed into the AR/VR environment,
providing a comprehensive view of machine health, performance and
issues.
Just as DNA defines an organism’s identity, business continuity must be deeply
embedded in every aspect of your organization. It is more than just a
collection of emergency plans or procedures; it embodies a philosophy that
ensures not only survival during disruptions, but long-term sustainability as
well. ... An organization without continuity is like a tree without
roots—fragile and vulnerable to the slightest shock. Continuity serves as an
anchor, allowing organizations to navigate crises while staying aligned with
their strategic goals. Any organization that aims to grow and thrive must take
a proactive approach to continuity. Continuity strategies and initiatives can
be seen as the roots of a tree, natural extensions that provide stability and
sustain growth. ... It is essential that both leaders and team members possess
the experience and skills needed to execute their work
effectively. ... Thoroughly assess your key vulnerabilities. This
involves two primary methods: a BIA, which analyzes the impacts of a
disturbance over time to determine recovery priorities, resource requirements,
and appropriate responses; and risk analysis, which identifies risks tied to
prioritized activities and critical resources. Together, these two approaches
offer a comprehensive understanding of your organization’s pain points.
Keep Your Network Safe From the Double Trouble of a ‘Compound Physical-Cyber Threat'

This phenomenon, a “compound physical-cyber threat,” where a cyberattack is
intentionally launched around a heatwave or hurricane, for example, would have
outsized and potentially devastating effects on businesses, communities, and
entire economies, according to a 2024 study led by researchers at Johns
Hopkins University. “Cyber-attacks are more disruptive when infrastructure
components face stresses beyond normal operating conditions,” the study
asserted. Businesses and their IT and risk management people would be wise to
take notice, because both cyberattacks and weather-related disasters are
increasing in frequency and in the cost they exact from their victims. ...
Take what you learn from the risk assessment to develop a detailed plan that
outlines the steps your organization intends to take to preserve
cybersecurity, business continuity, and network connectivity during a crisis.
Whether you’re a B2B or B2C organization, your customers, employees, suppliers
and other stakeholders expect your business to be “always on,” 24/7/365. How
will you keep the lights on, the lines of communications open, and your
network insulated from cyberattack during a disaster?
‘It Won’t Happen to Us:’ The Dangerous Mindset Minimizing Crisis Preparation

The main mistakes in crisis situations include companies staying silent and
not releasing official statements from management, creating a vacuum of
information and promoting the spread of rumors. ... First and foremost,
companies should not underestimate the importance of communication, especially
when things are not going well. During a crisis, many companies prefer to sit
quietly and wait without informing or sharing anything about their measures
and actions in connection with the crisis. This is the wrong approach. Silence
gives competitors enough space to thrive and gain a market advantage.
Meanwhile, journalists won’t stop working on hot stories. When you don’t share
anything meaningful with them or your audience, they may collect and publish
rumors and misinformation about your company. And the lack of comments creates
the ground for negative interpretations. Therefore, transparency and
efficiency are key principles of anti-crisis communication. If you are clear
in your messages and give quick responses, it allows the company to control
the information agenda. The surefire way to gain and maintain trust is to
promptly and regularly inform your company’s investors during a crisis through
your own channels.




































:format(webp)/cdn.vox-cdn.com/uploads/chorus_image/image/67002921/Holographic_optics_hero.0.png)

