Quantum Computing: Researchers Achieve 100 Million Quantum Operations
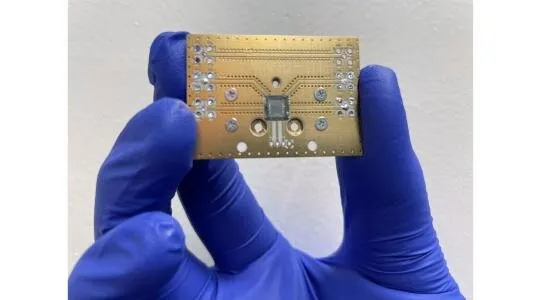
Quantum computing systems are notoriously difficult to maintain in coherent
states. The fragile nature of the "ordered chaos" is such that qubit information
and qubit connection (entanglement) usually deteriorates in scales much lower
than a second. The new research brings quantum computing coherency to
human-perceivable scales of time. Using a technique they've termed "single shot
readout," the researchers used precise laser pulses to add single electrons to
qubits. ... While it may not sound like much, time flows differently in
computing; going from stable quantum states in the order of fractions of a
second up to five seconds increases the amount of useful computing time
extracted from the available qubits. Moreover, it opens up new ways of
increasing processing power beyond pure qubit count - the researchers calculate
that they can perform around 100 million quantum operations in that five-second
slice. So perhaps quantum computing will be a threat to Bitcoin and the current
government, commercial and personal encryption schemes much earlier than
expected?
Meta to bring in mandatory distances between virtual reality avatars

Meta announced on Friday that it is introducing personal boundaries on two VR
apps: Horizon Worlds, where people can meet fellow VR users and design their own
world; and Horizon Venues, which hosts VR events such as comedy shows or music
gigs. The company said the distance between people will be the VR equivalent of
four feet. “A personal boundary prevents anyone from invading your avatar’s
personal space. If someone tries to enter your personal boundary, the system
will halt their forward movement as they reach the boundary,” said the company.
Meta is introducing the 4ft boundary as a default setting and will consider
further changes such as letting people set their own boundaries. “We think this
will help to set behavioural norms – and that’s important for a relatively new
medium like VR,” said Meta. The UK data watchdog has also said it is seeking
clarification from Meta about parental controls on the company’s popular Oculus
Quest 2 VR headset, as campaigners warned that it could breach an online
children’s safety code.
Platform Engineering Challenge: Security vs. Dev Experience

There are a few things that you can do to make things easier for developers.
First, ensure that all developers affected by the new policies are aware of
them. That lack of knowledge is a common reason for mistakes. Once the developer
team knows the security policies, they can work with those policies in mind.
Next, remember that mistakes can happen. To mitigate this, automate as many
items as possible with a proper continuous integration (CI) pipeline. In the CSP
example, it is possible to crawl your application automatically and report CSP
violations with a little bit of initial setup. Automating the verification step
can drastically reduce the possibility of mistakes. This doesn’t just apply to
CSP; it is relevant for any check you want to implement to ensure that your devs
follow particular guidelines or standards. Another potential inter-team headache
is vulnerabilities in third-party packages. Usually, the dev teams will install
new packages. Depending on your business structure, though, it might fall to the
platform or security teams to fix any vulnerabilities found.
Satya Nadella: Microsoft has “permission to build the next Internet”

[In] the Microsoft I grew up in, I always think about three things—and we added
a fourth. The three things that we always had are: we built tools for people to
write software; we built tools for people to drive their personal and
organizational productivity; and we built games. That’s the three things that
Microsoft has done from time immemorial. The first game, I think, was built
before Windows was there. existed on DOS. And so, to me, gaming, coding,
productivity, or knowledge worker tools are at the core. The thing that we added
pretty successfully—that most people thought we would never be able to do—is
become an enterprise company... actually really build enterprise
infrastructure... and business applications. And guess what? We now do that as
well. ... Take what’s happening with the metaverse. What is the metaverse?
Metaverse is essentially about creating games. It is about being able to put
people, places, things [in] a physics engine and then having all the people,
places, things in the physics engine relate to each other.
Council Post: Role of AI in creating inclusive products & solutions

Artificial Intelligence has the potential to create a more inclusive society.
Let’s consider two dimensions: language and disability. Language is often the
greatest barrier towards access to information, and hence, opportunities. Today
language translation using AI is removing that barrier. For example, Microsoft’s
Azure AI now empowers organizations to translate between 100 languages and
dialects globally, making information in text and documents accessible to more
than 5.6 billion people worldwide3. These include not only the world’s most
spoken languages like English, Chinese, Hindi, Arabic and Spanish, but also
dialects that are native or preferred by a smaller population. There are close
to 7,000 languages spoken around the world, but sadly, every two weeks a
language dies with its last speaker. Recent advances in AI have enabled
inclusion of low resource, and often endangered, languages and dialects such as
Tibetan, Assamese and Inuktitut. A multilingual AI model called Z-code combines
several languages from a language family such as Hindi, Marathi, and
Gujarati.
Mozilla is shutting down its VR web browser, Firefox Reality
A top VR web browser is closing down. Today, Mozilla announced it’s shutting
down its Firefox Reality browser — the four-year-old browser built for use in
virtual reality environments. The technology had allowed users to access the web
from within their VR headset, doing things like visiting URLs, performing
searches and browsing both the 2D and 3D internet using your VR hand
controllers, instead of a mouse. Firefox Reality first launched in fall
2018 and has been available on Viveport, Oculus, Pico and HoloLens platforms
through their various app stores. While capable of surfing the 2D web, the
expectation was that users would largely use the new technology to browse and
interact with the web’s 3D content, like 360-degree panoramic images and videos,
3D models and WebVR games, for example. But in an announcement published today,
Mozilla says the browser will be removed from the stores where it’s been
available for download in the “coming weeks.” Mozilla is instead directing users
who still want to utilize a web browser in VR to Igalia’s upcoming open source
browser, Wolvic, which is based on Firefox Reality’s source code.
How SQL can unify access to APIs

Software construction requires developers to compose solutions using a growing
proliferation of APIs. Often there’s a library to wrap each API in your
programming language of choice, so you’re spared the effort of making raw REST
calls and parsing the results. But each wrapper has its own way of representing
results, so when composing a multi-API solution you have to normalize those
representations. Since combining results happens in a language-specific way,
your solution is tied to that language. And if that language is JavaScript or
Python or Java or C# then it is arguably not the most universal and powerful way
to query (or update) a database. ... Steampipe is an open-source tool that
fetches data from diverse APIs and uses it to populate tables in a database. The
database is Postgres, which is, nowadays, a platform on which to build all kinds
of database-like systems by creating extensions that deeply customize the core.
One class of Postgres extension, the foreign data wrapper (FDW), creates tables
from external data. Steampipe embeds an instance of Postgres that loads an
API-oriented foreign data wrapper.
The wrong data privacy strategy could cost you billions

Regulators have long understood that de-identification is not a silver bullet
due to re-identification with side information. When regulators defined
anonymous or de-identified information, they refrained from giving a precise
definition and deliberately opted for a practical one based on the reasonable
risks of someone being re-identified. GDPR mentions “all the means reasonably
likely to be used” whereas CCPA defines de-identified to be “information that
cannot reasonably identify” an individual. The ambiguity of both definitions
leaves places the burden of privacy risk assessment onto the compliance team.
For each supposedly de-identified dataset, they need to prove that the
re-identification risk is not reasonable. To meet those standards and keep up
with proliferating data sharing, organizations have had to beef up their
compliance teams. This appears to have been the process that Netflix followed
when they launched a million-dollar prize to improve its movie recommendation
engine in 2006. They publicly released a stripped-down version of their dataset
with 500,000 movie reviews, enabling anyone in the world to develop and test
prediction engines that could beat theirs.
What the Rise in Cyber-Recon Means for Your Security Strategy

Enterprises need to be aware that an increase in new cybercriminals armed with
advanced technologies will increase the likelihood and volume of attacks.
Standard tools must be able to scale to address potential increases in attack
volumes. These tools also need to be enhanced with artificial intelligence (AI)
to detect attack patterns and stop threats in real time. Critical tools should
include anti-malware engines using AI detection signatures, endpoint detection
and response (EDR), advanced intrusion prevention system (IPS) detection,
sandbox solutions augmented with MITRE ATT&CK mappings and next-gen
firewalls (NGFWs). In the best-case scenario, these tools are deployed
consistently across the distributed network (data center, campus, branch,
multi-cloud, home office, endpoint) using an integrated security platform that
can detect, share, correlate and respond to threats as a unified solution.
Cybercriminals are opportunistic, and they’re also growing increasingly crafty.
We’re now seeing them spend more time on the reconnaissance side of
cyberattacks.
Want Real Cybersecurity Progress? Redefine the Security Team

The strategies described above share one trait in common: They all leave
security mostly in the hands of an elite security team. No matter how many
security tools a business buys, how far left it shifts security, or how many
compliance rules it enforces, security operations still remain the realm
primarily of security engineers and analysts (perhaps with just a bit of help
from developers and IT Ops teams at businesses that take DevSecOps seriously).
That fact is part of what makes the concept of collective security so
innovative. It fundamentally breaks a mold that has been in place for decades:
the mold that forces a single team to “own” security across the entire business,
leaving little opportunity for stakeholders who are not security experts to
contribute to security initiatives. By shifting to a strategy in which security
is everyone’s responsibility — and, just as important, where everyone has the
ability to define security rules and validate resources without having to know
how to code or use sophisticated security tools — businesses make it possible
for everyone to understand the state of cybersecurity in their organization, as
well as to help enforce cybersecurity standards.
Quote for the day:
"Great leaders go forward without
stopping, remain firm without tiring and remain enthusiastic while growing" --
Reed Markham
No comments:
Post a Comment