Quote for the day:
"The most powerful thing a leader can do is take something complicated and make it clear. Clarity is the ultimate competitive advantage." -- Gordon Tredgold
🎧 Listen to this digest on YouTube Music
▶ Play Audio DigestDuration: 24 mins • Perfect for listening on the go.
Edge + Cloud data modernisation: architecting real-time intelligence for IoT
 The article by Chandrakant Deshmukh explores the critical shift from traditional
"cloud-first" IoT architectures to a modernized edge-cloud continuum, which is
essential for achieving true real-time intelligence. The author argues that
purely cloud-centric models are failing due to prohibitive latency, high
bandwidth costs, and complex data sovereignty requirements. To address these
challenges, enterprises must adopt a tiered architectural approach governed by
"data gravity," where raw signals are processed locally at the edge for
immediate control, while the cloud is reserved for long-horizon analytics and
model training. This modernization relies on three core technical pillars: an
event-driven transport spine using protocols like MQTT and Kafka, a dedicated
stream-processing layer for real-time data handling, and digital twins to
synchronize physical assets with digital representations. Beyond technology, the
article emphasizes the importance of intellectual property governance, urging
organizations to clarify data ownership and lineage early in vendor contracts.
By treating edge and cloud as complementary tiers rather than competing
locations, businesses can unlock significant returns on investment, including
predictive maintenance and enhanced operational efficiency. Ultimately,
successful IoT modernization is not merely a technical project but a strategic
commitment to processing data at the most efficient tier to drive industrial
intelligence.
The article by Chandrakant Deshmukh explores the critical shift from traditional
"cloud-first" IoT architectures to a modernized edge-cloud continuum, which is
essential for achieving true real-time intelligence. The author argues that
purely cloud-centric models are failing due to prohibitive latency, high
bandwidth costs, and complex data sovereignty requirements. To address these
challenges, enterprises must adopt a tiered architectural approach governed by
"data gravity," where raw signals are processed locally at the edge for
immediate control, while the cloud is reserved for long-horizon analytics and
model training. This modernization relies on three core technical pillars: an
event-driven transport spine using protocols like MQTT and Kafka, a dedicated
stream-processing layer for real-time data handling, and digital twins to
synchronize physical assets with digital representations. Beyond technology, the
article emphasizes the importance of intellectual property governance, urging
organizations to clarify data ownership and lineage early in vendor contracts.
By treating edge and cloud as complementary tiers rather than competing
locations, businesses can unlock significant returns on investment, including
predictive maintenance and enhanced operational efficiency. Ultimately,
successful IoT modernization is not merely a technical project but a strategic
commitment to processing data at the most efficient tier to drive industrial
intelligence.AI Code Review Only Catches Half of Your Bugs
The O’Reilly Radar article, "AI Code Review Only Catches Half of Your Bugs," explores the critical limitations of using artificial intelligence for automated code verification. While AI tools like GitHub Copilot and CodeRabbit are proficient at identifying structural defects—such as null pointer dereferences, resource leaks, and race conditions—they struggle significantly with "intent violations." These are logical bugs that occur when the code executes successfully but fails to do what the developer actually intended. Research indicates that while AI can catch approximately 65% of structural issues, it often misses the deeper 35% to 50% of defects rooted in misunderstood requirements or complex business logic. The article emphasizes that AI lacks the institutional memory and operational context that human engineers possess. For instance, an AI agent might suggest an efficient code refactor that inadvertently bypasses a necessary security wrapper or violates a project-specific architectural guideline. To bridge this gap, the author suggests a shift toward "context-aware reasoning" and the use of tools like the Quality Playbook. This approach involves feeding AI agents specific documentation, such as READMEs and design notes, to help them "infer" intent. Ultimately, the piece argues that while AI is a powerful assistant, human oversight remains essential for catching the subtle, high-stakes errors that automated systems cannot yet perceive.Small Language Models (SLMs) as the gold standard for trust in AI
 The article argues that Small Language Models (SLMs) are emerging as the "gold
standard" for establishing trust in artificial intelligence, particularly in
precision-dependent industries like finance. While Large Language Models
(LLMs) often prioritize sounding confident and clever over being accurate,
they frequently succumb to hallucinations because they are trained on vast,
unverified datasets. In contrast, SLMs are trained on narrow, high-quality
data, allowing them to be faster, more cost-effective, and significantly more
accurate in their results. They aim to be "correct, not clever," making them
ideal for high-stakes environments where even minor errors can lead to severe
financial loss or compliance nightmares. The most resilient business strategy
involves orchestrating a hybrid architecture where LLMs serve as the intuitive
reasoning layer and user interface, while a "swarm" of specialized SLMs acts
as the deterministic verifiers for specific, granular tasks. This
collaboration is facilitated by tools like the Model Context Protocol,
ensuring that final outputs are grounded in fact rather than statistical
probability. Furthermore, trust is reinforced by incorporating confidence
scores and human-in-the-loop verification processes. Ultimately, shifting
toward specialized, connected AI architectures allows professionals to move
away from tedious manual data entry and focus on high-impact advisory work,
ensuring that AI remains a reliable and secure partner in complex professional
workflows.
The article argues that Small Language Models (SLMs) are emerging as the "gold
standard" for establishing trust in artificial intelligence, particularly in
precision-dependent industries like finance. While Large Language Models
(LLMs) often prioritize sounding confident and clever over being accurate,
they frequently succumb to hallucinations because they are trained on vast,
unverified datasets. In contrast, SLMs are trained on narrow, high-quality
data, allowing them to be faster, more cost-effective, and significantly more
accurate in their results. They aim to be "correct, not clever," making them
ideal for high-stakes environments where even minor errors can lead to severe
financial loss or compliance nightmares. The most resilient business strategy
involves orchestrating a hybrid architecture where LLMs serve as the intuitive
reasoning layer and user interface, while a "swarm" of specialized SLMs acts
as the deterministic verifiers for specific, granular tasks. This
collaboration is facilitated by tools like the Model Context Protocol,
ensuring that final outputs are grounded in fact rather than statistical
probability. Furthermore, trust is reinforced by incorporating confidence
scores and human-in-the-loop verification processes. Ultimately, shifting
toward specialized, connected AI architectures allows professionals to move
away from tedious manual data entry and focus on high-impact advisory work,
ensuring that AI remains a reliable and secure partner in complex professional
workflows.Upgrading legacy systems: How to confidently implement modernised applications
In the article "Upgrading legacy systems: How to confidently implement
modernised applications," Ger O’Sullivan explores the critical shift from
outdated technology to agile, AI-enhanced operational frameworks. For years,
legacy systems have served as organizational backbones but now present
significant hurdles, including high maintenance costs, security
vulnerabilities, and reduced agility. O’Sullivan argues that modernization is
no longer an optional luxury but a strategic imperative for sustained
competitiveness and growth. Fortunately, the emergence of AI-enabled tooling
and structured, end-to-end frameworks has made this process more predictable
and cost-effective than ever before. These advancements allow
organizations—particularly in the public sector where systems are often
undocumented and deeply integrated—to move away from risky "start from
scratch" approaches toward incremental, value-driven transformations. The
author emphasizes that successful modernization must be business-aligned
rather than purely technical, suggesting that leaders should prioritize
applications based on their potential business value and risk profile. By
starting with small, manageable pilots, teams can demonstrate quick wins,
build momentum, and refine their governance processes before scaling across
the enterprise. Ultimately, O’Sullivan highlights that with the right
strategic advisors and a focus on long-term outcomes, organizations can
transform their legacy burdens into powerful drivers of innovation, service
quality, and operational resilience.
 In the article "Relying on LLMs is nearly impossible when AI vendors keep
changing things," Evan Schuman examines the growing instability enterprise IT
faces when integrating generative AI systems. The core issue revolves around
AI vendors frequently implementing background updates without notifying
customers, a practice highlighted by a candid report from Anthropic. This
report detailed several instances where adjustments—meant to improve latency
or efficiency—inadvertently degraded model performance, such as reducing
reasoning depth or causing "forgetfulness" in sessions. Schuman argues that
while businesses have long accepted limited control over SaaS platforms, the
opaque nature of Large Language Models (LLMs) represents a new extreme.
Because these systems are non-deterministic and highly interdependent,
performance regressions are difficult for both vendors and users to detect or
reproduce accurately. Furthermore, the article notes a potential conflict of
interest: since most enterprise clients pay per token, vendors have a
financial incentive to make changes that increase consumption. Ultimately, the
author warns that the reliability of mission-critical AI applications is
currently at the mercy of vendors who can "dumb down" services overnight. He
concludes that internal monitoring of accuracy, speed, and cost is no longer
optional for organizations seeking a clean return on investment in an
environment defined by "buyer beware."
In the article "Relying on LLMs is nearly impossible when AI vendors keep
changing things," Evan Schuman examines the growing instability enterprise IT
faces when integrating generative AI systems. The core issue revolves around
AI vendors frequently implementing background updates without notifying
customers, a practice highlighted by a candid report from Anthropic. This
report detailed several instances where adjustments—meant to improve latency
or efficiency—inadvertently degraded model performance, such as reducing
reasoning depth or causing "forgetfulness" in sessions. Schuman argues that
while businesses have long accepted limited control over SaaS platforms, the
opaque nature of Large Language Models (LLMs) represents a new extreme.
Because these systems are non-deterministic and highly interdependent,
performance regressions are difficult for both vendors and users to detect or
reproduce accurately. Furthermore, the article notes a potential conflict of
interest: since most enterprise clients pay per token, vendors have a
financial incentive to make changes that increase consumption. Ultimately, the
author warns that the reliability of mission-critical AI applications is
currently at the mercy of vendors who can "dumb down" services overnight. He
concludes that internal monitoring of accuracy, speed, and cost is no longer
optional for organizations seeking a clean return on investment in an
environment defined by "buyer beware."
Relying on LLMs is nearly impossible when AI vendors keep changing things
 In the article "Relying on LLMs is nearly impossible when AI vendors keep
changing things," Evan Schuman examines the growing instability enterprise IT
faces when integrating generative AI systems. The core issue revolves around
AI vendors frequently implementing background updates without notifying
customers, a practice highlighted by a candid report from Anthropic. This
report detailed several instances where adjustments—meant to improve latency
or efficiency—inadvertently degraded model performance, such as reducing
reasoning depth or causing "forgetfulness" in sessions. Schuman argues that
while businesses have long accepted limited control over SaaS platforms, the
opaque nature of Large Language Models (LLMs) represents a new extreme.
Because these systems are non-deterministic and highly interdependent,
performance regressions are difficult for both vendors and users to detect or
reproduce accurately. Furthermore, the article notes a potential conflict of
interest: since most enterprise clients pay per token, vendors have a
financial incentive to make changes that increase consumption. Ultimately, the
author warns that the reliability of mission-critical AI applications is
currently at the mercy of vendors who can "dumb down" services overnight. He
concludes that internal monitoring of accuracy, speed, and cost is no longer
optional for organizations seeking a clean return on investment in an
environment defined by "buyer beware."
In the article "Relying on LLMs is nearly impossible when AI vendors keep
changing things," Evan Schuman examines the growing instability enterprise IT
faces when integrating generative AI systems. The core issue revolves around
AI vendors frequently implementing background updates without notifying
customers, a practice highlighted by a candid report from Anthropic. This
report detailed several instances where adjustments—meant to improve latency
or efficiency—inadvertently degraded model performance, such as reducing
reasoning depth or causing "forgetfulness" in sessions. Schuman argues that
while businesses have long accepted limited control over SaaS platforms, the
opaque nature of Large Language Models (LLMs) represents a new extreme.
Because these systems are non-deterministic and highly interdependent,
performance regressions are difficult for both vendors and users to detect or
reproduce accurately. Furthermore, the article notes a potential conflict of
interest: since most enterprise clients pay per token, vendors have a
financial incentive to make changes that increase consumption. Ultimately, the
author warns that the reliability of mission-critical AI applications is
currently at the mercy of vendors who can "dumb down" services overnight. He
concludes that internal monitoring of accuracy, speed, and cost is no longer
optional for organizations seeking a clean return on investment in an
environment defined by "buyer beware."The evolution of data protection: Why enterprises must move beyond traditional backup
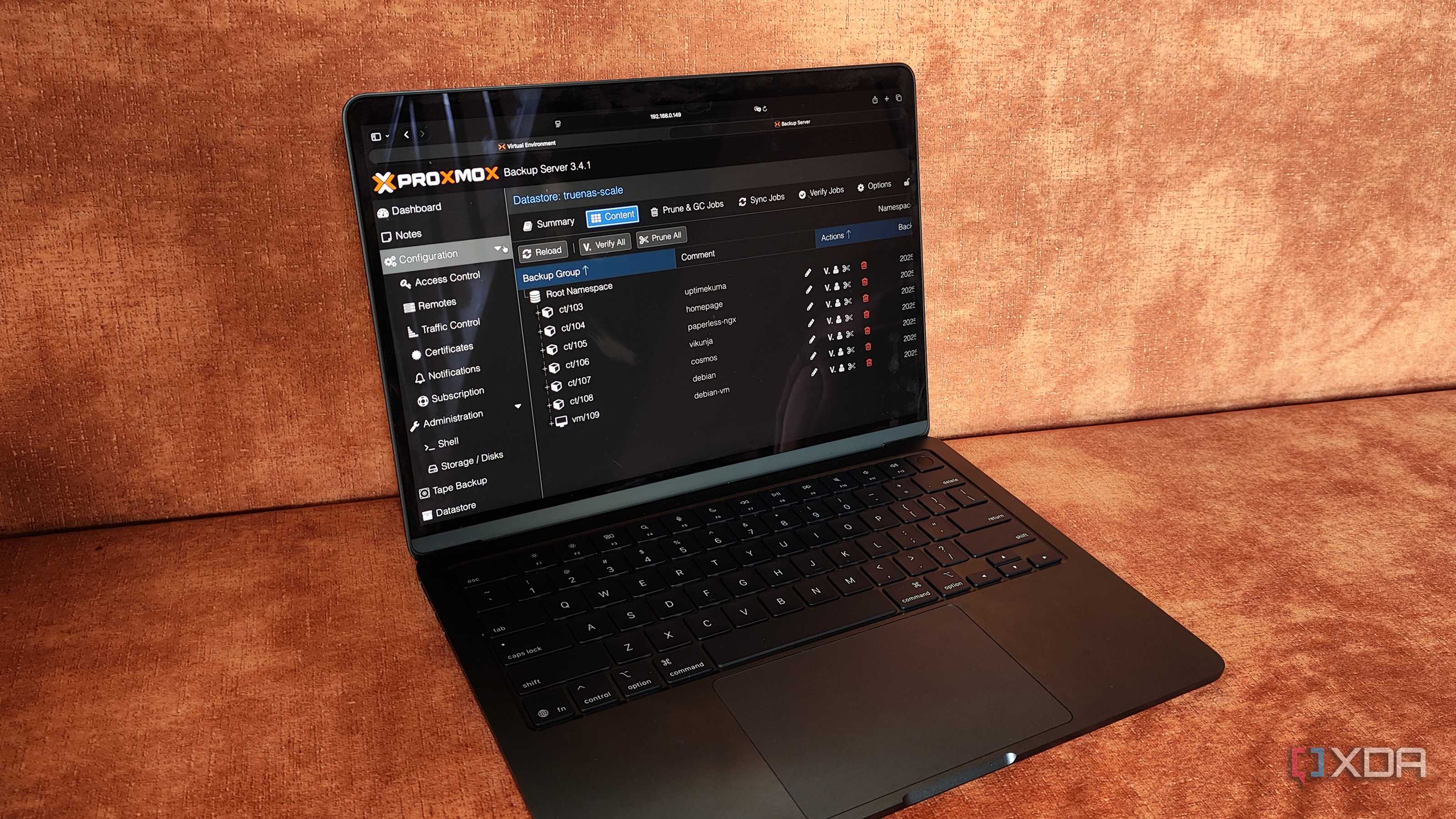
The article titled "The Evolution of Data Protection: Why Enterprises Must
Move Beyond Traditional Backup" explores the paradigm shift from simple data
recovery to comprehensive enterprise resilience. Author Seemanta Patnaik
argues that in today’s landscape of sophisticated AI-driven cyber threats and
ransomware, traditional backups serve only as a starting point rather than a
total solution. Modern enterprises face significant vulnerabilities, including
flat network architectures, legacy infrastructures, and human susceptibility
to phishing, necessitating a holistic lifecycle approach that encompasses
prevention, detection, and rapid response. Patnaik emphasizes that data
protection must be driven by risk-based thinking rather than mere regulatory
compliance, as sectors like banking and insurance face increasingly complex
legal mandates. Key strategies highlighted include the "3-2-1-1-0" rule,
rigorous testing of recovery systems, and the use of automation to manage the
scale of distributed data environments. Furthermore, critical metrics like
Recovery Time Objective (RTO) and Recovery Point Objective (RPO) are presented
as essential benchmarks for measuring business continuity effectiveness.
Ultimately, the piece asserts that true resilience requires executive-level
governance and a proactive shift toward predictive security models. By
integrating AI for faster threat detection and automated recovery,
organizations can better navigate the evolving digital ecosystem and ensure
they return to business as usual with minimal disruption.
What researchers learned about building an LLM security workflow
 The Help Net Security article "What researchers learned about building an LLM
security workflow" highlights critical findings from the University of Oslo
and the Norwegian Defence Research Establishment regarding the integration of
Large Language Models into Security Operations Centers. While vendors often
market LLMs as immediate solutions for alert triage, the research reveals that
these models fail significantly when operating in isolation. Specifically,
when provided with only high-level summaries of malicious network activity,
popular models like GPT-5-mini and Claude 3 Haiku achieved a zero percent
detection rate. However, performance improved dramatically when the models
were embedded within a structured, agentic workflow. By implementing a system
where models could plan investigations, execute specific SQL queries against
logs, and iteratively summarize evidence, malicious detection accuracy surged
to an average of 93 percent. This shift demonstrates that a model's
effectiveness is not solely dependent on its internal intelligence but rather
on the constrained tools and rigorous processes surrounding it. Despite this
success, the models often flagged benign cases as "uncertain," suggesting that
while such workflows reduce missed threats, they may still necessitate human
oversight. Ultimately, the study emphasizes that a well-defined architecture
is essential for transforming LLMs from passive data recipients into
proactive, reliable security analysts.
The Help Net Security article "What researchers learned about building an LLM
security workflow" highlights critical findings from the University of Oslo
and the Norwegian Defence Research Establishment regarding the integration of
Large Language Models into Security Operations Centers. While vendors often
market LLMs as immediate solutions for alert triage, the research reveals that
these models fail significantly when operating in isolation. Specifically,
when provided with only high-level summaries of malicious network activity,
popular models like GPT-5-mini and Claude 3 Haiku achieved a zero percent
detection rate. However, performance improved dramatically when the models
were embedded within a structured, agentic workflow. By implementing a system
where models could plan investigations, execute specific SQL queries against
logs, and iteratively summarize evidence, malicious detection accuracy surged
to an average of 93 percent. This shift demonstrates that a model's
effectiveness is not solely dependent on its internal intelligence but rather
on the constrained tools and rigorous processes surrounding it. Despite this
success, the models often flagged benign cases as "uncertain," suggesting that
while such workflows reduce missed threats, they may still necessitate human
oversight. Ultimately, the study emphasizes that a well-defined architecture
is essential for transforming LLMs from passive data recipients into
proactive, reliable security analysts.Cyber-physical resilience reshaping industrial cybersecurity beyond perimeter defense to protect core processes
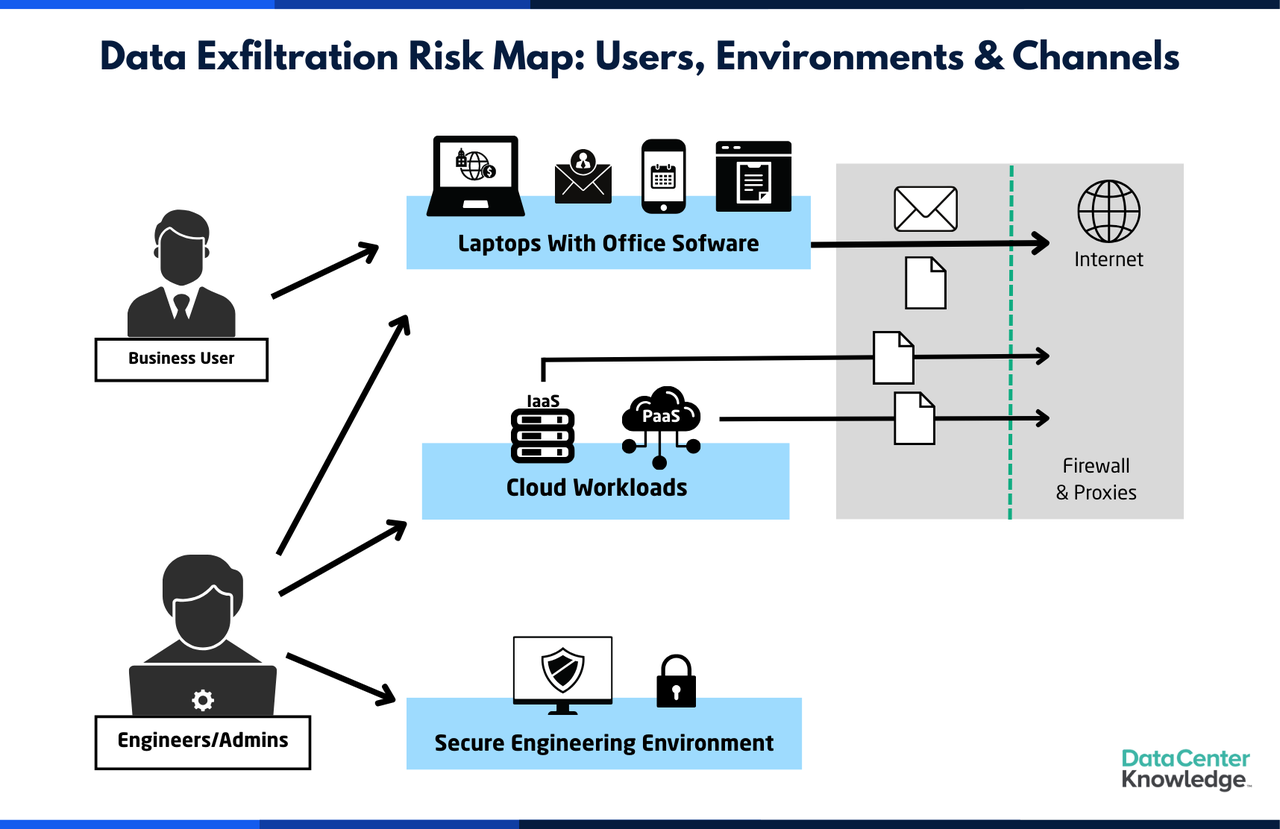
The article explores the critical transition from perimeter-centric defense to cyber-physical resilience in industrial cybersecurity, driven by the dissolution of traditional barriers between IT and OT environments. As operational technology becomes increasingly interconnected, conventional "air gaps" have vanished, leaving 78% of industrial control devices with unfixable vulnerabilities. Experts from firms like Booz Allen Hamilton and Fortinet emphasize that modern resilience is no longer just about preventing every attack but ensuring that essential services—such as power and water—continue to function even during a compromise. This proactive approach prioritizes the integrity of core processes over the absolute security of individual systems. Key challenges highlighted include a dangerous overconfidence among operators and a persistent lack of visibility into serial and analog communications, which remain the backbone of physical processes. With approximately 21% of industrial companies facing OT-specific attacks annually, the shift toward resilience demands continuous monitoring, cross-disciplinary collaboration, and dynamic recovery strategies. Ultimately, cyber-physical resilience is defined by an organization's capacity to identify, mitigate, and recover from disruptions without halting production. By focusing on process-level protection rather than just network boundaries, critical infrastructure can adapt to a landscape where cyber threats have direct, real-world physical consequences.AI exposes attacks traditional detection methods can’t see
 Evan Powell’s article on SiliconANGLE highlights a critical vulnerability in
modern cybersecurity: the inherent architectural limitations of rule-based
detection systems. For decades, security has relied on signatures, thresholds,
and anomaly baselines to identify threats. However, these traditional methods
are increasingly blind to side-channel attacks and sophisticated, AI-assisted
intrusions that utilize legitimate tools or encrypted channels. Because these
maneuvers do not produce discrete "matchable" signals or cross predefined
boundaries, they often remain invisible to standard scanners. The article
argues that the industry is currently deploying AI at the wrong layer; most
tools focus on post-detection response—such as summarizing alerts and
automating investigations—rather than the initial detection process itself.
This misplaced focus leaves a significant gap where attackers can operate
indefinitely without triggering a single alert. To close this divide, security
architecture must evolve beyond simple rules toward advanced AI systems
capable of interpreting complex patterns in timing, sequencing, and
interaction. Currently, the most dangerous signals are not traditional
indicators at all, but rather subtle behaviors that require a fundamental
shift in how detection is engineered. Without moving AI deeper into the
observation layer, organizations will continue to optimize their response to
known threats while remaining entirely exposed to a growing class of silent,
architectural-level attacks.
Evan Powell’s article on SiliconANGLE highlights a critical vulnerability in
modern cybersecurity: the inherent architectural limitations of rule-based
detection systems. For decades, security has relied on signatures, thresholds,
and anomaly baselines to identify threats. However, these traditional methods
are increasingly blind to side-channel attacks and sophisticated, AI-assisted
intrusions that utilize legitimate tools or encrypted channels. Because these
maneuvers do not produce discrete "matchable" signals or cross predefined
boundaries, they often remain invisible to standard scanners. The article
argues that the industry is currently deploying AI at the wrong layer; most
tools focus on post-detection response—such as summarizing alerts and
automating investigations—rather than the initial detection process itself.
This misplaced focus leaves a significant gap where attackers can operate
indefinitely without triggering a single alert. To close this divide, security
architecture must evolve beyond simple rules toward advanced AI systems
capable of interpreting complex patterns in timing, sequencing, and
interaction. Currently, the most dangerous signals are not traditional
indicators at all, but rather subtle behaviors that require a fundamental
shift in how detection is engineered. Without moving AI deeper into the
observation layer, organizations will continue to optimize their response to
known threats while remaining entirely exposed to a growing class of silent,
architectural-level attacks.Why service desks are emerging as a critical security weakness
The article from SecurityBrief Australia examines the escalating vulnerability
of corporate service desks, which have become primary targets for
sophisticated cybercriminals. While many organizations invest heavily in
technical perimeters, the service desk represents a critical "human element"
that is easily exploited through social engineering. Attackers utilize tactics
like voice phishing, or "vishing," to impersonate employees or high-level
executives, often leveraging personal information gathered from social media
or previous data breaches. Their ultimate objective is to manipulate help desk
staff into resetting passwords, enrolling unauthorized multi-factor
authentication devices, or bypassing standard security controls. This issue is
intensified by the broad permissions typically granted to service desk agents,
where a single compromised identity can provide a gateway to the entire
corporate network. Furthermore, the rise of remote work and the use of virtual
private networks have made verifying identities over digital channels
increasingly difficult. To combat these threats, the article advocates for a
fundamental shift toward the principle of least privilege and the
implementation of robust, automated identity verification processes, such as
biometric checks, to replace reliance on easily discoverable personal data.
Ultimately, organizations must prioritize securing the service desk to prevent
it from inadvertently serving as an open door for devastating ransomware
attacks and data breaches.







/dq/media/media_files/2026/02/04/tiny-ai-2026-02-04-16-39-39.jpg)