Quote for the day:
"You learn more from failure than from success. Don't let it stop you. Failure builds character." -- Unknown
🎧 Listen to this digest on YouTube Music
▶ Play Audio DigestDuration: 24 mins • Perfect for listening on the go.
CISOs step into the AI spotlight
 The article "CISOs step into the AI spotlight" examines the transformative
impact of artificial intelligence on the role of Chief Information Security
Officers (CISOs), who are increasingly transitioning from tactical overseers
to central strategic business partners. With 95% of security leaders now
engaging with boards multiple times a month, the CISO’s prominence is surging,
often leading to direct reporting lines to the board rather than the CIO.
Security experts like Barry Hensley, Shaun Khalfan, and Jeff Trudeau emphasize
that modern leadership requires balancing rapid AI adoption with robust
governance frameworks to ensure technology remains reliable and secure. This
shift necessitates that CISOs move beyond being the "department of no" to
become business enablers who translate technical risks into business value and
growth. Key challenges identified include the acceleration of AI-driven
phishing and automated vulnerability exploitation, which demand real-time
patching and continuous, embedded security practices. Furthermore, managing
the complexity of machine and human identities remains a top priority.
Ultimately, the article argues that successful contemporary CISOs must
actively use AI to understand its nuances, build organizational trust through
consistent guidance, and foster highly cohesive teams, ensuring that
cybersecurity becomes a competitive advantage rather than a friction point in
the era of agent-driven transactions.
The article "CISOs step into the AI spotlight" examines the transformative
impact of artificial intelligence on the role of Chief Information Security
Officers (CISOs), who are increasingly transitioning from tactical overseers
to central strategic business partners. With 95% of security leaders now
engaging with boards multiple times a month, the CISO’s prominence is surging,
often leading to direct reporting lines to the board rather than the CIO.
Security experts like Barry Hensley, Shaun Khalfan, and Jeff Trudeau emphasize
that modern leadership requires balancing rapid AI adoption with robust
governance frameworks to ensure technology remains reliable and secure. This
shift necessitates that CISOs move beyond being the "department of no" to
become business enablers who translate technical risks into business value and
growth. Key challenges identified include the acceleration of AI-driven
phishing and automated vulnerability exploitation, which demand real-time
patching and continuous, embedded security practices. Furthermore, managing
the complexity of machine and human identities remains a top priority.
Ultimately, the article argues that successful contemporary CISOs must
actively use AI to understand its nuances, build organizational trust through
consistent guidance, and foster highly cohesive teams, ensuring that
cybersecurity becomes a competitive advantage rather than a friction point in
the era of agent-driven transactions.The Future Of Engineering Is Hybrid
 Jo Debecker’s article, "The Future of Engineering is Hybrid," argues that the
evolution of the field depends on the intentional synergy between human
ingenuity and machine precision rather than AI’s solo capabilities. Far from
replacing engineers, AI serves as a powerful augmentative tool that
accelerates innovation and optimizes complex workflows in sectors like
aerospace and defense. The author emphasizes that while AI can automate
deterministic tasks and process vast datasets, human oversight remains
indispensable for judgment, ethical accountability, and validating outcomes
through a modern "four-eyes principle." Critical thinking and domain expertise
become even more vital as the engineer’s role shifts toward selecting,
grounding, and customizing AI models for specific industrial applications.
Effective hybrid engineering requires a multidisciplinary approach,
integrating cross-functional teams that combine technical, business, and data
perspectives. Furthermore, organizations must prioritize robust governance and
proactive upskilling to ensure AI adoption remains ethical and value-driven.
Ultimately, the hybrid model does not present a choice between humans or
machines but advocates for an "and" strategy where AI elevates human
potential. By maintaining clear human control points and fostering AI fluency,
the engineering landscape can achieve unprecedented efficiency and reliability
while keeping human responsibility at the core of technological progress.
Jo Debecker’s article, "The Future of Engineering is Hybrid," argues that the
evolution of the field depends on the intentional synergy between human
ingenuity and machine precision rather than AI’s solo capabilities. Far from
replacing engineers, AI serves as a powerful augmentative tool that
accelerates innovation and optimizes complex workflows in sectors like
aerospace and defense. The author emphasizes that while AI can automate
deterministic tasks and process vast datasets, human oversight remains
indispensable for judgment, ethical accountability, and validating outcomes
through a modern "four-eyes principle." Critical thinking and domain expertise
become even more vital as the engineer’s role shifts toward selecting,
grounding, and customizing AI models for specific industrial applications.
Effective hybrid engineering requires a multidisciplinary approach,
integrating cross-functional teams that combine technical, business, and data
perspectives. Furthermore, organizations must prioritize robust governance and
proactive upskilling to ensure AI adoption remains ethical and value-driven.
Ultimately, the hybrid model does not present a choice between humans or
machines but advocates for an "and" strategy where AI elevates human
potential. By maintaining clear human control points and fostering AI fluency,
the engineering landscape can achieve unprecedented efficiency and reliability
while keeping human responsibility at the core of technological progress.Why Most App Modernization Efforts Fail, and How a Capabilities-Driven Strategy Can Stop the Billion-Dollar Bleed
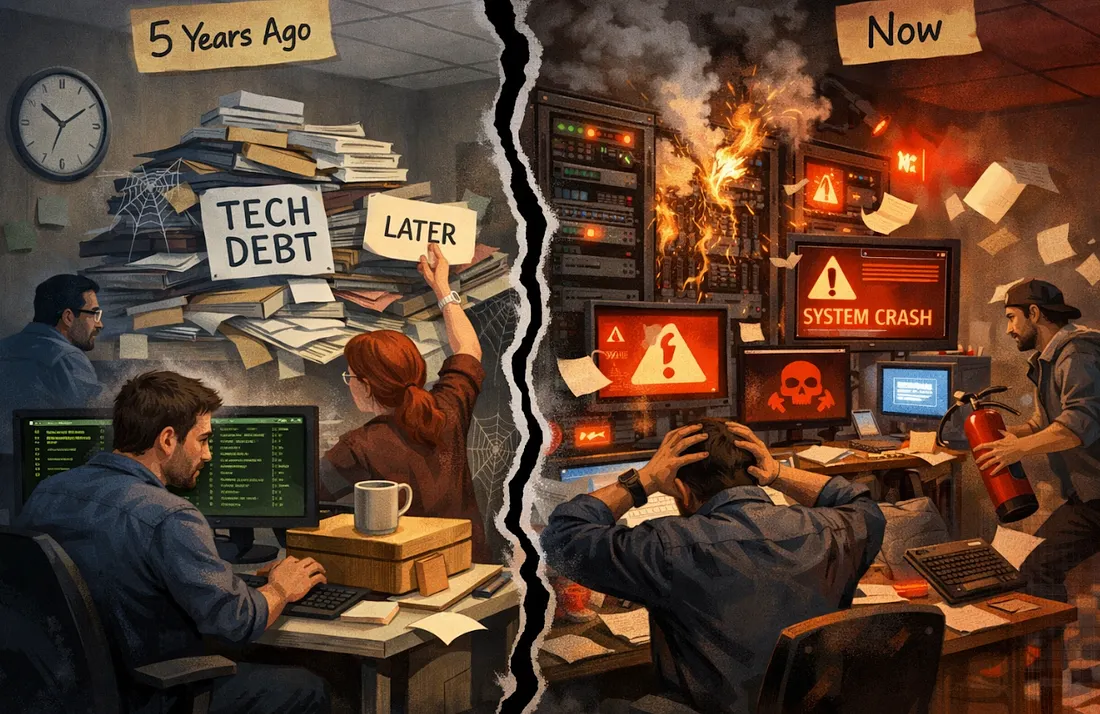
 The article "Why Most App Modernization Efforts Fail, and How a
Capabilities-Driven Strategy Can Stop the Billion-Dollar Bleed" explores the
pervasive struggle of organizations to modernize their legacy systems, noting
that a staggering 79% of such initiatives end in failure. These failures are
primarily attributed to deep-seated issues like unsustainable technical debt,
monolithic architectures that hinder scalability, and escalating security
risks. Furthermore, many projects falter because they lack alignment with
business value—often attempting to "boil the ocean" with overly complex,
multi-year programs that succumb to the "bowl of spaghetti" problem, where
minor changes trigger widespread system regressions. To combat these pitfalls,
the author advocates for a capabilities-driven strategy that shifts the focus
from mere technology replacement to business outcome enablement. By anchoring
modernization decisions to specific organizational business
capabilities—classified as strategic, core, or supporting—enterprises can
ensure cross-functional alignment and create a prioritized roadmap. This
approach allows for the decomposition of massive, risky programs into smaller,
independently deliverable increments that provide measurable value.
Ultimately, by aligning technology domains with capability boundaries,
organizations can reduce the "blast radius" of individual failures, maintain
stakeholder support, and achieve a sustainable architecture that truly
supports digital transformation and market agility.
The article "Why Most App Modernization Efforts Fail, and How a
Capabilities-Driven Strategy Can Stop the Billion-Dollar Bleed" explores the
pervasive struggle of organizations to modernize their legacy systems, noting
that a staggering 79% of such initiatives end in failure. These failures are
primarily attributed to deep-seated issues like unsustainable technical debt,
monolithic architectures that hinder scalability, and escalating security
risks. Furthermore, many projects falter because they lack alignment with
business value—often attempting to "boil the ocean" with overly complex,
multi-year programs that succumb to the "bowl of spaghetti" problem, where
minor changes trigger widespread system regressions. To combat these pitfalls,
the author advocates for a capabilities-driven strategy that shifts the focus
from mere technology replacement to business outcome enablement. By anchoring
modernization decisions to specific organizational business
capabilities—classified as strategic, core, or supporting—enterprises can
ensure cross-functional alignment and create a prioritized roadmap. This
approach allows for the decomposition of massive, risky programs into smaller,
independently deliverable increments that provide measurable value.
Ultimately, by aligning technology domains with capability boundaries,
organizations can reduce the "blast radius" of individual failures, maintain
stakeholder support, and achieve a sustainable architecture that truly
supports digital transformation and market agility.Why Australia's ransomware spike misses the bigger story
 The article "Why Australia’s ransomware spike misses the bigger story"
explains that regional surges in ransomware often distract from more critical
shifts in the global threat landscape. While Australia recently experienced a
prominent spike in attacks, the author contends that ransomware groups are
primarily opportunistic rather than geographically focused. A drop in regional
victim rankings often reflects a temporary shift in attacker attention—such as
targeting specific geopolitical events—rather than a genuine improvement in
local security. The "bigger story" lies in the evolving nature of
cyberattacks, where the "time-to-exploit" window has collapsed from days to
just hours, forcing a move from reactive to proactive defense. Modern
attackers are increasingly utilizing "living-off-the-land" (LOTL) techniques
to blend in with legitimate network activity, bypassing traditional malware
detection. Additionally, techniques like "bring your own vulnerable driver"
(BYOVD) allow them to disable system-level protections. Automation further
accelerates the attack lifecycle, allowing for rapid reconnaissance and
exploitation at scale. Ultimately, the article argues that organizations must
stop focusing on fluctuating regional statistics and instead prioritize
hardening internal defenses. This requires redefining what constitutes
"normal" network behavior and implementing robust security practices that
align with these faster, stealthier, and more dynamic modern threats.
The article "Why Australia’s ransomware spike misses the bigger story"
explains that regional surges in ransomware often distract from more critical
shifts in the global threat landscape. While Australia recently experienced a
prominent spike in attacks, the author contends that ransomware groups are
primarily opportunistic rather than geographically focused. A drop in regional
victim rankings often reflects a temporary shift in attacker attention—such as
targeting specific geopolitical events—rather than a genuine improvement in
local security. The "bigger story" lies in the evolving nature of
cyberattacks, where the "time-to-exploit" window has collapsed from days to
just hours, forcing a move from reactive to proactive defense. Modern
attackers are increasingly utilizing "living-off-the-land" (LOTL) techniques
to blend in with legitimate network activity, bypassing traditional malware
detection. Additionally, techniques like "bring your own vulnerable driver"
(BYOVD) allow them to disable system-level protections. Automation further
accelerates the attack lifecycle, allowing for rapid reconnaissance and
exploitation at scale. Ultimately, the article argues that organizations must
stop focusing on fluctuating regional statistics and instead prioritize
hardening internal defenses. This requires redefining what constitutes
"normal" network behavior and implementing robust security practices that
align with these faster, stealthier, and more dynamic modern threats.
AI saddles CIOs with new make-or-break expectations
 The rapid rise of artificial intelligence has significantly transformed the
role of Chief Information Officers (CIOs), saddling them with new
"make-or-break" expectations that extend far beyond traditional IT management.
According to Deloitte’s 2026 Global Leadership Technology Study, modern IT
leaders are no longer just evaluated on system uptime and technical delivery;
they are now increasingly judged on their ability to drive enterprise value
and navigate complex organizational transformations. While many CIOs
prioritize business outcomes, they face immense pressure to foster AI and data
fluency across their organizations while building specialized, AI-ready teams.
This shift requires CIOs to act as pathfinders and strategic evangelists who
can bridge the gap between technical potential and practical workflow changes.
One of the most significant hurdles remains a critical shortage of AI talent,
forcing leaders to adopt creative strategies such as retraining current staff
and strengthening partnerships with human resources. Furthermore, the
transition necessitates a focus on psychological safety, as leaders must
reassure employees by emphasizing job augmentation rather than replacement.
Ultimately, successful CIOs in this era must master the art of redesigning
work and decision-making processes, ensuring that the human and digital
workforces can collaborate effectively to deliver tangible business results in
a rapidly evolving technological landscape.
The rapid rise of artificial intelligence has significantly transformed the
role of Chief Information Officers (CIOs), saddling them with new
"make-or-break" expectations that extend far beyond traditional IT management.
According to Deloitte’s 2026 Global Leadership Technology Study, modern IT
leaders are no longer just evaluated on system uptime and technical delivery;
they are now increasingly judged on their ability to drive enterprise value
and navigate complex organizational transformations. While many CIOs
prioritize business outcomes, they face immense pressure to foster AI and data
fluency across their organizations while building specialized, AI-ready teams.
This shift requires CIOs to act as pathfinders and strategic evangelists who
can bridge the gap between technical potential and practical workflow changes.
One of the most significant hurdles remains a critical shortage of AI talent,
forcing leaders to adopt creative strategies such as retraining current staff
and strengthening partnerships with human resources. Furthermore, the
transition necessitates a focus on psychological safety, as leaders must
reassure employees by emphasizing job augmentation rather than replacement.
Ultimately, successful CIOs in this era must master the art of redesigning
work and decision-making processes, ensuring that the human and digital
workforces can collaborate effectively to deliver tangible business results in
a rapidly evolving technological landscape.
Do Software QA Engineers Need a Personal Brand?
In her insightful article, Anna Kovalova explores why software quality assurance engineers should prioritize personal branding to bridge the gap between technical expertise and professional visibility. She emphasizes that a personal brand is essentially the mental image colleagues and potential employers hold regarding your reliability and problem-solving capabilities. While many testers believe that strong work speaks for itself, Kovalova argues that talent requires a marketing multiplier to reach its full impact beyond a single team. By becoming more visible through professional platforms like LinkedIn, QA engineers can reduce uncertainty for others, making it significantly easier for new opportunities and high-level partnerships to materialize organically. The author clarifies that branding does not necessitate becoming a social media influencer; rather, it involves being consistent, clear, and human about one’s professional contributions. Practical steps include focusing on specific niche topics, sharing small but valuable lessons regularly, and using AI tools to enhance structure while maintaining a unique, authentic voice. Ultimately, personal branding serves as a career-scaling mechanism that ensures your reputation enters the room before you do. By shifting from being "invisible" to recognizable, QA professionals can unlock greater financial rewards, professional confidence, and a robust industry network that provides long-term security in an ever-evolving software testing job market.Large Language Models in Software Security Analysis
 The article "Large Language Models in Software Security Analysis" explores the
revolutionary shift toward autonomous Cyber-Reasoning Systems (CRSs) powered
by Large Language Models (LLMs). As modern software scales in complexity
across diverse languages and environments, traditional manual security audits
become increasingly unsustainable. To address this, the authors propose a
consolidated CRS framework decomposed into seven essential sub-components.
These include static analysis to build a system-level understanding,
identifying build and execution requirements, and generating testcases
designed to trigger vulnerabilities. Once a potential flaw is identified, the
system moves through vulnerability analysis, generates a reproducible
proof-of-vulnerability (PoV), synthesizes an automated patch, and finally
validates that remediation against the original exploit. An orchestrator
manages these processes, allocating resources and facilitating communication
between LLM-driven and traditional analysis tools. While LLMs offer
unprecedented capabilities in handling polyglot code and creative
problem-solving, the paper highlights technical hurdles such as budget
management and the need for holistic reasoning in heterogeneous systems.
Drawing inspiration from the DARPA AI CyberChallenge, the research articulates
a roadmap for integrating generative AI into the software security pipeline,
transforming it from a reactive, human-centric task into a proactive, fully
autonomous operation. Ultimately, the authors argue that this paradigm shift
represents a fundamental transformation in how we discover and repair critical
vulnerabilities at scale.
The article "Large Language Models in Software Security Analysis" explores the
revolutionary shift toward autonomous Cyber-Reasoning Systems (CRSs) powered
by Large Language Models (LLMs). As modern software scales in complexity
across diverse languages and environments, traditional manual security audits
become increasingly unsustainable. To address this, the authors propose a
consolidated CRS framework decomposed into seven essential sub-components.
These include static analysis to build a system-level understanding,
identifying build and execution requirements, and generating testcases
designed to trigger vulnerabilities. Once a potential flaw is identified, the
system moves through vulnerability analysis, generates a reproducible
proof-of-vulnerability (PoV), synthesizes an automated patch, and finally
validates that remediation against the original exploit. An orchestrator
manages these processes, allocating resources and facilitating communication
between LLM-driven and traditional analysis tools. While LLMs offer
unprecedented capabilities in handling polyglot code and creative
problem-solving, the paper highlights technical hurdles such as budget
management and the need for holistic reasoning in heterogeneous systems.
Drawing inspiration from the DARPA AI CyberChallenge, the research articulates
a roadmap for integrating generative AI into the software security pipeline,
transforming it from a reactive, human-centric task into a proactive, fully
autonomous operation. Ultimately, the authors argue that this paradigm shift
represents a fundamental transformation in how we discover and repair critical
vulnerabilities at scale.
Agent Observability Shouldn't Just Be About Vulnerabilities
The SecureWorld article "Agent Observability Shouldn't Just Be About Vulnerabilities" argues that cybersecurity teams must move beyond simple risk metrics to provide leadership with a comprehensive map of how AI agents drive business value. While monitoring vulnerabilities is essential for risk management, the piece emphasizes that board-level executives are primarily concerned with ROI, productivity gains, and the operationalization of successful AI use cases. Currently, many organizations are rapidly adopting AI without robust governance, making it difficult to evaluate effectiveness. Identifying these agents is a complex, non-deterministic task that involves monitoring API traffic, logs, and account access rather than traditional file scanning. Because security teams are already doing the heavy lifting of characterizing agent behavior and data interaction, they are uniquely positioned to describe business functions to stakeholders. By categorizing telemetry into meaningful projects—such as supply chain optimization, automated customer service, or healthcare documentation—CISOs can transition from being perceived as "blockers" to being drivers of business success. Ultimately, effective agent observability provides the visibility needed to secure workloads while simultaneously uncovering where AI is creating the most significant tangible value, ensuring that cybersecurity remains integral to the organization’s broader strategic transformation and long-term innovation goals.Time-Series Storage: Design Choices That Shape Cost and Performancet
/articles/time-series-storage-design/en/smallimage/Time-Series-Storage-Design-Choices-That-Shape-Cost-and-Performance-thumb-1778155792101.jpg) The article "Time-Series Storage: Design Choices That Shape Cost and
Performance" explores fundamental architectural decisions in time-series
database design using practical tools like PostgreSQL and Apache Parquet. A
central theme is the efficiency gained through normalization, where separating
series identity into dedicated metadata tables can reduce storage requirements
by roughly forty-two percent. The author emphasizes keeping high-cardinality
fields out of these identities to prevent linear growth in indexing costs.
Strategy choices like using flexible JSON for tags offer schema agility but
require careful indexing to avoid performance drift. Furthermore, the article
highlights time partitioning as a critical mechanism for O(1) data expiration
and improved query pruning, especially when combined with a second axis like
series identity to balance write loads. Downsampling is presented as a
powerful optimization, drastically reducing row counts for historical data
while retaining high-resolution accuracy for recent windows. For large-scale
deployments, the design shifts toward decoupling compute from storage,
utilizing Parquet files on object storage and open table formats like Apache
Iceberg to ensure ACID compliance and broad engine compatibility. Ultimately,
the piece argues that these structural choices governing row layout,
compression, and partitioning influence cost and performance far more
significantly than the specific database engine selected.
The article "Time-Series Storage: Design Choices That Shape Cost and
Performance" explores fundamental architectural decisions in time-series
database design using practical tools like PostgreSQL and Apache Parquet. A
central theme is the efficiency gained through normalization, where separating
series identity into dedicated metadata tables can reduce storage requirements
by roughly forty-two percent. The author emphasizes keeping high-cardinality
fields out of these identities to prevent linear growth in indexing costs.
Strategy choices like using flexible JSON for tags offer schema agility but
require careful indexing to avoid performance drift. Furthermore, the article
highlights time partitioning as a critical mechanism for O(1) data expiration
and improved query pruning, especially when combined with a second axis like
series identity to balance write loads. Downsampling is presented as a
powerful optimization, drastically reducing row counts for historical data
while retaining high-resolution accuracy for recent windows. For large-scale
deployments, the design shifts toward decoupling compute from storage,
utilizing Parquet files on object storage and open table formats like Apache
Iceberg to ensure ACID compliance and broad engine compatibility. Ultimately,
the piece argues that these structural choices governing row layout,
compression, and partitioning influence cost and performance far more
significantly than the specific database engine selected.

















/articles/architecting-autonomy-scale/en/smallimage/architecting-autonomy-scale-thumbnail-1774360140662.jpg)


/dq/media/media_files/2026/02/25/is-ai-killing-sustainability-2026-02-25-16-14-35.jpg)