Quote for the day:
"The starting point of all achievement is desire." -- Napolean Hill
Senate Bill Seeks Privacy Protection for Brain Wave Data
 The senators contend that a growing number of consumer wearables and devices
"are quietly harvesting sensitive brain-related data with virtually no oversight
and no limits on how it can be used." Neural data, such as brain waves or
signals from neural implants can potentially reveal thoughts, emotions or
decisions-making patterns that could be collected and used by third parties,
such as data brokers, to manipulate consumers and even potentially threaten
national security, the senators said. ... Colorado defines neural data "as
information that is generated by the measurement of the activity of an
individual's central or peripheral nervous systems and that can be processed by
or with the assistance of a device,'" Rose said. Neural data is a subcategory of
"biological data," which Colorado defines as "data generated by the
technological processing, measurement, or analysis of an individual's
biological, genetic, biochemical, physiological, or neural properties,
compositions, or activities or of an individual's body or bodily functions,
which data is used or intended to be used, singly or in combination with other
personal data, for identification purposes," she said. ... Neuralink is
currently in clinical trials for an implantable, wireless brain device designed
to interpret a person's neural activity. The device is designed to help patients
operate a computer or smartphone "by simply intending to move - no wires or
physical movement are required."
The senators contend that a growing number of consumer wearables and devices
"are quietly harvesting sensitive brain-related data with virtually no oversight
and no limits on how it can be used." Neural data, such as brain waves or
signals from neural implants can potentially reveal thoughts, emotions or
decisions-making patterns that could be collected and used by third parties,
such as data brokers, to manipulate consumers and even potentially threaten
national security, the senators said. ... Colorado defines neural data "as
information that is generated by the measurement of the activity of an
individual's central or peripheral nervous systems and that can be processed by
or with the assistance of a device,'" Rose said. Neural data is a subcategory of
"biological data," which Colorado defines as "data generated by the
technological processing, measurement, or analysis of an individual's
biological, genetic, biochemical, physiological, or neural properties,
compositions, or activities or of an individual's body or bodily functions,
which data is used or intended to be used, singly or in combination with other
personal data, for identification purposes," she said. ... Neuralink is
currently in clinical trials for an implantable, wireless brain device designed
to interpret a person's neural activity. The device is designed to help patients
operate a computer or smartphone "by simply intending to move - no wires or
physical movement are required." The hidden cyber risks of deploying generative AI
 Unfortunately, organizations aren’t thinking enough about security. The World
Economic Forum (WEF) reports that 66% of organizations believe AI will
significantly affect cybersecurity in the next 12 months, but only 37% have
processes in place to assess AI security before deployment. Smaller businesses
are even more exposed—69% lack safeguards for secure AI deployment, such as
monitoring training data or inventorying AI assets. Accenture finds similar
gaps: 77% of organizations lack foundational data and AI security practices, and
only 20% express confidence in their ability to secure generative AI models. ...
Both WEF and Accenture emphasize that the organizations best prepared for the AI
era are those with integrated strategies and strong cybersecurity capabilities.
Accenture’s research shows that only 10% of companies have reached what it calls
the “Reinvention-Ready Zone,” which combines mature cyber strategies with
integrated monitoring, detection and response capabilities. Firms in that
category are 69% less likely to experience AI-powered cyberattacks than less
prepared organizations. ... For enterprises, the path forward is about balancing
ambition with caution. AI can boost efficiency, creativity and competitiveness,
but only if deployed responsibly. Organizations should make AI security a
board-level priority, establish clear governance frameworks, and ensure their
cybersecurity teams are trained to address emerging AI-driven threats.
Unfortunately, organizations aren’t thinking enough about security. The World
Economic Forum (WEF) reports that 66% of organizations believe AI will
significantly affect cybersecurity in the next 12 months, but only 37% have
processes in place to assess AI security before deployment. Smaller businesses
are even more exposed—69% lack safeguards for secure AI deployment, such as
monitoring training data or inventorying AI assets. Accenture finds similar
gaps: 77% of organizations lack foundational data and AI security practices, and
only 20% express confidence in their ability to secure generative AI models. ...
Both WEF and Accenture emphasize that the organizations best prepared for the AI
era are those with integrated strategies and strong cybersecurity capabilities.
Accenture’s research shows that only 10% of companies have reached what it calls
the “Reinvention-Ready Zone,” which combines mature cyber strategies with
integrated monitoring, detection and response capabilities. Firms in that
category are 69% less likely to experience AI-powered cyberattacks than less
prepared organizations. ... For enterprises, the path forward is about balancing
ambition with caution. AI can boost efficiency, creativity and competitiveness,
but only if deployed responsibly. Organizations should make AI security a
board-level priority, establish clear governance frameworks, and ensure their
cybersecurity teams are trained to address emerging AI-driven threats.7 hard-earned lessons of bad IT manager hires
 Hiring IT managers is difficult. You are looking for a unicorn-like set of
skills: the technical acuity to understand projects and guide engineers, the
people skills to do so without ruffling feathers, and a leadership mindset that
can build a team and take it in the right direction. Hiring for any tech role
can be fraught with peril — with IT managers it’s even more so. One recent study
found that 87% of technology leaders are struggling to find talent that has the
skills they need. And when they do find that rare breed, it’s often not as
perfect as it first seemed. Deloitte’s 2025 Global Human Capital Trends survey
found that, for two-thirds of managers and executives, recent hires did not have
what was needed. Given this landscape, you’re bound to make mistakes. But you
don’t have to make all of them yourself. You can learn from what others have
experienced and go into this effort with hard-won experience — even if it isn’t
your own. ... Managing that many people is crushing. “It’s hard to keep track of
what they’re all working on or how to set them up for success,” Mishra says. “I
saw signs of dysfunction. People felt directionless and were getting blocked.
Some brilliant engineers were taking on manager tasks because I was in
back-to-back meetings and firefighting all the time. Productivity lowered
because my top performers were doing things not natural to them.”
Hiring IT managers is difficult. You are looking for a unicorn-like set of
skills: the technical acuity to understand projects and guide engineers, the
people skills to do so without ruffling feathers, and a leadership mindset that
can build a team and take it in the right direction. Hiring for any tech role
can be fraught with peril — with IT managers it’s even more so. One recent study
found that 87% of technology leaders are struggling to find talent that has the
skills they need. And when they do find that rare breed, it’s often not as
perfect as it first seemed. Deloitte’s 2025 Global Human Capital Trends survey
found that, for two-thirds of managers and executives, recent hires did not have
what was needed. Given this landscape, you’re bound to make mistakes. But you
don’t have to make all of them yourself. You can learn from what others have
experienced and go into this effort with hard-won experience — even if it isn’t
your own. ... Managing that many people is crushing. “It’s hard to keep track of
what they’re all working on or how to set them up for success,” Mishra says. “I
saw signs of dysfunction. People felt directionless and were getting blocked.
Some brilliant engineers were taking on manager tasks because I was in
back-to-back meetings and firefighting all the time. Productivity lowered
because my top performers were doing things not natural to them.”When Your CEO’s Leadership Creates Chaos
By speaking her CEO’s language, she shifted from being perceived as obstructive to being seen as a trusted advisor. Leaders are far more receptive when ideas connect directly to their stated priorities. Test every message against your CEO’s core priorities, growth, clients, investors, or whatever drives them. Reinforce your case with external validation such as market data, board expectations, or customer benchmarks. ... Fast-moving CEOs often create organizational whiplash by revisiting decisions or overruling execution midstream. Ambiguity fuels frustration. The antidote is building explicit agreements, which reduces micromanagement while preserving momentum. ... To avoid overlap and blind spots, the group divided responsibilities into distinct categories: customer acquisition, customer retention, and operational efficiency. Together, they then presented a unified, comprehensive strategy to the CEO. This not only made their recommendations harder to dismiss but also replaced a sense of isolation with coordinated leadership. Informal dinners, side meetings, and peer check-ins strengthened the coalition and amplified their collective voice. ... At the offsite, Alex connected her weekly progress updates to a broader organizational direction-setting check-in: revisiting the vision, identifying big moves, reallocating resources, and choosing one operating principle to shift. This kept her updates both visible and tied to strategy.From outdated IT to smart modern workplaces: how to do that?
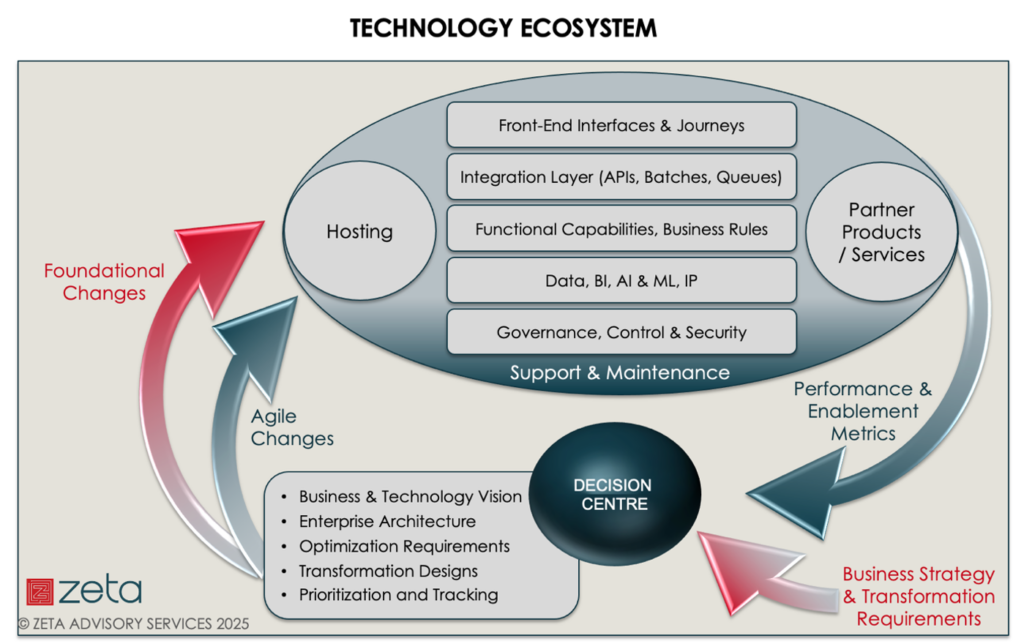
 Many organizations still run critical systems on-premises, while at the same
time wanting to use cloud applications. As a result, traditional management with
domains and Group Policy Objects (GPOs) is slowly disappearing. Microsoft Intune
offers an alternative, but in practice, it is less streamlined. “What you used
to manage centrally with GPOs now has to be set up in different places in
Intune,” explains Van Wingerden. ... A hybrid model inevitably involves
more complex budgeting. Costs for virtual machines, storage, or licenses only
become apparent over time, which means financial surprises are lurking.
Technical factors also play a role. Some applications perform better locally due
to latency or regulations, while others benefit from cloud scalability. The
result? ... The traditional closed workplace no longer suffices in this new
landscape. Zero Trust is becoming the starting point, with dynamic verification
per user and context. “We can say: based on the user’s context, we make things
possible or impossible within that Windows workplace,” says Van Wingerden. Think
of applications that run locally at the office but are available as remote apps
when working from home. This creates a balance between ease of use and security.
This context-sensitive approach is sorely needed. Cybercriminals are
increasingly targeting endpoints and user accounts, where traditional perimeters
fall short.
Many organizations still run critical systems on-premises, while at the same
time wanting to use cloud applications. As a result, traditional management with
domains and Group Policy Objects (GPOs) is slowly disappearing. Microsoft Intune
offers an alternative, but in practice, it is less streamlined. “What you used
to manage centrally with GPOs now has to be set up in different places in
Intune,” explains Van Wingerden. ... A hybrid model inevitably involves
more complex budgeting. Costs for virtual machines, storage, or licenses only
become apparent over time, which means financial surprises are lurking.
Technical factors also play a role. Some applications perform better locally due
to latency or regulations, while others benefit from cloud scalability. The
result? ... The traditional closed workplace no longer suffices in this new
landscape. Zero Trust is becoming the starting point, with dynamic verification
per user and context. “We can say: based on the user’s context, we make things
possible or impossible within that Windows workplace,” says Van Wingerden. Think
of applications that run locally at the office but are available as remote apps
when working from home. This creates a balance between ease of use and security.
This context-sensitive approach is sorely needed. Cybercriminals are
increasingly targeting endpoints and user accounts, where traditional perimeters
fall short.
Cisco Firewall Zero-Days Exploited in China-Linked ArcaneDoor Attacks
 “Attackers were observed to have exploited multiple zero-day vulnerabilities and
employed advanced evasion techniques such as disabling logging, intercepting CLI
commands, and intentionally crashing devices to prevent diagnostic analysis,”
Cisco explains. While it has yet to be confirmed by the wider cybersecurity
community, there is some evidence suggesting that the hackers behind the
ArcaneDoor campaign are based in China. ... Users are advised to update their
devices as soon as possible, as the fixed release will automatically check the
ROM and remove the attackers’ persistence mechanism. Users are also advised to
rotate all passwords, certificates, and keys following the update. “In cases of
suspected or confirmed compromise on any Cisco firewall device, all
configuration elements of the device should be considered untrusted,” Cisco
notes. The company also released a detection guide to help organizations hunt
for potential compromise associated with the ArcaneDoor campaign. ... An
attacker could exploit this vulnerability by sending crafted HTTP requests to a
targeted web service on an affected device after obtaining additional
information about the system, overcoming exploit mitigations, or both. A
successful exploit could allow the attacker to execute arbitrary code as root,
which may lead to the complete compromise of the affected device,” the company
notes.
“Attackers were observed to have exploited multiple zero-day vulnerabilities and
employed advanced evasion techniques such as disabling logging, intercepting CLI
commands, and intentionally crashing devices to prevent diagnostic analysis,”
Cisco explains. While it has yet to be confirmed by the wider cybersecurity
community, there is some evidence suggesting that the hackers behind the
ArcaneDoor campaign are based in China. ... Users are advised to update their
devices as soon as possible, as the fixed release will automatically check the
ROM and remove the attackers’ persistence mechanism. Users are also advised to
rotate all passwords, certificates, and keys following the update. “In cases of
suspected or confirmed compromise on any Cisco firewall device, all
configuration elements of the device should be considered untrusted,” Cisco
notes. The company also released a detection guide to help organizations hunt
for potential compromise associated with the ArcaneDoor campaign. ... An
attacker could exploit this vulnerability by sending crafted HTTP requests to a
targeted web service on an affected device after obtaining additional
information about the system, overcoming exploit mitigations, or both. A
successful exploit could allow the attacker to execute arbitrary code as root,
which may lead to the complete compromise of the affected device,” the company
notes.
5 ways you can maximize AI's big impact in software development
 Tony Phillips, engineering lead for DevOps services at Lloyds Banking Group,
said his firm is running a program called Platform 3.0, which aims to modernize
infrastructure and lay the groundwork for adopting AI. He said the next step is
to move beyond using AI to assist with coding and to boost all areas of the
development process. "We are creating productivity boosts in our developer
community, but we are now looking at how we take that forward across the rest of
the pipeline for what we ship." ... He said the bank's initial explorations into
AI suggest that learning from experiences is an important best practice.
"There's always a balance, because you've got to let people get hold of the
technology, put it in their context of what they're doing, and then understand
what good looks like," he said. "Then you've got to build the capacity for what
gets fed back so that you can respond quickly." ... Like others, Terry said
governance is crucial. Give developers feedback when they take non-compliant
actions -- and AI might help with this process. "We have a lot of different
platforms and maybe haven't created a dotted line between all the platforms," he
said. "AI might be the opportunity to do that and give developers the chance to
do the right thing from the beginning." ... Terry also referred to the rise
of vibe coding and suggested it shouldn't be used by people who have just begun
coding in an enterprise setting.
Tony Phillips, engineering lead for DevOps services at Lloyds Banking Group,
said his firm is running a program called Platform 3.0, which aims to modernize
infrastructure and lay the groundwork for adopting AI. He said the next step is
to move beyond using AI to assist with coding and to boost all areas of the
development process. "We are creating productivity boosts in our developer
community, but we are now looking at how we take that forward across the rest of
the pipeline for what we ship." ... He said the bank's initial explorations into
AI suggest that learning from experiences is an important best practice.
"There's always a balance, because you've got to let people get hold of the
technology, put it in their context of what they're doing, and then understand
what good looks like," he said. "Then you've got to build the capacity for what
gets fed back so that you can respond quickly." ... Like others, Terry said
governance is crucial. Give developers feedback when they take non-compliant
actions -- and AI might help with this process. "We have a lot of different
platforms and maybe haven't created a dotted line between all the platforms," he
said. "AI might be the opportunity to do that and give developers the chance to
do the right thing from the beginning." ... Terry also referred to the rise
of vibe coding and suggested it shouldn't be used by people who have just begun
coding in an enterprise setting.
Ethical cybersecurity practice reshapes enterprise security in 2025
The tension between innovation and risk management represents an important challenge for modern organisations. Push too hard for innovation without adequate safeguards and companies risk data breaches and compliance violations. Focus too heavily on risk mitigation, and organisations may find themselves unable to compete in evolving markets. ... The ethical AI component emphasises explainability. Rather than generating “black box” alerts, ManageEngine’s systems explain their reasoning. An alert might read: “The endpoint cannot log in at this time and is trying to connect to too many network devices.” ... The balance between necessary security monitoring and privacy invasion represents one of the most delicate aspects of ethical cybersecurity practices. Raymond acknowledges that while proactive monitoring is essential for detecting threats early, over-monitoring risks creating a surveillance environment that treats employees as suspects rather than trusted partners. ... For organisations seeking to integrate ethical considerations into their cybersecurity strategies, Raymond recommends three concrete steps: adopting a cybersecurity ethics charter at the board level, embedding privacy and ethics in technology decisions when selecting vendors, and operationalising ethics through comprehensive training and controls that explain not just what to do, but why it matters.What is infrastructure as code? Automating your infrastructure builds
 Infrastructure as code is a practice of writing plain-text declarative
configuration files that automated tools use to manage and provision servers and
other computing resources. In the pre-cloud days, sysadmins would often
customize the configuration of individual on-premises server systems; but as
more and more organizations move to the cloud, those skills became less relevant
and useful. ... and Puppet founder Luke Kanies started to use the terminology.
In a world of distributed applications, hand-tuning servers was never going to
scale, and scripting had its own limitations, so being able to automate
infrastructure provisioning became a core need for many first movers back in the
early days of cloud. Today, that underlying infrastructure is more commonly
provisioned as code, thanks to popular early tools in this space such as Chef,
Puppet, SaltStack, and Ansible. ... But the neat boundaries between tools and
platforms have blurred, and many enterprises no longer rely on a single IaC
solution, but instead juggle multiple tools across different teams or cloud
providers. For example, Terraform or OpenTofu may provision baseline resources,
while Ansible handles configuration management, and Kubernetes-native frameworks
like Crossplane provide a higher layer of abstraction. This “multi-IaC” reality
introduces new challenges in governance, dependency management, and avoiding
configuration drift.
Infrastructure as code is a practice of writing plain-text declarative
configuration files that automated tools use to manage and provision servers and
other computing resources. In the pre-cloud days, sysadmins would often
customize the configuration of individual on-premises server systems; but as
more and more organizations move to the cloud, those skills became less relevant
and useful. ... and Puppet founder Luke Kanies started to use the terminology.
In a world of distributed applications, hand-tuning servers was never going to
scale, and scripting had its own limitations, so being able to automate
infrastructure provisioning became a core need for many first movers back in the
early days of cloud. Today, that underlying infrastructure is more commonly
provisioned as code, thanks to popular early tools in this space such as Chef,
Puppet, SaltStack, and Ansible. ... But the neat boundaries between tools and
platforms have blurred, and many enterprises no longer rely on a single IaC
solution, but instead juggle multiple tools across different teams or cloud
providers. For example, Terraform or OpenTofu may provision baseline resources,
while Ansible handles configuration management, and Kubernetes-native frameworks
like Crossplane provide a higher layer of abstraction. This “multi-IaC” reality
introduces new challenges in governance, dependency management, and avoiding
configuration drift.















/articles/fitness-functions-architecture/en/smallimage/fitness-functions-architecture-thumbnail-1744359549803.jpg)




_Borka_Kiss_Alamy.jpg?width=1280&auto=webp&quality=95&format=jpg&disable=upscale)


/pcq/media/media_files/2025/03/28/FMHV44KuuMhvUZSHNwsy.webp)