Quote for the day:
"Stories are the single most powerful weapon in a leader's arsenal." -- Howard Gardner
AI ambitions collide with legacy integration problems
 Many enterprises have moved beyond experimentation and are preparing for
formal deployment. The survey found that 85% have begun adopting AI or expect
to do so within the next 12 months. Respondents also reported efforts to
formalise AI governance, reflecting greater attention to risk, accountability
and oversight. ... Integration sits at the centre of that tension. AI
initiatives often depend on clean data, consistent definitions and reliable
access across multiple applications, requirements that legacy estates can
complicate. The survey links these constraints to compliance risks, including
data retention, access controls and auditability across connected systems. ...
Security and privacy concerns featured prominently. Data privacy across
systems was cited as a top risk by 49% of respondents, while 48% said they
were concerned about third parties handling sensitive data. The results
highlight the difficulty of managing information flows when AI systems
interact with multiple internal applications and external providers.
Governance approaches varied. Fewer than half (47%) said board-level reporting
forms part of risk management for AI and related technology work, suggesting
uneven executive oversight as AI moves into operational settings where
incidents can carry regulatory and reputational consequences. ... Despite
pressure to move quickly on AI initiatives, respondents said engineering
quality remains a priority.
Many enterprises have moved beyond experimentation and are preparing for
formal deployment. The survey found that 85% have begun adopting AI or expect
to do so within the next 12 months. Respondents also reported efforts to
formalise AI governance, reflecting greater attention to risk, accountability
and oversight. ... Integration sits at the centre of that tension. AI
initiatives often depend on clean data, consistent definitions and reliable
access across multiple applications, requirements that legacy estates can
complicate. The survey links these constraints to compliance risks, including
data retention, access controls and auditability across connected systems. ...
Security and privacy concerns featured prominently. Data privacy across
systems was cited as a top risk by 49% of respondents, while 48% said they
were concerned about third parties handling sensitive data. The results
highlight the difficulty of managing information flows when AI systems
interact with multiple internal applications and external providers.
Governance approaches varied. Fewer than half (47%) said board-level reporting
forms part of risk management for AI and related technology work, suggesting
uneven executive oversight as AI moves into operational settings where
incidents can carry regulatory and reputational consequences. ... Despite
pressure to move quickly on AI initiatives, respondents said engineering
quality remains a priority. Striking the Right Balance Between Automation and Manual Processes in IT
Rather than thinking of applying AI wherever possible and over-automating,
leaders should think about the most beneficial uses of the technology and
begin implementation of the technology in those areas first before expanding
further. Automation is a powerful tool, but humans are the most powerful tool
in the IT stack. Let’s discuss how today’s IT leaders can strike the right
balance between automation and manual processes. ... Even with the many
benefits of automation, human-led processes still reign supreme in certain
areas. For example, optimal IT operations happen at the intersection of tools
and teamwork. IT teams must still foster a collaborative culture, working with
other departments to ensure cross team visibility and alignment on business
goals. While the latest AI technology can help in these efforts, ultimately,
humans must do this collaborative work. Team dynamics can also be complex at
times. Conflict resolution and major team decisions are not things that
automation can solve. Moreover, if there is a critical system issue, DBAs must
be able to work with IT leaders to resolve this issue and forge a path
forward. Finally, manual processes are often necessitated by convoluted
workflows. Many DBA teams have workflows in which every step is a set of
if-then-else decisions, with each possible outcome also encumbered with many
if-then decisions cascading through multiple levels of decisions.
 The fundamental challenge in demonstrating data science ROI is that most
analytics infrastructure feels optional until it becomes essential. During
normal operations, executives tolerate delays in reporting and gaps in
visibility. During a crisis, those same gaps become existential threats. ...
The turning point came when I realized we weren’t facing a data problem or a
technology problem. We were facing a decision-making problem. Our leadership
needed to maintain operational stability for a multi-trillion-dollar asset
manager during unprecedented disruption. Every day without visibility meant
delayed decisions, missed opportunities, and compounding uncertainty. ...
Speed-to-value often trumps technical sophistication. The COVID dashboard
taught me this lesson definitively. We could have spent months building a
comprehensive data warehouse with sophisticated ETL pipelines and machine
learning-powered forecasting. Instead, we focused ruthlessly on the minimum
viable solution that executives needed immediately. ... Strategic
positioning creates a disproportionate impact. I served as strategic
architect for a major product repositioning — a multi-million-dollar
initiative essential for our competitive positioning. My data-backed
strategies produced immediate, quantifiable market share gains and resulted
in substantially larger deal sizes and accelerated acquisition rates that
fundamentally altered our market position.
The fundamental challenge in demonstrating data science ROI is that most
analytics infrastructure feels optional until it becomes essential. During
normal operations, executives tolerate delays in reporting and gaps in
visibility. During a crisis, those same gaps become existential threats. ...
The turning point came when I realized we weren’t facing a data problem or a
technology problem. We were facing a decision-making problem. Our leadership
needed to maintain operational stability for a multi-trillion-dollar asset
manager during unprecedented disruption. Every day without visibility meant
delayed decisions, missed opportunities, and compounding uncertainty. ...
Speed-to-value often trumps technical sophistication. The COVID dashboard
taught me this lesson definitively. We could have spent months building a
comprehensive data warehouse with sophisticated ETL pipelines and machine
learning-powered forecasting. Instead, we focused ruthlessly on the minimum
viable solution that executives needed immediately. ... Strategic
positioning creates a disproportionate impact. I served as strategic
architect for a major product repositioning — a multi-million-dollar
initiative essential for our competitive positioning. My data-backed
strategies produced immediate, quantifiable market share gains and resulted
in substantially larger deal sizes and accelerated acquisition rates that
fundamentally altered our market position.
 Many widely used libraries and systems default to infinite or extremely
large timeouts. In Java, common HTTP clients treat a timeout of zero as
“wait indefinitely” unless explicitly configured. In Python, requests will
wait indefinitely unless a timeout is set explicitly. The Fetch API does not
define a built-in timeout at all. These defaults aren’t careless. They’re
intentionally generic. Libraries optimize for the correctness of a single
request because they can’t know what “too slow” means for your system.
Survivability under partial failure is left to the application. ... Long
timeouts can also mask deeper design problems. If a request regularly times
out because it returns thousands of items, the issue isn’t the timeout
itself. It’s missing pagination or poor request shaping. By optimizing for
individual request success, teams unintentionally trade away system-level
resilience. ... A timeout defines where a failure is allowed to stop.
Without timeouts, a single slow dependency can quietly consume threads,
connections and memory across the system. With well-chosen timeouts,
slowness stays contained instead of spreading into a system-wide failure.
... A timeout is a decision about value. Past a certain point, waiting
longer does not improve user experience. It increases the amount of wasted
work a system performs after the user has already left. A timeout is also a
decision about containment. Without bounded waits, partial failures turn
into system-wide failures through resource exhaustion: blocked threads,
saturated pools, growing queues and cascading latency.
Many widely used libraries and systems default to infinite or extremely
large timeouts. In Java, common HTTP clients treat a timeout of zero as
“wait indefinitely” unless explicitly configured. In Python, requests will
wait indefinitely unless a timeout is set explicitly. The Fetch API does not
define a built-in timeout at all. These defaults aren’t careless. They’re
intentionally generic. Libraries optimize for the correctness of a single
request because they can’t know what “too slow” means for your system.
Survivability under partial failure is left to the application. ... Long
timeouts can also mask deeper design problems. If a request regularly times
out because it returns thousands of items, the issue isn’t the timeout
itself. It’s missing pagination or poor request shaping. By optimizing for
individual request success, teams unintentionally trade away system-level
resilience. ... A timeout defines where a failure is allowed to stop.
Without timeouts, a single slow dependency can quietly consume threads,
connections and memory across the system. With well-chosen timeouts,
slowness stays contained instead of spreading into a system-wide failure.
... A timeout is a decision about value. Past a certain point, waiting
longer does not improve user experience. It increases the amount of wasted
work a system performs after the user has already left. A timeout is also a
decision about containment. Without bounded waits, partial failures turn
into system-wide failures through resource exhaustion: blocked threads,
saturated pools, growing queues and cascading latency.
 For years, the standard for vertical software has been the nightly sync. You
collect data all day, run a massive batch job at 2:00 AM, and provide your
customers with a clean report the next morning. In a world of 2026, that
delay is becoming a liability rather than a best practice. ... Data
streaming isn’t just about moving bits faster; it’s about changing the
fundamental value proposition of your application. Instead of being a system
of record that tells a user what happened, your software becomes a system of
agency that tells them what is happening right now. This shift requires a
mental move away from static databases toward event-driven architectures.
You’re no longer just storing a “state” (like current inventory); you’re
capturing every “event” (every scan, every sale, every sensor ping) that
leads to that state. ... One of the biggest mistakes I see software leaders
make is treating real-time data as a “table stakes” feature that they give
away for free. Streaming infrastructure is expensive to run and even more
expensive to maintain. If you bake these costs into your standard
subscription without a clear monetization strategy, you’ll watch your gross
margins shrink as your customers’ data volumes grow. ... When you process
data at the edge, you’re also solving the “data gravity” problem. Sending
thousands of high-frequency sensor pings from a factory floor to the cloud
just to filter out the noise is a waste of bandwidth and money.
For years, the standard for vertical software has been the nightly sync. You
collect data all day, run a massive batch job at 2:00 AM, and provide your
customers with a clean report the next morning. In a world of 2026, that
delay is becoming a liability rather than a best practice. ... Data
streaming isn’t just about moving bits faster; it’s about changing the
fundamental value proposition of your application. Instead of being a system
of record that tells a user what happened, your software becomes a system of
agency that tells them what is happening right now. This shift requires a
mental move away from static databases toward event-driven architectures.
You’re no longer just storing a “state” (like current inventory); you’re
capturing every “event” (every scan, every sale, every sensor ping) that
leads to that state. ... One of the biggest mistakes I see software leaders
make is treating real-time data as a “table stakes” feature that they give
away for free. Streaming infrastructure is expensive to run and even more
expensive to maintain. If you bake these costs into your standard
subscription without a clear monetization strategy, you’ll watch your gross
margins shrink as your customers’ data volumes grow. ... When you process
data at the edge, you’re also solving the “data gravity” problem. Sending
thousands of high-frequency sensor pings from a factory floor to the cloud
just to filter out the noise is a waste of bandwidth and money.
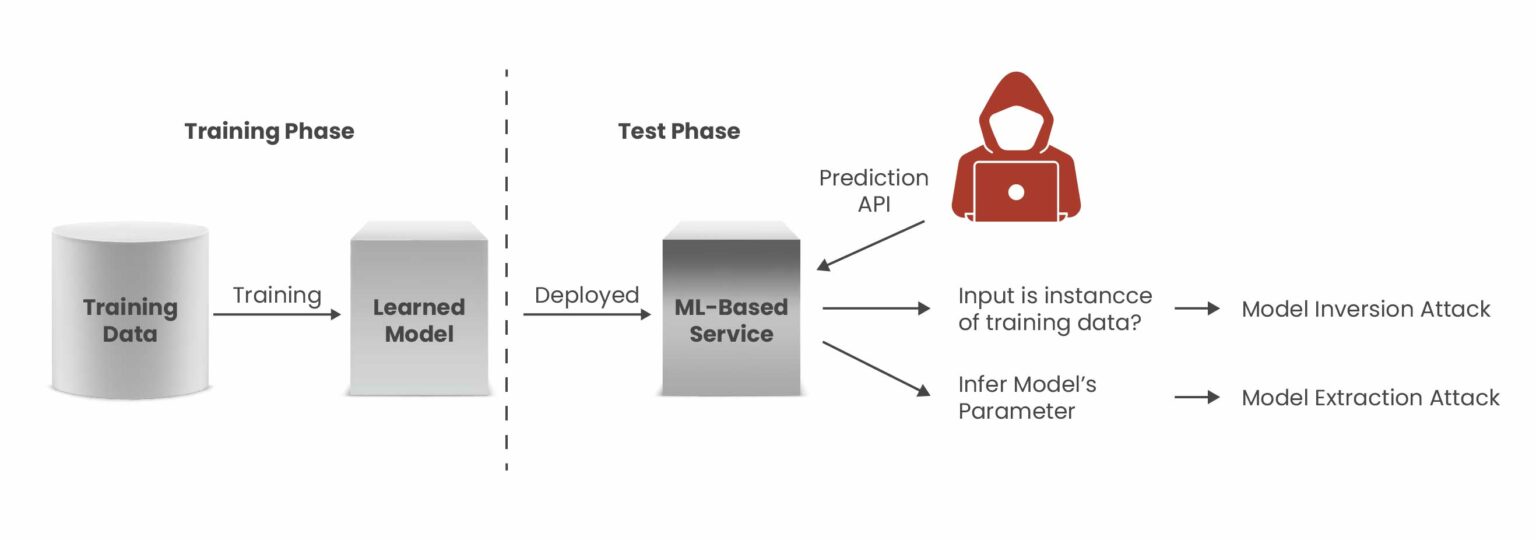
 From a data privacy standpoint, one of the major issues is data leakage,
while from a security perspective, there are several things that may cause
issues, including prompt injections, difficulty in distinguishing between
verified and unverified servers, and the fact that MCP servers sit below
typical security controls. ... Fulkerson went on to say that runtime
execution is another issue, and legacy tools for enforcing policies and
privacy are static and don’t get enforced at runtime. When you’re dealing
with non-deterministic systems, there needs to be a way to verifiably
enforce policies at runtime execution because the blast radius of runtime
data access has outgrown the protection mechanisms organizations have. He
believes that confidential AI is the solution to these problems.
Confidential AI builds on the properties of confidential computing, which
involves using hardware that has an encrypted cache, allowing data and
inference to be run inside an encrypted environment. While this helps prove
that data is encrypted and nobody can see it, it doesn’t help with the
governance challenge, which is where Fulkerson says confidential AI comes
in. Confidential AI treats everything as a resource with its own set of
policies that are cryptographically encoded. For example, you could limit an
agent to only be able to talk to a specific agent, or only allow it to
communicate with resources on a particular subnet.
From a data privacy standpoint, one of the major issues is data leakage,
while from a security perspective, there are several things that may cause
issues, including prompt injections, difficulty in distinguishing between
verified and unverified servers, and the fact that MCP servers sit below
typical security controls. ... Fulkerson went on to say that runtime
execution is another issue, and legacy tools for enforcing policies and
privacy are static and don’t get enforced at runtime. When you’re dealing
with non-deterministic systems, there needs to be a way to verifiably
enforce policies at runtime execution because the blast radius of runtime
data access has outgrown the protection mechanisms organizations have. He
believes that confidential AI is the solution to these problems.
Confidential AI builds on the properties of confidential computing, which
involves using hardware that has an encrypted cache, allowing data and
inference to be run inside an encrypted environment. While this helps prove
that data is encrypted and nobody can see it, it doesn’t help with the
governance challenge, which is where Fulkerson says confidential AI comes
in. Confidential AI treats everything as a resource with its own set of
policies that are cryptographically encoded. For example, you could limit an
agent to only be able to talk to a specific agent, or only allow it to
communicate with resources on a particular subnet.
 Increasingly, energy providers are turning to digital twins to model and
simulate critical infrastructure across generation, transmission and
distribution environments. By feeding live telemetry from supervisory control
and data acquisition systems, intelligent electronic devices and other OT
assets into IT-based simulation platforms, utilities can create real-time
digital replicas of substations, turbines, transformers and even entire grid
segments. This enables teams to test load-balancing strategies, maintenance
schedules or DER integrations without disrupting service. ... Private 5G
networks offer a compelling alternative. Designed for high reliability and low
latency, private 5G can operate effectively in interference-heavy environments
such as substations or generation facilities. When paired with TSN, utilities
can achieve deterministic, sub-millisecond communication between protection
systems, controllers and analytics platforms. ... Federated machine learning
allows utilities to train AI models locally at the edge — analyzing equipment
performance, detecting anomalies and refining predictive maintenance
strategies — without centralizing raw operational data. For industries such as
energy and oil, remote sites can run local anomaly detection models tailored
to site-specific conditions, while still sharing insights that strengthen
enterprisewide safety and operational protocols.
Increasingly, energy providers are turning to digital twins to model and
simulate critical infrastructure across generation, transmission and
distribution environments. By feeding live telemetry from supervisory control
and data acquisition systems, intelligent electronic devices and other OT
assets into IT-based simulation platforms, utilities can create real-time
digital replicas of substations, turbines, transformers and even entire grid
segments. This enables teams to test load-balancing strategies, maintenance
schedules or DER integrations without disrupting service. ... Private 5G
networks offer a compelling alternative. Designed for high reliability and low
latency, private 5G can operate effectively in interference-heavy environments
such as substations or generation facilities. When paired with TSN, utilities
can achieve deterministic, sub-millisecond communication between protection
systems, controllers and analytics platforms. ... Federated machine learning
allows utilities to train AI models locally at the edge — analyzing equipment
performance, detecting anomalies and refining predictive maintenance
strategies — without centralizing raw operational data. For industries such as
energy and oil, remote sites can run local anomaly detection models tailored
to site-specific conditions, while still sharing insights that strengthen
enterprisewide safety and operational protocols.
 It’s now happening all the time: in the sale of location data and browsing
histories to brokers who assemble and sell our highly personal profiles, and
in DOGE’s and other data grabs across the federal government, where housing,
tax, and health information is being weaponized for immigration enforcement or
misleading voter fraud “investigations.” With AI agents, it just gets worse.
Data betrayal is an even more intimate act. Yet the people who granted
OpenClaw access to their accounts were making a reasonable choice—to use a
powerful tool on their behalf. ... The data aggregation capabilities of AI add
another dimension of risk that rarely gets even a mention, but represent a
change in scale that adds up to a sea change, making someone marketed as
“productivity” software a menacing vector for data weaponization. The same
capabilities that make agents useful—synthesizing enormous amounts of
information across sources and acting autonomously across platforms with
persistence and memory—make them extraordinarily powerful instruments for
state surveillance and targeted repression. An autocratic government could
build dossiers on dissidents, journalists, or voters from financial records,
social media, location data, and communications metadata, acting in real time:
micro-targeting people with persuasion campaigns, swarming targets with
coordinated social media attacks, engineering entrapment schemes, or flagging
individuals based on patterns no court ever authorized.
It’s now happening all the time: in the sale of location data and browsing
histories to brokers who assemble and sell our highly personal profiles, and
in DOGE’s and other data grabs across the federal government, where housing,
tax, and health information is being weaponized for immigration enforcement or
misleading voter fraud “investigations.” With AI agents, it just gets worse.
Data betrayal is an even more intimate act. Yet the people who granted
OpenClaw access to their accounts were making a reasonable choice—to use a
powerful tool on their behalf. ... The data aggregation capabilities of AI add
another dimension of risk that rarely gets even a mention, but represent a
change in scale that adds up to a sea change, making someone marketed as
“productivity” software a menacing vector for data weaponization. The same
capabilities that make agents useful—synthesizing enormous amounts of
information across sources and acting autonomously across platforms with
persistence and memory—make them extraordinarily powerful instruments for
state surveillance and targeted repression. An autocratic government could
build dossiers on dissidents, journalists, or voters from financial records,
social media, location data, and communications metadata, acting in real time:
micro-targeting people with persuasion campaigns, swarming targets with
coordinated social media attacks, engineering entrapment schemes, or flagging
individuals based on patterns no court ever authorized.
Translating data science capabilities into business ROI
 The fundamental challenge in demonstrating data science ROI is that most
analytics infrastructure feels optional until it becomes essential. During
normal operations, executives tolerate delays in reporting and gaps in
visibility. During a crisis, those same gaps become existential threats. ...
The turning point came when I realized we weren’t facing a data problem or a
technology problem. We were facing a decision-making problem. Our leadership
needed to maintain operational stability for a multi-trillion-dollar asset
manager during unprecedented disruption. Every day without visibility meant
delayed decisions, missed opportunities, and compounding uncertainty. ...
Speed-to-value often trumps technical sophistication. The COVID dashboard
taught me this lesson definitively. We could have spent months building a
comprehensive data warehouse with sophisticated ETL pipelines and machine
learning-powered forecasting. Instead, we focused ruthlessly on the minimum
viable solution that executives needed immediately. ... Strategic
positioning creates a disproportionate impact. I served as strategic
architect for a major product repositioning — a multi-million-dollar
initiative essential for our competitive positioning. My data-backed
strategies produced immediate, quantifiable market share gains and resulted
in substantially larger deal sizes and accelerated acquisition rates that
fundamentally altered our market position.
The fundamental challenge in demonstrating data science ROI is that most
analytics infrastructure feels optional until it becomes essential. During
normal operations, executives tolerate delays in reporting and gaps in
visibility. During a crisis, those same gaps become existential threats. ...
The turning point came when I realized we weren’t facing a data problem or a
technology problem. We were facing a decision-making problem. Our leadership
needed to maintain operational stability for a multi-trillion-dollar asset
manager during unprecedented disruption. Every day without visibility meant
delayed decisions, missed opportunities, and compounding uncertainty. ...
Speed-to-value often trumps technical sophistication. The COVID dashboard
taught me this lesson definitively. We could have spent months building a
comprehensive data warehouse with sophisticated ETL pipelines and machine
learning-powered forecasting. Instead, we focused ruthlessly on the minimum
viable solution that executives needed immediately. ... Strategic
positioning creates a disproportionate impact. I served as strategic
architect for a major product repositioning — a multi-million-dollar
initiative essential for our competitive positioning. My data-backed
strategies produced immediate, quantifiable market share gains and resulted
in substantially larger deal sizes and accelerated acquisition rates that
fundamentally altered our market position.The reliability cost of default timeouts
 Many widely used libraries and systems default to infinite or extremely
large timeouts. In Java, common HTTP clients treat a timeout of zero as
“wait indefinitely” unless explicitly configured. In Python, requests will
wait indefinitely unless a timeout is set explicitly. The Fetch API does not
define a built-in timeout at all. These defaults aren’t careless. They’re
intentionally generic. Libraries optimize for the correctness of a single
request because they can’t know what “too slow” means for your system.
Survivability under partial failure is left to the application. ... Long
timeouts can also mask deeper design problems. If a request regularly times
out because it returns thousands of items, the issue isn’t the timeout
itself. It’s missing pagination or poor request shaping. By optimizing for
individual request success, teams unintentionally trade away system-level
resilience. ... A timeout defines where a failure is allowed to stop.
Without timeouts, a single slow dependency can quietly consume threads,
connections and memory across the system. With well-chosen timeouts,
slowness stays contained instead of spreading into a system-wide failure.
... A timeout is a decision about value. Past a certain point, waiting
longer does not improve user experience. It increases the amount of wasted
work a system performs after the user has already left. A timeout is also a
decision about containment. Without bounded waits, partial failures turn
into system-wide failures through resource exhaustion: blocked threads,
saturated pools, growing queues and cascading latency.
Many widely used libraries and systems default to infinite or extremely
large timeouts. In Java, common HTTP clients treat a timeout of zero as
“wait indefinitely” unless explicitly configured. In Python, requests will
wait indefinitely unless a timeout is set explicitly. The Fetch API does not
define a built-in timeout at all. These defaults aren’t careless. They’re
intentionally generic. Libraries optimize for the correctness of a single
request because they can’t know what “too slow” means for your system.
Survivability under partial failure is left to the application. ... Long
timeouts can also mask deeper design problems. If a request regularly times
out because it returns thousands of items, the issue isn’t the timeout
itself. It’s missing pagination or poor request shaping. By optimizing for
individual request success, teams unintentionally trade away system-level
resilience. ... A timeout defines where a failure is allowed to stop.
Without timeouts, a single slow dependency can quietly consume threads,
connections and memory across the system. With well-chosen timeouts,
slowness stays contained instead of spreading into a system-wide failure.
... A timeout is a decision about value. Past a certain point, waiting
longer does not improve user experience. It increases the amount of wasted
work a system performs after the user has already left. A timeout is also a
decision about containment. Without bounded waits, partial failures turn
into system-wide failures through resource exhaustion: blocked threads,
saturated pools, growing queues and cascading latency.From dashboards to decisions: How streaming data transforms vertical software
 For years, the standard for vertical software has been the nightly sync. You
collect data all day, run a massive batch job at 2:00 AM, and provide your
customers with a clean report the next morning. In a world of 2026, that
delay is becoming a liability rather than a best practice. ... Data
streaming isn’t just about moving bits faster; it’s about changing the
fundamental value proposition of your application. Instead of being a system
of record that tells a user what happened, your software becomes a system of
agency that tells them what is happening right now. This shift requires a
mental move away from static databases toward event-driven architectures.
You’re no longer just storing a “state” (like current inventory); you’re
capturing every “event” (every scan, every sale, every sensor ping) that
leads to that state. ... One of the biggest mistakes I see software leaders
make is treating real-time data as a “table stakes” feature that they give
away for free. Streaming infrastructure is expensive to run and even more
expensive to maintain. If you bake these costs into your standard
subscription without a clear monetization strategy, you’ll watch your gross
margins shrink as your customers’ data volumes grow. ... When you process
data at the edge, you’re also solving the “data gravity” problem. Sending
thousands of high-frequency sensor pings from a factory floor to the cloud
just to filter out the noise is a waste of bandwidth and money.
For years, the standard for vertical software has been the nightly sync. You
collect data all day, run a massive batch job at 2:00 AM, and provide your
customers with a clean report the next morning. In a world of 2026, that
delay is becoming a liability rather than a best practice. ... Data
streaming isn’t just about moving bits faster; it’s about changing the
fundamental value proposition of your application. Instead of being a system
of record that tells a user what happened, your software becomes a system of
agency that tells them what is happening right now. This shift requires a
mental move away from static databases toward event-driven architectures.
You’re no longer just storing a “state” (like current inventory); you’re
capturing every “event” (every scan, every sale, every sensor ping) that
leads to that state. ... One of the biggest mistakes I see software leaders
make is treating real-time data as a “table stakes” feature that they give
away for free. Streaming infrastructure is expensive to run and even more
expensive to maintain. If you bake these costs into your standard
subscription without a clear monetization strategy, you’ll watch your gross
margins shrink as your customers’ data volumes grow. ... When you process
data at the edge, you’re also solving the “data gravity” problem. Sending
thousands of high-frequency sensor pings from a factory floor to the cloud
just to filter out the noise is a waste of bandwidth and money.MCP leaves much to be desired when it comes to data privacy and security
 From a data privacy standpoint, one of the major issues is data leakage,
while from a security perspective, there are several things that may cause
issues, including prompt injections, difficulty in distinguishing between
verified and unverified servers, and the fact that MCP servers sit below
typical security controls. ... Fulkerson went on to say that runtime
execution is another issue, and legacy tools for enforcing policies and
privacy are static and don’t get enforced at runtime. When you’re dealing
with non-deterministic systems, there needs to be a way to verifiably
enforce policies at runtime execution because the blast radius of runtime
data access has outgrown the protection mechanisms organizations have. He
believes that confidential AI is the solution to these problems.
Confidential AI builds on the properties of confidential computing, which
involves using hardware that has an encrypted cache, allowing data and
inference to be run inside an encrypted environment. While this helps prove
that data is encrypted and nobody can see it, it doesn’t help with the
governance challenge, which is where Fulkerson says confidential AI comes
in. Confidential AI treats everything as a resource with its own set of
policies that are cryptographically encoded. For example, you could limit an
agent to only be able to talk to a specific agent, or only allow it to
communicate with resources on a particular subnet.
From a data privacy standpoint, one of the major issues is data leakage,
while from a security perspective, there are several things that may cause
issues, including prompt injections, difficulty in distinguishing between
verified and unverified servers, and the fact that MCP servers sit below
typical security controls. ... Fulkerson went on to say that runtime
execution is another issue, and legacy tools for enforcing policies and
privacy are static and don’t get enforced at runtime. When you’re dealing
with non-deterministic systems, there needs to be a way to verifiably
enforce policies at runtime execution because the blast radius of runtime
data access has outgrown the protection mechanisms organizations have. He
believes that confidential AI is the solution to these problems.
Confidential AI builds on the properties of confidential computing, which
involves using hardware that has an encrypted cache, allowing data and
inference to be run inside an encrypted environment. While this helps prove
that data is encrypted and nobody can see it, it doesn’t help with the
governance challenge, which is where Fulkerson says confidential AI comes
in. Confidential AI treats everything as a resource with its own set of
policies that are cryptographically encoded. For example, you could limit an
agent to only be able to talk to a specific agent, or only allow it to
communicate with resources on a particular subnet.3 Ways OT-IT Integration Helps Energy and Utilities Providers Modernize Grid Operations
 Increasingly, energy providers are turning to digital twins to model and
simulate critical infrastructure across generation, transmission and
distribution environments. By feeding live telemetry from supervisory control
and data acquisition systems, intelligent electronic devices and other OT
assets into IT-based simulation platforms, utilities can create real-time
digital replicas of substations, turbines, transformers and even entire grid
segments. This enables teams to test load-balancing strategies, maintenance
schedules or DER integrations without disrupting service. ... Private 5G
networks offer a compelling alternative. Designed for high reliability and low
latency, private 5G can operate effectively in interference-heavy environments
such as substations or generation facilities. When paired with TSN, utilities
can achieve deterministic, sub-millisecond communication between protection
systems, controllers and analytics platforms. ... Federated machine learning
allows utilities to train AI models locally at the edge — analyzing equipment
performance, detecting anomalies and refining predictive maintenance
strategies — without centralizing raw operational data. For industries such as
energy and oil, remote sites can run local anomaly detection models tailored
to site-specific conditions, while still sharing insights that strengthen
enterprisewide safety and operational protocols.
Increasingly, energy providers are turning to digital twins to model and
simulate critical infrastructure across generation, transmission and
distribution environments. By feeding live telemetry from supervisory control
and data acquisition systems, intelligent electronic devices and other OT
assets into IT-based simulation platforms, utilities can create real-time
digital replicas of substations, turbines, transformers and even entire grid
segments. This enables teams to test load-balancing strategies, maintenance
schedules or DER integrations without disrupting service. ... Private 5G
networks offer a compelling alternative. Designed for high reliability and low
latency, private 5G can operate effectively in interference-heavy environments
such as substations or generation facilities. When paired with TSN, utilities
can achieve deterministic, sub-millisecond communication between protection
systems, controllers and analytics platforms. ... Federated machine learning
allows utilities to train AI models locally at the edge — analyzing equipment
performance, detecting anomalies and refining predictive maintenance
strategies — without centralizing raw operational data. For industries such as
energy and oil, remote sites can run local anomaly detection models tailored
to site-specific conditions, while still sharing insights that strengthen
enterprisewide safety and operational protocols.Even if AI demand fades, India need not worry - about data centres
AI pushes rack densities from ~5–10kW to 50–100kW+, making liquid cooling, greater power capacity, and purpose‑built ‘AI‑ready’ Data Centre campuses essential — whether for regional training clusters or dense inference. What makes a Data Centre AI-ready is the ability to support advanced cooling, predictable scalability and direct access to clouds, networks and partners in a sustainable manner. ... In India, enterprises are rapidly adopting hybrid and multi-cloud architectures as they modernise their digital infrastructure. Domestic enterprises, particularly in BFSI and broking, are moving away from in-house data centres toward third-party colocation facilities to gain scalability, efficient interconnection with their required ecosystem, operational efficiency and access to specialised talent. This shift is being further accelerated by distributed AI, hybrid multi-cloud architectures and a growing focus on sustainability. ... India’s Data Centre market is distinctive because of the scale of its digital consumption, combined with the early stage of ecosystem development. India generates a significant share of global data, yet its installed data centre capacity remains comparatively low, creating strong long-term growth potential. This growth is now being amplified by hyperscalers and AI-led demand. India aims to become a USD 1 T digital economy by 2028. It is already making significant progress, supported by the country’s thriving startup ecosystem, the third largest in the world, and initiatives like Startup India.Surprise! The One Being Ripped Off by Your AI Agent Is You
 It’s now happening all the time: in the sale of location data and browsing
histories to brokers who assemble and sell our highly personal profiles, and
in DOGE’s and other data grabs across the federal government, where housing,
tax, and health information is being weaponized for immigration enforcement or
misleading voter fraud “investigations.” With AI agents, it just gets worse.
Data betrayal is an even more intimate act. Yet the people who granted
OpenClaw access to their accounts were making a reasonable choice—to use a
powerful tool on their behalf. ... The data aggregation capabilities of AI add
another dimension of risk that rarely gets even a mention, but represent a
change in scale that adds up to a sea change, making someone marketed as
“productivity” software a menacing vector for data weaponization. The same
capabilities that make agents useful—synthesizing enormous amounts of
information across sources and acting autonomously across platforms with
persistence and memory—make them extraordinarily powerful instruments for
state surveillance and targeted repression. An autocratic government could
build dossiers on dissidents, journalists, or voters from financial records,
social media, location data, and communications metadata, acting in real time:
micro-targeting people with persuasion campaigns, swarming targets with
coordinated social media attacks, engineering entrapment schemes, or flagging
individuals based on patterns no court ever authorized.
It’s now happening all the time: in the sale of location data and browsing
histories to brokers who assemble and sell our highly personal profiles, and
in DOGE’s and other data grabs across the federal government, where housing,
tax, and health information is being weaponized for immigration enforcement or
misleading voter fraud “investigations.” With AI agents, it just gets worse.
Data betrayal is an even more intimate act. Yet the people who granted
OpenClaw access to their accounts were making a reasonable choice—to use a
powerful tool on their behalf. ... The data aggregation capabilities of AI add
another dimension of risk that rarely gets even a mention, but represent a
change in scale that adds up to a sea change, making someone marketed as
“productivity” software a menacing vector for data weaponization. The same
capabilities that make agents useful—synthesizing enormous amounts of
information across sources and acting autonomously across platforms with
persistence and memory—make them extraordinarily powerful instruments for
state surveillance and targeted repression. An autocratic government could
build dossiers on dissidents, journalists, or voters from financial records,
social media, location data, and communications metadata, acting in real time:
micro-targeting people with persuasion campaigns, swarming targets with
coordinated social media attacks, engineering entrapment schemes, or flagging
individuals based on patterns no court ever authorized.






















/articles/building-ai-agent-gateway-mcp/en/smallimage/building-ai-agent-gateway-mcp-thumbnail-1771417896950.jpg)