Quote for the day:
“To be successful you need friends and to be very successful you need enemies.” -- Sidney Sheldon
AI agents to outnumber humans, warns Token Security
 Many agents now run in controlled, non-production environments. Token Security
predicts that organisations will soon connect them directly to live systems. The
company says this will force enterprises to manage agent permissions and
lifecycle controls more actively. It also expects new processes for assigning
accountability when an autonomous system carries out an action on behalf of a
team or individual. Apelblat believes established compliance structures will not
cope with this change in the workforce. Traditional frameworks assume that
humans sit at the centre of most workflows. ... "Despite innovation in agentic
AI, enterprises will enter 2026 still relying on static API keys and long-term
credentials. These legacy mechanisms will quietly weaken agent identity
integrity, creating fragile trust chains that attackers can easily exploit,"
said Shlomo. Shlomo also predicts a reversal of some progress made in reducing
secrets stored on endpoints. Many companies have moved staff onto single sign-on
and centralised identity systems. He believes poor management of local Model
Context Protocol servers will now cause a resurgence of cleartext service
credentials on employee devices. ... "The industry is shifting from breaches
caused by human identity failures to breaches rooted in AI agent identity
compromise. As agents become operational backbones, attacks targeting their
tokens, personas, and delegated authority will define the next wave of
high-impact incidents," said Shlomo.
Many agents now run in controlled, non-production environments. Token Security
predicts that organisations will soon connect them directly to live systems. The
company says this will force enterprises to manage agent permissions and
lifecycle controls more actively. It also expects new processes for assigning
accountability when an autonomous system carries out an action on behalf of a
team or individual. Apelblat believes established compliance structures will not
cope with this change in the workforce. Traditional frameworks assume that
humans sit at the centre of most workflows. ... "Despite innovation in agentic
AI, enterprises will enter 2026 still relying on static API keys and long-term
credentials. These legacy mechanisms will quietly weaken agent identity
integrity, creating fragile trust chains that attackers can easily exploit,"
said Shlomo. Shlomo also predicts a reversal of some progress made in reducing
secrets stored on endpoints. Many companies have moved staff onto single sign-on
and centralised identity systems. He believes poor management of local Model
Context Protocol servers will now cause a resurgence of cleartext service
credentials on employee devices. ... "The industry is shifting from breaches
caused by human identity failures to breaches rooted in AI agent identity
compromise. As agents become operational backbones, attacks targeting their
tokens, personas, and delegated authority will define the next wave of
high-impact incidents," said Shlomo.AI killed the cloud-first strategy: Why hybrid computing is the only way forward now
 Existing infrastructures now configured with cloud services simply may not be
ready for emerging AI demands, a recent analysis from Deloitte warned. "The
infrastructure built for cloud-first strategies can't handle AI economics," the
report, penned by a team of Deloitte analysts led by Nicholas Merizzi, said.
"Processes designed for human workers don't work for agents. Security models
built for perimeter defense don't protect against threats operating at machine
speed. IT operating models built for service delivery don't drive business
transformation." ... AI token costs have dropped 280-fold in two years, they
observe -- yet "some enterprises are seeing monthly bills in the tens of
millions." The overuse of cloud-based AI services "can lead to frequent API hits
and escalating costs." There's even a tipping point in which on-premises
deployments make more sense. ... AI often demands near-zero latency to deliver
actions. "Applications requiring response times of 10 milliseconds or below
cannot tolerate the inherent delays of cloud-based processing," the Deloitte
authors point out. ... Resilience is also part of the pressing requirements for
fully functional AI processes. These include "mission-critical tasks that cannot
be interrupted require on-premises infrastructure in case connection to the
cloud is interrupted," the analysts state. ... Whether employing cloud or
on-premises systems, companies should always take direct responsibility for
security and monitoring, Rana said.
Existing infrastructures now configured with cloud services simply may not be
ready for emerging AI demands, a recent analysis from Deloitte warned. "The
infrastructure built for cloud-first strategies can't handle AI economics," the
report, penned by a team of Deloitte analysts led by Nicholas Merizzi, said.
"Processes designed for human workers don't work for agents. Security models
built for perimeter defense don't protect against threats operating at machine
speed. IT operating models built for service delivery don't drive business
transformation." ... AI token costs have dropped 280-fold in two years, they
observe -- yet "some enterprises are seeing monthly bills in the tens of
millions." The overuse of cloud-based AI services "can lead to frequent API hits
and escalating costs." There's even a tipping point in which on-premises
deployments make more sense. ... AI often demands near-zero latency to deliver
actions. "Applications requiring response times of 10 milliseconds or below
cannot tolerate the inherent delays of cloud-based processing," the Deloitte
authors point out. ... Resilience is also part of the pressing requirements for
fully functional AI processes. These include "mission-critical tasks that cannot
be interrupted require on-premises infrastructure in case connection to the
cloud is interrupted," the analysts state. ... Whether employing cloud or
on-premises systems, companies should always take direct responsibility for
security and monitoring, Rana said.Agentic AI breaks out of the lab and forces enterprises to grow up
 The first major stride is the shift from improvisation to repeatable patterns.
Early agentic projects were nearly all “glue code”, prompt chains stitched
together with brittle tool wiring and homegrown memory hacks. Every workflow
was a snowflake. But now, mature organizations are creating shared agentic
primitives that development teams can reuse. ... The second major stride is
the rise of enterprise grade governance and safety frameworks designed
specifically for agentic workflows. Traditional AI governance wasn’t built for
systems that take autonomous actions, call tools, modify infrastructure, and
reason over long sequences. Enterprises are now treating governance as a first
class engineering challenge. ... The third stride is a philosophical and
architectural shift in where enterprises choose to invest. Many companies
spent months crafting custom planning modules, memory layers, tool registries,
and agent routers, believing these would become strategic assets. But
experience is proving otherwise. ... The fourth and most important stride is
the move toward building durable components that will matter long after
orchestration layers become commoditized. Enterprises increasingly understand
that their competitive advantage will come from institutional intelligence:
domain specific tool schemas, curated datasets, validated decision policies,
and deep integration with their existing SDLC, incident response, and SOC
workflows.
The first major stride is the shift from improvisation to repeatable patterns.
Early agentic projects were nearly all “glue code”, prompt chains stitched
together with brittle tool wiring and homegrown memory hacks. Every workflow
was a snowflake. But now, mature organizations are creating shared agentic
primitives that development teams can reuse. ... The second major stride is
the rise of enterprise grade governance and safety frameworks designed
specifically for agentic workflows. Traditional AI governance wasn’t built for
systems that take autonomous actions, call tools, modify infrastructure, and
reason over long sequences. Enterprises are now treating governance as a first
class engineering challenge. ... The third stride is a philosophical and
architectural shift in where enterprises choose to invest. Many companies
spent months crafting custom planning modules, memory layers, tool registries,
and agent routers, believing these would become strategic assets. But
experience is proving otherwise. ... The fourth and most important stride is
the move toward building durable components that will matter long after
orchestration layers become commoditized. Enterprises increasingly understand
that their competitive advantage will come from institutional intelligence:
domain specific tool schemas, curated datasets, validated decision policies,
and deep integration with their existing SDLC, incident response, and SOC
workflows.Businesses have always complained about compliance obligations. Could they automate themselves out of it?
 Compliance can often seem like an exercise in Kafkaesque absurdity. Nutanix’s
director of systems engineering, James Sturrock, says it’s not uncommon for
two in-house experts to have differing opinions on how to solve the same
thorny regulatory conundrum. That isn’t even getting into how competing
jurisdictions might view the problem. ... Equally important are potential
unknowns such as contaminated soil or sewers that don’t appear on maps or
where data is incomplete. These don’t just represent potential holdups to work
– and resulting penalties – but represent further risks in themselves. ...
Automating alerts or making it easier to spot compliance headaches early is
one thing. But what might AI contribute toward simplifying more complex
compliance conundrums, like those encountered by the financial services
industry? In that sector, explains Pegasystems’ global banking industry lead
Steve Morgan, such models have to be readily explainable not only to
customers, but internal audit teams and regulators, too. Even then, it’s
already clear that certain types of AI applications aren’t completely suitable
for insertion into compliance workflows – most notably, GenAI. “Unless you
have a very special model that’s trained” on a specific use case, says Morgan,
the answers that such models provide compliance experts just aren’t
predictable or accurate enough to meet the high standards demanded of banks.
Compliance can often seem like an exercise in Kafkaesque absurdity. Nutanix’s
director of systems engineering, James Sturrock, says it’s not uncommon for
two in-house experts to have differing opinions on how to solve the same
thorny regulatory conundrum. That isn’t even getting into how competing
jurisdictions might view the problem. ... Equally important are potential
unknowns such as contaminated soil or sewers that don’t appear on maps or
where data is incomplete. These don’t just represent potential holdups to work
– and resulting penalties – but represent further risks in themselves. ...
Automating alerts or making it easier to spot compliance headaches early is
one thing. But what might AI contribute toward simplifying more complex
compliance conundrums, like those encountered by the financial services
industry? In that sector, explains Pegasystems’ global banking industry lead
Steve Morgan, such models have to be readily explainable not only to
customers, but internal audit teams and regulators, too. Even then, it’s
already clear that certain types of AI applications aren’t completely suitable
for insertion into compliance workflows – most notably, GenAI. “Unless you
have a very special model that’s trained” on a specific use case, says Morgan,
the answers that such models provide compliance experts just aren’t
predictable or accurate enough to meet the high standards demanded of banks.
Security coverage is falling behind the way attackers behave
 Cybercriminals keep tweaking their procedures, trying out new techniques, and
shifting tactics across campaigns. Coverage that worked yesterday may miss how
those behaviors appear today. ... Activity expanded from ransomware driven
campaigns into espionage aligned behavior, with targets including telecom,
energy, military, and government organizations. Researchers tracked changes in
tooling, credential access, and detection evasion, including expanded use of
advanced techniques against cloud and enterprise environments. ... The report
describes zero-day use as commoditized. Exploits move quickly from discovery
into active abuse. This compresses defender response windows from weeks into
days. Early detection depends on identifying behavior tied to exploitation
rather than waiting for vulnerability disclosures or patches. ... Identity
became a primary target. Campaigns focused on SaaS access, cloud administration,
and single sign-on abuse. Luna Moth evolved from simple callback phishing into
multi-channel operations combining voice, email, and infrastructure control. ...
One theme that runs through the findings is the presence of defensive gaps at
the procedure level. Many organizations track techniques and tools, while
execution details that signal intent receive less attention. The research
connects observed procedures directly to detection and prevention controls,
showing where coverage holds and where it breaks down.
Cybercriminals keep tweaking their procedures, trying out new techniques, and
shifting tactics across campaigns. Coverage that worked yesterday may miss how
those behaviors appear today. ... Activity expanded from ransomware driven
campaigns into espionage aligned behavior, with targets including telecom,
energy, military, and government organizations. Researchers tracked changes in
tooling, credential access, and detection evasion, including expanded use of
advanced techniques against cloud and enterprise environments. ... The report
describes zero-day use as commoditized. Exploits move quickly from discovery
into active abuse. This compresses defender response windows from weeks into
days. Early detection depends on identifying behavior tied to exploitation
rather than waiting for vulnerability disclosures or patches. ... Identity
became a primary target. Campaigns focused on SaaS access, cloud administration,
and single sign-on abuse. Luna Moth evolved from simple callback phishing into
multi-channel operations combining voice, email, and infrastructure control. ...
One theme that runs through the findings is the presence of defensive gaps at
the procedure level. Many organizations track techniques and tools, while
execution details that signal intent receive less attention. The research
connects observed procedures directly to detection and prevention controls,
showing where coverage holds and where it breaks down.Widely Used Malicious Extensions Steal ChatGPT, DeepSeek Conversations
 Stolen browser history data includes not only the complete URLs from all Chrome
tabs, but also search queries containing sensitive keywords and research topics,
URL parameters that could contain session tokens, user IDs, and authentication
data, and internal corporate URLs revealing organizational structure and tools.
... Extensions are used to improve and customize users’ browsing experience.
More people are using browsers, which can expand the attack surface of the
individual and the companies they work for, according to security experts.
“Browser extensions aren’t niche tools anymore; they’re deeply embedded in how
people work,” Grip Security researchers Ben Robertson and Guy Katzir wrote
earlier this year. “But that convenience comes with risk, especially when
security teams don’t have visibility into what’s installed, what it can access,
or how it behaves after login. The attack surface has shifted. And while
endpoint agents and network controls still matter, they can’t see what’s
happening inside the browser. That’s where threats like token hijacking and data
leakage quietly take shape.” ... In the most recent case, the hackers created
malicious extensions that impersonated a legitimate browser created by a company
called AITOPIA. The extension puts a sidebar onto any website to give users the
ability to chat with popular AI LLMs, OX Security’s Siman and Bustan
wrote.
Stolen browser history data includes not only the complete URLs from all Chrome
tabs, but also search queries containing sensitive keywords and research topics,
URL parameters that could contain session tokens, user IDs, and authentication
data, and internal corporate URLs revealing organizational structure and tools.
... Extensions are used to improve and customize users’ browsing experience.
More people are using browsers, which can expand the attack surface of the
individual and the companies they work for, according to security experts.
“Browser extensions aren’t niche tools anymore; they’re deeply embedded in how
people work,” Grip Security researchers Ben Robertson and Guy Katzir wrote
earlier this year. “But that convenience comes with risk, especially when
security teams don’t have visibility into what’s installed, what it can access,
or how it behaves after login. The attack surface has shifted. And while
endpoint agents and network controls still matter, they can’t see what’s
happening inside the browser. That’s where threats like token hijacking and data
leakage quietly take shape.” ... In the most recent case, the hackers created
malicious extensions that impersonated a legitimate browser created by a company
called AITOPIA. The extension puts a sidebar onto any website to give users the
ability to chat with popular AI LLMs, OX Security’s Siman and Bustan
wrote. 2026: The year we stop trusting any single cloud
 The real story is not that cloud platforms failed; it’s that enterprises quietly
allowed those platforms to become single points of failure for entire business
models. In 2025, many organizations discovered that their digital transformation
had traded physical single points of failure for logical ones in the form of a
single region, a single provider, or even a single managed database. When a
hyperscaler region had trouble, companies learned the hard way that “highly
available within a region” is not the same as “business resilient.” What caught
even seasoned teams off guard was the hidden dependency chain. ... Expect to see
targeted workload shifts that move critical customer-facing systems from
single-region to multi-region or cross-cloud setups, re-architecting data
platforms with replicated storage and active-active databases (meaning that we
have two running, with one backing up the other). Also, relocating some systems
to private or colocation environments based on risk. ... In 2026, smart
enterprises will start asking their vendors the hard questions. Which regions
and providers do you use? Do you have a tested failover strategy across regions
or providers? What happens to my data and SLAs if your primary cloud has a
regional incident? Many will diversify not just across hyperscalers, but across
SaaS and managed services, deliberately avoiding over-concentration on any
provider that cannot demonstrate meaningful redundancy.
The real story is not that cloud platforms failed; it’s that enterprises quietly
allowed those platforms to become single points of failure for entire business
models. In 2025, many organizations discovered that their digital transformation
had traded physical single points of failure for logical ones in the form of a
single region, a single provider, or even a single managed database. When a
hyperscaler region had trouble, companies learned the hard way that “highly
available within a region” is not the same as “business resilient.” What caught
even seasoned teams off guard was the hidden dependency chain. ... Expect to see
targeted workload shifts that move critical customer-facing systems from
single-region to multi-region or cross-cloud setups, re-architecting data
platforms with replicated storage and active-active databases (meaning that we
have two running, with one backing up the other). Also, relocating some systems
to private or colocation environments based on risk. ... In 2026, smart
enterprises will start asking their vendors the hard questions. Which regions
and providers do you use? Do you have a tested failover strategy across regions
or providers? What happens to my data and SLAs if your primary cloud has a
regional incident? Many will diversify not just across hyperscalers, but across
SaaS and managed services, deliberately avoiding over-concentration on any
provider that cannot demonstrate meaningful redundancy.
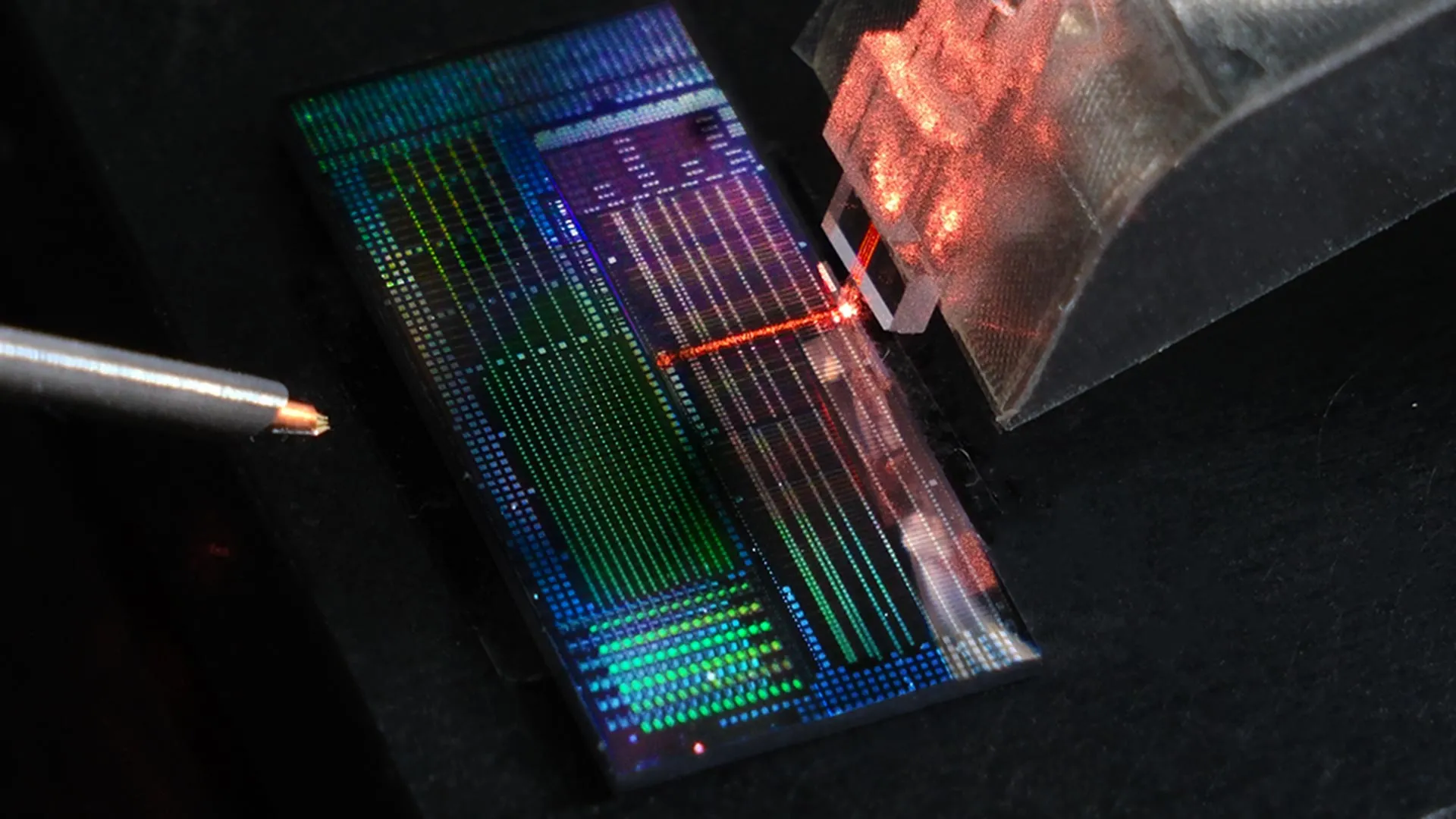
AI Is Forcing Businesses To Rethink Their Data Strategies
 One of the biggest misconceptions about cloud repatriation is that it’s a simple
reversal of a cloud migration. In reality, AI workloads frequently exceed the
capabilities of existing on-prem infrastructure. “Servers that were procured
three years ago may not be able to handle what these applications require,”
Brodsky says. As a result, repatriation decisions often trigger broader
modernization efforts, including new hardware, increased power and cooling
capacity, and redesigned architectures. Before making those investments,
organizations need a clear understanding of their current environment and future
requirements. ... “You have to evaluate whether your on-prem environment can
actually ingest and protect what you’re bringing down from the cloud,” he says.
Timelines and approaches vary. Some organizations opt for high-level assessments
to guide strategy, while others pursue deeper technical workshops or phased
transitions based on business priorities and service-level agreements. Despite
the renewed interest in on-prem infrastructure, cloud repatriation doesn’t
signal a retreat from cloud computing. Instead, it reflects a more mature
understanding of hybrid IT. “Five years ago, we had daily conversations with
customers who wanted to be 100% cloud,” Brodsky says. “Very few actually got
there.” Today, most organizations operate hybrid environments by necessity,
balancing cloud flexibility with on-prem performance, cost predictability and
governance.
One of the biggest misconceptions about cloud repatriation is that it’s a simple
reversal of a cloud migration. In reality, AI workloads frequently exceed the
capabilities of existing on-prem infrastructure. “Servers that were procured
three years ago may not be able to handle what these applications require,”
Brodsky says. As a result, repatriation decisions often trigger broader
modernization efforts, including new hardware, increased power and cooling
capacity, and redesigned architectures. Before making those investments,
organizations need a clear understanding of their current environment and future
requirements. ... “You have to evaluate whether your on-prem environment can
actually ingest and protect what you’re bringing down from the cloud,” he says.
Timelines and approaches vary. Some organizations opt for high-level assessments
to guide strategy, while others pursue deeper technical workshops or phased
transitions based on business priorities and service-level agreements. Despite
the renewed interest in on-prem infrastructure, cloud repatriation doesn’t
signal a retreat from cloud computing. Instead, it reflects a more mature
understanding of hybrid IT. “Five years ago, we had daily conversations with
customers who wanted to be 100% cloud,” Brodsky says. “Very few actually got
there.” Today, most organizations operate hybrid environments by necessity,
balancing cloud flexibility with on-prem performance, cost predictability and
governance.













/dq/media/media_files/2025/12/29/godspeed-curtain-twitchers-2025-12-29-12-33-59.jpg)