How acceptable is your acceptable use policy?

Your AUP needs to be auditable and enforceable—but there’s a tricky balance between protecting employees and making them feel like they’re working for an authoritarian regime. “It should be written to the end user rather than the technical person who works in security,” says Michaels. “One of the pitfalls that we see in the development of policies is the security leader will either own the creation of the policy or delegate it to somebody on their team, and they won’t go out and source feedback and check that they’re on the right track.” More mature security programs source feedback and have closer partnerships with HR and the other functions in the business. But many companies are “still trying to do the basic blocking and tackling,” Michaels says. “They’re still more focused on the technology and the process rather than the people that they’re impacting.” The AUP should be clear, concise, and easy to understand—not technobabble or legalese. But getting employee buy-in could also come down to something as simple as word choice.
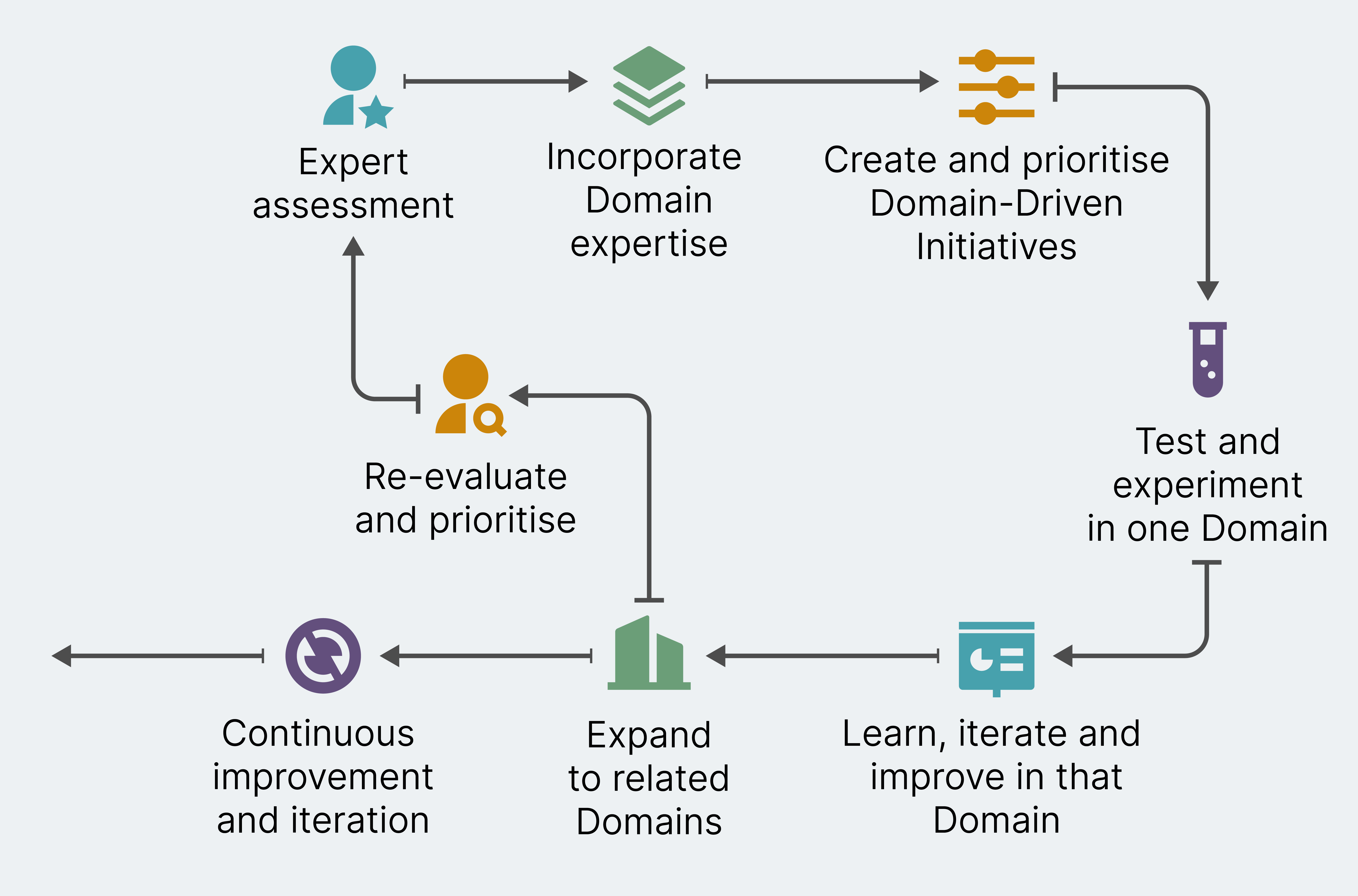
The power of incremental momentum

Companies can get the type of disruptive innovation they need to survive and create lasting change, without moving fast and breaking things. This can be achieved by building momentum for change incrementally. It’s not a new approach, but it can get overlooked when a sense of urgency arises and appears to dictate swift action. ... Incremental momentum has been successfully used in other endeavors. Almost 120 years after Roosevelt’s work, a team of environmental scientists in Finland surveyed the success of incremental change in achieving the country’s sustainability goals. They concluded: “The strengths of small wins include the ability to react to the constantly changing, dynamic conditions…and to deepen trust, commitment and understanding among people.” The report continued, small wins “can facilitate progress and interfere with old routines by bringing about small steps that may result in continuous transformational change and generate radical changes in the long run.” ... The risks were great. The SAP executive team had to balance putting effort into building cloud solutions with maintaining engineering support for the ERP system innovations that its customers relied on.
IT leaders face reality check on hybrid productivity

Organizations are realizing that hybrid work is more about how teams come
together — not just what’s right for the organization or individual, says
Jonathan Pearce, workforce strategies lead at Deloitte Consulting. So more
companies are ratcheting up expectations for their team leaders to decide how
work gets done, and then hold them accountable as a team when it comes to
performance and rewards. “We’re expecting more team leaders to have open
discussions with their teams on what’s working and not working around
communication, the norms around [how quickly] they’re expected to respond and
how we come together when we need to collaborate,” Pearce says. “The question
now becomes how do we up their game as managers — not just managers of work but
really orchestrators of a more complex team environment,” Pearce says. Good
managers make work more enjoyable for their teams, are better able to identify
and use each employee’s strengths and help those workers gain more skills and
experience they need to develop their careers and be more productive, he adds.
Improving Cyberresilience in an Age of Continuous Attacks
Effective cybersecurity is about risk management. For example, when banks lend
money or issue credit cards, the chief risk officer (CRO) has created a model
based on profiles that assume there will be a default rate, meaning certain
borrowers may not ever repay their obligations. This is communicated to the
chief executive officer (CEO) so that the entire management team understands
that it will incur losses from certain customers. Banks are then able to plan
and reserve for these losses before they happen. Enterprises must think of
cybersecurity in the same manner in which banks lend money. It is only a matter
of time before a breach occurs. If the right controls are in place, these
breaches are nothing more than a simple incident of 1 machine being compromised
vs. an entire network’s worth of data being compromised. Each new attack has the
potential to change the threat model. This may not be the first thing on
cybersecurity team members’ minds after an attack, but changes could be required
immediately.
The 3G shutdown: Here are the impacted devices. Do you own any?

So, what does this all mean for older hardware like cell phones, alarms, and
GPS systems that thrive on the 3G spectrum? To put it bluntly, many of the
network-driven features will become obsolete, presenting some unforeseen
dangers. Fortunately, there are steps that you and your loved ones can take
to safely transition from aging to future-proof tech. In some cases,
manufacturers may even be able to give your older gadgets new life through
software upgrades. ... Besides ushering in the revolution of smartphones, 3G
has played a foundational role in the navigation and alarm-based systems
that we rely on during our everyday commutes. With the institution of faster
and more reliable 5G, roadside assistance and emergency crash alerts are
among the many network-based features that will be affected by the shutting
down of 3G. Many cars also have an emergency SOS button that, when pressed,
dials first responders via 3G. That, too, will lose functionality. Vehicles
from popular automakers like Toyota, Lexus, Nissan, Hyundai, Dodge, and more
released before 2019 are susceptible to the issues mentioned above.
Quantum Computing Will Change Our Lives. But Be Patient, Please
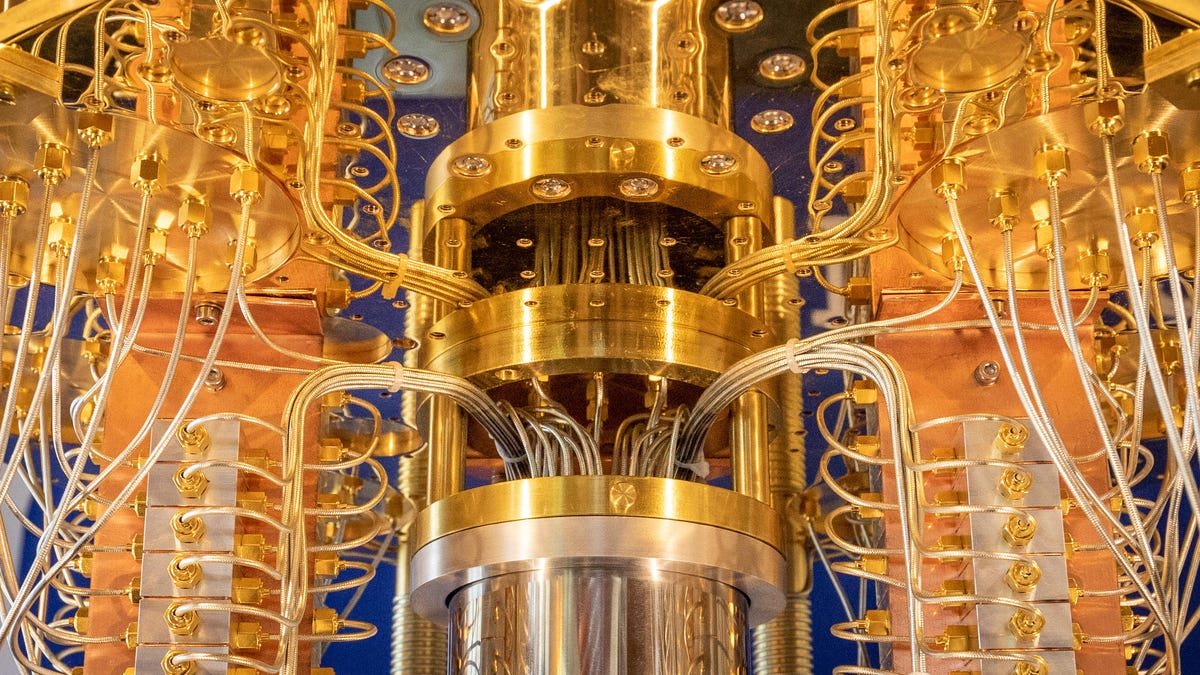
Over and over at Q2B, quantum computing advocates showed themselves to be
measured in their predictions and guarded about promising imminent
breakthroughs. Comments that quantum computing will be "bigger than fire"
are the exception, not the rule. Instead, advocates prefer to point to a
reasonable track record of steady progress. Quantum computer makers have
gradually increased the scale of quantum computers, improved its software
and decreased the qubit-perturbing noise that derails calculations. The race
to build a quantum computer is balanced against patience and technology road
maps that stretch years into the future. ... And new quantum computing
efforts keep cropping up. Cloud computing powerhouse Amazon, which started
its Braket service with access to others' quantum computers, is now at work
on its own machines too. At Q2B, the Novo Nordisk Foundation -- with funding
from its Novo Nordisk pharmaceutical company -- announced a plan to fund a
quantum computer for biosciences at the University of Copenhagen's Niels
Bohr Institute in Denmark.
The Future: Data Access Must Be Intelligently Automated

Of course, an AI engine must contain certain features, including the ability
to provide transparent explanations to data managers regarding processes and
the capability to receive data manager feedback for learning and improving
the DPP. It must also boost efficiency and accuracy when automating and
improving how policies are built, maintained and enforced. Then, over time,
these policy applications become more accurate, flexible and intelligently
automated. An AI engine also requires vast data sets for training. However,
it’s possible to reduce the time required by applying the “human in the loop
concept,” where data managers educate the AI. Through this process, the AI
engine learns faster and makes better decisions and suggestions. Policies
can then be maintained and updated, improving the DPP and supporting
organizations to quickly and automatically decide on sharing processes that
are safe, secure and compliant. This is the ideal convergence of human
expertise and AI technology. And it’s the future of data access governance
and lifecycle management. Is your business ready to take advantage?
How much digital trust can you place on zero-trust?

One very important principle of zero-trust that is often understated is
assumed breach. All too often, some identity and access management (IAM)
product suppliers are quick to share how they can help enterprises achieve
zero-trust. This is all well and good, except for the fact that they often
cover the first two principles of i) verify explicitly and ii) use least
privilege access, but not enough of iii) assume breach. While the first two
principles help to limit any attack blast radius and hinder a breach as it
steps through the attack kill chain, the third and last principle is
critical to effective and efficient detection and containment of a breach in
the ability to detect fast, contain fast and recover fast. If we believe
that breaches are inevitable, assume breach requires a bigger stage. ...
With the increase of triple-extortion ransomware and ransom cartels, it is
important to zoom in on decoys. The deployment of time-based database
honeytokens shortens incident response time by allowing an enterprise to
quickly determine whether the source of a data leak arose from any system
breach within the enterprise or was the result of a case of re-hashing of
past leaked data from breach databases.
The Great Resignation isn’t over yet

One in four employees don’t feel secure in their current positions and
almost half of them plan to explore new job options in 2023, according to a
new report that indicates the Great Resignation remains in full swing. Over
the past year, more than 4 million workers have quit their jobs every month,
according to US Bureau of Labor Statistics The report, by human
resource management software provider isolved, says the top way employers
can improve company culture and retain their workers is by paying their
employees market value. “This comes as no surprise, considering pay
transparency laws have jumped to the forefront, and the pressure is on
employers to eliminate pay inequality within their organizations,” isolved
said in its report. “Data shows employees are more anxious, burnt-out and
financial security-driven than ever," ” James Norwood, isolved’s chief
strategy officer, said in a statement. "To combat these concerns, HR
departments of all sizes must evaluate what they can automate and gain
efficiencies in, enhance what they can to improve employee experience, and
extend the impact of their team."
The Professionalization of Ransomware: What You Need to Know

Carson says it is critical that IT professionals are current with the
ransomware trends and techniques, as it will help IT professionals identify
the best ways to reduce those risks and enhance the security controls for
the business they are hired to protect. From his perspective, the breakup of
some of the large ransomware criminal gangs makes it more likely that
smaller splinter groups will become the top threat in 2023. “They have the
knowledge of a larger ransomware gang and can now operate more efficiently,
sometimes even more targeted,” he says. Kirk explains ransomware is still
largely successful due to security mistakes or weaknesses that usually can
be mitigated or eliminated. “The risk from stolen login credentials can be
mitigated by employing multifactor authentication,” he says. “Cybersecurity
awareness training can reduce the likelihood an employee may be tricked into
downloading a malicious attachment.” He adds that promptly patching software
-- particularly for internet-facing systems such as email servers or VPNs --
is extremely important, as is ensuring that remote connectivity software is
securely managed.
Quote for the day:
"Brilliant strategy is the best
route to desirable ends with available means." -- Max McKeown