How Your Organization Can Enhance Its Cybersecurity Posture

You need to be prepared for the worst-case scenario. Most organizations are
unaware that they have been breached until their data is held to ransom or has
been publicly exposed According to the Information Commissioners Office, "you
must report a notifiable breach to the ICO without undue delay, but not later
than 72 hours after becoming aware of it. If you take longer than this, you must
give reasons for the delay." After you have made the report, how do you go
forward on securing the rest of your business? And do you know what steps can be
used to lessen the damage done? Controlling the users, logs and security is
essential. "This is especially true when regarding data protection and
information security. Even more so when this data concerns the handing of
financial, personal and/or client-sensitive information," SecurityHQ says.
... How often do you do security testing, and what types of security
testing do you do? Do you conduct simulated phishing attacks? Do you have
vulnerability management in place? Do you know how secure your firewalls are? Do
you conduct red team exercises?
Brooklyn Hospitals Decried for Silence on Cyber Incident
Errol Weiss, chief security officer at the Health Information Sharing and
Analysis Center, says a lack of transparency by healthcare organizations dealing
with ransomware incidents is a common problem. "Despite being a member of an
ISAC, we still see organizations reluctant to share attack details when they are
a victim of a cyber incident," he says. Senior leaders at those organizations
may not trust the anonymity and trust built into information-sharing processes
and may be concerned about further exposure and negative reputational impact
from unauthorized disclosures, he says. "Given our incredibly litigious society,
internal counsel at the impacted organization may also recommend against
disclosure outside the company because it could possibly be used against the
firm in future litigation," he says. Many organizations do not realize that they
have liability protections involving cyber information sharing under the
Cybersecurity Information Sharing Act of 2015, he says. "We just need the
government and society to create a culture that rewards sharing and does not
punish the victim."
8 things to consider amid cybersecurity vendor layoffs

Layoffs of engineers and developers should be the most concerning for CISOs and
security teams, Burn adds, describing them as the “canary in the coalmine” when
it comes to spotting and fixing security threats. “Often, when we see some of
these early layoffs, they impact recruitment or marketing staff, but that
shouldn’t concern you really.” However, if you’re looking on LinkedIn and seeing
engineers or developers being laid off, that should give you pause for thought,
Burn says. Dickson concurs, adding that sales or marketing cuts are unlikely to
affect the ability to get security value from the vendor, but cuts to key
service or engineering staff could well do just that. For Thacker, the biggest
risks to customers would come from a reduction in DevSecOps staffing, “which
would potentially bring about a reduction in security oversight, feature
updates, and even impact upon the general availability of the service,” while
Yuval Wollman, chief cyber officer and managing director of UST, thinks cuts to
innovation and research staff could have a direct impact on a product’s
efficiency and reliability as the threat landscape evolves and changes.
Is AI moving too fast for ethics? | The AI Beat

The Stable Diffusion news nearly drowned out the applause and chatter of the
previous two days, which was all around Meta’s latest AI research announcement
about Cicero, an AI agent that masters the difficult and popular strategy game
Diplomacy — showing off the machine’s ability to master negotiation, persuasion
and cooperation with humans. In a paper published last week in Science, Cicero
is said to have ranked in the top 10 percent of players in an online Diplomacy
league and achieved more than double the average score of the human players — by
combining language models with strategic reasoning. Even AI critics like Gary
Marcus found plenty to cheer about regarding Cicero’s prowess: “Cicero is in
many ways a marvel,” he said. “It has achieved by far the deepest and most
extensive integration of language and action in a dynamic world of any AI system
built to date. It has also succeeded in carrying out complex interactions with
humans of a form not previously seen.”
Talent development: 4 upskilling success stories

Career development is a focus for all employees, even entry-level workers, and
everyone is given several opportunities to grow their skills and learn new
technologies. For example, an entry-level code developer at Altria will be
thrown into highly technical work right away, so they gain experience fast. And
then throughout their first five to six years with the company, they will be
moved around IT departments to work on different projects, gaining more
experience and potentially finding out what they’re most passionate about. “In
many cases, we’re trying to put them into a role that ultimately is going to
make them sweat — it’s going to really challenge them,” says Dan Cornell, vice
president and CIO of Altria Group. Employees also go through an annual talent
planning review process to assess where they are in their careers, what they
aspire to within the organization, and how they want to shape their career
moving forward. Managers can identify areas for growth, what skills can be
developed, opportunities for training, and potential experiences in other
departments they might benefit from.
The Metaverse Could Become a Top Avenue for Cyberattacks in 2023

Privacy will emerge as a major concern in the metaverse, Kaspersky predicted.
"As the metaverse experience is universal and does not obey regional data
protection laws, such as GDPR, this might create complex conflicts between the
requirements of the regulations regarding data breach notification," Kaspersky
said. Others have also expressed concern over the increased amount of personal
information that will be collected in fully immersive environments via VR
headsets and their collection of cameras, microphones, and motion trackers. Many
expect the data will reveal a lot about a user's location, appearance, and other
private information while also enabling attackers to carry out more
sophisticated phishing and social engineering scams. At least some of the
attacks in virtual reality and augmented reality environments will involve
virtual abuse and sexual assault — such as that involving cases of avatar rape,
Kaspersky said. The security vendor pointed to an incident where an avatar
associated with a researcher at a nonprofit advocacy group was raped on a
metaverse platform owned by Meta as one example of the kind of issues consumers
can increasingly run into.
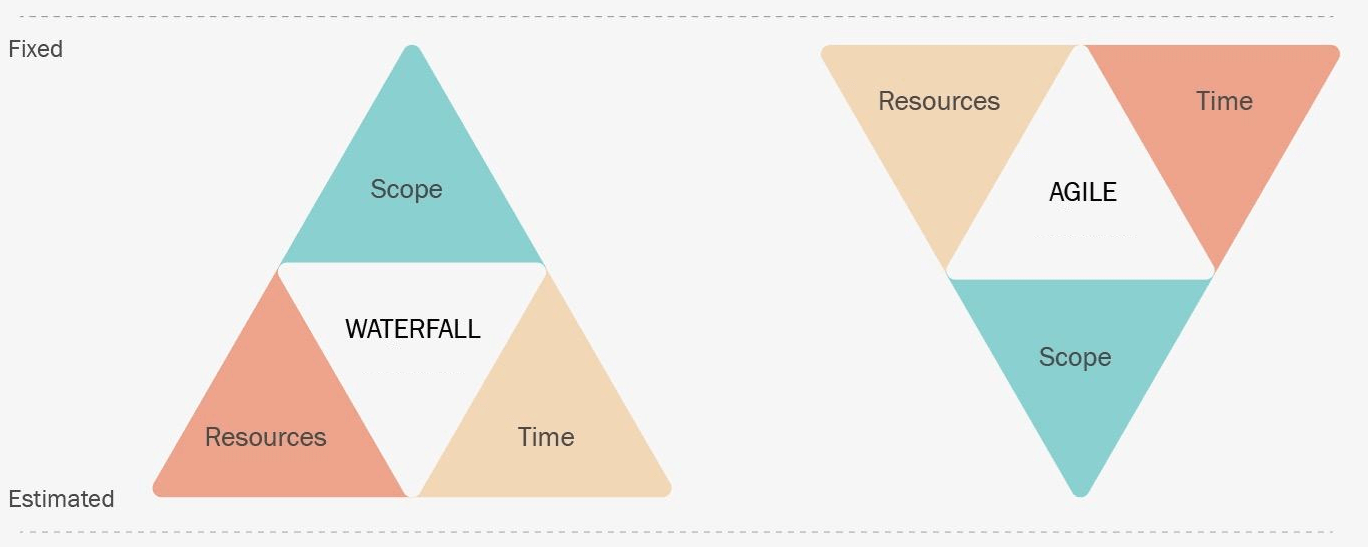
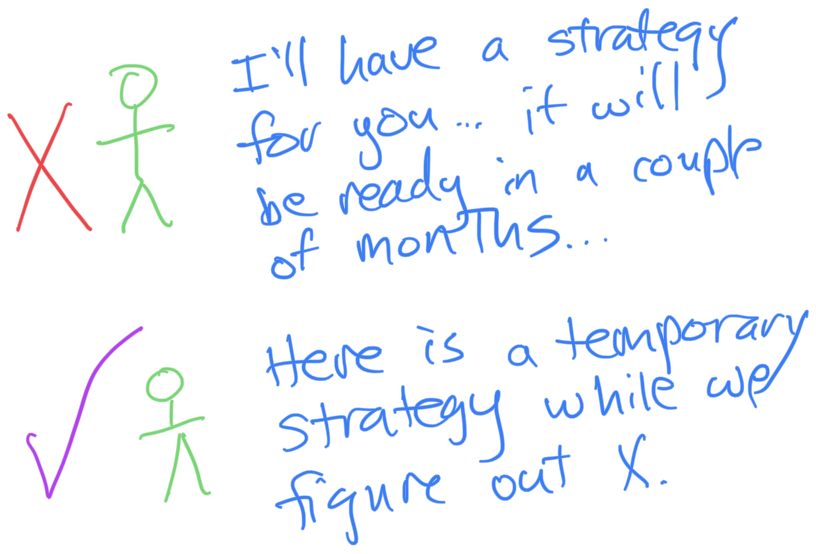
Why Change Management Skills Are Essential To Data-Driven Success

A simple way of looking at change management is to view it as a set of
people-related strategies and tactics that can help shift behaviors and
mindsets. It’s an essential skill set for everyone who works with data from the
Chief Data Officer (CDO) down to junior analysts. Data leaders will be primarily
focused on cultural and procedural resistance, whereas analysts may only deal
with decisional resistance. The scope will differ across roles, but everyone
plays a valuable part in the transformative process. Change management is a
deep, multi-faceted subject, and there is a vast body of work on the topic. ...
To build momentum with your data initiatives, it’s important to deliver quick
wins. Rather than waiting for a long-term payoff, potential skeptics or
detractors need to see faster returns. When people get a taste of what’s
possible through real-world improvements, it becomes easier for them to envision
what the future state with data looks like and get on board with the changes.
5 top qualities you need to become a next-gen CISO

Next-gen CISOs are charismatic, innovative, well-connected, and well-respected
individuals across the organization and the security industry. They never waste
an opportunity to show the value information security brings to the business.
They are increasingly creating reporting structures outside of IT to emphasize
their independence. Next-gen CISOs regularly participate in industry events and
often share their experiences across social media as well as broadcast and print
media, helping to further their reputation and influence.Understands the
business, earns trust, and practices empathy Next-gen CISOs need to understand
the business context behind day-to-day challenges faced by employees, without
which they cannot make the right security decisions. They should help build
employee, customer, partner, and business stakeholder trust through regular
engagement and collaboration. CISOs must shed their ivory tower mentality and
build bridges with those departments and managers known to be critical of
information security.
From capex to opex: Storage procurement options bloom

What we are seeing among storage suppliers is the emergence of consumption
models of purchasing for on-site capacity that mirror the ways we buy cloud
services. Cloud – in the sense of services delivered remotely – is not always
suited to the ways customers work. Some avoid the cloud for reasons of
performance, compliance, or risk to security or availability. And so, although
true pay-as-you-go storage may have its roots in the cloud, there are now
on-site options that bring the same levels of flexibility. These can range from
opex-based consumption models in which the hardware remains the supplier’s
property and customers pay only for the capacity they use, to fully owned capex
spend but where hardware upgrades, as required, are built in. At the opex end of
things, customers usually commit to base levels of usage, while upgrades to
storage and controller hardware are delivered as required. At the capex end of
the spectrum, customers can purchase storage hardware outright. But here, some
suppliers now offer the option to buy the hardware while still benefiting from
upgrades to storage hardware, with monitoring and predictive analytics.
Event-driven automation: How to build an event-driven automation architecture
In addition to the events topic, we also have a few other messaging pipelines
handled by AMQ (create the task, invoke automation and automation results
listener). Each of these will be communicating with the services layer which
will handle system events, task management, automation invocation and automation
results tracking. These services will also be required to communicate with the
intelligent router, which will handle the prioritization based on built-in logic
set by your organization. And finally, in this network we include the task and
execution stores that hold the data being transacted upon throughout these
events. The Manage Task microservice will need to log information into the
ticketing system, which isn’t required to be on an isolated network, but is
depicted as such to clarify it only needs to communicate with that service, and
not the entire architecture. Similarly, the Automation Results service will
communicate with both the orchestrator and the results listener, but it’s not
required for an isolated network if you want to simplify things in your own
implementation.
Quote for the day:
"Integrity is the soul of leadership!
Trust is the engine of leadership!" -- Amine A. Ayad