Large-Scale Phishing Campaign Bypasses MFA
In the phishing campaign observed by Microsoft researchers, attackers initiate
contact with potential victims by sending emails with an HTML file attachment to
multiple recipients in different organizations. The messages claim that the
recipients have a voicemail message and need to click on the attachment to
access it or it will be deleted in 24 hours. If a user clicks on the link, they
are redirected to a site that tells them they will be redirected again to their
mailbox with the audio in an hour. Meanwhile, they are asked to sign in with
their credentials. At this point, however, the attack does something unique
using clever coding by automatically filling in the phishing landing page with
the user’s email address, “thus enhancing its social engineering lure,”
researchers noted. If a target enters his or her credentials and gets
authenticated, he or she is redirected to the legitimate Microsoft office.com
page. However, in the background, the attacker intercepts the credentials and
gets authenticated on the user’s behalf, providing free reign to perform
follow-on activities, researchers said.
Mergers and acquisitions put zero trust to the ultimate test
Zero trust is getting a hard look by enterprises that are pushing more workloads
into the cloud and edge amid more employees working remotely, all of which are
beyond the boundaries datacenter security. The architecture assumes that no
user, device, or application on the network can be trusted. Instead, a
zero-trust framework relies on identity, behavior, authentication, and policies
to verify and validate everything on the network and to determine such issues as
access and privileges. ... "When a company [buys another], they have to identify
which applications of the acquired company they should keep and which they
should eliminate," he said. "Then, for a period of time, the acquired company
will only give them limited access to applications in the acquiring company and
vice-versa. To do so, traditionally they have to bring the two corporate
networks together. When they integrate corporate networks, it creates problems.
"Each site has the same IP address name. They call them 'overlapping IP
addresses.' Now they have to rename and create the stuff. It takes time, money
and effort."
8 servant leadership do’s and don’ts

Being a servant leader doesn’t mean giving up control or “letting people do
whatever they want,” Dotlich says. “I don’t think it means that you do whatever
[employees] ask either, which is how we normally think of ‘servants.’ But it is
really facilitating people’s performance, goals, achievements, and aspirations.
In that way you’re serving who they want to be or what they want to achieve.”
... During periods of high pressure, “sometimes we as leaders want to keep
pushing forward but that’s exactly the wrong thing to do,” Reis says. “Sometimes
it’s just better to take a minute, reframe, and then re-engage.” Leaders can
also show empathy with feedback, he says. “It would be easy to hear a list of
complaints and for defensiveness to set in,” Reis says. “But the empathy is in
understanding that the issues being raised are part of the teammates’ sincere
desire to make things better. You’re empathizing with that frustration and
really hearing that,” he says. ... It’s important for each organization to
define servant leadership “in a way that works in your own system, that people
understand and that is not misleading,” Dotlich says.
Researchers trained an AI model to ‘think’ like a baby, and it suddenly excelled
Typically, AI models start with a blank slate and are trained on data with many
different examples, from which the model constructs knowledge. But research on
infants suggests this is not what babies do. Instead of building knowledge from
scratch, infants start with some principled expectations about objects. For
instance, they expect if they attend to an object that is then hidden behind
another object, the first object will continue to exist. This is a core
assumption that starts them off in the right direction. Their knowledge then
becomes more refined with time and experience. The exciting finding by Piloto
and colleagues is that a deep-learning AI system modelled on what babies do,
outperforms a system that begins with a blank slate and tries to learn based on
experience alone. ... If you show an infant a magic trick where you violate this
expectation, they can detect the magic. They reveal this knowledge by looking
significantly longer at events with unexpected, or “magic” outcomes, compared to
events where the outcomes are expected.
12 Ways to Improve Your Monolith Before Transitioning to Microservices
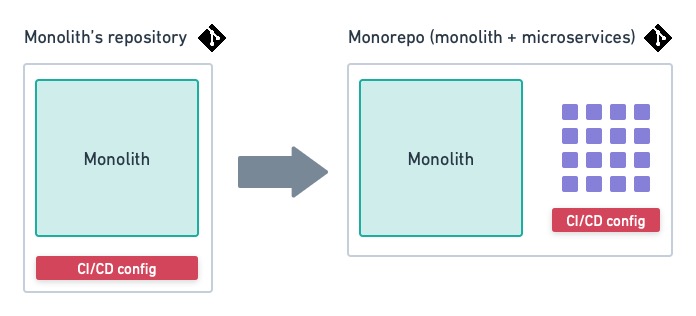
A rewrite is never an easy journey, but by moving from monolith to
microservices, you are changing more than the way you code; you are changing the
company’s operating model. Not only do you have to learn a new, more complex
tech stack but management will also need to adjust the work culture and
reorganize people into smaller, cross-functional teams. How to best reorganize
the teams and the company are subjects worthy of a separate post. In this
article, I want to focus on the technical aspects of the migration. First, it’s
important to research as much as possible about the tradeoffs involved in
adopting microservices before even getting started. You want to be absolutely
sure that microservices (and not other alternative solutions such as modularized
monoliths) are the right solution for you. ... During development, you’ll not
only be constantly shipping out new microservices but also re-deploying the
monolith. The faster and more painless this process is, the more rapidly you can
progress. Set up continuous integration and delivery (CI/CD) to test and deploy
code automatically.
A Data Professional without Business Acumen Is Like a Sword without a Handle
In my journey to become an impactful data professional, I’ve found three
statements to be an excellent pivot:Identify what you love doing in your career,
and more importantly, what you do not. It is okay to feel overwhelmed by the
depth data science and analytics has to offer. Start small with the basics, and
build your way up to complex projects at your own pace. Read what people are
working on. That can inspire you, set expectations, and introduce you to the
latest and greatest in the data community. Take time to create your value
proposition as a data person and work to be the subject matter expert for a
niche. Be the pacesetter of goals for people to turn to you for knowledge,
advice, or to get stuff done. Also, a data professional without business acumen
is like a sword without a handle. The ability to translate business problems
into data and connect it back to business impact is compelling and much
appreciated in today’s world. If all of these still don’t connect with you,
there are plenty of other roles in data beyond data scientists and analysts!
There’s a lot in store for a technology enthusiast today.
Making sense of data with low-code environments

A serious low-code environment provides data scientists flexibility around the
tools they use. At the same time, it allows focus on the interesting parts of
their job, while abstracting away from tool interfacing and different versions
of involved libraries. A good environment lets data scientists reach out to code
if they want to, but ensures they do not have to touch code every time they want
to control the interna of an algorithm. Essentially, this allows visual
programming of a data flow process — data science done for real is complex,
after all. If done right, the low-code environment continues to allow access to
new technologies, making it future proof for ongoing innovations in the field.
But the best low-code environments also ensure backward compatibility and
include a mechanism to easily package and deploy trained models together with
all the necessary steps for data transformations into production. ... The
business people often complain that the data folks work slowly, don’t quite
understand the real problem and, at the end of it all, don’t quite arrive at the
answer the business side was looking for.
Technology is providing the resilience that businesses need at uncertain times
From the blockchain to the Metaverse to emotional AI, digital technologies are
rapidly advancing at a time when enterprises face more pressure than ever to
innovate to gain a competitive advantage. . How can companies apply
human-centric technologies to transform the future of their business? Radically
Human, a new book from Accenture Technology leaders Paul Daugherty and H. James
Wilson, offers business leaders an easy-to-understand breakdown of today's most
advanced human-inspired technologies and an actionable IDEAS framework that will
help you approach innovation in a completely new way. In Radically Human,
Daugherty and Wilson show this profound shift, fast-forwarded by the pandemic,
toward more human -- and more humane -- technology. The book introduces us to a
new innovation framework and the basic building blocks of business --
Intelligence, Data, Expertise, Architecture, and Strategy (IDEAS) -- that are
transforming competition. Daugherty also highlights the three stages of
human-machine interactions.
Low-code development becoming business skill ‘table stakes’

Cloud computing software provider ServiceNow said that more than 80% of its
customer base now uses its low-code solution, App Engine. And App Engine’s
active developer base grows by 47% every month, the company said. Marcus
Torres, general manager of the App Engine Business at ServiceNow, said the
ability to create business applications with low-code and no-code tools is
becoming an expected skill set for businesses. Much of that is because the
business side of the house understands the application needs of a company
better than an IT shop. The millennials and younger workers that make up the
majority of today’s workforce are far more comfortable with technology,
including software development, than older workers. “They understand there is
an app that provides some utility for them,” Torres said. “With these
[low-code] platforms, people typically try it out, get some initial success,
and then try to do more.” Torres has seen groups ranging from facilities teams
to human resources departments develop applications, with the development work
done by people who typically don’t have technology pedigree.
Why tech professionals are leaving IT companies for MBA
The IT experience with the business training provides a big picture of the
direction of the tech firm, from the view point of clients, various
departments, cost, and the firm’s future. The right kind of MBA program allows
hands on experience of creating products and services and working in an
environment similar to tech firms. Besides the soft skills like leadership,
team work, communication, etc. the hard skills – problem solving, strategic
planning, data analytics – working within the frame work of the fast-evolving
tech world can really increase the hiring value of MBAs with prior tech
experience. Good MBA programs also expose their graduates to various hubs
including tech companies. It opens up networking opportunities with peers and
current leaders who are all invested in building the right kind of talent for
the future. This surely beats being stuck in a dead-end software job role with
little learning and development. Good MBA programs also increase the value of
its grads, with better salary opportunities than with pre-MBA
experience.
Quote for the day:
"A leader or a man of action in a
crisis almost always acts subconsciously and then thinks of the reasons for
his action." -- Jawaharlal Nehru