Metaverse Standards Forum Makes Data Interoperable But Only For Big Tech

Interoperability is the driving force for the growth and adoption of the open
metaverse. Hence, the Metaverse Standards Forum aims to analyze the
interoperability necessary for running the metaverse. More than 30 companies
took up their respective posts as founding members of the forum. Game
developers, architects, and engineers are mere clicks away from building the
next cutting-edge metaverse project with artificial intelligence and advanced
hardware. Setting interoperability standards with consideration to available
technology is crucial to the mass adoption of the metaverse. Similar to the
Metaverse Standards Forum, some key players are missing from the Oasis
Consortium, like Meta. And in the past, groups like this have become smaller and
smaller once internal conflict inevitably arises. The Metaverse Standards Forum
is led by the Khronos Group, a nonprofit consortium working on AR/VR, artificial
intelligence, machine learning, and more. Khronos has already tried to set a
standard for VR APIs with its similarly named VR Standards Initiative in 2016,
which included companies like Google, Nvidia. Epic Games and Oculus, which is
now part of Meta.
Identity Access Management Is Set for Exploding Growth, Big Changes — Report

As SaaS and cloud subscription services have proliferated in the space, smaller
firms increasingly have found IAM within their reach, and this study says to
expect this trend to snowball. Whereas the subscription model makes up 60% of
the market now, in five years the researchers forecast it will make up 94% of
all IAM spending. Meanwhile, other, broader IT trends such as the explosion in
cloud computing, bring-your-own-device (BYOD) policies, mobile computing,
Internet of Things (IoT), and more geographically dispersed workers are all
spurring greater IAM services spending to solve an acute need for saner access
control. "There are more devices and services to be managed than ever before,
with different requirements for associated access privileges," according to
Juniper's analysts. "With so much more to keep track of, as employees migrate
through different roles in an organization, it becomes increasingly difficult to
manage identity and access." According to Naresh Persaud, managing director in
cyber-identity services for Deloitte Risk & Financial Advisory, the market
has been especially jumpstarted in the last 12 to 18 months as organizations
work to accommodate a broader range and larger scale of remote-work
situations.
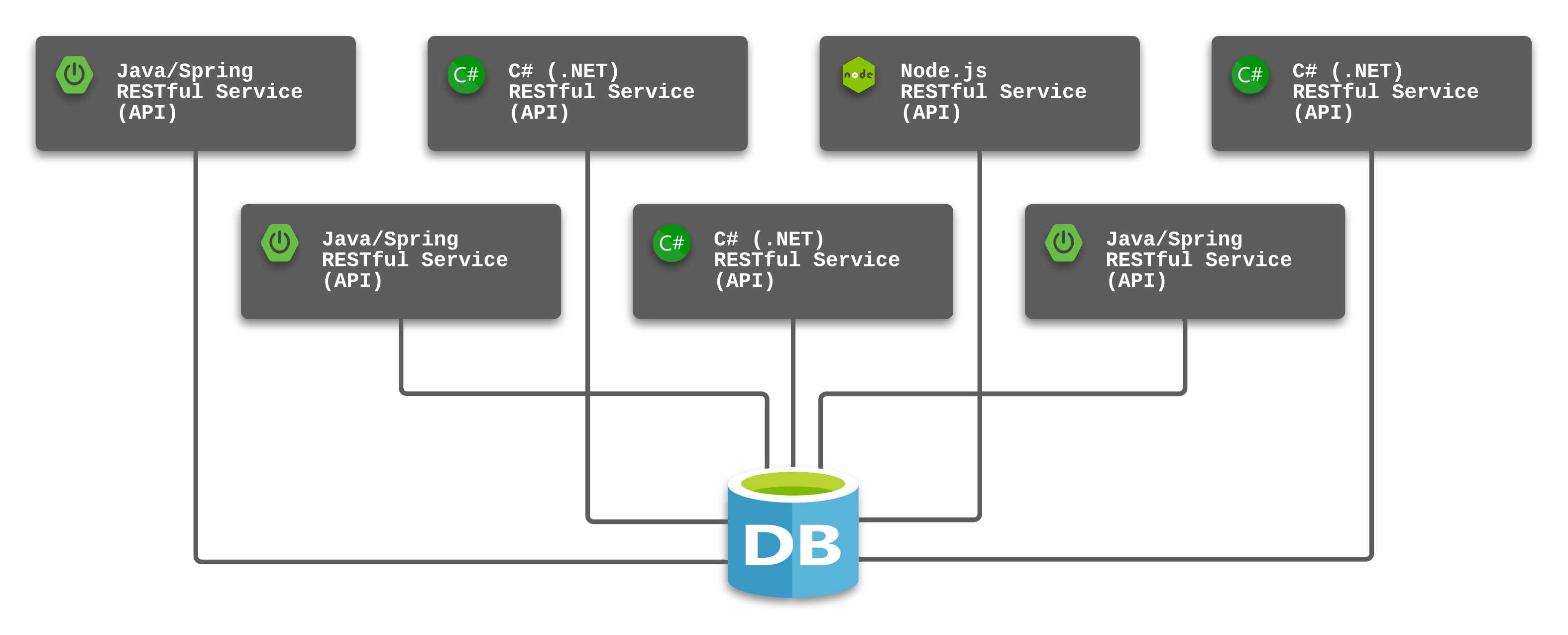
Working with Microsoft’s .NET Rules Engine

Getting started with the .NET Rule Engine is relatively simple. You will need to
first consider how to separate rules from your application and then how to
describe them in lambda expressions. There are options for building your own
custom rules using public classes that can be referred to from a lambda
expression, an approach that gets around the limitations associated with lambda
expressions only being able to use methods from .NET’s system namespace. You can
find a JSON schema for the rules in the project’s GitHub repository. It’s a
comprehensive schema, but in practice, you’re likely to only need a relatively
basic structure for your rules. Start by giving your rules workflow a name and
then following it up with a nested list of rules. Each rule needs a name, an
event that’s raised if it’s successful, an error message and type, and a rule
expression that’s defined as a lambda expression. Your rule expression needs to
be defined in terms of the inputs to the rules engine. Each input is an object,
and the lambda function evaluates the various values associated with the
input.
10 Questions to Ask Yourself Before Starting Your Entrepreneurial Journey
Entrepreneurship is over-glorified and misrepresented on social media. In
reality, it is about building a business that solves a problem for a consumer.
It's not about driving nice cars or posting nice pictures on social media. In
fact, real entrepreneurship looks quite contrary to what we see on social media.
Do we require a certain level of luck, genetics and an environment around us to
be an entrepreneur? Yes — somewhat, for sure. But also, anyone can solve
problems anywhere in the world. That is true for both small problems and big
problems. The choice comes in the decision to find people who have needs, wants
and issues that you can offer a solution for. It is also a choice that each of
us gets to make on how well we wish to solve that issue — how obsessed we are
willing to become with that solution and how above and beyond we are willing to
go with servicing the customers well. Beyond the business solution also comes
the personal and emotional responsibility — shaping and growing ourselves to be
able to handle and maneuver through constant stress and difficulties.
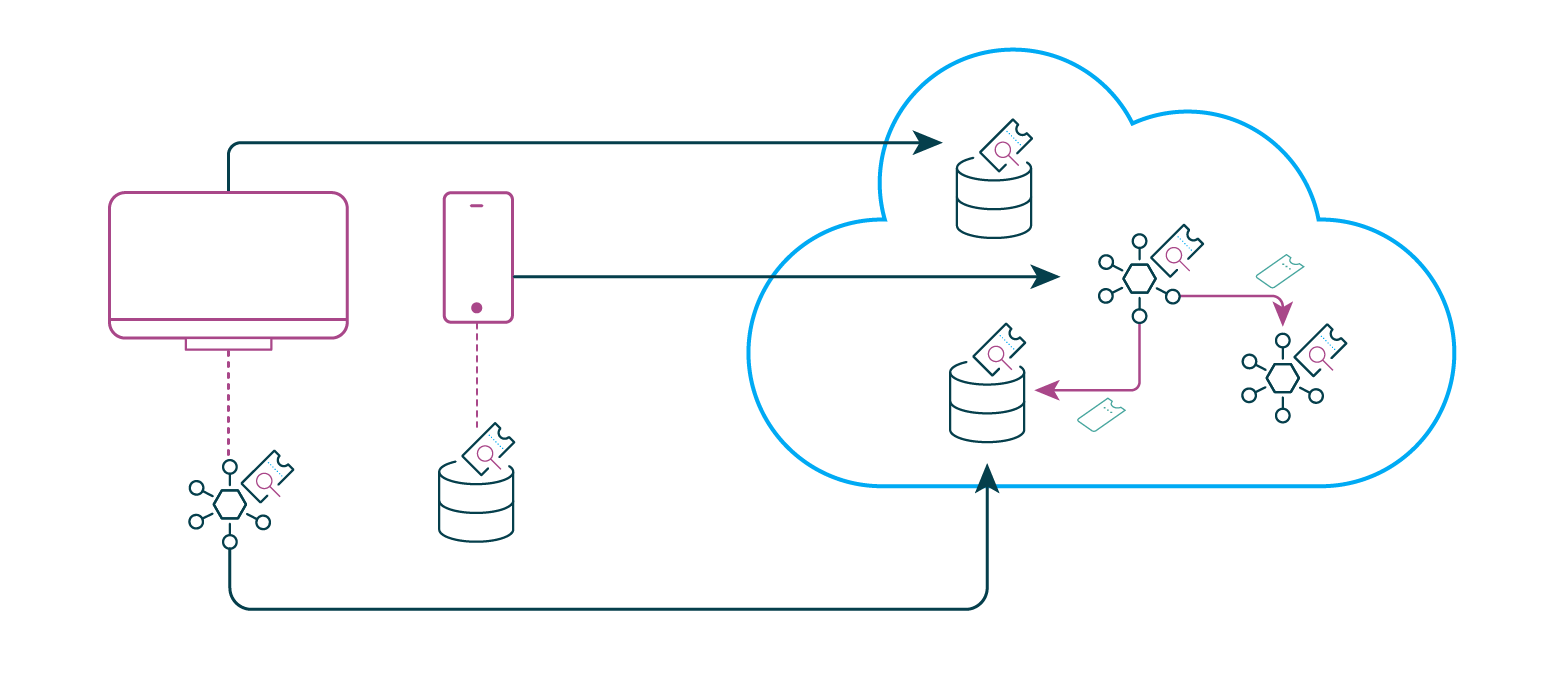
Don’t let automation break change management

Where automation is essential and unavoidable, network teams need to make sure
all the good they can do with automation is not done at the expense of or in
conflict with one of the other pillars of enterprise IT: change management.
They need to make sure automation is controlled by change management, and that
they are keeping change management processes in step with their increasing
reliance on automation. One aspect is to implement change management on the
automation, including the scripts, config files, and playbooks, used to manage
the network. The use of code management tools helps with this: check-out and
check-in events help staff remember to follow other parts of proper process.
Applying change management at this level means describing the intended
modifications to the automation, testing them, planning deployment, having a
fallback plan to the previous known-good code where that is applicable, and
determining specific criteria by which to judge whether the change succeeded
or needs to be rolled back.
Imagination is key to effective data loss prevention
SecOps teams are charged with protecting data on a network or endpoint in each
of its forms: at rest, in use, and in motion. To be in the driver’s seat and
create the appropriate rules or policies to protect data across these three
classifications requires teams to understand their environment fully. This is
why organizations should consider implementing a flexible, scalable XDR
(extended detection and response) architecture that can seamlessly integrate
with their current security tools and connect all the dots to eliminate
security gaps. With native integrations and connections for security policy
orchestration across data and users, endpoints and collaboration, clouds and
infrastructure, an XDR architecture provides SecOps teams with maximum
visibility and control. ... Knowing what to protect, even before establishing
protection, is key. So much so that comprehensive data visibility is a
critical tenet for any SecOps team. Achieving this enables security teams to
have the flexibility to create data protection parameters tailored to their
own specific needs, creating an environment where the only limit on what they
can achieve is their imagination.
The importance of digital skills bootcamps to UK tech industry success

The success of digital skills bootcamps in helping to secure the UK tech
industry’s future is heavily contingent on the level of involvement from
businesses. At present, however, not enough organisations are devoting the
time needed to upskill or reskill staff, with research conducted by MPA Group
finding that over a third of companies – 35 per cent – only allow workers to
devote less than two hours per week to training, research, and development.
Although there may be a number of reasons for this, MPA Group’s research
indicated that ‘a lack of budget’ was considered by businesses to be the
largest barrier for workplaces allowing staff to spend time on development.
Digital skills bootcamps are helping to solve this problem by enabling
companies to take advantage of the considerable state investment in the
initiative, meaning organisations are given more affordable access to
industry-led training. What’s more, with bootcamps having already been
trialled to great success in places like the West Midlands – where
approximately 2,000 adults have been trained with essential tech skills over
the past few years – firms have the opportunity to hire recent programme
graduates who can help impart what they have learned onto their workers.
The Parity Problem: Ensuring Mobile Apps Are Secure Across Platforms
So to build a robust defense, mobile developers need to implement a
multi-layered defense that is both ‘broad’ and ‘deep’. By broad, I'm talking
about multiple security features from different protection categories, which
complement each other, such as encryption + obfuscation. By ‘deep’, I mean
that each security feature should have multiple methods of detection or
protection. For example, a jailbreak-detection SDK that only performs its
checks when the app launches won’t be very effective because attackers can
easily bypass the protection. Or consider anti-debugging, which is an
important runtime defense to prevent attackers from using debuggers to perform
dynamic analysis – where they run the app in a controlled environment for
purposes of understanding or modifying the app’s behavior. There are many
different types of debuggers – some based on LLDB – for native code like C++
or objective C, others that inspect at the Java or Kotlin layer, and a lot
more. Every debugger works a little bit differently in terms of how it
attaches to and analyzes the app.
4 ways CIOs can create resilient organizations

As CIO, you need to make sure your technology investments enable change. After
all, you might need to support an entirely remote employee population. You
might need to offer new capabilities that attract top talent or quickly shut
down business in a region wracked by geopolitical conflict. Organizations
invest large sums in migrating to the cloud. One reason is the ability to grow
with needs. But technology scale is no longer the primary benefit of the
cloud. And scale is no longer a guarantee of resilience. Rather, focus your
cloud and software-as-a-service (SaaS) investments on supporting rapid change.
Multi-cloud strategy, containerization, agile DevSecOps development
methodologies: All should be designed around elasticity that equips you to
make quick wins or pivot to new business models. ... Data analytics can
provide holistic views and predictive models that help CIOs and others
understand emerging trends. Those insights support data-driven decision-making
and ultimately, resilience. That’s because you no longer have to rely on gut
feel to prepare for an otherwise unpredictable future.
What happens when there’s not enough cloud?

Most companies struggle to find enough customers to buy their products.
According to Selipsky in a Mad Money interview, cloud companies like AWS might
have the opposite problem. “IT is going to move to the cloud. And it’s going
to take a while. You’ve seen maybe only, call it 10% of IT today move. So it’s
still day 1. It’s still early. … Most of it’s still yet to come.” Years ago I
noted that the cloud will take time. Not because there’s limited demand, but
precisely because even with enterprises on a full sprint to the cloud, there
are trillions of dollars’ worth of IT to modernize. As MongoDB CMO Peder
Ulander responded to McLaughlin, “If anything, the growing shortage of
capacity is a watershed moment for AWS, Google Cloud, and Microsoft Azure.”
(Disclosure: I work for MongoDB.) In a hot market, it’s standard for demand to
outstrip supply. Ulander cites products as diverse as Teslas or Tickle Me Elmo
toys. What’s interesting here is that we’re having the enterprise equivalent
of a 1996 Tickle Me Elmo shortage.
Quote for the day:
"Leaders know the importance of having
someone in their lives who will unfailingly and fearlessly tell them the
truth." -- Warren G. Bennis