Can computers become conscious?
AI-hard problems are hypothesized to include general computer vision, natural language understanding, and dealing with unexpected circumstances while solving any real-world problem. As it stands, AI-hard problems cannot be solved with current computer technology alone. They still require human intervention, and probably always will. Following this trend, AI will not become self-aware. So, the doomsday conspiracy theorists are wrong. AI will not become the dominant form of intelligence on Earth, with computers and robots taking over the world. Still, there’s nothing wrong with taking a few precautionary measures to ensure that future superintelligent machines remain under human control. However, I don’t think a robot uprising is possible. Nonetheless, there are those who believe that machines have minds or soon will. This is why scientists have developed a number of experiments to test AI, to find out what the limits of artificial intelligence are.
Custom Response Caching Using NCache in ASP.NET Core
Response caching enables you to cache the server responses of a request so that the subsequent requests can be served from the cache. It is a type of caching in which you would typically specify cache-related headers in the HTTP responses to let the clients know to cache responses. You can take advantage of the cache control header to set browser caching policies in requests that originate from the clients as well as responses that come from the server. As an example, cache-control: max-age=90 implies that the server response is valid for a period of 90 seconds. Once this time period elapses, the web browser should request a new version of the data. The key benefits of response caching include reduced latency and network traffic, improved responsiveness, and hence improved performance. Proper usage of response caching can lower bandwidth requirements and improve the application’s performance. You can take advantage of response caching to cache items that are static and have minimal chance of being modified, such as CSS, JavaScript files, etc.
It's a great time to tackle core IT upgrades

There are hundreds of thousands of security patches out there, but Vulcan will tell you that a few of the important ones will eliminate many related security issues. A little work now goes a long way -- if you know what to do. With consumers and business buyers stuck at home, it is the e-commerce side of a business that is super important. During the important fourth-quarter holiday sales season, companies won't risk making any changes to their e-commerce systems. Now things are reversed, it is the main IT systems that can be upgraded and patched with less risk of downtime problems. But don't mess with the e-commerce systems. Vulcan's platform is designed to scale and to interface with all the standard IT tools. It makes heavy use of machine learning and also human intelligence -- IT experts that can analyze new security threats and solutions. And sometimes a patch isn't needed and a simple workaround will eliminate dozens of related issues, says Bar-Dayan. Vulcan's reports identify the top vulnerabilities and the detailed remediation steps necessary. It is a huge time-saver for cybersecurity teams.
Shadow Broker leaked NSA files point to unknown APT group

Juan Guerrero-Saade, a security researcher and adjunct professor at Johns Hopkins University’s School of Advanced International Studies, wasn’t convinced, arguing that misleading files make their way onto VirusTotal all the time. He realised that the file in question was a 15Mb memory dump of a McAfee installer. In short, it’s a red herring. Investigating godown.dllfurther, he found that the file was a drop from a larger multi-stage infection framework. The tools and techniques that the framework used indicated a unique cluster of activity. It pointed to an advanced persistent threat group that wasn’t publicly known until now. Although it’s difficult to directly attribute the attack to a specific actor, Guerrero-Saade noted that some of the resources in the files mention Farsi (Persian), which is native to countries including Iran. The name used in the root debug path, c:/khzer, apparently means ‘to survey or monitor’ according to friends of his that are acquainted with the language, and so he decided to call the attack group Nazar, after the heart-shaped amulet supposed to protect people against the evil eye in many countries across the middle east.
The true costs incurred by businesses for technology downtime

The research, conducted by Vanson Bourne, which surveyed 1,000 senior IT decision-makers and 2,000 end users at organizations with at least 1,500 employees across the U.S., the U.K., France, and Germany, shows that employees are losing an average of 28 minutes every time they have an IT-related problem. The report also shows that IT decision makers believe employees are experiencing approximately two IT issues per week, wasting nearly 50 hours a year. However, as only just over half of IT issues are being reported, the numbers are more likely to be nearly double that – close to 100 hours (two work weeks) a year. This has led to a vicious cycle of employees trying to fix IT problems on their own, leading to less engagement with the IT department, which doesn’t have visibility into how the technology is being consumed. There exists a major disconnect between IT departments and employees, with 84% of employees believing that their organizations should be doing more to improve the digital experience at work. However, a staggering 90% of IT leaders believe that workers are satisfied with technology in the workplace, highlighting the discrepancy between perception and reality of the digital employee experience.
Judges and lawyers learn Zoom rules in real time during coronavirus crisis

Ines Swaney, a certified Spanish interpreter, said her first experience with Zoom was a three-way conversation during a legal visit between an attorney in one city, the attorney's incarcerated client joining the conversation from jail in another city, and herself serving as an interpreter in a third city. One drawback with the Zoom platform is that it forces an interpreter to use consecutive interpreting instead of simultaneous interpreting, which is the preferred approach. Swaney said that online platforms also need to allow private conversations between an attorney and the judge, and among an attorney, client and interpreter who may need to speak privately for a brief period of time during a hearing. Tony Sirna, legal strategist and customer success manager at Verbit, said there are serious considerations the courts are working through, particularly ensuring due process with remote proceedings, technology interruptions, unauthorized recordings, exhibits, and the impact virtual appearances will have on defendants, for example. Sirna said in addition to standardizing software and recording technology, courts need to agree on procedural best practices, such as how exhibits and stipulations will be handled remotely.
Text ‘bomb’ crashes iPhones, iPads, Macs and Apple Watches – what you need to know

The problem appears to exists in how the latest shipping versions of Apple’s operating system handle a Unicode symbol representing specific characters written in Sindhi, an official language in part of Pakistan. The problem occurs most irritatingly when your device attempts to display a message notification. If you have configured your iPhone, for instance, to display a new message notification which includes a preview of the message, then iOS fails to properly render the characters and crashes with unpredictable results. You may find the only way to get around the problem is to completely reboot your device – but there is always the risk that you will receive a new boobytrapped notification. The problem can also manifest itself inside apps. For instance, some mischievous Twitter users have tweeted the offending characters causing other users to have their devices crash. Android users, meanwhile, are unaffected – and can watch the chaos with bemusement. Some of the earliest reports suggested that for the attack to work the Sindhi characters had to be used in conjunction with an Italian flag emoji.
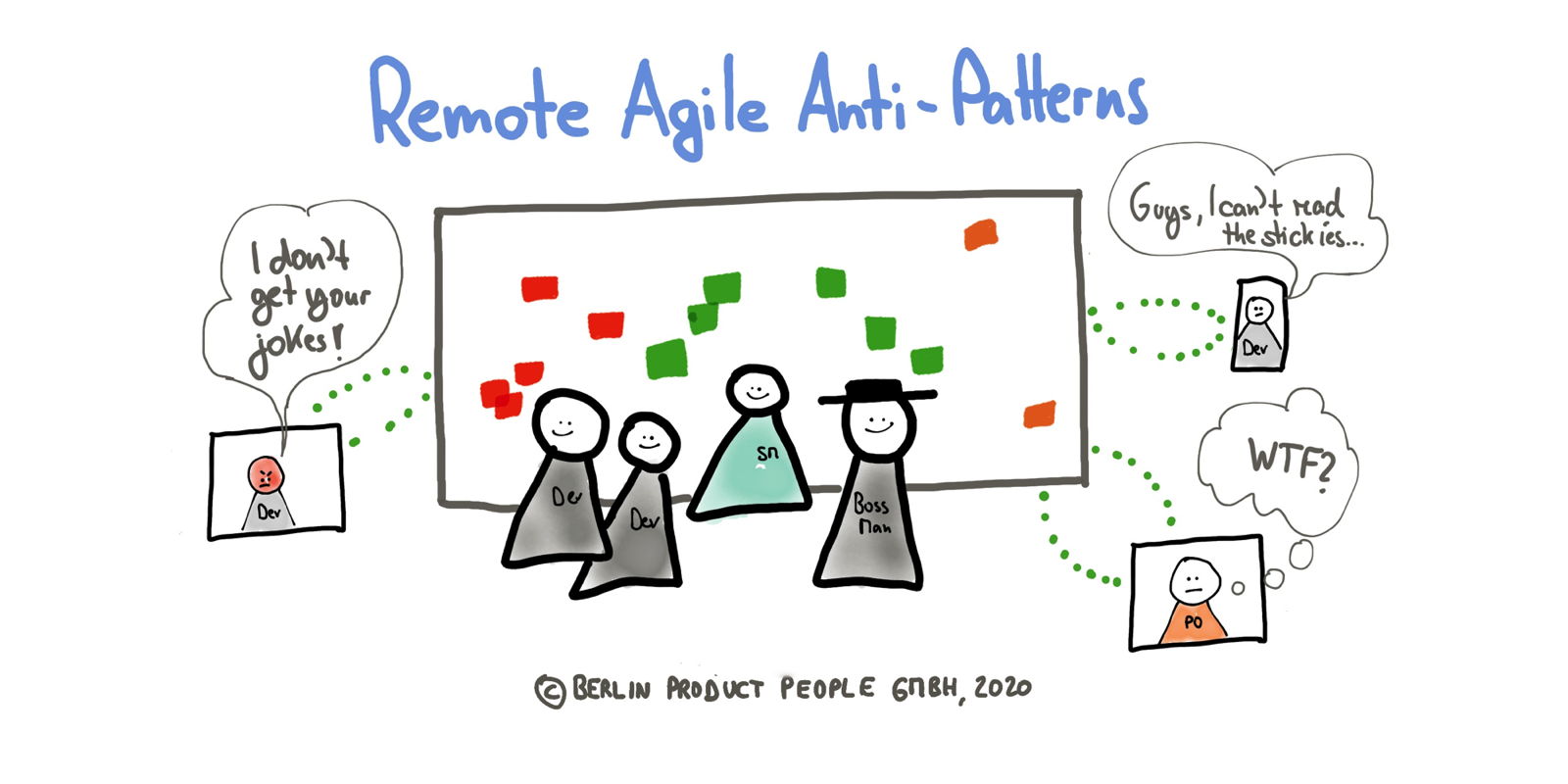
What Is Agile Enterprise Architecture? Just Enough, Just in Time
Agile is based on the concept of “just in time.” You can see this in many of the agile practices, especially in DevOps. User stories are created when they are needed and not before, and releases happen when there is appropriate value in releasing, not before and not after. Additionally, each iteration has a commitment that is met on time by the EA team. EA is missing the answer to the question of “what exactly is getting delivered?” This is where we introduce the phrase “just enough, just in time” because stakeholders don’t just simply want it in time, they also want just enough of it — regardless of what it is. This is especially important when communicating with non-EA professionals. In the past, enterprise architects have focused on delivering all of the EA assets to stakeholders and demonstrating the technical wizardry required to build the actual architecture. ... Create a marketing-style campaign to focus on EA initiatives, gathering and describing only what is required to satisfy the goal of the campaign.
Safe shopping: Your best options for NFC and contactless payments

Near-Field Communications, or NFC, is a technology built-in to many modern families of mobile devices, such as the iPhone, the Samsung Galaxy, Google Pixel, and many other Android smartphones. NFC, introduced in 2002, allows contactless data transfer between mobile devices and can to emulate a credit card for payments at POS terminals in retail stores. NFC lets the user pass their smartphone device over a payment terminal at a retailer in order to complete the purchase, provided that a supported "e-Wallet" platform is used. Keep in mind, however, that NFC still requires you get relatively close to the payment terminal and the person running it, and may even require you physically interact with a keypad or virtual keypad/screen to initiate a transaction -- so wear gloves or have the employee initiate the transaction on your behalf, and if you have to touch the terminal, do not touch your face, and wash your hands immediately afterward. Be sure you maintain safe distances when using it, or shop where there is a plexiglass barrier between you and the retail employee.
Go as a Scripting Language
Go's growing adoption as a programming language that can be used to create high-performance networked and concurrent systems has been fueling developer interest in its use as a scripting language. While Go is not currently ready "out of the box" to be used as a replacement for Bash or Python, this can be done with a little effort. As Codelang's Elton Minetto explained, Go has quite some appeal to be used as a scripting language, including its power and simplicity, support for goroutines, and more. Google software engineer Eyal Posener adds more reasons to adopt Go as a scripting language, such as the availability of a rich set of libraries and the language terseness, which makes maintenance easier. ... Being able to use the same language for day-to-day tasks and less frequent scripting task would greatly improve efficiency. Go is also a strongly typed language, notes Cloudflare engineer Ignat Korchagin, which can help to make Go scripts more reliable and less prone to runtime failure due to such trivial errors as typos.
Quote for the day:
"A leader is one who sees more than others see and who sees farther than others see and who sees before others see." -- Leroy Eimes