Cisco integrates SD-WAN connectivity with Google Cloud

The Cisco/Google platform is important because software- and infrastructure-as-a-service (SaaS and IaaS) offerings have been driving SD-WAN implementations in the past year, experts say. “One of the key drivers of SD-WAN has been the increasing consumption of cloud services in the enterprise, across both IaaS and SaaS applications,” said Rohit Mehra, vice president, network infrastructure at IDC. “With some of the largest public cloud providers playing an increasing role in how these enterprise apps are consumed and delivered, and bringing their vast global networks to bear, they will increasingly have a role to play with how WANs are architected going forward.” For enterprises, one of the key takeaways from this announcement is that “SD-WANs will now be able to play a better functional role in the delivery of cloud services such as IaaS and SaaS, and likewise, the large public-cloud purveyors will benefit from providing a stronger value proposition towards multi-cloud deployments,” Mehra said. "Secondly, enterprises will benefit in terms of extending policy and governance beyond applications to other attributes such as locations/geo and multiple clouds.”
The new normal: A step-by-step guide for the enterprise
From a business perspective, we need to identify and understand the negative effects that occurred during the lockdown. What additional damage will likely occur in the short and long terms? This can range from relatively minor problems, such as a slowdown of some customer deliveries or lack of materials for manufacturing, to a complete shutdown of some operations due to on-premises systems that could not be maintained or fixed during the lockdown. You need to assign dollar amounts to each issue. Keep in mind that some of these will be hard costs, meaning sales and billing. Others will be soft costs, such as reputation. What points hurt the business the most? We need this information to prioritize triage. For most enterprises, this step will immediately identify the need to migrate some assets to cloud. The migration will typically target existing on-premises systems that managed to limp through the crisis. Based on historical migration data, the most common move will involve a “lift and shift” of resources, such as storage and compute, to a public cloud provider. Most enterprises will opt to refactor the applications at a later date; a few will refactor as the applications migrate.
Here are six tech roles companies want to fill now, despite the coronavirus lockdown

"The fact that recruitment is still continuing with relative strength in IT is perhaps unsurprising due to the on-going need across most sectors to conduct operations remotely," said Ann Swain, CEO of APSCo. John Gaughan, managing director of technology recruitment firm Finlay James, said he has a number of clients who are hiring and using remote on-boarding when filling SaaS tech sales roles and technology leadership positions. Recruiters are switching from in-person interview to video meetings with candidates, and in some cases, with everyone working from home, it may be some time before new recruits actually meet the people they are working with. The APSCo report also noted that recruitment for marketing has also held up surprisingly well, which it said is probably down to businesses ramping up their digital marketing and communications activities. There has also been an increase in roles involving employee engagement. "With many teams now working from home, the challenge of keeping remote employees engaged and operating as a cohesive unit has never been greater," the report said.
Contactless Payments: Healthy COVID-19 Defense

From a fraud-fighting standpoint, compared with swiping a card and signing a paper receipt, contactless is much more secure. And while some call these capabilities "tap and go," in reality, there's no contact required: You just have to wave your card or compatible smartphone close to the card reader until it beeps. Cards with this capability began to be rolled out in the U.K. in 2008, and the vast majority of payment terminals in stores now work with them. Other systems that don't get refreshed very often - for example, inside buses - have been slowly catching up. Here in the Scottish city of Dundee, last year most buses finally got upgraded with the ability to accept contactless payments. Many newer smartphones also have contactless capability via Apple Pay, Android Pay or Samsung Pay. Just load a payment card and use your smartphone to pay without touching anything, up to certain amounts. As a bonus, the smartphone-based approaches add additional layers of security, such as needing to use your fingerprint or face to unlock the contactless payment capability.
Remote Agile (Part 4): Anti-Patterns
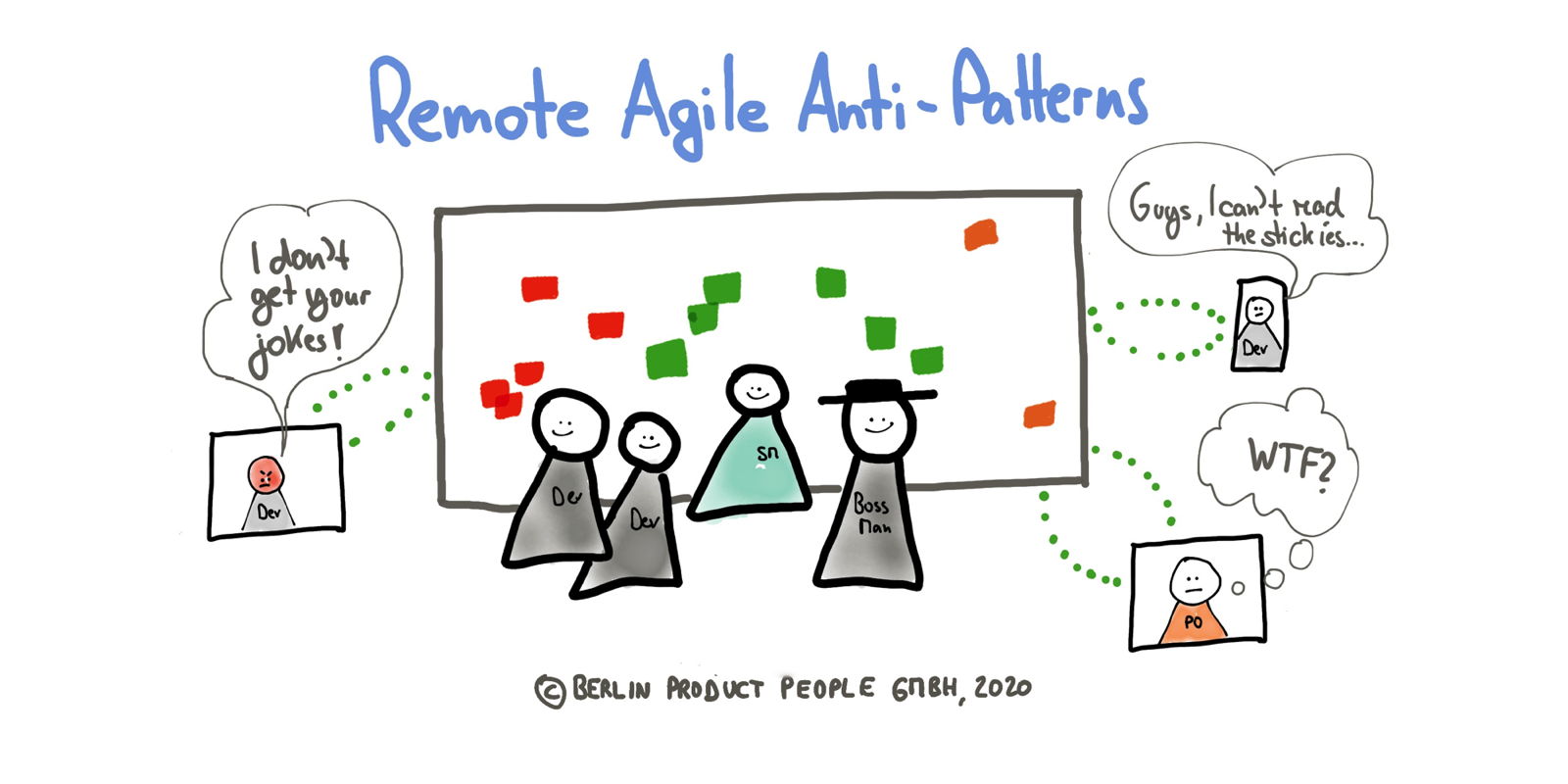
Hybrid events create two classes of teammates — remote and co-located — where the co-located folks are calling the shots. Beware of the distance bias — when out of sight means out of mind — thus avoiding the creation of a privileged subclass of teammates: “Distance biases have become all too common in today’s globalized world. They emerge in meetings when folks in the room fail to gather input from their remote colleagues, who may be dialing in on a conference line.” To avoid this scenario, make sure that once a single participant joins remotely, all other participants “dial in,” too, to level the playing field. Every communication feels like a (formal) meeting. ... Instead, put trust in people, uphold the prime directive, and be surprised what capable, self-organizing people can achieve once you get out of their way. Trust won’t be built by surveilling and micro-managing team members. Therefore, don’t go rogue; the prime directive rules more than ever in a remote agile setup. Trust in people and do not spy on them — no matter how tempting it might be. Read more about the damaging effect of a downward spiraling trust dynamic from Esther Derby.
COVID-19 & The Digital Imperative

In a recent interview, John Chambers, former Cisco CEO and now Venture Capitalist, said the pandemic will force many “companies to use this moment to make the transition to digital. Things will get worse before they get better— that is the realistic optimist in me speaking,” said Chambers, who has predicted up to 40% of the Fortune 500 and 70% of startups will no longer be around in a decade if they don’t make the digital transition. The disruptions brought about by the pandemic can be expected to accelerate the shift to digital that has already been underway. It is not just that organizations the world over have radically altered their work environments to accommodate work from home and technologies such as video conferencing and remote networking on a massive scale. It is also that the consequences of the pandemic are likely creating digital disruption opportunities and imperatives across the economy, in industries as diverse as food and beverage, hospitality, real estate, travel, and government.
How microsegmentation architectures differ

It's important to remember that microsegmentation is not just a data center-oriented technology. "Many security incidents start on end-user workstations, because employees click on phishing links or their systems become compromised by other means," Cross says. From that initial point of infection, attackers can spread throughout an organization's network. "A microsegmentation platform should be able to enforce policies in the data center, on cloud workloads, and on end-user workstations from a single console," he explains. "It should also be able to stop attacks from spreading in any of these environments." As with many emerging technologies, vendors are approaching microsegmentation from various directions. Three traditional microsegmentation types are host-agent segmentation, hypervisor segmentation and network segmentation. ... This microsegmentation type relies on agents positioned in the endpoints. All data flows are visible and relayed to a central manager, an approach that can help reduce the pain of discovering challenging protocols or encrypted traffic.
Google wants to make it easier to analyse health data in the cloud

Dr John Halamka, president of Mayo Clinic Platform, said: "We're in a time where technology needs to work fast, securely, and most importantly in a way that furthers our dedication to our patients. Google Cloud's Healthcare API accelerates data liquidity among stakeholders, and in-return, will help us better serve our patients." The issue of interoperability remains a tricky subject within healthcare. Battles over data formats and ownership stymies efforts to join up healthcare systems and make patient data available to healthcare professionals whenever and wherever they need it. In the US, inroads have been made recently through the passing of rules by Centers for Medicare and Medicaid Services (CMS) and the National Coordinator for Health Information Technology (ONC) to make it easier for healthcare organisations to exchange patient data, and for patients to access their own information. Google said its Cloud Healthcare API was designed to scale and support interoperability and patient access. It added that the COVID-19 pandemic had made the need for increased data interoperability more important than ever.
How developer teams went remote overnight

Remote work isn’t new for communications API specialist Twilio, but the pandemic has caused a massive shift. Prior to the coronavirus outbreak, CEO Geoff Lawson told TechCrunch that around 10 percent of the company worked remotely. “For a company like us to go from partially virtual to fully virtual in a short period of time, it’s not without its hiccups, but it has worked pretty well,” he said. Some of that 10 percent of remote workers included the team of Marcos Placona, manager for developer evangelism at Twilio. “My team has always worked on a distributed basis with direct reports in the US, UK, and across Europe,” Placona told InfoWorld. The various time zones involved make it “tough to work this way,” he admits, “but we have regular check-ins with the team and individuals with weekly one-to-ones.” Developer evangelists at Twilio still contribute code and have to track contributions, alongside writing documentation and filtering through reams of customer feedback. During the pandemic this team has shifted to holding daily remote stand-ups.
A Tale of 3 Breaches: Incident Response Challenges

Three recently disclosed health data security incidents - including the discovery of a large email hack that happened nearly a year ago - serve as reminders of the ongoing incident response challenges facing healthcare organizations. A 2019 email hacking incident that affected 112,000 individuals was disclosed last week by Dearborn, Michigan-based Beaumont Health. Also recently reported were: a February ransomware attack on Wilmington, Del.-based substance abuse treatment provider Brandywine Counseling and Community Services that affected clinical records of an undisclosed number of patients, and a phishing scam impacting more than 27,000 patients and employees of Wisconsin-based Advocate Aurora Health. The COVID-19 crisis is likely to make it even more difficult for healthcare organizations to respond to security incidents, some observers say. "As long as COVID-19 drives IT activities in supporting remote workers and setting up patient triage tents with access to technology infrastructure, IT may have difficulty monitoring network activity for anomalous events unless a security operations center is in place to monitor around the clock, along with centralized log event management that can automate detection of and alerting on activities of concern," notes Keith Fricke
Quote for the day:
"Many men may see the King in a Kid but it takes a true leader to nurture it" -- Bernard Kelvin Clive
No comments:
Post a Comment