Sophia shared several messages with the president and responded to what he was saying. Sophia’s structural framework includes a camera that looks for visual cues such as facial expressions when deciding when to keep a conversation moving. The humanoid, whom Hanson Robotics gave an Audrey Hepburn look for this leg of the trip, started the conversation by telling Aliyev how she had obtained an ASAN visa at Baku airport and described Baku’s architecture. Sophia praised Aliyev for championing the ASAN initiative; “Your visit here [at the ASAN complex dedication] underscores the special attention you are giving to e-governance and the innovation ecosystem.” The visit mainly underscored two things; firstly that the ASAN agency is harnessing the electronic and cyber worlds to make citizens’ lives better, and secondly, it further shows Hanson Robotics is capable of making a robot whose artificial intelligence can not only help it learn tasks — like cleaning — but also have robust conversations with humans.
It’s banking Jim, but not as we know it
A completely different FinTech world had also emerged out of Asia, and many suddenly woke up to the fact that they hadn’t even been looking. By way of example, in 2018, Alipay and WeChat Pay EACH processed more dollars in a month through their apps than PayPal processes in a year. China has seen an explosion of online mobile payments, rising from $5 trillion in 2016 to $15.5 trillion in 2017 and predicted to boom to $45 trillion in 2020. Compare this to the USA and you see a quiet revolution, and it is not just about Alibaba and Tencent, but the whole FinTech scene emerging from Asia, Africa and South America. This FinTech scene began without the blinkers of big bank thinking, and has created wholly integrated internet finance on mobile apps, or superapps, seamlessly. ... Banks should feel duly threatened by FinTech 3.0 because they are control freaks by nature, who partner with no one unless they have to. For a big bank to about face and start to become an open market collaborator is a huge cultural change and, in the meantime, the challenger banks are actively building their ecosystems. FinTech 3.0, which starts around now and will play through 2025, will be the most interesting of these three phases as yes, it truly does disrupt banking.
Enterprise Architecture Governance: A Holistic View
Enterprise Architecture Governance is a practice encompassing the fundamental aspects of managing a business. It involves firm leadership, a complete knowledge of organizational structure, a confident direction, and the enablement of effective IT processes to promote an enterprise’s strategies. However, if distilled into just one area, the objective of EA Governance is to harmonize the architectural requirements of an enterprise into an understandable set of policies, processes, procedures and standards—all of which to ensure an organization’s visions and standards are aligned with actual business requirements. It is not an academic discipline detached from present reality, nor is it based on speculations of what is and what is not occurring. EA Governance is an integral part of deploying and maintaining business strategies. And in many ways, it is a never-ending job. Without EA Governance, an organization is likely to tumble into a web of non-standardized technology, bad product purchases or development, and monolithic architectures.
Designing Organisations with Purposeful Agile
If we think of organisations as a living system, similar to an individual human being, I like to define the culture of an organisation as its "unconscious" part. The first thing needed to change any culture is to become aware of the installed one. This is a very difficult piece. People love to do things rather than observe what things they do, and how they do them. Revealing the installed culture may be one of the most difficult parts to get to the 3rd stage. There is no change that can happen if there is no space for change. Usually the "change space" is filled with our common beliefs and mental models that make us behave the way we behave and make decisions the way we do. An example of creating space for change is working on managers’ agenda, making them available for their teams. It enables listening to the way the organisation operates and seeing what emerges. Freeing the busy agendas allows change to take place and helps us sense and grow awareness of the "installed culture".
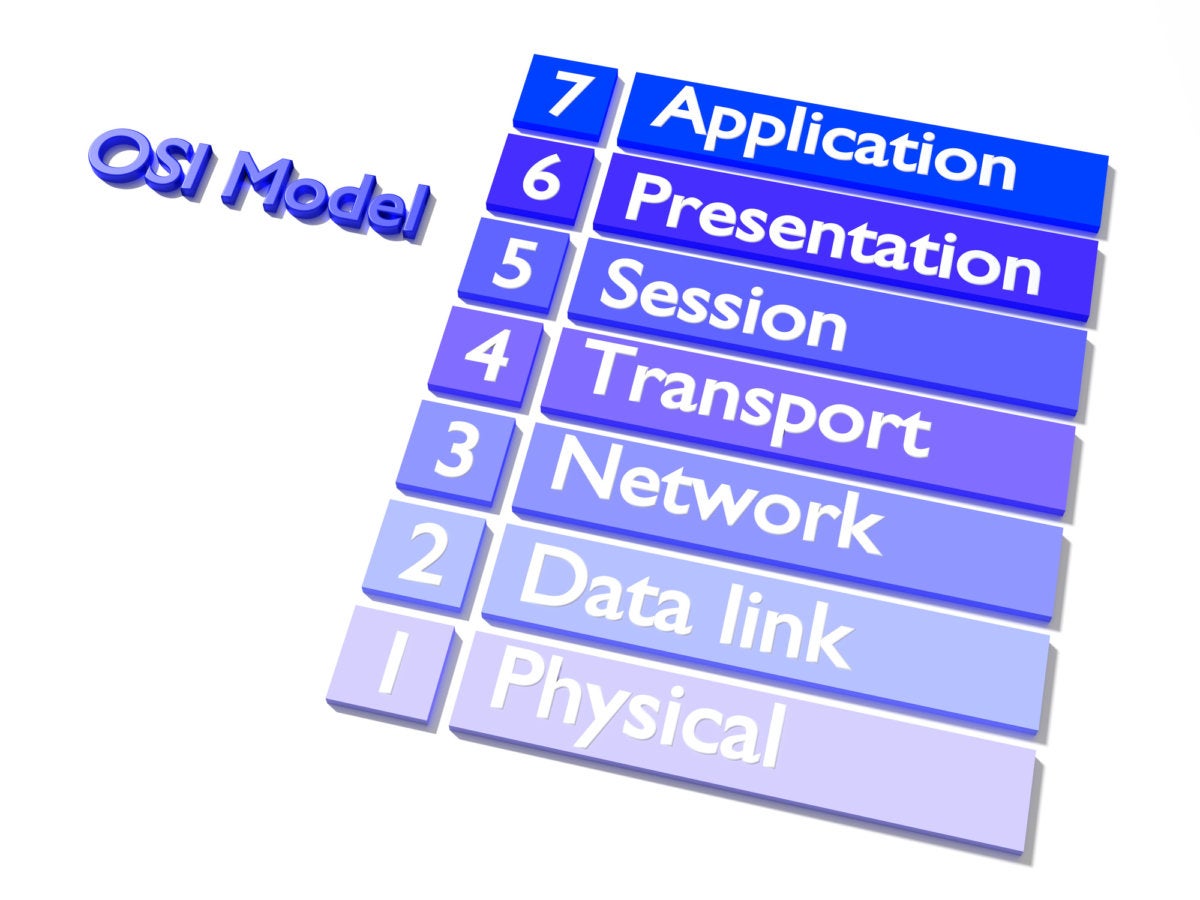
Enterprise Agility Through Enterprise Architecture

Understanding Enterprise Architecture capabilities is a very important aspect while driving this transformation as it supports the representation of the business and IT aspects of the enterprise and their inter-relationships and dependencies. Enterprise Architecture is depiction of the target structure for organizations processes. It describes how business goals are realized by business processes, and how this business processes can be better served through technology. It has a critical role and is a strategic tool in addressing how business aligns well with the IT teams for addressing the changing business needs (changes from both business process and technology perspective); how the complexity in handling these challenges can be simplified by breaking down further into multiple aspects to tackle them; to deal with the dependencies between various upstream and downstream systems of various portfolios/LOBs by taking an abstraction view at each layer.
Behavioral Economics & Enterprise Architecture (2): Enterprise Architecture
The promise of enterprise architecture is that it helps improve decision making. Typically, the role of the enterprise architect is to advise and enable other stakeholders to make better decisions. Therefore, Enterprise Architecture – more than anything else – is a social discipline, in that it demands social skills and interaction in order for practitioners to successfully engage with stakeholders and change their behavior. Not surprisingly, enterprise architects are more effective in steering decisions when they consider that they are dealing with Humans. And Humans, as we’ve explained in our previous blog, can be irrational, naïve and impulsive. By taking these biases into consideration and making choices as easy as possible for decision makers, architects can dramatically increase the likelihood of getting their point across and ultimately help deliver better business outcomes for the organization. Here, we present some principles to get you started.
How to build your enterprise architecture using the cloud

Due to the risks and implications of cybercrime and data breaches, many businesses are opting for a security-first tenet – and rightly so. The emphasis will be making sure that data is as secure as possible, both while in transit and during storage. In addition, all workloads may need to be authorised by the security team prior to deployment. Some companies operate on a zero-trust basis with their cloud service provider, retaining control of all encryption keys (e.g. managing key rotation, storing keys on an HSM, etc.). Others operate on a total trust basis, relying on the cloud provider's own enterprise-grade security processes to keep data secure. Whichever level of trust you employ depends on a variety of factors, such as your security approach and your familiarity with the cloud provider you’re using. The importance of prioritising tenets cannot be understated. If done correctly, they will help you to frame your policies, procedures and standards, building an enduring foundation for your enterprise architecture.
How to Build a Secure API Strategy for the API Economy
APIs could expose a company’s transactional systems to the outside world in unprecedented ways. Systems of record are not intended to be available publicly. As such, development teams must test, test, and retest APIs stringently before release. Once developers embed an unsecured API into an enterprise's applications, it can infiltrate and reduce that organization’s overall security posture. Some enterprises have hundreds of consumer-facing web applications, and each of those websites could have anywhere from five to 32 vulnerabilities — that’s a staggering risk of exposure. Sometimes, developers mistake the capabilities of API management tools and expect them to solve all API security challenges. API management tools do provide security policies that work at the perimeter, but not all of them play a role in securing the business logic that serves up the API. For this, developers need to treat APIs as yet another form factor for their applications and ensure that adequate attention is paid to securing them.
Edge Computing: The Driving Force in New Architecture Innovation
Every edge computing project starts with collecting data from IoT devices, sensors or mobile users, and the success of the project depends on ability to transform the data and into actionable intelligence while delivering a return on investment. Initial deployments start with connecting gateway-class devices to IoT devices/sensors at the edge and performing most of the data processing in the server class infrastructure in a backend data center or cloud. Gateways perform the data collection, aggregation, and filtering, and send the useful data for processing to a centralized cloud or data center. As we see larger scale deployments and more devices (e.g. smart factories, oil & gas, connected vehicles), server class infrastructure will move closer to edge to enable data processing and decision making at scale with lower latency. These servers may reside on-premise at the edge location where sensors and gateways are located or they may reside at a central office or micro-data centers between the edge location and backend centralized cloud.
How This Blockchain Innovation Could Impact Billions
Athman Ali, CEO of impact investing firm 1000 Alternatives, has partnered with Everest to address some of the economic challenges facing people and countries in Sub-Saharan Africa. The partnership was originally focused on reducing transportation costs in the region—cut costs of transport and the cost of almost everything else will fall, too. “We have since deepened our partnership to position the Everest platform for use by innovators, incubation hubs and social entrepreneurs to spur innovations in the various areas that 1000 Alternatives focuses towards achieving positive social impact,” Ali says. The expanded relationship now includes another area with the potential to impact people in dramatic ways. “Legal identity, land titles tracking and documentation of ownership and transfers of assets remain a big challenge in African countries,” Ali says. “Opportunities to use the blockchain platform to improve services in education, health and livelihoods is another set of opportunities.”
Quote for the day:
"Nobody in your organization will be able to sustain a level of motivation higher than you have as their leader." -- Danny Cox