
Digital channels can provide an effective gateway to emotionally connect an organization to its consumers. Technology companies that are consumers’ favorite brands not only have best-in-class digital capabilities; they also do a superior job integrating digital and physical environments and integrating both strategically to foster an emotional connection. Amazon’s digital prowess allows customers to discover, research, and buy products in minutes, while enabling its physical supply chain to deliver the goods most efficiently. Merging the physical with the virtual/digital is key to superior customer experience: putting the “real in digital and digital in real.” According to our survey, consumers are more likely to increase use of digital channels (both online and mobile) if banks increase security, provide more real-time problem resolution, and allow for more regular banking transactions to be handled digitally. On the other side, adding digital self-service screens at brick-and-mortar locations, or being able to connect with a bank representative virtually will increase consumers’ likelihood to use branches.
DevSecOps An Effective Fix for Software Flaws
Veracode judges the duration of a flaw based on how many times the same issue shows up in a scan after its initial discovery, Eng says. "If the flaw shows up three, four, five times, we can see that this was discovered in January, and you scanned it every month, and it's still there in May—then in June it goes away. So you assume that to mean that they closed it after four months," he explains. Eng's use of "months" as the time scale for remediation is not arbitrary. According to the Veracode research, more than 70% of all flaws were still present a month after initial discovery, and nearly 55% had not been remediated after three months. In fact, while roughly a quarter of all code flaws were dealt with inside 21 days, another quarter were still open issues after a year. The length of time from discovery to fix varied according to the flaw's severity — but not very much, Eng says. Based on a scale that rates the most severe issues a 5 and the least severe a 1, he explains, "We expected the fives to be fixed the fastest and then the fours, threes, twos, but it wasn't like that."
Cathay Pacific under fire over breach affecting 9.4 million passengers

Brian Vecci, technical evangelist at Varonis, said that as insiders and external actors get more sophisticated, organisations must be able to do a better job of detecting suspicious activity quickly and reducing the time it takes to investigate an incident. “Months went by between when this attack was apparently noticed and when investigators figured out sensitive data might have been stolen, and then almost half a year passed before it was announced,” he said. “That is unacceptable and highlights just how far behind the eight ball most organisations are when it comes to threat hunting and incident response.” The data breach includes 860,000 passport numbers, about 245,000 Hong Kong identity card numbers, 403 expired credit card numbers and 27 credit card numbers with no card verification value (CVV) that were accessed, although the airline claims no passwords were compromised. Breached data also includes passenger names, nationalities, dates of birth, telephone numbers, email and physical addresses, passport numbers, identity card numbers and historical travel information – all extremely valuable to cyber criminals for identity theft, phishing and fraud.
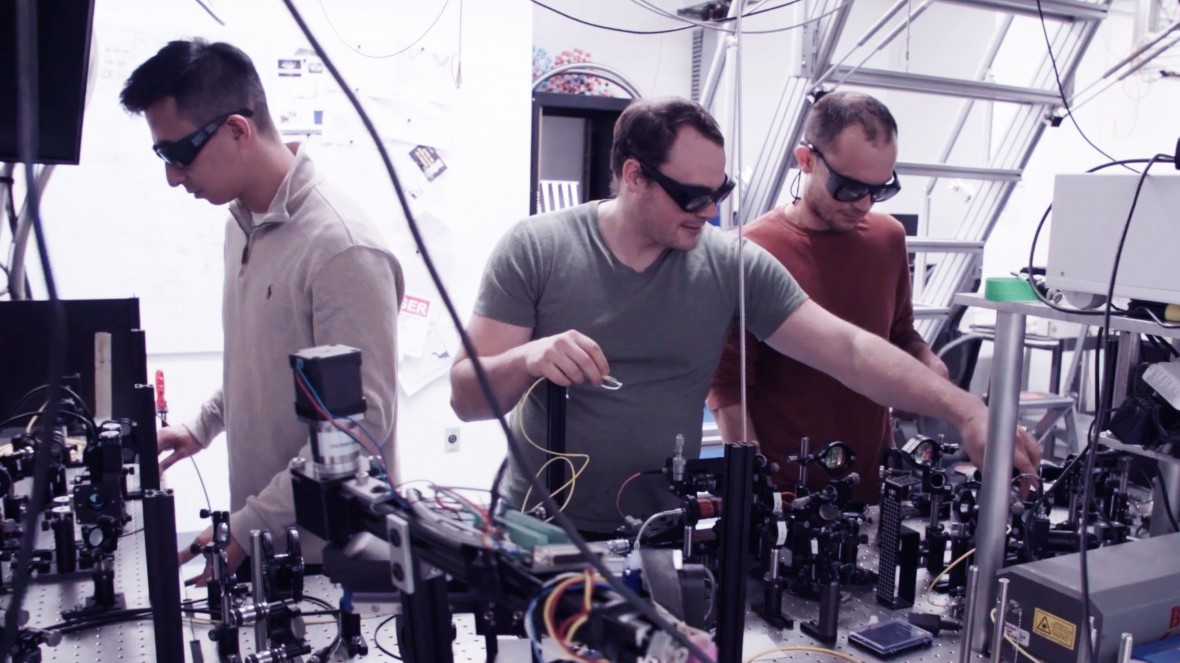
The US pushes to build unhackable quantum networks
The QKD approach used by Quantum Xchange works by sending an encoded message in classical bits while the keys to decode it are sent in the form of quantum bits, or qubits. These are typically photons, which travel easily along fiber-optic cables. The beauty of this approach is that any attempt to snoop on a qubit immediately destroys its delicate quantum state, wiping out the information it carries and leaving a telltale sign of an intrusion. The initial leg of the network, linking New York City to New Jersey, will allow banks and other businesses to ship information between offices in Manhattan and data centers and other locations outside the city. However, sending quantum keys over long distances requires “trusted nodes,” which are similar to repeaters that boost signals in a standard data cable. Quantum Xchange says it will have 13 of these along its full network. At nodes, keys are decrypted into classical bits and then returned to a quantum state for onward transmission. In theory, a hacker could steal them while they are briefly vulnerable.
Technology risks: What CIOs should know and steps they can take
CIOs should ensure that any new technology is only accessible to those who absolutely need it for their job, OpenVPN's Dinha recommended. Any access point should utilize two-factor authentication to keep hackers from taking control with brute-force attacks, and CIOs should educate their teams to make sure they understand technology risks and their role in protecting the company's data and privacy, he said. "Have a clear policy on how cybersecurity is managed with each individual piece of new technology and educate everyone on the best practices," Dinha said. When developers are creating AI or task automation, CIOs should be wary of what shortcuts their teams take and what "Band-Aids" are being deployed, SiteLock's Ortega said. One major concern is to ensure that AI has access only to the data necessary to complete its assigned task, she explained. "Taking a proactive approach and instilling a culture of security awareness stops convenience from becoming dangerous, keeping sensitive data safe at every level," Ortega said.
How 802.11ax Improves the Experience for Everyone

In 802.11ax OFDMA, the access point assigns client traffic to sub-channels, not just for the downlink but also for the uplink. The new ‘trigger frame’ mechanism allows the access point to poll clients to discover what traffic they wish to send on the uplink. When it collects the trigger frame responses, it designs a schedule and sends it to clients in another trigger frame. Clients then construct frames according to their instructions, setting data rates, transmit levels and sub-channels, and transmit data frames back to the access point. The other multi-user mechanism in 802.11ax is multi-user MIMO. This uses the same trigger-frame control protocol as OFDMA, improving on 802.11ac. Multi-user MIMO is itself a complex protocol, requiring sounding packets to determine multipath conditions and group MIMO clients, all under the control of the access point. At any moment, the access point can choose to use traditional single-user transmissions, or multi-user, with OFDMA or MIMO. This opens new dimensions in traffic management.
Bridging the IT Talent Gap: Find Scarce Experts
The technology industry's unemployment rate is well below the national average, forcing companies to compete aggressively for top talent. When presented with a range of recruitment strategies by a recent Robert Half Technology questionnaire — including using recruiters, providing job flexibility and offering more pay — most IT decision makers said they are likely to try all approaches in order to land the best job candidates for their teams. ... Look beyond the typical sources, suggested Art Langer, a professor and director of the Center for Technology Management at Columbia University and founder and chairman of Workforce Opportunity Services (WOS), a nonprofit organization that connects underserved and veteran populations with IT jobs. "There is a large pool of untapped talent from underserved communities that companies overlook," he explained. Businesses are now competing in a global market. "New technology allows us to connect with colleagues and potential partners around the world as easily as with our neighbors," Langer said. "Companies hoping to expand overseas can benefit from employees who speak multiple languages."
Scaling Agile in a Data-Driven Company

Agile is, first of all, a mindset: practicing Agile is not being Agile. Changing and evolving the organization's mindset was not easy. Understanding and assimilating the values and principles of the Agile Manifesto requires exercise, practice, patience and a continuous work with people and on the company culture. Aspects such as micro-management and the continuous push on the teams were part of our daily life, and only with continuous coaching and on-the-job training we managed to bring out the value and the trust of an empowered and autonomous team. Also the interpretation of the roles of Product Owner and Scrum Master were very difficult at the beginning: the PO was often focused more on “How to do” instead of “What to do”, while the Scrum Master who came from Technical Leaders often did not focus on their role as facilitators/ Servant Leaders. It was important to understand the essence of the two roles in Scrum. An Agile transformation is first of all a cultural transformation, then it also becomes a process change; the process is the child of culture.
U.S. state banking regulators sue government to stop fintech charters
A body of U.S. state banking regulators on Thursday sued the federal government to void its decision to award national bank charters to online lenders and payment companies, saying it was unconstitutional and puts consumers and taxpayers at risk. The Conference of State Bank Supervisors (CSBS) said it had filed a complaint in the U.S. District Court for the District of Columbia against the Office of the Comptroller of the Currency (OCC) over its plan, announced in July, to issue bank charters to financial technology firms. “Common sense and the law tell us that a nonbank is not a bank. Thus, CSBS is calling on the courts to stop the unlawful, unwarranted expansion of powers by the OCC,” John Ryan, CSBS president and CEO said in a statement. Fintech firms have long pushed for national bank charters to let them operate nationwide without needing licenses in every state, a process they say can impede growth and boost costs. OCC spokesman Bryan Hubbard did not immediately respond to a request for comment. The regulator has previously said it would vigorously defend its authority to grant the charters.
Defense, security and the real enemies

Recognize the dangers presented by these countries at all levels of government. This is one of the times where party affiliation or stances on issues do not matter. We need to take the agencies and people we’ve empowered with H.R. 1616 - Strengthening State and Local Cyber Crime Fighting Act of 2017, and Executive Order 13800, Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure, both of which have been signed by President Trump, and make actual protection the national priority. The latter bill is very comprehensive and provides an excellent start as to what companies should be doing. We need to plan to protect what we deploy as part of how we implement technology and plan to keep the technology as current as possible and most importantly well-protected with an engaged team. We make it easy for Moscow, Beijing or Pyongyang when we don’t protect ourselves. Many of these successful attacks take advantage of long-standing security holes to devastating effect.
Quote for the day:
"Before you are a leader, success is all about growing yourself. When you become a leader, success is all about growing others" -- Jack Welch
No comments:
Post a Comment