Quote for the day:
"Supreme leaders determine where generations are going and develop outstanding leaders they pass the baton to." -- Anyaele Sam Chiyson
Why code quality should be a C-suite concern
 At first, speed feels like progress. Then the hidden costs begin to surface:
escalating maintenance effort, rising incident frequency, delayed roadmaps and
growing organizational tension. The expense of poor code slowly eats into
return on investment — not always in ways that show up neatly on a
spreadsheet, but always in ways that become painfully visible in daily
operations. ... During the planning phase, rushed architectural decisions
often lead to tightly coupled, monolithic systems that are expensive and risky
to change. During development, shortcuts accumulate into what we call
technical debt: duplicated logic, brittle integrations and outdated
dependencies that appear harmless at first but quietly erode system stability
over time. Like financial debt, technical debt compounds. ... Architecture
always comes first. I advocate for modular growth — whether through a well-
structured modular monolith that can later evolve into microservices, or
through service-oriented architectures with clear domain boundaries. Platforms
such as Kubernetes enable independent scaling of components, but only when the
underlying architecture is cleanly segmented. Language and framework choices
matter more than most leaders realize. ... The technologies we select, the
boundaries we define and the failure modes we anticipate all place invisible
limits on how far an organization can grow. From what I’ve seen, you simply
cannot scale a product on a foundation that was never designed to evolve.
At first, speed feels like progress. Then the hidden costs begin to surface:
escalating maintenance effort, rising incident frequency, delayed roadmaps and
growing organizational tension. The expense of poor code slowly eats into
return on investment — not always in ways that show up neatly on a
spreadsheet, but always in ways that become painfully visible in daily
operations. ... During the planning phase, rushed architectural decisions
often lead to tightly coupled, monolithic systems that are expensive and risky
to change. During development, shortcuts accumulate into what we call
technical debt: duplicated logic, brittle integrations and outdated
dependencies that appear harmless at first but quietly erode system stability
over time. Like financial debt, technical debt compounds. ... Architecture
always comes first. I advocate for modular growth — whether through a well-
structured modular monolith that can later evolve into microservices, or
through service-oriented architectures with clear domain boundaries. Platforms
such as Kubernetes enable independent scaling of components, but only when the
underlying architecture is cleanly segmented. Language and framework choices
matter more than most leaders realize. ... The technologies we select, the
boundaries we define and the failure modes we anticipate all place invisible
limits on how far an organization can grow. From what I’ve seen, you simply
cannot scale a product on a foundation that was never designed to evolve.How to regulate social media for teens (and make it stick)
 Noting that age assurance proposals have broad support from parents and
educators, Allen says “the question is not whether children deserve
safeguarding (they do) but whether prohibition is an effective tool for
achieving it.” “History suggests that bans succeed or fail not on the basis of
intention, but on whether they align with demand, supply, moral legitimacy and
enforcement capacity. Prohibition does not remove human desire; it reallocates
who fulfils it. Whether that reallocation reduces harm or increases it depends
on how well policy engages with the underlying economics and psychology of
behaviour.” ... “There is little evidence that young people themselves view
social media as morally repugnant. On the contrary, it is where friendships
are maintained, identities are explored and social status is negotiated. That
does not mean it is harmless. It means it is meaningful.” “This creates a
problem for prohibition. Where demand remains strong, supply will be found.”
Here, Allen’s argument falters somewhat, in that it follows the logic that
says bans push kids onto less regulated and more dangerous platforms. I.e.,
“the risk is not simply that prohibition fails. It is that it succeeds in
changing who supplies children’s social connectivity.” The difference is that,
while a basket of plums and some ingenuity are all you need to produce
alcohol, social media platforms have their value in the collective. Like Star
Trek’s Borg, they are more powerful the more people they assimilate.
Noting that age assurance proposals have broad support from parents and
educators, Allen says “the question is not whether children deserve
safeguarding (they do) but whether prohibition is an effective tool for
achieving it.” “History suggests that bans succeed or fail not on the basis of
intention, but on whether they align with demand, supply, moral legitimacy and
enforcement capacity. Prohibition does not remove human desire; it reallocates
who fulfils it. Whether that reallocation reduces harm or increases it depends
on how well policy engages with the underlying economics and psychology of
behaviour.” ... “There is little evidence that young people themselves view
social media as morally repugnant. On the contrary, it is where friendships
are maintained, identities are explored and social status is negotiated. That
does not mean it is harmless. It means it is meaningful.” “This creates a
problem for prohibition. Where demand remains strong, supply will be found.”
Here, Allen’s argument falters somewhat, in that it follows the logic that
says bans push kids onto less regulated and more dangerous platforms. I.e.,
“the risk is not simply that prohibition fails. It is that it succeeds in
changing who supplies children’s social connectivity.” The difference is that,
while a basket of plums and some ingenuity are all you need to produce
alcohol, social media platforms have their value in the collective. Like Star
Trek’s Borg, they are more powerful the more people they assimilate. The era of agentic AI demands a data constitution, not better prompts
 If a data pipeline drifts today, an agent doesn't just report the wrong
number. It takes the wrong action. It provisions the wrong server type. It
recommends a horror movie to a user watching cartoons. It hallucinates a
customer service answer based on corrupted vector embeddings. ... In
traditional SQL databases, a null value is just a null value. In a vector
database, a null value or a schema mismatch can warp the semantic meaning of
the entire embedding. Consider a scenario where metadata drifts. Suppose your
pipeline ingests video metadata, but a race condition causes the "genre" tag
to slip. Your metadata might tag a video as "live sports," but the embedding
was generated from a "news clip." When an agent queries the database for
"touchdown highlights," it retrieves the news clip because the vector
similarity search is operating on a corrupted signal. The agent then serves
that clip to millions of users. At scale, you cannot rely on downstream
monitoring to catch this. By the time an anomaly alarm goes off, the agent has
already made thousands of bad decisions. Quality controls must shift to the
absolute "left" of the pipeline. ... Engineers generally hate guardrails. They
view strict schemas and data contracts as bureaucratic hurdles that slow down
deployment velocity. When introducing a data constitution, leaders often face
pushback. Teams feel they are returning to the "waterfall" era of rigid
database administration.
If a data pipeline drifts today, an agent doesn't just report the wrong
number. It takes the wrong action. It provisions the wrong server type. It
recommends a horror movie to a user watching cartoons. It hallucinates a
customer service answer based on corrupted vector embeddings. ... In
traditional SQL databases, a null value is just a null value. In a vector
database, a null value or a schema mismatch can warp the semantic meaning of
the entire embedding. Consider a scenario where metadata drifts. Suppose your
pipeline ingests video metadata, but a race condition causes the "genre" tag
to slip. Your metadata might tag a video as "live sports," but the embedding
was generated from a "news clip." When an agent queries the database for
"touchdown highlights," it retrieves the news clip because the vector
similarity search is operating on a corrupted signal. The agent then serves
that clip to millions of users. At scale, you cannot rely on downstream
monitoring to catch this. By the time an anomaly alarm goes off, the agent has
already made thousands of bad decisions. Quality controls must shift to the
absolute "left" of the pipeline. ... Engineers generally hate guardrails. They
view strict schemas and data contracts as bureaucratic hurdles that slow down
deployment velocity. When introducing a data constitution, leaders often face
pushback. Teams feel they are returning to the "waterfall" era of rigid
database administration.QA engineers must think like adversaries
Test engineers are now expected to understand pipelines, cloud-native
architectures, and even prompt engineering for AI tools. The mindset has
become more preventive than detective. AI has become part of QA’s toolkit,
helping predict weak spots and optimise testing. At the same time, QA must
validate the integrity and fairness of AI systems — making it both a user and
a guardian of AI. ... With DevOps, QA became embedded into the pipeline —
automated test execution, environment provisioning, and feedback loops are all
part of CI/CD now. With SecOps, we’re adding security scans and penetration
checks earlier, creating a DevTestSecOps model. QA is no longer a separate
stage. It’s a mindset that exists throughout the lifecycle — from requirements
to observability in production. ... Regression testing has become AI-augmented
and data-driven. Instead of re-running all test cases, systems now prioritise
based on change impact analysis. The SDET role is also evolving — they now
bridge coding, observability, and automation frameworks, often owning quality
gates within CI/CD. ... Security checks are now embedded as automated gates
within pipelines. Performance testing, too, is moving earlier — with synthetic
monitoring and API-level load simulations. In effect, security and speed can
coexist, provided teams integrate validation rather than treat it as an
afterthought.
The biggest AI bottleneck isn’t GPUs. It’s data resilience
 The risks of poor data resilience will be magnified as agentic AI enters the
mainstream. Whereas generative AI applications respond to a prompt with an
answer in the same manner as a search engine, agentic systems are woven into
production workflows, with models calling each other, exchanging data,
triggering actions and propagating decisions across networks. Erroneous data
can be amplified or corrupted as it moves between agents, like the party game
“telephone.” ... Experts cite numerous reasons data protection gets short
shrift in many organizations. A key one is an overly intense focus on
compliance at the expense of operational excellence. That’s the difference
between meeting a set of formal cybersecurity metrics and being able to
survive real-world disruption. Compliance guidelines specify policies,
controls and audits, while resilience is about operational survivability, such
as maintaining data integrity, recovering full business operations, replaying
or rolling back actions and containing the blast radius when systems fail or
are attacked. ... “Resilience and compliance-oriented security are handled by
different teams within enterprises, leading to a lack of coordination,” said
Forrester’s Ellis. “There is a disconnect between how prepared people think
they are and how prepared they actually are.” ... Missing or corrupted data
can lead models to make decisions or recommendations that appear plausible but
are far off the mark.
The risks of poor data resilience will be magnified as agentic AI enters the
mainstream. Whereas generative AI applications respond to a prompt with an
answer in the same manner as a search engine, agentic systems are woven into
production workflows, with models calling each other, exchanging data,
triggering actions and propagating decisions across networks. Erroneous data
can be amplified or corrupted as it moves between agents, like the party game
“telephone.” ... Experts cite numerous reasons data protection gets short
shrift in many organizations. A key one is an overly intense focus on
compliance at the expense of operational excellence. That’s the difference
between meeting a set of formal cybersecurity metrics and being able to
survive real-world disruption. Compliance guidelines specify policies,
controls and audits, while resilience is about operational survivability, such
as maintaining data integrity, recovering full business operations, replaying
or rolling back actions and containing the blast radius when systems fail or
are attacked. ... “Resilience and compliance-oriented security are handled by
different teams within enterprises, leading to a lack of coordination,” said
Forrester’s Ellis. “There is a disconnect between how prepared people think
they are and how prepared they actually are.” ... Missing or corrupted data
can lead models to make decisions or recommendations that appear plausible but
are far off the mark. When open science meets real-world cybersecurity
If there is no collaboration, usually the product that emerges is a great
scientific specimen with very risky implementations. The risk is usually
caught by normal cyber processes and reduced accordingly; however, scientists
who see the value in IT/cyber collaboration usually also end up with a great
scientific specimen. There is also managed risk in the implementation with
almost no measurable negative impacts or costs. We’ve seen that if
collaboration is planned into the project very early on, cybersecurity can
provide value. ... Cybersecurity researchers often are confused and look for
issues on the internet where they stumble onto the laboratory IT footprint and
make claims that we are leaking non-public information. We clearly label and
denote information that is releasable to the public, but it always seems there
are folks who are quicker to report than to read the dissemination labels. ...
Encryption at rest (EIR) is really a control to prevent data loss when the
storage medium is no longer in your control. So, when the data has been
reviewed for public release, we don’t spend the extra time, effort, and money
to apply a control to data stores that provide no value to either the
implementation or to a cyber control. ... You can imagine there are many
custom IT and OT parts that run that machine. The replacement of components is
not on a typical IT replacement schedule. This can present longer than ideal
technology refresh cycles. The risk here is that integrating modern cyber
technology into an older IT/OT technology stack has its challenges.
4 issues holding back CISOs’ security agendas
 CISOs should aim to have team members know when and how to make prioritization
calls for their own areas of work, “so that every single team is focusing on the
most important stuff,” Khawaja says. “To do that, you need to create clear
mechanisms and instructions for how you do decision-support,” he explains.
“There should be criteria or factors that says it’s high, medium, low priority
for anything delivered by the security team, because then any team member can
look at any request that comes to them and they can confidently and effectively
prioritize it.” ... According to Lee, the CISOs who keep pace with their
organization’s AI strategy take a holistic approach, rather than work deployment
to deployment. They establish a risk profile for specific data, so security
doesn’t spend much time evaluating AI deployments that use low-risk data and can
prioritize work on AI use cases that need medium- or high-risk data. They also
assign security staffers to individual departments to stay on top of AI needs,
and they train security teams on the skills needed to evaluate and secure AI
initiatives. ... the challenge for CISOs not being about hiring for technical
skills or even soft skills, but what he called “middle skills,” such as risk
management and change management. These skills he sees becoming more crucial for
aligning security to the business, getting users to adopt security protocols,
and ultimately improving the organization’s security posture. “If you don’t have
[those middle skills], there’s only so far the security team can go,” he says.
CISOs should aim to have team members know when and how to make prioritization
calls for their own areas of work, “so that every single team is focusing on the
most important stuff,” Khawaja says. “To do that, you need to create clear
mechanisms and instructions for how you do decision-support,” he explains.
“There should be criteria or factors that says it’s high, medium, low priority
for anything delivered by the security team, because then any team member can
look at any request that comes to them and they can confidently and effectively
prioritize it.” ... According to Lee, the CISOs who keep pace with their
organization’s AI strategy take a holistic approach, rather than work deployment
to deployment. They establish a risk profile for specific data, so security
doesn’t spend much time evaluating AI deployments that use low-risk data and can
prioritize work on AI use cases that need medium- or high-risk data. They also
assign security staffers to individual departments to stay on top of AI needs,
and they train security teams on the skills needed to evaluate and secure AI
initiatives. ... the challenge for CISOs not being about hiring for technical
skills or even soft skills, but what he called “middle skills,” such as risk
management and change management. These skills he sees becoming more crucial for
aligning security to the business, getting users to adopt security protocols,
and ultimately improving the organization’s security posture. “If you don’t have
[those middle skills], there’s only so far the security team can go,” he says.
Rethinking data center strategy for AI at scale
Traditional data centers were engineered for predictable, transactional workloads. Your typical enterprise rack ran at 8kW, cooled with forced air, powered through 12-volt systems. This worked fine for databases, web applications, and cloud storage. Yet, AI workloads are pushing rack densities past 120kW. That's not an incremental change—it's a complete reimagining of what a data center needs to be. At these densities, air cooling becomes physically impossible. ... Walk into a typical data center today. The HVAC system has its own monitoring dashboard. Power distribution runs through a separate SCADA system. Compute performance lives in yet another tool. Network telemetry? Different stack entirely. Each subsystem operates in isolation, reporting intermittently through proprietary interfaces that don't talk to each other. Operators see dashboards, not decisions. ... Cooling systems can respond instantly to thermal changes, and power orchestration becomes adaptive rather than provisioned for theoretical peaks. AI clusters can scale based not just on demand, but in coordination with available power, cooling capacity, and network bandwidth. ... Real-time visibility, unified data architectures, and adaptive control will define performance, efficiency, and competitiveness in AI-ready data centers. The organizations that thrive in the AI era won't necessarily be those with the most data centers or the biggest chips; they'll be the ones that treat infrastructure as an intelligent, responsive system capable of sensing, adapting, and optimizing in real time.Microsoft handed over BitLocker keys to law enforcement, raising enterprise data control concerns
 The US Federal Bureau of Investigation approached Microsoft with a search
warrant in early 2025, seeking keys to unlock encrypted data stored on three
laptops in a case of alleged fraud involving the COVID unemployment assistance
program in Guam. As the keys were stored on a Microsoft server, Microsoft
adhered to the legal order and handed over the encryption keys ... While the
encryption of BitLocker is robust, enterprises need to be mindful of who has
custody of the keys, as this case illustrates. ... Enterprises using BitLocker
should treat the recovery keys as highly sensitive, and avoid default cloud
backup unless there is a clear business requirement and the associated risks are
well understood and mitigated. ... CISOs should also ensure that when devices
are repurposed, decommissioned, or moved across jurisdictions, keys should be
regenerated as part of the workflow to ensure old keys cannot be used. ... If
recovery keys are stored with a cloud provider, that provider may be compelled,
at least in its home jurisdiction, to hand them over under lawful order, even if
the data subject or company is elsewhere without notifying the company. This
becomes even more critical from the point of view of a pharma company,
semiconductor firm, defence contractor, or critical-infrastructure operator, as
it exposes them to risks such as exposure of trade secrets in cross‑border
investigations.
The US Federal Bureau of Investigation approached Microsoft with a search
warrant in early 2025, seeking keys to unlock encrypted data stored on three
laptops in a case of alleged fraud involving the COVID unemployment assistance
program in Guam. As the keys were stored on a Microsoft server, Microsoft
adhered to the legal order and handed over the encryption keys ... While the
encryption of BitLocker is robust, enterprises need to be mindful of who has
custody of the keys, as this case illustrates. ... Enterprises using BitLocker
should treat the recovery keys as highly sensitive, and avoid default cloud
backup unless there is a clear business requirement and the associated risks are
well understood and mitigated. ... CISOs should also ensure that when devices
are repurposed, decommissioned, or moved across jurisdictions, keys should be
regenerated as part of the workflow to ensure old keys cannot be used. ... If
recovery keys are stored with a cloud provider, that provider may be compelled,
at least in its home jurisdiction, to hand them over under lawful order, even if
the data subject or company is elsewhere without notifying the company. This
becomes even more critical from the point of view of a pharma company,
semiconductor firm, defence contractor, or critical-infrastructure operator, as
it exposes them to risks such as exposure of trade secrets in cross‑border
investigations.
Moore’s law: the famous rule of computing has reached the end of the road, so what comes next?
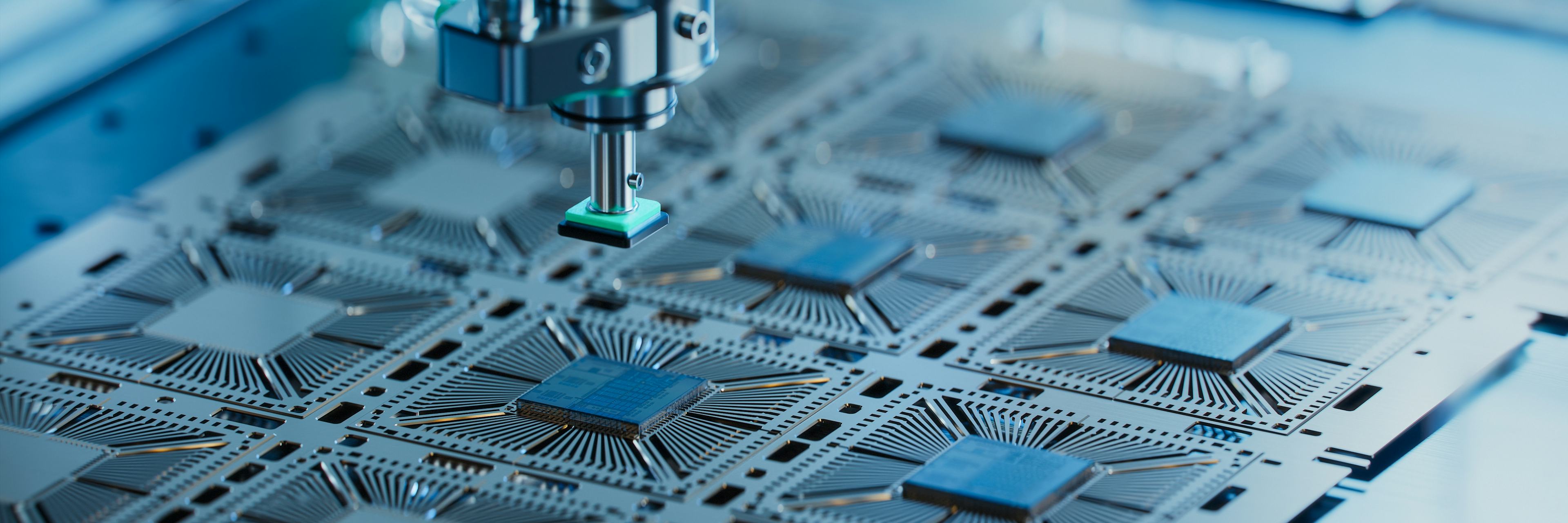 For half a century, computing advanced in a reassuring, predictable way.
Transistors – devices used to switch electrical signals on a computer chip –
became smaller. Consequently, computer chips became faster, and society quietly
assimilated the gains almost without noticing. ... Instead of one
general-purpose processor trying to do everything, modern systems combine
different kinds of processors. Traditional processing units or CPUs handle
control and decision-making. Graphics processors, are powerful processing units
that were originally designed to handle the demands of graphics for computer
games and other tasks. AI accelerators (specialised hardware that speeds up AI
tasks) focus on large numbers of simple calculations carried out in parallel.
Performance now depends on how well these components work together, rather than
on how fast any one of them is. Alongside these developments, researchers are
exploring more experimental technologies, including quantum processors (which
harness the power of quantum science) and photonic processors, which use light
instead of electricity. ... For users, life after Moore’s Law does not mean that
computers stop improving. It means that improvements arrive in more uneven and
task-specific ways. Some applications, such as AI-powered tools, diagnostics,
navigation, complex modelling, may see noticeable gains, while general-purpose
performance increases more slowly.
For half a century, computing advanced in a reassuring, predictable way.
Transistors – devices used to switch electrical signals on a computer chip –
became smaller. Consequently, computer chips became faster, and society quietly
assimilated the gains almost without noticing. ... Instead of one
general-purpose processor trying to do everything, modern systems combine
different kinds of processors. Traditional processing units or CPUs handle
control and decision-making. Graphics processors, are powerful processing units
that were originally designed to handle the demands of graphics for computer
games and other tasks. AI accelerators (specialised hardware that speeds up AI
tasks) focus on large numbers of simple calculations carried out in parallel.
Performance now depends on how well these components work together, rather than
on how fast any one of them is. Alongside these developments, researchers are
exploring more experimental technologies, including quantum processors (which
harness the power of quantum science) and photonic processors, which use light
instead of electricity. ... For users, life after Moore’s Law does not mean that
computers stop improving. It means that improvements arrive in more uneven and
task-specific ways. Some applications, such as AI-powered tools, diagnostics,
navigation, complex modelling, may see noticeable gains, while general-purpose
performance increases more slowly.