The Future Is Now: AI and Risk Management in 2024

Generative AI can write code, generate personalized content, and even compose
music. IT and business leaders are incorporating custom LLMs into their
workflows to maximize worker productivity and streamline routine procedures.
Governments are developing regulations for the use of all forms of AI, with the
goal of making it safer for humans to use. Organizations are also writing
internal guidelines to clarify and standardize the deployment of AI in their own
operations. ... Generic, generative AI isn’t reliable – especially when lives
are on the line. AI for risk management is tailored to industry-specific needs,
providing accurate, relevant data to allow for expedited decisions and swift
actions. It considers historic threats and delivers updates in real time as
events unfold. It can also understand linguistic nuances specific to risk
management. ... AI-powered risk intelligence must be continuously fed quality
data vetted by expert data scientists who specialize in machine learning and
risk intelligence. The technology should be monitored and trained by humans to
ensure it provides only the most accurate and trustworthy information.
Strengthening Cyber Security

In today’s interconnected digital ecosystem, the ramifications of a cyber
breach extend far beyond mere data loss. They can disrupt essential services,
compromise national security and erode public trust in Government
institutions. Therefore, the imperative to fortify cyber security measures
cannot be overstated. Regular security audits serve as a pre-emptive measure
to identify vulnerabilities, assess risks and implement corrective actions
before they can be exploited by malicious actors. By mandating such audits,
the GAD is not only demonstrating foresight but also fostering a culture of
vigilance and accountability within Government Departments. Moreover, the
emphasis on engaging CERT-in-empanelled agencies underscores the importance of
leveraging expertise and best practices in cyber security. ... Equally crucial
is the timely implementation of audit findings and recommendations. Too often,
audits yield valuable insights that languish in bureaucratic inertia, leaving
vulnerabilities unaddressed. This entails establishing clear lines of
responsibility, allocating adequate resources, and instituting mechanisms for
continuous monitoring and evaluation.
The Complexity and Need to Manage Mental Well-Being in the Security Team

“Security people are often overwhelmed,” comments Thea Mannix, director of
research (and a cyberpsychologist) at Praxis Security Labs. Apart from the day
to day work, she adds, “They’re expected to be futurologists able to predict
the future, and psychologists able to understand the human elements of
security – how users may react to social engineering and how they may subvert
security controls to make work easier. And they never get any positive
feedback; it’s mostly negative because the whole process of security is mostly
negative – stop the outside bad guys doing anything bad, and stop the inside
good guys doing anything wrong.” But there’s also a disturbing edge to this
‘human’ side of cybersecurity. Security teams sometimes work with SBIs and the
FBI on criminal investigations. Tim Morris, chief security advisor at Tanium,
knows what can be involved because he and his team have done this. “We do
cybersecurity to protect data and people. And the only reason we must do this
is because there’s an evil side of humanity.
How to Become a Cyber Security Analyst? A Step By Step Guide

If you’re contemplating a career in cybersecurity, you’re positioned
advantageously. The field is experiencing a robust surge and is poised for
continued expansion in the coming years. ... The core responsibility of a
cyber security analyst revolves around safeguarding a company’s network and
systems against cyber attacks. This entails various tasks such as researching
emerging IT trends, devising contingency plans, monitoring for suspicious
activities, promptly reporting security breaches, and educating the
organization’s staff on security protocols. Additionally, cyber security
analysts play a pivotal role in implementing threat protection measures and
security controls. They may conduct simulated security attacks to identify
potential vulnerabilities within the organization’s infrastructure. Given the
ever-evolving tactics and tools employed by hackers, cyber security analysts
must remain abreast of the latest developments in digital threats. Staying
informed about emerging cyber threats ensures that analysts can effectively
anticipate and counteract evolving security risks.
Viewpoint: AI Is Changing the Cyber Risk Landscape

Any time an organization adopts new technology, that organization inherently
opens itself up to risk by introducing a new set of unknowns to their business
practices. Allowing the wrong users access to a program, for example, or flaws
in the program’s code, are technological issues that can create security
vulnerabilities which need to be addressed by IT and cybersecurity
professionals. The practice of hacking – where cybercriminals use code to
break through an organization’s cybersecurity systems – is increasingly
difficult, but the sudden ubiquity of AI offers a new way to create
vulnerabilities by targeting system users with lifelike dupes. Emails that
look genuine but are designed to extract important security credentials are
not a new phenomenon, but generative AI has allowed new, sophisticated forms
of phishing attacks to proliferate on an unprecedented scale. Deepfakes are a
convincing new form of cyberattack where criminals develop highly convincing
visual and auditory assets to impersonate others.
Achieving Data Excellence: How Generative AI Revolutionizes Data Integration
Data integration combines data from various sources for a unified view.
Artificial intelligence (AI) improves integration by automating tasks, boosting
accuracy, and managing diverse data volumes. Here are the top four data
integration strategies/patterns using AI: Automated data matching and merging –
AI algorithms, such as ML and natural language processing (NLP), can match and
automatically merge data from disparate sources. Real-time data integration – AI
technologies, such as stream processing and event-driven architectures, can
facilitate real-time data integration by continuously ingesting, processing, and
integrating data as it becomes available. Schema mapping and transformation –
AI-driven tools can automate the process of mapping and transforming data
schemas from different formats or structures. This includes converting data
between relational databases, NoSQL databases, and other data formats — plus
handling schema evolution over time. Knowledge graphs and graph-based
integration – AI can build and query knowledge graphs representing relationships
between entities and concepts.
Generative AI, the Digital Divide, and the Tremendous Opportunity

Access to generative AI and tools such as ChatGPT is becoming the new table
stakes for many walks of life. As businesses implement this technology, workers
will need to be upskilled. Children -- the next generation of workers -- will
need access at school and at home. And leaders must continually strive for an AI
future that’s fair and equitable. The reality is that those who know how to use
AI tools will have a significant advantage over those who don’t. For telecoms,
adopting an ESG-principled strategy to introduce or enhance broadband services
in low-income areas is more than an opportunity to enhance the quality of life
among people who have been historically under-connected; it can also build their
brand and grow their subscriber base. By aligning business strategy with a clear
ESG framework, companies can significantly reduce the cost of borrowing when
raising capital to invest in major GenAI infrastructure projects. In the KPMG US
2023 ESG and Financial Value survey, 43% of business leaders at companies with
more than 10,000 employees cited access to new capital sources as one of the top
financial benefits of their ESG strategies.
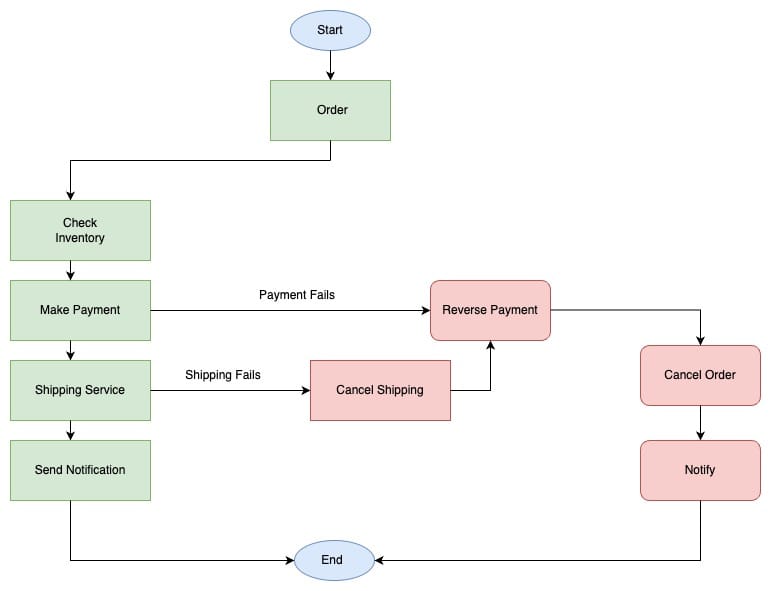
How to design and deliver an effective cybersecurity exercise
Playbooks come in a variety of styles, including action plans, flow charts and
storylines. They are based on cyber-attack scenarios and are used by
facilitators to guide participants throughout the cybersecurity exercise. They
include pieces of information for participants (e.g., indicators of compromise,
a customer complaint, a help desk report, a piece of threat intelligence or a
SOC alert), as well as key stages of the exercise. ... An appropriate target
audience must be identified before considering the type of cyber exercise to
perform. Audiences can consist of different functions, levels and areas of an
organization such as executives, crisis management, incident response or
operational teams (among others). The audience will shape the objectives,
injects, discussion areas and storyline of the scenario. Tailoring these
specifically to an audience is paramount to conducting a successful exercise.
... The organization must select suitable targets for cybersecurity exercises.
Targets can comprise one or more types of assets, such as critical business
applications, technical infrastructure, physical devices, people, or
office/factory locations.
How data centers can drive a more sustainable world

In spite of the race to greater sustainability, the demand for more data speed
and bandwidth is still driving the need for increased DCI network performance,
capacity, and scalability. In order to meet these demands while maintaining
competitiveness, hyperscalers must cut costs and streamline operational
efficiency, even as they enhance capacity. Traditionally, the wavelength range
of ROADM networks was limited because conventional transmission solutions were
divided into C-band and L-band. This is particularly problematic in metro and
long-haul DCI networks. Recent advances in continuous C+L ROADM architecture
allow transport platforms to handle both wavelength bands at once. This not only
increases maximum transmission capacity and simplifies network capacity
upgrades, it also reduces environmental impact by using half the common line
system equipment versus current bolt-on or C-band overbuild approaches.In
addition to capacity enhancements, technology advances are contributing to
increased distance for long-haul DCI networks.
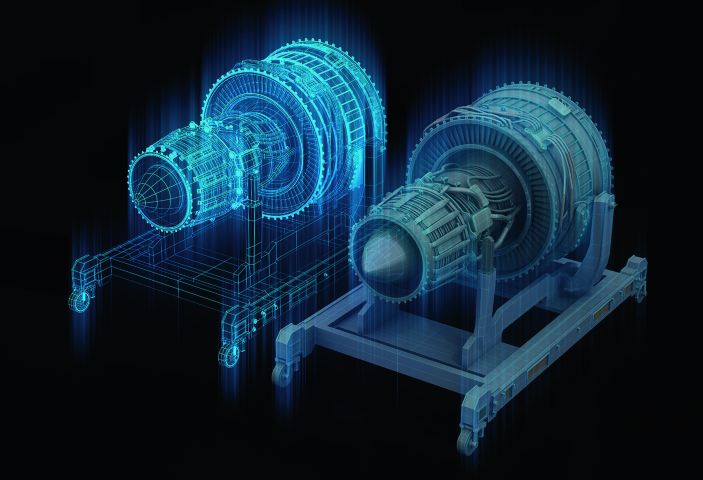
The metaverse mystique- Reshaping virtual interaction

For all businesses, the metaverse will eventually develop into a platform where
they have to engage with their customers. A host of global brands, from Adidas
to JP Morgan have launched metaverse initiatives. It offers businesses an
unprecedented opportunity to connect with their customers on a deeper level –
offering a Metaverse platform can potentially allow businesses and brands to
develop an even deeper 360-degree view of their customers which allows for more
accurate and granular segmentation analytics, enabling customer insights in ways
previously unimaginable. This will facilitate the delivery of products and
services with unparalleled precision, aligning them seamlessly with customer
insights and expectations. The potential for businesses in the Metaverse is
staggering, with McKinsey estimating its value creation potential to reach up to
$5 trillion by 2030. Beyond the consumer-centric applications, industrial uses
are also gaining traction. Augmented Reality (AR) and Virtual Reality (VR)
tools, along with digital twin architectures, are increasingly finding
applications in various industrial sectors.
Quote for the day:
''To so great things is difficult; but
to command great things is more difficult.'' --
Friedrich Nietzsche

/filters:no_upscale()/articles/getting-tech-debt-on-roadmap/en/resources/7fig3-1710944508954.jpg)