DSPM: Control Your Data to Prevent Issues Later

Simply put, it’s becoming increasingly hard to prevent data security breaches
and hacks — the attack surfaces have become too complex. Today, there are
petabytes of data being stored, but only a small percentage is actually used and
touched on a regular basis. Once the data is stored, it flows seemingly to
everyone, and before long, no one knows what data is stored where and who has
access to it. Data has become prevalent, especially with the increase in the
number of cloud and SaaS applications. All employees, not only engineers,
generate and transmit data, sometimes sensitive PII data that is subject to
regulations like GDPR and HIPAA. Of course, companies attempt to maintain good
data hygiene with risk assessments, labeling, written policies and procedures
(that no employee actually reads). All of this is largely done manually and adds
more work on IT teams that are already drowning in security and risk assessments
as well as security alerts. Add to that the fact that manual assessments are
unsustainable and are out of date the second they are completed because they are
point-in-time and don’t capture any changes.
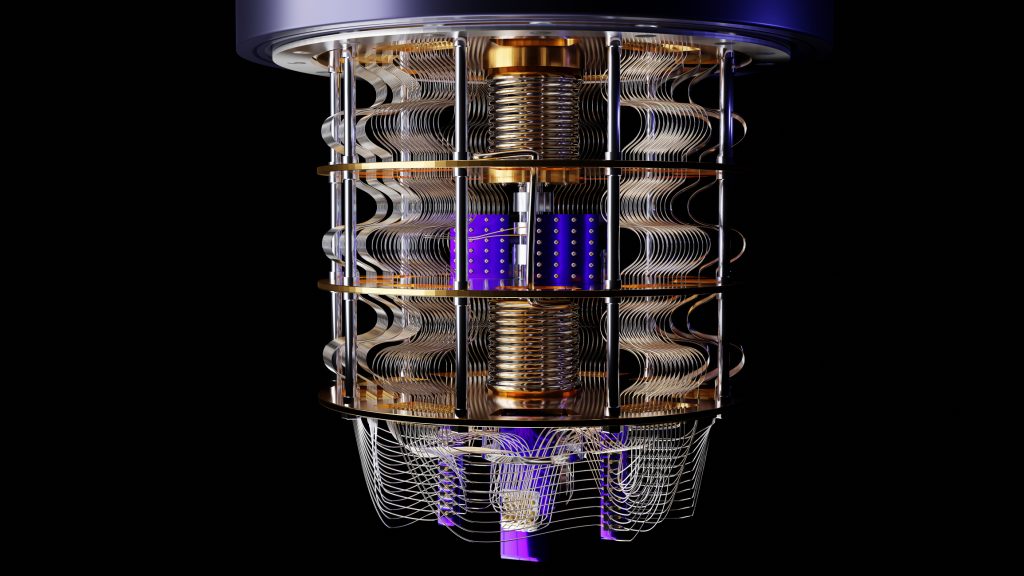
Cracking the code: solving for 3 key challenges in generative AI

People are really afraid of machines replacing humans. And their concerns are
valid, considering the human-like nature of AI tools and systems like GPT. But
machines aren’t going to replace humans. Humans with machines will replace
humans without machines. Think of AI as a co-pilot. It’s the user’s
responsibility to keep the co-pilot in check and know its powers and
limitations. Shankar Arumugavelu, SVP and Global CIO at Verizon, says we
should start by educating our teams. He calls it an AI literacy campaign. “We’ve
been spending time internally within the company on raising the awareness of
what generative AI is, and also drawing a distinction between traditional ML and
generative AI. There is a risk if we don’t clarify machine learning, deep
learning, and generative AI – plus when you would use one versus the other.”
Then the question is: What more can you do if something previously took you two
weeks and now it takes you two hours? Some leaders will get super efficient and
talk about reducing headcount and the like. Others will think, I’ve got all
these people, what can I do with them?
Training AI Models – Just Because It’s ‘Your’ Data Doesn’t Mean You Can Use It

The rise of generative AI has inspired many companies to leverage the data and
content they have amassed over the years, to train AI models. It is important
that these companies ensure they have the right to use this data and content for
this purpose. The lessons from Everalbum are worth heeding. However, the FTC is
not the only threat to companies training AI models. Class action attorneys are
circling the waters and smell blood. At least one recent class action suit has
been filed based on the use of images uploaded by users to train AI models,
arguably without the proper consent to do so. ... The foregoing cases primarily
address situations where companies used data they already had to train AI
models, at least arguably without consent to do so. Many companies are newly
collecting data and content from various sources to build databases upon which
they can train AI models. In these cases, it is important to ensure that data is
properly acquired and that its use to train models is permitted. This too has
led to lawsuits and more will likely be filed.
How Platform Engineering Bridges the IT and DevOps Divide
Platforming engineering and “platform as a product” have been key to the PaaS
ecosystem for years but are now gaining fresh traction in the industry. In
Puppet’s State of DevOps Report, 51% of respondents said they had already
adopted platform engineering and 93% said it was a step in the right direction.
Gartner predicted 80% of software engineering organizations will have platform
teams by 2026. The concept can be defined in several ways. Gartner reported
platform engineering is “an emerging trend intended to modernize enterprise
software delivery… designed to support the needs of software developers and
others by providing common, reusable tools and capabilities, and interfacing to
complex infrastructure.” PlatformEngineering.org’s recent blog post defines it
as the discipline of designing and building toolchains and workflows for
self-service capabilities in software engineering organizations during the
cloud-native era. Regardless of definition, platform engineering is the latest
iteration of IT centralization, though now attempting to retain all the benefits
of distributed team empowerment through “composition” rather than converged
control.
Wi-Fi 7: Everything you need to know about the next era of wireless networking

With each iteration of Wi-Fi standards, channel widths have widened to allow for
more simultaneous data transfer streams. It's intended to enable multiple
devices to communicate, but increasing the channel width doesn't necessarily
equate to faster speeds. There are often benefits to sticking with lower
channels around 20 - 40MHz, but Wi-Fi 7 jumps to 320MHz for its 6GHz band. Wi-Fi
6E already uses a 6GHz band but is limited to 160MHz, so doubling the channel
width is a big selling point for the upcoming standard. As with most technical
advancements, real-world performance upgrades will rely on whether your devices
are efficiently designed to support the maximum theoretical speeds of Wi-Fi
7.
... MU-MIMO (multi-user, multiple input, multiple output) increases to
16 streams for Wi-Fi 7 alongside the wider channel, doubling the bandwidth from
the 8 streams of Wi-Fi 6. The more antennas on your router, internal or
external, the better equipped it will be to handle the maximum theoretical
bandwidth limits.
ChatGPT and Digital Trust: Navigating the Future of Information Security
As we navigate this monumental shift, the focus on information security and
safeguarding against risks becomes paramount, particularly in the realm of AI.
This is where the fascinating and complex issue of digital trust comes into
play. Amidst recent news stories of data breaches and privacy concerns, the
importance of digital trust and robust information security have never been more
critical. ... In the age of AI, maintaining trust in our digital world is an
ongoing process that requires constant attention and adaptation. It involves
asking tough questions, making complex decisions and collaborating as a tech
community. As we continue to integrate AI technologies like ChatGPT into our
digital landscape, let’s focus on building a strong foundation of trust that
promotes innovation while prioritizing the safety and well-being of everyone
involved. As professionals in the technology field, it’s our responsibility to
understand, adapt and innovate in a responsible and ethical manner. Let’s keep
exploring, questioning and learning because that’s what the journey of
technology is all about, especially when it comes to reinforcing information
security.
Gartner: Generative AI not yet influencing IT spending, but enterprises should plan for it
“The generative AI frenzy shows no signs of abating,” said Frances Karamouzis,
distinguished VP analyst at Gartner, in a statement. “Organizations are
scrambling to determine how much cash to pour into generative AI solutions,
which products are worth the investment, when to get started and how to mitigate
the risks that come with this emerging technology.” That same poll found that
68% of executives believe the benefits of generative AI outweigh the risks,
compared with just 5% that feel the risks outweigh the benefits. “Initial
enthusiasm for a new technology can give way to more rigorous analysis of risks
and implementation challenges,” Karamouzis stated. “Organizations will likely
encounter a host of trust, risk, security, privacy and ethical questions as they
start to develop and deploy generative AI.” Another survey, this one published
by MIT Technology Review Insights and sponsored by enterprise data management
company Databricks, polled 600 senior data and technology executives.
IDEA: a Framework for Nurturing a Culture of Continuous Experimentation
Empathy and trust goes a long way when building relationships. If the team is
expected to pick up new skills, they need to have dedicated and uninterrupted
time to practice and learn. As a team, you can timebox the uninterrupted time
you need. However, expecting your team to pick up new skills while they’re also
expected to work full-time on their current projects will end up in
disappointment and burnout. Another important factor is that people adopt new
skills differently. Some people learn better in groups and some alone. I always
respect individual preferences. However, having a couple hours of workshops for
the whole team often benefits everyone. During these workshops everyone can
discuss their learning, questions, and interesting facts they found out. From my
experience as a consultant, I often find myself stepping into the unknown with
new clients and projects. This has taught me that openness, honesty and
curiosity are fundamental.
Study: We Are Wasting Up to 20 Percent of Our Time on Computer Problems

Surprisingly, studies reveal that a significant amount of our time spent on
computers, averaging between 11 and 20 percent, is wasted due to malfunctioning
systems or complex interfaces that hinder our ability to accomplish desired
tasks. Professor Kasper Hornbæk, one of the researchers involved in the study,
deems this situation far from satisfactory. “It’s astonishing how high this
percentage is. Almost everyone has experienced the frustration of a critical
PowerPoint presentation not being saved or a system crashing at a crucial
moment. While it is widely recognized that creating IT systems that align with
users’ needs is challenging, the occurrence of such issues should be much lower.
This highlights the insufficient involvement of ordinary users during the
development of these systems,” Professor Hornbæk asserts. Professor Morten
Hertzum, the other researcher contributing to the study, emphasizes that the
majority of frustrations stem from the performance of everyday tasks, rather
than complex endeavors.
Mitigating the organisational risks of generative AI
Firstly, keeping an eye on how their systems are being used, by rolling up
topics, attacks and other exploits to understand the moving threat landscape
will be key — along with keeping warning thresholds low for anomalous events.
Ensuring all AI-augmented platforms and services have a dedicated ‘kill switch’
with the ability to revoke keys and other methods of access will become ever
more vital as we advance to peak GenAI. ... It’s often a great yardstick of how
a service, function or platform is performing in the market, so keeping a watch
on service and keywords after a big product launch is always a good idea —
especially when it comes to picking up any AI responses that break ethics or are
reputationally damaging. Providing access to the latest AI-related news on the
underlying technologies they’re using for any engineering teams is another
preventative measure you can put in place. This will support in the battle to
quickly spot any upstream problems, allowing engineers to proactively restrict
affected services as required.
Quote for the day:
“If we wait until we’re ready, we’ll be
waiting for the rest of our lives.” -- Lemony Snicket



















:format(webp)/cdn.vox-cdn.com/uploads/chorus_image/image/72422275/GettyImages_1255249339.0.jpg)