Industry groups call for changes to EU Cyber Resiliency Act

The first recommendation made by the collective is that the proposed scope of
the CRA should be made narrower and clearer. "Any reference to 'remote data
processing solutions' should be excluded from the scope of the CRA to ensure
legal clarity, and to avoid overlaps with existing legislation and unnecessary
burden," they wrote. Software as a service, platform as a service, or
infrastructure as a service should not be considered within the scope of the
CRA, and this clarification should be reflected in the core legal text to
provide greater legal certainty and to facilitate implementation across the EU,
the recommendation read. ... The second recommendation calls for a more
proportionate approach to determining a product's risk-level, along with greater
certainty for manufacturers to ascertain if a product is deemed a critical one.
"A transparent and inclusive review process involving economic operators should
be set up to determine whether a product is critical," the groups wrote. This
would avoid wrongfully designating too many products as "critical," making them
more expensive...
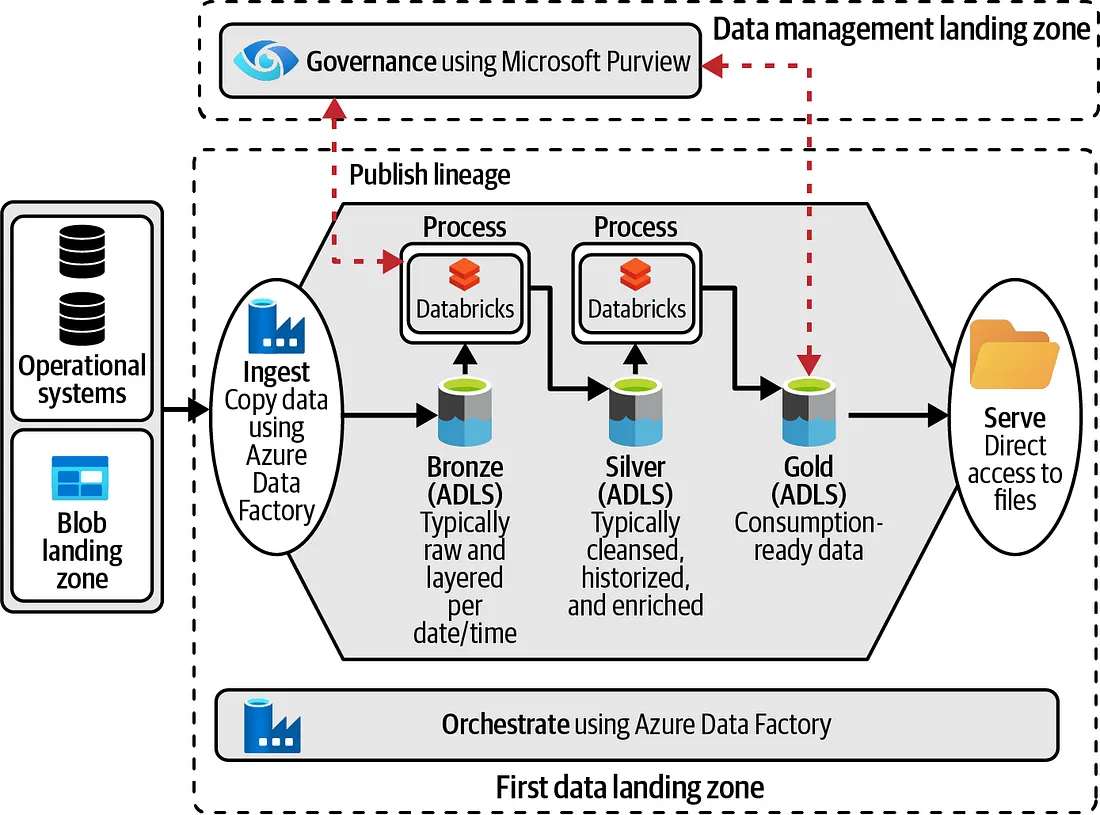
AI’s Impact on Security, Risk and Governance in a Hybrid Cloud World
To build an AI-driven compliance, security and governance solution, you must
first be able to scale and learn from large data sets. To learn from the data,
you must build training models for the data to be processed effectively by the
AI component. These training models require the ability to analyze and operate
at scale and support different training models for different use cases. Since we
need to analyze and operate at scale continuously, we have moved from the
underlying tech of machine learning (ML) to deep learning (DL) based on neural
net technology. With this technology, we can detect, analyze and prioritize the
findings. The second part of this is auto-remediation; this enables us to
understand where the problem is developing and what actions, if taken, would
create the biggest impact. This prioritization technique driven by AI and our
proprietary technology working together creates a scenario of a self-healing
environment. In this environment, a problem is addressed before it becomes a
serious issue.
9 tips for recruiting high-end IT talent

“Create a brand and reputation to attract this kind of talent to the work you
do and your company’s culture,” says Drees. “That could be LinkedIn content or
articles you post on your company site.” It could be stories in the news about
your company or what personnel and clients say about the company in social
media. ... “Give people the ability to grow, mature, and evolve,” says Majeed,
whose leadership team has spent a great deal of time, thought, and money on
this idea, focusing on creating a culture that nurtures and incubates talent,
going so far as to build customized learning programs that encourage people to
learn new technical skills and to grow their career. “We also give people so
much flexibility to do what they want to do,” he says. This might sound like a
distraction from work — time consuming, perhaps, or expensive. But it’s
effective, he says. “It makes people more productive — they are working with
passion and purpose.” ... “Leverage the engineers on your team, who are
excited about the challenges they’re solving,” says Drees.
Combatting data governance risks of public generative AI tools
Integration enables users to obtain answers or sentences derived from
enterprise data relevant to their queries. While publicly available generative
AI tools permit natural language querying, world wide web data is not always
applicable to the use case. Knowledge management solutions connect data from
various data sources and business applications to consolidate the data into a
central knowledge base. When it comes to querying about a customer or details
of a business document, this is the only way to retrieve answers based on
specific company entities. Additionally, delta crawling (i.e., crawling for
new data only) certifies that the model’s data is always up to date, so users
aren’t receiving old and obsolete information. ... ChatGPT and other
publicly available models, like Google Bard, do not cite where their outputs
came from. So, how do you know if the content came from a reliable source
versus an opinionated blog or insignificant public forum? Adding the source
allows users to open the corresponding document or file and view all the
details to confirm accuracy and gain further insight into their query.
Civil society groups call on EU to put human rights at centre of AI Act

The groups are therefore calling on the EU institutions to draw clear limits
on the use of AI by national security, law enforcement and migration
authorities, particularly when it comes to “harmful and discriminatory”
surveillance practices. They say these limits must include a full ban on
real-time and retrospective "remote biometric identification" technologies in
publicly accessible spaces, by all actors and without exception; a prohibition
on all forms of predictive policing; a removal of all loopholes and exemptions
for law enforcement and migration control; and a full ban on emotion
recognition systems. They added the EU should also reject the Council’s
attempt to include a blanket exemption for systems developed or deployed for
national security purposes; and prohibit the use of AI in migration contexts
to make individualised risk assessments, or to otherwise “interdict, curtail
and prevent” migration. The groups are also calling for the EU to properly
empower members of the public to understand and challenge the use of AI
systems
The Challenges and Rewards of Zero Trust Privacy
A primary challenge that occurs with the implementation of zero trust privacy
is the lack of a compliance footprint. A compliance footprint is a list of all
the laws, regulations and standards the organization must adhere to. Often,
companies do not have a team or individual responsible to monitor changes in
the compliance landscape. Failure to do this impacts privacy compliance and
the ability to implement zero trust privacy. Organizations cannot guarantee
that the system architecture restricts the flow of data beyond that which is
legal because they do not know their obligations. We see this today with the
increase in privacy fines that have been issued for inappropriate collection
and transmission of personal data. Another challenge is that organizations
often start with identity and access management. When users’ access and
authorization permissions are enabled for an unknown set of data elements,
organizations cannot guarantee compliance with least privilege requirements.
Microsoft jumps into competitive security service edge (SSE) arena

Analysts say Microsoft, while a late to the market, will be a welcome player
in the SSE arena given its large customer base. “Cisco, Palo Alto Networks,
Symantec, and Zscaler have a multi-year start over Microsoft. Gaining momentum
in a crowded market will take work,” wrote Dell ‘Oro Group research director,
Mauricio Sanchez in a blog about the SSE announcement. “Everyone knows who
Microsoft is and generally enjoys substantial goodwill among its customer
base. A large salesforce and partner ecosystem will open many doors,” Sanchez
stated. “Large enterprises that are strong Microsoft shops and take advantage
of Microsoft’s Enterprise Licensing Agreement benefits could lead to
significant uptake of Microsoft SSE solution.” Also, no other SSE vendor has
the same identity vendor chops that Microsoft brings. SSE is identity-heavy,
which Microsoft can exploit by owning the identity use cases end-to-end,
Sanchez stated. Microsoft Windows and Office 365 clients can preview the SSE
software, and it will be generally available for other operating systems later
this year.
The obsession advantage in transformation
During tough times, it’s easy to look at customers as a means to an end—a way
to drive revenue and help your bottom line. But that’s a terrible approach;
your customer also is going through the same difficult times, and this is your
chance to support them. Obsess about their pain points and learn how you can
be there for them. Work from my PwC colleagues has shown that when companies
wire a deep understanding of customers into their business models, operations,
and decision-making, they not only increase value for customers, but gain
insights that help to further differentiate the business. ... The most
transformation-ready leaders look to other innovative approaches to gain new
perspectives. Whether this is through conversations with executives in
different industries, speaking with sports coaches or sociologists, reading
and researching relevant case studies, or speaking one-to- one with more
junior employees at your own company, gaining a new perspective can often lead
to powerful inspiration. Don’t wait for these views to come to you,
either.
Building a Data Driven Organization

"The key lies in democratizing data assets and their utilization by providing
user-friendly tools, offering literacy courses, and promoting approaches that
enable employees across the organization to generate insights," he says. He
adds it is not enough for top management to merely include data-driven
initiatives in their business strategy -- they must visibly and consistently
support the cultural transformation. "This involves actively measuring
progress, recognizing early adopters as champions, and rewarding them
accordingly," he says. "Holding leaders accountable for driving cultural
change in their respective areas is essential." ... The data governance
element is also critical, which means establishing goals, measurements, and
continuous improvement practices to maximize the value derived from data and
ensure user satisfaction. "Set clear objectives for data utilization,
monitoring performance against these goals, and consistently refining
processes to optimize data-driven practices," he says. By implementing these
practices, organizations can foster a data-driven culture where employees are
equipped with the necessary tools, skills, and mindset to leverage data
effectively in their decision-making processes.
Leap to leader: Make yourself heard

It’s not just a matter of going into a meeting and asking for a raise or
promotion. Instead, imagine how an agent or headhunter would represent you.
How would they make the case for you getting the job or the raise you deserve?
And remember, it’s not just your boss you have to convince; your goal is to
give them specifics so that they can go make a case for you to their boss and
to HR. Ground the conversation in facts. What have you accomplished? How has
your work helped drive the business? Can you point to concrete ways in which
you’ve added value? ... There’s a mental loop people can get caught in that
might keep them from pushing for more money, whether negotiating for a raise
or for a pay package that comes with the new job. “I don’t want to rock the
boat,” they say to themselves. “I want to make sure things start on a positive
note. I’m grateful for the opportunity.” As a result, they settle too quickly.
But for more senior roles, the person on the other side of the table is
expecting you to push, and they’ve probably built in some negotiating room for
when you do start pushing.
Quote for the day:
"It is not fair to ask of others what
you are not willing to do yourself." -- Eleanor Roosevelt