CIOs Still Waiting for Cloud Investments to Pay Off

“You discover your cloud architecture is immature when you’re surprised by the
bill,” said Mr. Roese. “Usually the reason it was expensive is that they
processed the data in a suboptimal way, in the wrong place with the wrong tools
with the wrong economic model.” Roughly 67% of 1,000 senior technology leaders
at U.S. firms across industries said they have yet to see a significant return
on cloud investments, KPMG said Thursday in its annual technology survey. “Many
first movers expected significant IT cost efficiency from their cloud
investments,” said Barry Brunsman, a principal in KPMG’s CIO Advisory group. “We
have seen a shift away from that expectation in favor of speed and agility.” Mr.
Brunsman said the most common issues preventing a better return on cloud
spending were insufficient talent or skills among tech teams, added security and
compliance requirements, and a misalignment on expected outcomes. Global cloud
spending is projected to reach $830.5 billion by the end of the year, up 17.5%
from 2021, but slowing from last year’s growth rate of 18.3%, according to
International Data Corp. It expects growth to drop to 16.3% next year.
To Code or Not to Code: The Benefits of Automating Software Testing
The hoped-for solution to these problems has been test automation. This offers a
way to reduce manual involvement, test greater volumes, remove the risk of human
error and accelerate time to market as much as tenfold for a serious competitive
advantage. Yet, even organizations that have rolled out automated testing have
discovered that a big problem remains. They can’t easily scale these solutions
because professional-grade coding skills are still required. Even if they are
marketed as “low-code,” they’re still far too complex for business users. Even
testers usually lack the coding skills to set up tests on their own. As a
result, coding skills remain a resource bottleneck that slows down the testing
process and limits collaboration with business users. What’s more, as automated
testing becomes more pervasive throughout the organization, the maintenance
workload grows. All those test engineers an organization hired to implement an
automation framework increasingly spend their time maintaining code instead of
building bigger and smarter test scopes. Scaling becomes impossible.
Where JavaScript is headed in 2022

Angular is showing ominous signs of weakness around retention and interest,
ranking near the bottom at #9. Nevertheless, it remains #2 for actual usage, and
#3 for awareness. Vue continues to be a strong contender, with a decent ranking
across all categories. Overall the story on the front end is of incremental
refinements, rather than revolutionary upheaval. And on the back end? Next.js
instigated the full-stack JavaScript movement, and remains second only to
Express in both awareness and usage. The comparison of Next to Express is of
course imperfect. Express is a server-side framework only, the workhorse of
Node-based HTTP. ... Another interesting discovery in relation to languages that
compile to JavaScript is the popularity of Elm. Elm is an ingenious functional
language geared for web development, and highly regarded for its enablement of
fast and fluent applications. But it’s also a mothballed project without any
commits for months. The takeaway? Clearly the basic ideas in Elm are still
desirable and popular. Perhaps a new leader could take up the project and carry
it forward to the benefit of the entire ecosystem.
Blockchain: An Immutable Future?
The general consensus is that the pandemic delayed the adoption of distributed ledger technologies. Companies worldwide felt the repercussions of supply chain disruption and changes to consumer habits, which meant that the implementation of blockchain fell low on priority lists. However, in some cases, blockchain technology was used effectively to coordinate logistics. Despite the limited use, the global crisis helped drive further discussion about blockchain’s benefits; for example, ledger technologies could potentially have helped counter the fake vaccines that flooded the market during the height of the pandemic. This topic also feeds into a wider conversation about the influx of counterfeit medicines in pharma supply chains. ... The computing power needed to mine (add information to the blockchain) plus the duplication of work is an obvious source of environmental concern. Beyond environmental challenges, every piece of data added to a blockchain needs to be transcribed onto every copy of the blockchain, resulting in a much greater cost than server or cloud storage.
The 5 Absolute Best X-Factors That Increase Enterprise Value

The problem with the traditional business model is that you don’t know when
clients return, if at all. Both cash flow and forecasting are problematic. The
first step in transforming your business model is implementing recurring
revenue. Again, you can look to Software as a Service (SaaS) for inspiration.
Chances are, you pay a monthly fee for your favorite movie streaming service.
Customers don’t miss hidden billing surprises as they know exactly what they’ll
pay. You enjoy the predictability of cash flow and now have accurate budgets.
The second step in transforming your business model is creating long-term
exclusive contracts. Your mission is to show clients why they are better off
with a long-term commitment. ... A rich and thriving culture is the foundation
of your business. It’s your culture that plays a role in the customer
experience. Your culture determines if you leverage a market opportunity or not.
Buyers look for a culture that promotes resilience, innovation, and
accountability. Your future buyer knows that people come and go in a business,
including you. A rich and thriving culture transcends people and takes a life of
its own.
Three Ways Banks Can Engage Younger Consumers in the Metaverse
The metaverse lets banks roll out the virtual red carpet for customers, with
tailored experiences for specific segments and personas. Personalized virtual
banking enables that special something that leaves customers feeling valued.
Within a metaverse branch, banks can create virtual rooms in which avatars of
relationship managers and customer advisors work one-on-one with high-net-worth
individuals, for instance. They might also provide services to individuals
looking to create a college fund or businesses interested in obtaining loans.
Metaverse banking’s combination of personalization and community puts a fresh,
modern spin on CX, and it’s an especially powerful draw for young banking
consumers who are critical to the future of banking. ... To connect with the
next generation of connected consumers, banks must begin building their presence
among the more popular metaverses and increase engagement with younger
demographic audiences through 3D banking, personalized services and DAOs. The
good news? For payment providers and retail and commercial banks, there are no
obstacles surrounding the preparation, and it is not too late to get
ahead.
Biology Inspires a New Kind of Water-Based Circuit That Could Transform Computing
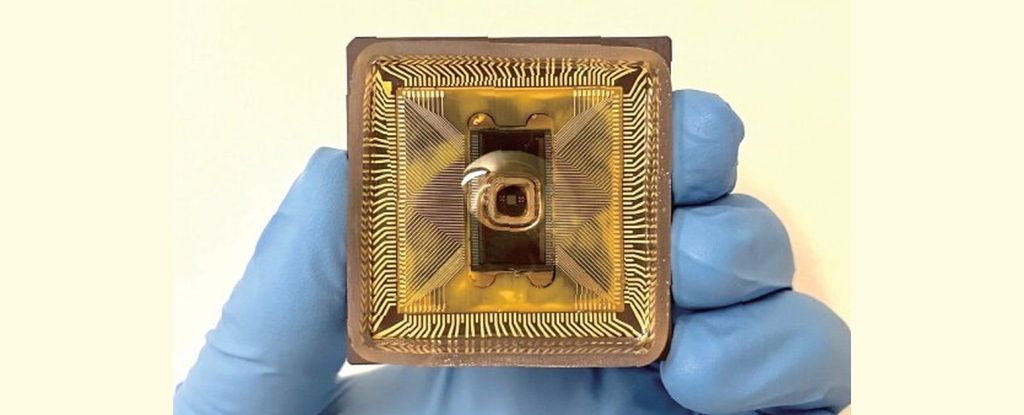
Since this is closer to the way the brain transports information, they say,
their device could be the next step forward in brain-like computing. "Ionic
circuits in aqueous solutions seek to use ions as charge carriers for signal
processing," write the team led by physicist Woo-Bin Jung of the Harvard John A.
Paulson School of Engineering and Applied Sciences (SEAS) in a new paper. "Here,
we report an aqueous ionic circuit… This demonstration of the functional ionic
circuit capable of analog computing is a step toward more sophisticated aqueous
ionics." A major part of signal transmission in the brain is the movement of
charged molecules called ions through a liquid medium. Although the incredible
processing power of the brain is extremely challenging to replicate, scientists
have thought that a similar system might be employed for computing: pushing ions
through an aqueous solution. This would be slower than conventional,
silicon-based computing, but it might have some interesting advantages.
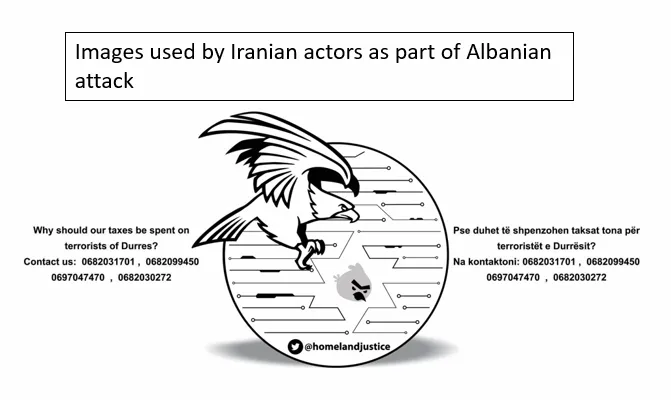
Failure of Russia’s cyber attacks on Ukraine is most important lesson for NCSC

She said three things could be attributed to the “unexpected” lack of success –
“impressive” Ukrainian cyber defences, “incredible” support from the cyber
security sector and “impressive collaboration” between the US, EU, Nato, the UK,
and others. “Just as we have seen inspirational and heroic defence by Ukrainian
military on the battlefield, we have seen incredibly impressive defensive cyber
operations by Ukrainian cyber security practitioners. Many commentators have
suggested that this has been the most effective defensive cyber activity
undertaken under sustained pressure in history,” added Cameron. She said the
constant cyber attacks on Ukraine, emanating from Russia, over the past decade
had prepared the country’s cyber defences. “In many ways, Russia has made
Ukraine match fit over the past 10 years by consistently attacking them,” said
Cameron. “We haven’t seen ‘cyber Armageddon’, but that’s not a surprise to cyber
professionals, who never expected it. What we have seen is a very significant
conflict in cyber space – probably the most sustained and intensive cyber
campaign on record.”
Feds: Chinese Hacking Group Undeterred by Indictment

The United States began publicly indicting Chinese hackers in 2014 in a strategy
to pressure Beijing by exposing the organizations and individuals behind
state-sponsored cybertheft. The strategy seemed to pay dividends when Chinese
leader Xi Jinping in September 2015 pledged to cease cyber-enabled economic
espionage. The strategy's utility has since come under mounting fire as it
became apparent that Chinese state-sponsored hacking responded to Xi's promise
by becoming stealthier rather than by ending. "The indictment did not hinder
APT41's operations as they progressed into 2021," concludes the Department of
Health and Human Services' Health Sector Cybersecurity Coordination Center in a
Thursday threat brief. "Stealing foreign IP is a primary objective of
state-sponsored Chinese cyberespionage groups such as APT41, as it contributes
to China's ambitious business and economic development goals," says Paul
Prudhomme, a former Department of Defense threat analyst who is head of threat
intelligence advisory at Rapid7.
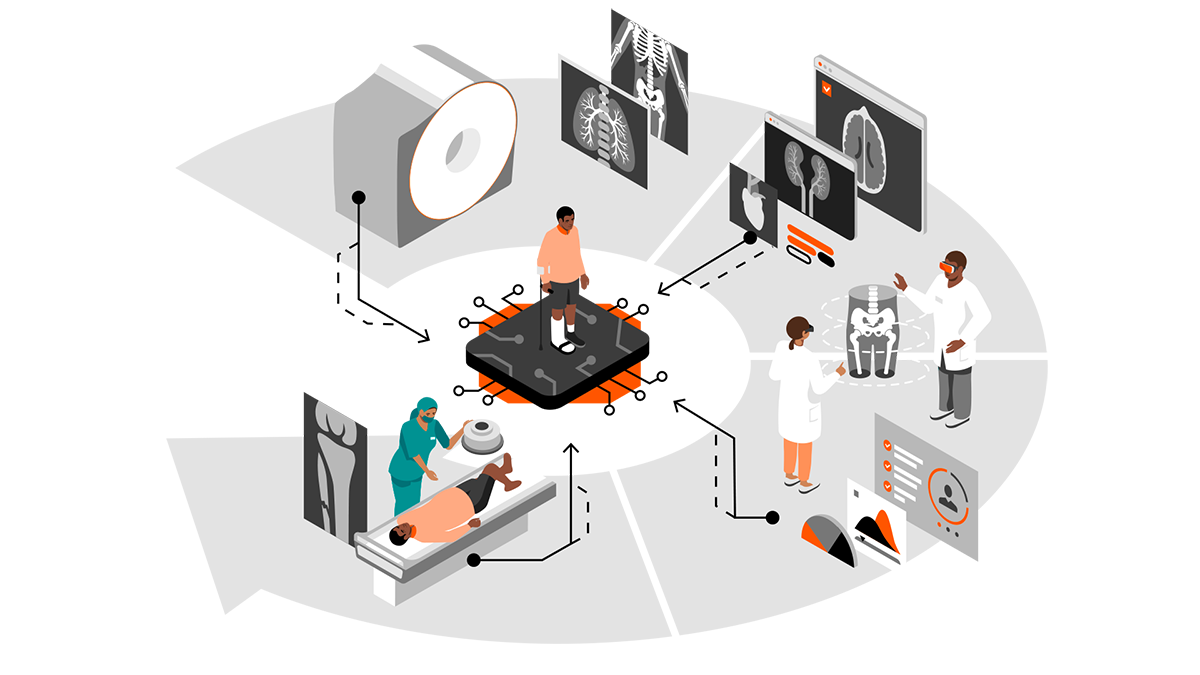
What Is Artificial Intelligence in Software Testing?
You may wonder, “Don’t test automation tools do this already?” Of course, test
automation tools already have AI in effect, but they have limitations. Where AI
shines in software development is when it’s applied to remove those limitations,
enabling software test automation tools to provide even more value to developers
and testers. The value of AI comes from reducing the direct involvement of the
developer or tester in the most mundane tasks. We still have a great need for
human intelligence in applying business logic, strategic thinking, creative
ideas, and the like. For example, consider that most, if not all, test
automation tools run tests for you and deliver results. Most don’t know which
tests to run, so they run all of them or some predetermined set. What if an
AI-enabled bot could review the current state of test statuses, recent code
changes, code coverage, and other metrics, and then decide which tests to run
and run them for you? Bringing in decision-making that’s based on changing data
is an example of applying AI. Good news! Parasoft handles automated software
testing at this level.
Quote for the day:
"It's not the position that makes the leader. It_s the leader that makes
the position." -- Stanley Huffty