Is this the end of the Point of Sale (PoS)?

The best part of all about this, in my opinion, is the further digital
acceleration it affords us. It allows you to retire old equipment that’s often
temperamental; you get to integrate quicker; and you get to deliver new digital
interactions far quicker than waiting for a PoS integration team. Testing
becomes simplified, and all devices become commodity mobile phones and tablets.
The icing on the cake is that the barrier for entry is incredibly low; you can
integrate with a payment system for next to no cost, and being a service
provider, they’ve made it as simple as possible. The integration of an app-based
PoS into an app ecosystem allows for a single, seamless journey that’s personal
to the customer, empowering, and overall just a better experience for many
users. However, one of the hurdles to get over is the level of app installation
fatigue, as not everybody wants an app per place they visit. This is a huge
opportunity for Uber equivalents to come in and provide a unified platform
(which is working well for things like food delivery), as mobile-first web apps
aren’t always a very slick experience.
World Bank Launches Global Cybersecurity Fund
The new cybersecurity initiative aims to accelerate digital transformation by
improving governments' technical capabilities and their efforts to increase
security awareness. A spokesperson for the World Bank tells Information Security
Media Group that associated funds will be disbursed "using diverse
implementation models" to catalyze specific cybersecurity investments. The
amount of funding to be provided was not revealed. The bank calls particular
attention to security investments that improve critical infrastructure -
including the energy, transportation, finance and healthcare sectors. "These
systems [designed prior to, or during the early years of the digital revolution]
… are today highly vulnerable to cybersecurity attacks with possibly serious
outcomes," the bank says on the fund's dedicated webpage. The World Bank
spokesperson says its new funding can help improve cybersecurity awareness at
the national level and enable governments to identify risks, fund technical
solutions and prepare for infrastructure investments.
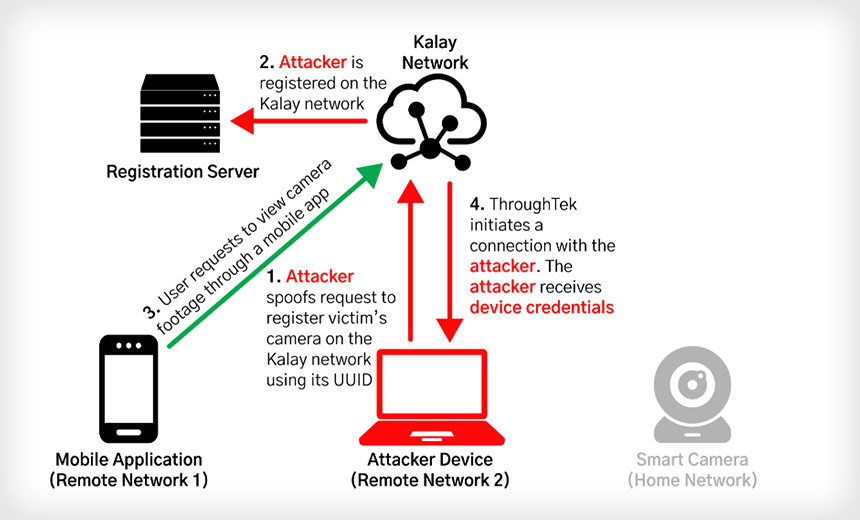
How attackers could exploit breached T-Mobile user data

T-Mobile is offering all impacted customers a free two-year subscription for
McAfee's ID Theft Protection Service, which includes credit monitoring,
full-service identity restoration, identity insurance, dark web monitoring, and
more. Business and postpaid customers can also enable T-Mobile's Account
Takeover Protection service for free and all T-Mobile users can use the
company's Scam Shield app that enables caller ID and automatically blocks calls
flagged as scams. More generally, all mobile subscribers should check with their
carriers what options they have to secure their accounts against SIM swapping or
number porting and they should enable that additional verification. Using text
messages or phone calls for two-factor authentication should be disabled where
possible in favor of two-factor authentication via a mobile app or a dedicated
hardware token, especially for high-value accounts. Email accounts are
high-value accounts because they are used to confirm password reset requests for
most other online accounts. Finally, be wary of email or text messages that ask
for sensitive information such as passwords, PINs, access tokens, or that direct
you to websites that ask for such information
Open Banking Transforming Business Models Forever

The potential to use APIs to broaden relationships and improve the customer
experiences has exploded over the past decade, with platform organizations such
as Apple, Google, Amazon. Uber and Facebook using the model to grow
exponentially and grab significant market share from established firms,
including banks and credit unions. But, you don’t have to be a tech giant to
benefit from APIs — the opportunity is being leveraged in virtually every
industry and by organizations of all sizes. In fact, small and midsize financial
institutions that want to reach digital audiences beyond their existing
geography or traditional product set can leverage open APIs. The options include
creating an independent platform, partnering to jointly create a platform, or
becoming part of another platform’s ecosystem. And there are many third-party
solution providers who are willing to assist. According to the Harvard Business
Review, “Smaller firms could have an agility advantage by unbundling their
capabilities, designing for their consumers, and exploiting opportunities in
their respective ecosystems.
10 Tips to Overcome Obstacles of AI-Enabled Digital Transformation
The bottom line: don’t add too many unknowns to your transformation program. AI
projects require iterative testing and evolution of supporting processes and
clean, consistent, well-architected data is the price of admission. Don’t assume
that the data is in place and usable for the target process, and don’t take the
promises of vendors or status of program leaders far removed from the front
lines as reality. The best way to determine whether supporting processes and
data are at the level required for success is through competitive benchmarking,
internal benchmarking, heuristic evaluations, and maturity assessments. You need
objective metrics to know if your data is adequate. A heuristic (collection of
best practices and rules of thumb) evaluation can provide a snapshot of how well
the organization is doing on current efforts. What does the organization have to
work with? Are foundational processes and data quality strong? Or does
strengthening the foundation require significant time and effort? A maturity
assessment cuts across multiple dimensions that may appear beyond the scope of
the domain but would impact downstream processes for a given area.
Defence in Depth – Time to start thinking outside the box

By embedding another link within an article, linked to from an email, this lured
the recipient into clicking a bad link, and bypassed the normal scanning tools.
This illustrates that even with anti-phishing in place, defences can still be
breached. So, what could have been done to prevent this? Firstly, you might be
asking why the IPS solution didn’t prevent this in the first place. Normally, it
would; however, these days, we are mostly at home, so the average home router
does not have this functionality and people are not always connected to a VPN.
To analyse what went wrong, and to prevent further attacks, we firstly checked
the Cyber-attack Chain, or the Mitre Att&ck framework. This is a globally
accessible knowledge base of adversary tactics and techniques based on
real-world observations. This helped us to understand how an attacker had
bypassed the previous measures. When we dug deeper, we saw there had been a
successful Defence Evasion; the email solution was exploited by allowing a
phishing email through. This could have easily led to Credential Access or
Installation with further persistence.
Counterintuitive Strategies for the Digital Economy

The most common explanations include running out of capital, underestimating the
competition, or overinvesting in the product. “Many companies think ‘if I add in
another feature I’ll grow,’ but companies which are more focused on the fit and
how to address it to the buyer tend to do better,” said Finkeldey. Other reasons
to fail include incorrect go-to-market business models, a lack of business model
fit, and poor marketing. This last one was an interesting inclusion and was
backed up with some Gartner research. Often, marketing, brand building, and
thought leadership can be seen as luxuries, but they are key to opening up new
markets and achieving growth and success. Finkeldey’s Gartner colleague Alastair
Woolcock pointed out that around 47% of the operational spend could be on sales
and marketing among successful companies in the SaaS space. For those spending
much less than that, say up to 15%, just increasing it by 5% or 10% was not the
answer. “Stepping in half the way only gets them half the way,” said Woolcock.
So, while the temptation is to “run and hire a bunch of sellers,” outsourcing
this function was often misplaced investment in the current market.
Why automated pentesting won’t fix the cybersecurity skills gap
Security teams need to have the adversarial or hacker mindset – i.e., they have
to think as an attacker. They need to stay a step ahead of the cyber criminals
and advise the rest of the organization on the important and timely actions to
take. Not every vulnerability is obvious. The best way to defend the enterprise
is for defenders to think like attackers and try harder every time they
seemingly hit a dead-end – not giving up easily on something they see that
doesn’t make sense. Successfully defending systems, networks, and applications
requires not only an understanding of the tools an attacker could use, but how
they use them and when they use them. This requires a lot of judgement calls,
asking a lot of questions that start with “why”, and those cannot be
accomplished with automated tests. Automated tests are only as good as what you
tell them to look for and do. What makes security hard is that each time, the
attacker is doing something different and new. Attackers don’t need a massive
vulnerability to impact organizations – they are patient, waiting for an
individual to make a mistake to let them in, either via phishing or social
engineering.
Hackers are getting better at their jobs, but people are getting better at prevention

One of the other issues, though, that you should realize is that even if there
is going to be federal legislation, it's only going to make a difference if it
overrides and preempts state laws, and the states do not want that to happen.
The states want to protect their own people, and any law that would be adopted
on the federal level would be unlikely to be as comprehensive as some of the
state laws. But in any case, I'll tell you that in order to comply with these
laws, any one of them, California for example, requires a great deal of work.
It requires an understanding of all the data you collect, who has access to
that data, where it's stored, who uses that data, who in your supply chain is
involved in that project. And that is a very, very big endeavor. Now, it's a
very valuable endeavor because a company that understands its collection and
use of data is going to understand its business much, much better. I've
actually seen companies that go through that process and realize that they can
improve their businesses, but it's like going on a diet and working
out.
Top 6 Time Wastes as a Software Engineer
There's a delicate balance that you've to take care of while choosing between
automation and manual testing. So let's understand how you, as a software
engineer, can use this to work out an efficient testing strategy. It's easy to
write a small manual test to ensure that the new feature you added is working
fine. But when you scale, running those manual tests needs more hours off the
clock, especially when you're trying to find that pesky bug that keeps
breaking your code. If your application or website has many components, the
chances of you not running a specific test by mistake also increase. Automated
tests or even a system to run tests more efficiently helps avoid this. You
would need to spend a bit more time setting up your automated tests. Once they
are written, though, they can be reused and triggered as soon as you make any
code changes. So you don't have to manually re-test previous functions just
because you added a new one. Conversely, choosing the right tasks to automate
is just as important. Unfortunately, it is one of the most common mistakes of
QA automation testing. It's tempting to fall into the trap of over-automating
things and end up replicating tests script-by-script.
Quote for the day:
"Successful leadership requires
positive self-regard fused with optimism about a desired outcome." --
Warren Bennis






:format(webp)/cdn.vox-cdn.com/uploads/chorus_image/image/69754581/VRG_1777_Android_12_002.0.jpg)