Time-series monitoring helps ops teams predict long-term trends based on patterns found in historical data. This type of monitoring digs into past metrics to forecast what's likely to occur next in a system. Organizations can use time-series monitoring to predict trends around autoscaling, required capacity and more. The time-series method can also support more accurate troubleshooting due to the expansive range of data collected over time. ... APM tools track the performance of enterprise software. They monitor an application over time, offering data around memory demands, code execution, network bandwidth and disk read/write speeds. Admins can use this data to evaluate how an app's dependencies might affect its performance and to pinpoint the cause of any performance issues ... This category of monitoring measures IT performance, based specifically on the perspective of end users. It might track, for example, the response time of a virtual desktop or other user-facing applications.
Clearly, the effective use of AI and data science can be game-changing, but it is not only small businesses that are struggling to deploy data science. The same report reveals that 51% of UK leaders admit their organisation does not currently have an AI strategy in place. Incorporating data science into an operating model is as big a challenge as it is an opportunity, but what are the issues specific to smaller businesses and are they so very different to larger companies? Data can be tricky to make sense of and, though start-ups or small organisations may not be sitting on the same volume of data as their larger counterparts, the variety and velocity will often be comparable. Precisely because small companies are often competing with larger, better-resourced competitors, it’s often absolutely critical that they can quickly make use of their data. The good news is that smaller organisations are in some ways better able to do this than larger, better-established ones.
With Pulumi, you can create, deploy, and manage any cloud resource using your favorite language. This includes application- and infrastructure- related resources, often in the same program. One area this gets really fun is serverless. Because we're using general purpose languages, we can create resources, and then wire up event handlers, just like normal event-driven programming. This is the way serverless should be! In this article, we'll see how. There's a broad range of options depending on what you want to do, and how your team likes to operate. We'll be using AWS and TypeScript, but other clouds and languages are available. ... Serverless app models today make you think of the event sources -- the S3 buckets -- and event handlers -- the Lambdas and associated code -- as very different things -- "infrastructure" versus "app code" -- managed with distinct tools and workflows. Pulumi, in contrast, gives you a single CLI, pulumi, to manage everything consistently.
Autism, Cybercrime, and Security's Skill Struggle
Rebecca Ledingham, vice president of cybersecurity at Mastercard, spotted the trend earlier in her career as a cyber agent for the UK's National Crime Agency. "They weren't the kinds of offenders I was used to dealing with in drugs and sex crimes," she said in an interview with Dark Reading. Their social behavior, she said, was different from what she'd seen in other areas of crime. Often, she continued, cybercriminals are first diagnosed as being on the autism spectrum during the criminal justice process. Later in her career, as a cyber agent for INTERPOL's Global Complex for Innovation (IGCI), she realized the issue was broader. Ledingham's work with global agencies revealed outside of cybercrime, no other offense came with a foundational condition. "There's no other organic set of offenders that may be predisposed to cybercrime due to the nuances of their disorder," she said. Autism presents itself at the age of two or three, and more than 17 million people worldwide are diagnosed, said Ledingham in an RSA Conference talk.
Middle East tech: Nine things the region must do to safeguard its financial future

The outlook for growth in the Middle East, North Africa region is expected to improve slightly in 2019 and 2020, the World Bank reported last June, noting a range of factors including "a favorable global environment, post-conflict reconstruction efforts, and from oil importers' reforms to boost domestic demand and increase foreign investment". Although welcome, these conclusions do not mask the longer-term economic realities that the region needs to address. The fourth industrial revolution driven primarily by AI and automation is going to radically change how we work, rest and play, bringing about major shifts to societies and economies. States such as Saudi Arabia, Qatar, UAE, and Oman have acknowledged this upheaval, with bold policy documents identifying a new vision for their counties. But the transition to these new digital realities will inevitably be haphazard and uncertain.
EU law enforcement agencies prepare for major cyber attacks

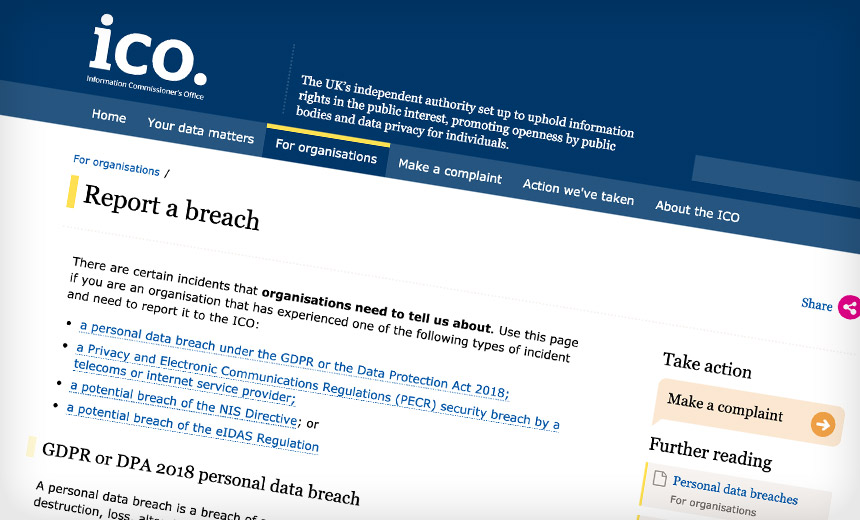
The newly adopted EU Law Enforcement Emergency Response Protocol determines the procedures, roles and responsibilities of key players both within the EU and beyond, including secure communication channels and contact points for the exchange of critical information as well as a coordination and de-confliction mechanism. The protocol is designed to complement the existing EU crisis management mechanisms, said Europol, by streamlining transnational activities and facilitating collaboration with the relevant EU and international players, making full use of Europol’s resources. It further facilitates the collaboration with the network and information security community and relevant private sector partners. Only cyber security events of a malicious and suspected criminal nature fall within the scope of this protocol. It will not cover incidents or crises caused by a natural disaster, man-made error or system failure.
3 ways AI is already changing medicine
/cdn.vox-cdn.com/uploads/chorus_image/image/63243907/GettyImages_1126452706.0.jpg)
Take ophthalmology. The top cause of loss of vision in adults worldwide is diabetic retinopathy, a condition that affects about a third of people with diabetes in the US. Patients should be screened for the condition, but that doesn’t always happen, which can delay sometimes diagnosis and treatment — and lead to more vision loss. Researchers at Google developed a deep learning algorithm that can automatically detect the condition with a great deal of accuracy, Topol found. According to one paper, the software had a sensitivity score of 87 to 90 percent and 98 percent specificity for detecting diabetic retinopathy, which they defined as “moderate or worse diabetic retinopathy or referable macular edema by the majority decision of a panel of at least seven US board-certified ophthalmologists.” Doctors at Moorfields Eye Hospital in London took that work a step further. They trained an algorithm that could recommend the correct treatment approach for more than 50 eye diseases with 94 percent accuracy.
Fortunately, not all MPs today are as dismissive of the cyber security threat as they may have been in the past. Sir David Amess provided an example from his constituency in Southend West, where he described “cybercrime having a devastating impact on individuals and businesses.” Amess spoke of a not-for-profit organisation being bankrupted as the result of a data breach – an all-too-familiar occurrence in recent years. MPs themselves are not immune to suffering data breaches. Onwurah explained how her office was a victim of a cyber-attack, but fortunate that it did no real damage. “As an MP’s office we had a big department supporting us and there was no compromise of constituents’ data,” Onwurah remarked. “If we had been a small business, we wouldn’t have had access to that kind of support, and it could have put us out of action for a lot longer.” This is undeniably true, as data breaches have become extinction events for many businesses.

Legacy protocols (such as POP and IMAP) make it more difficult for service administrators to implement authentication protections like multi-factor authentication, according to Proofpoint. In turn, the lack of multi-factor authentication means that threat actors launching attacks through IMAP can avoid account lock-out and compromise accounts unnoticed. “Attacks against Office 365 and G Suite cloud accounts using IMAP are difficult to protect against with multi-factor authentication, where service accounts and shared mailboxes are notably vulnerable,” researchers said. IMAP-based password-spraying campaigns appeared in high volumes between September 2018 and February 2019, according to the report, especially those targeting high-value users such as executives and their administrative assistants. “Targeted, intelligent brute-force attacks brought a new approach to traditional password-spraying, employing common variations of the usernames and passwords exposed in large credential dumps to compromise accounts,” researchers said in a posting.
Cybersecurity: Why bosses are confident, and tech workers are scared

At the top of business, there seems to be a lot of self-congratulatory box ticking, while elsewhere in the organisation there is a nagging sense that something very bad is about to happen. Two recent pieces of research reflect the ongoing disconnect. The UK government's annual survey of cyber security at big businesses shows that awareness of cyber risk is growing at the top of business. Nearly three quarters of firms said their board sees the risk of cyber threats to be high or very high, in comparison to all risks that they face. And nearly all FTSE 350 companies now have a cybersecurity strategy, even if only half of them will actually back up those fine words with cold, hard cash. Similarly, nearly all have a cybersecurity incident-response plan, even if only 57 percent actually test them on a regular basis. And yet, a separate survey by security company LogRhythm of 1,500 IT professionals in big businesses, shows that while the board may feel it is in control, the tech workers themselves are deeply worried.
Quote for the day:
"If you're not failing once in a while, it probably means you're not stretching yourself." -- Lewis Pugh














1552644002608.png?fm=png&auto=format)