/https%3A%2F%2Fblueprint-api-production.s3.amazonaws.com%2Fuploads%2Fcard%2Fimage%2F642692%2F5579d450-4569-4ae7-96eb-7d144b6df94d.jpg)
Since blockchains are still (relatively) new pieces of technology, we are not exactly sure which decentralized applications will survive long term. The only certainty is that with advancement comes disruption, and we are likely to see fundamental shifts in the way many common markets work. One of the more exciting ways in which blockchain is affecting an industry is in the independent freelancers’ space. Freelancers and independent contractors make up a sizable chunk of the U.S. population: there are currently over 55 million domestic freelancers. Though this group has been growing significantly over the past several years, they are still plagued with annoying transaction costs and plenty of competition. Blockchains, in theory, will open up new doors for freelancers across the globe.
You Let That In? IoT Security Concerns
To this day, malware attacks based on
similar technology are a part of daily Internet life.
Conservative estimates predict 25 billion Internetconnected
sensors by 2020. It’s unlikely that this
horde will be protected by strong security. Security experts are spooked about the dangers of IoT and have recommended that the US federal government regulate the field to ensure that standard cybersecurity measures are part of the new devices. However, the current administration looks askance at new regulations, and even if they were to act, it would take some years to stop the current onslaught of an insecure IoT. We will be left to our own devices for cybersecurity protection for the immediate future. Let’s step back and look at the risks and what the educated consumer can do about mitigation.
Why AI Is the ‘New Electricity’
Just as electricity transformed the way industries functioned in the past century, artificial intelligence — the science of programming cognitive abilities into machines — has the power to substantially change society in the next 100 years. AI is being harnessed to enable such things as home robots, robo-taxis and mental health chatbots to make you feel better. A startup is developing robots with AI that brings them closer to human level intelligence. Already, AI has been embedding itself in daily life — such as powering the brains of digital assistants Siri and Alexa. It lets consumers shop and search online more accurately and efficiently, among other tasks that people take for granted. “AI is the new electricity,” said Andrew Ng, co-founder of Coursera and an adjunct Stanford professor who founded the Google Brain Deep Learning Project, in a keynote speech at the AI Frontiers conference that was held this past weekend in Silicon Valley.
How patchable software can secure the IoT
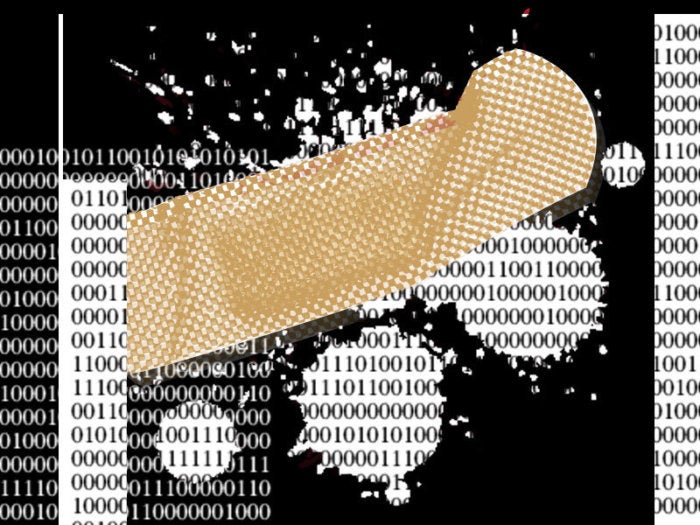
A new generation of patchable gadgets and software, such as Kidgy, is then needed for the IoT to endure. Already, smaller programs have sprung up from the initiative of tech-enthusiast around the country, but a broader approach, ideally one led by government regulators and tech-behemoths working in tandem, is desperately needed. Until the biggest fish in the pond realize that our current pattern of releasing unpatchable programs and hardware is fixed, the IoT will continue to suffer massive data breaches that plague companies and consumers alike. Of course, it shouldn’t come as a surprise to the business-savvy that the current generation of IoT gadgets is defined by their inability to be patched; the producers of these gadgets and software stand to make much more money if they can churn our unsecure products, and would shoulder the brunt of the cost if more stringent regulations were imposed.
Data Visionaries Help Companies Thrive Through Digital Transformation
Data Thrivers are taking steps to increase revenue, improve business outcomes, and transform data into dollars. Many Fortune 100 companies are building out innovation labs, as well as creating new roles for innovation executives and data management officers. Of the organizations who participated in the study, almost half already have a Chief Data Officer. Data Survivors are losing revenue opportunities, lagging in employing data to enhance customer satisfaction, and being overwhelmed by their data. They use disparate tools to manage data that is in different formats and different locations, which adds extra complexity to managing security, risk, privacy, and compliance. ... Organizations that exhibit Data Thriver behaviors are adopting a diverse set of technologies, including data services for the hybrid cloud.
Blockchain-as-a-service allows enterprises test distributed ledger technology

While heavily hyped, blockchain technology – which gained its initial notoriety from bitcoin cryptocurrency – has the potential to offer a new paradigm for the way information is shared; tech vendors and companies are rushing to figure out how they can use the distributed ledger technology to save time and admin costs. BaaS offerings are particularly attractive because many enterprises can look to their current cloud providers to offer them use of the nascent technology. "As with any new technology, there is a learning curve as enterprise customers put it into production," Fearnley said. "One advantage of partnering with a BaaS provider is users can leverage the lessons learned by the provider to help make their systems more secure." BaaS providers are also acting as consultants on the technology, Fearnley said.
Most Banks Still Not Ready For AI, Robotics: Study
The study reveals digitizing products and services, customer journey and security as top focus areas for innovation and transformation. According to the report, retail banks continue their thrust on innovation in all functional areas, with customer experience and channels (both at 78%) being at the forefront. Other segments that have witnessed higher spends in innovation include products (67%), process improvement (64%) and marketing (57%). The research, in which over 300 bankers globally participated, found that retail banks consider large technology companies, challenger banks, and smaller fintech start-ups as threats to their growth. Similar to 2016, the greatest impact of transformation is expected to be in the areas of payments and mobile wallets. The study however points out that the top three innovation challenges include systems integration, legacy technology, and the time and cost required to move from concept to reality.
Banks are increasingly turning to open source projects. Here’s why.

“We want to get to open source as quickly as possible, to start to unlock tools you can use to test software you’re developing in open source — things that won't save us a dime from a human perspective but will make our software better,” said John Stecher, managing director, group head of open innovation and Rise at Barclays. (Rise is the fintech co-working space Barclays runs in seven cities.) “If we pick up developers on the outside world that start to contribute bug fixes, we then benefit from the economies of scale of doing open source development.” This can be a tough sell inside a firm due to legal and regulatory constraints, he acknowledged. “It's a long process, it takes time, but there is a big payout at the end because you slowly start to get higher-quality software at the end of the day,” Stecher said.
The US Pentagon ready to embrace open source software
Commenting on the news is Javvad Malik, security advocate at AlienVault: “The arguments for and against the use of open-source software are long-standing. While licence costs are eliminated by using open source software, it doesn’t eliminate the associated costs of support, maintenance, and hardware requirements. In the big scheme of things, the license cost may be insignificant in some instances.” “The second widely-debated aspect is the security. The general consensus is that open source software may be more secure because there are more chances for researchers to discover flaws. However, as we saw with OpenSSH and similar, that is not always the case.” “Ultimately, it comes down to individual companies, its risk appetite, and financial requirements. ...”
The benefits of multi-cloud computing

Cloud-hosting providers come in all different and shapes and sizes, but rare is the provider that can fit all your requirements to a tee. Characteristics like upload speed, size requirements and more influence what makes the most sense for each of your business units can vary. Rather than bend your business processes to fit a specific provider’s setup and execution, play the field and explore different providers to find the best match for each part of your business to line up its functionality for a perfect fit. ... When the Rebel Alliance figured out that the Empire’s Death Star had a weakness in that small thermal exhaust port, it was only a matter of time before the whole battles station went up in smoke. Some SPOF events occur through machine errors, others come by hacker attacks. Web architects use redundancy to avoid SPOF incidents but what happens when the system host goes down?
Quote for the day:
Failure is the opportunity to begin again more intelligently. -- Henry Ford