Ransomware: It’s coming for your backup servers

Backup and recovery systems are at risk for two types of ransomware attacks:
encryption and exfiltration – and most on-premises backup servers are wide open
to both. This makes backup systems themselves the primary target of some
ransomware groups, and warrants special attention. Hackers understand that
backup servers are often under-protected and administered by junior personnel
that are less well versed in information security. And it seems no one wants to
do something about it lest they become the new backup expert responsible for the
server. This is an age-old problem that can allow backup systems to pass under
the radar of sound processes that protect most servers. It should be just the
opposite. Backup server should be the most updated and secure systems in the
data center. They should be the hardest to login to as Administrator or root.
And they should require jumping through the most hoops to login remotely. An
important role backup servers play is providing the means to recover from a
ransomware attack without paying the ransom.
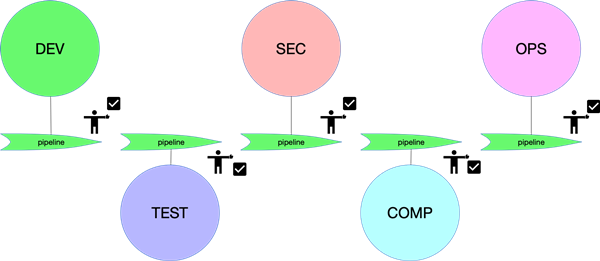
How We Improved Application’s Resiliency by Uncovering Our Hidden Issues Using Chaos Testing
The goal of chaos engineering is to educate and inform the organization of
unknown vulnerabilities and previously unanticipated outcomes of a computer
system. A primary focus of these complex testing procedures is to identify
hidden problems that can potentially arise during production environments
prior to an outage failure outside of the organization’s control. Only then
can the disaster recovery team address systematic weaknesses and enhance the
system’s overall fault-tolerance and resiliency. Hence, Chaos testing is being
carried out at various levels. ... Chaos testing is a new concept, but we
always had the mindset to perform it, and we did perform it sometimes, without
knowing that it was a chaos testing. It has its own principles, benefits and
pitfalls. However, I would advise all teams to weigh the pros and cons of
conducting these tests before formulating a plan. You should be very clear as
to what you want to achieve from these disruptive tests. Take permissions from
your bosses and convince them why it is important to carry out these
tests.
How Our Behavioral Bad Habits Are a Community Trait and Security Problem

Internal naming groups and conventions become exposed to the outside world in
a variety of ways. They're buried in website code, detailed in technical
documentation or as part of APIs, or just simply published in public system
information. Admittedly, this is a very large haystack, but finding the
needles is exactly what the patent I was involved in (US Patent 10,515,219)
endeavors to do. Site-scanning tools collect a range of information, and
unsurprisingly, an overload of information. My approach strips out all the
technical programming information (such as markup, JavaScript, etc.), and
leaves just words. It then compares results with lists of English words. The
algorithm then identifies groupings of words or abbreviations not present in
the selected language that, presumably, may signify an internal naming
convention or credentials. As is common with brute-force campaigns, it may
not, but as the axiom goes, the attacker only needs to be right once, so the
ability to generate context-sensitive word lists may make or break your next
campaign. This is when the picture may start to become clearer and the shape
of things such as user groups, system names, etc., manifest.
The Agile Compromise Calls for Courage
We cannot eliminate the risk of building the wrong thing with better design
and more focus groups. We can only do it by shorter and more frequent
iterations of a working product that is incomplete and maybe not that great
yet. That’s the Agile compromise. Shorter cycles decrease the risk of building
the wrong thing but increase the risk of degrading the process. Accruing
technical debt is one. Not a necessary consequence, just a standard price to
pay for quicker deliveries. No pundit with stories about the constant
commitment to quality will convince me otherwise. If you want greater speed,
accept more risks. The Agile compromise towards risk-taking also recognizes
that software, as a creative discipline, by nature exposes black swans: the
risks we didn’t know we would ever run into. No engineering approach provides
full reassurance against them, nor can testing and validation ever give you
full peace of mind. It’s a little bit scary, but if you pride yourself on an
Agile mindset, you must embrace it. Software is complex rather than
complicated. Its many moving parts behave in unpredictable ways when unleashed
on the world. Risks are a natural part of that property.
GPT: High-tech parlor trick or the first real AI for everyday use?

In many cases, such as ChatGPT, AI is still a parlor trick that will enthrall
us until the next trick comes along. In some cases, it’s a useful technology
that can augment both human and machine activities through incredibly fast
analysis of huge volumes of data to propose a known reaction. You can see the
promise of that in the GPT-fueled Copysmith.AI even as you experience the
Potemkin village reality of today. At a basic level, AI is pattern matching
and correlation done at incredible speeds that allow for fast reactions —
faster than what people can do in some cases, like detecting cyberattacks and
improving many enterprise activities. The underlying algorithms and the
training models that form the engines of AI try to impose some sense onto the
information and derived patterns, as well as the consequent reactions. AI is
not simply about knowledge or information, though the more information it can
successfully correlate and assess, the better AI can function. AI is also not
intelligent like humans, cats, dogs, octopi, and so many other creatures in
our world.
How you can stop corporate login credential theft

Organizations should take a layered approach to credential management. The
goal is to reduce the number of sites users have to put passwords into.
Organizations should endeavor to implement single sign-on (SSO) for all
reputable necessary work applications and websites. All SaaS providers
should support SSO. If there are logins that require different credentials,
a password manager would be helpful in the interim. This also provides a way
for employees to know if a login page can be trusted, as the password
manager won’t offer credentials up for a site it does not recognize.
Organizations should also enable multi-factor authentication (MFA) to secure
logins. FIDO2 is also gaining adoption. It will provide a more robust
solution than traditional authenticator apps, although those apps are still
better than codes sent via text messages. Not all of this is foolproof, and
risky login pages could slip through the net. A last resort is needed for
flagging risky login pages to employees. This can be done by analyzing, in
real time, threat intelligence metrics, webpage similarities, domain age and
how users got to a login page.
Security Risks, Serious Vulnerabilities Rampant Among XIoT Devices in the Workplace

The potential intent of assorted Chinese hardware manufacturers (such as
Huawei and ZTE) led to a 2018 ban on use of their equipment by federal
agencies. These devices remain widely in use in private organizations,
however, and sometimes banned devices slip through dragnets via the process
of “white labeling”. Organizations also often do not have visibility into
the code that XIoT devices run on. When these devices draw on third-party
firmware libraries, several possible security risks emerge. One is simply
that the vendor will abandon support for the device, no longer issuing
security patches to address emerging vulnerabilities. Another is that the
code may be maintained by open source developers, who have the capability to
insert malicious elements or even abandon or spike the project unexpectedly.
A simple problem that has dogged XIoT devices from the very beginning also
remains; the manufacturers are often not tech outfits and thus are not
familiar with security by design elements, and/or do not have the budget in
place to add them and still come in at their desired price points in
competitive markets.
Understanding e-signatures: the key differences and requirements

A QES is considered to have more probative value than an AES, which means
that courts will give more weight as evidence. The first key difference is
that they offer a higher level of security than AES. This is because
qualified signatures are created using a qualified signature creation device
(QSCD), which stores the signing key. Examples of physical QSCDs include
smart cards, SIM cards or USB tokens. It’s also possible for signatories to
create a QES without having a physical device in their hands. In this
instance, signatories remotely access a signing key, which is stored in a
trusted service provider’s data centre. This is often the preferred choice
for organisations since it streamlines device management. A QES must also be
based on a ‘qualified certificate for electronic signatures’, which is
another key difference between an AES and a QES. Only ‘Qualified trust
service providers’ (QTSPs) listed on the European Union’s trusted provider
database can issue this certificate. To become a QTSP, organisations must
successfully complete a series of evaluations and audits that ensure
compliance with eIDAS regulations.
Top cloud strategy mistakes CIOs can’t help making

“Not architecting for the cloud,” says IDC analyst Dave McCarthy, when asked
where CIOs commonly go wrong when building their cloud strategy. “While it
is possible to ‘lift and shift’ existing workloads, enterprises often
experience less than desirable costs and performance with this approach. You
need to adapt applications to cloud-native concepts to realize the full
value.” CIOs also often make the mistake of “not implementing enough
automation,” says McCarthy, who is research vice president of cloud and edge
infrastructure services for IDC. “Best practices in cloud include automating
everything from the deployment of infrastructure and applications to
management and security. Most outages or security breaches are the result of
manual misconfigurations. But perhaps the worst sin CIOs can make, analysts
across the spectrum agree, is fail to plan for the shift in culture and
skills required to devise and implement a successful cloud strategy. The
cloud functions differently than traditional IT systems, and a cloud
strategy must not only require new skills but a change in thinking about how
to design and manage the environment, McCarthy says.
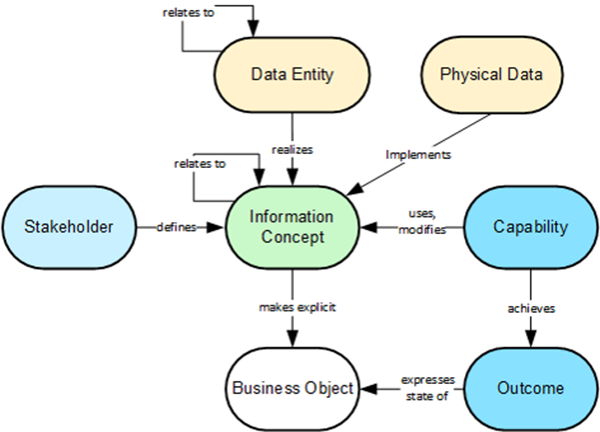
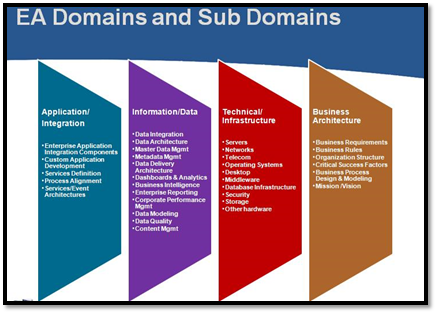
What is a business architect and how do you become one?

An enterprise architecture is comprised of different kinds of components
(business strategy and outcome, technology platforms and infrastructure, and
security), and a business architecture encompasses how all these things come
together to best serve the business. It is a component of enterprise
architecture. My responsibility as a business architect is to manage the
business architecture practice and its governance. I primarily focus on
establishing standards and best practices for our team's deliverables and
developing relationships within our organization. I also collect information
on our business and map domains (including capabilities, value streams,
information, and organization) according to the business architecture
framework to gain insights. I think business architecture is foundational to
organizations today. A strategy is a plan of action to achieve a goal. My
team receives business ideas and potential projects that align with our
organization's strategies and influence our performance as a leader in our
market.
Quote for the day:
"The leader has to be practical and
a realist, yet must talk the language of the visionary and the idealist."
-- Eric Hoffer