The number of data breach reports filed since GDPR went into effect has hit about 3,500 in Ireland, over 4,600 in Germany, 6,000 in France and 8,000 in the U.K. GDPR also gives Europeans the ability to file class-action lawsuits against breached organizations, and some law firms have already been exploring these types of actions. And under article 77 of GDPR - "Right to complain to a supervisory authority" - Europeans can also file complaints with regulators about organizations' data protection practices, as they were also able to do before enactment of the new regulation. Regulators say these complaints have also been increasing. Numerous national data protection authorities say they have seen an increase in both complaints as well as breach reports. But as information security expert Brian Honan has told Information Security Media Group, the increase in data breach reports does not mean there has been a surge in data breaches
Everything you need to know about the CDO explained
Because the role is so reliant on the use of technology, there is an overlap with the CIO position -- and there's some competition as a result, says Ellis. Yet rather than being experts in IT implementation, CDOs are commonly characterised as change agents. "Where CDOs can be very effective, and can initiate new approaches quickly, is where they buy cloud services and avoid in-house IT development in a traditional sense," says Ellis. "CIOs remain the owners of the technology infrastructure of any company." CDOs tend to be strong communicators. They talk about the power of disruption and get people to buy into change. Darren Curry, CDO at NHS Business Services Authority, says the role is about more than implementing digital services. "I support people, identify a vision and enable our people to do their very best," he says. "I see myself as leader who removes the blockers and barriers to allow our people to achieve their aims for our services. That's what I feel any leader -- whether that's a CDO or another senior role -- should be working to achieve."
Regardless of use case, AI/ML success depends on making the right infrastructure choice, which requires understanding the role of data. AI and ML success is largely based on the quality of data fed into the systems. There’s an axiom in the AI industry stating that “bad data leads to bad inferences”— meaning businesses should pay particular attention to how they manage their data. One could extend the axiom to “good data leads to good inferences,” highlighting the need for the right type of infrastructure to ensure the data is “good.” Data plays a key role in every use case of AI, although the type of data used can vary. For example, innovation can be fueled by having machine learning find insights in the large data lakes being generated by businesses. In fact, it’s possible for businesses to cultivate new thinking inside their organization based on data sciences. The key is to understand the role data plays at every step in the AI/ML workflow.
The Role Of Data Governance In An Effective Compliance Program
Data governance becomes more important the more systems and applications a compliance function uses. Compliance officers want systems that store data in a single repository with standardized data formats because strong data governance ensures accurate reports. From there, compliance officers can make accurate decisions based on what the data tells them. Here’s the rub: The current landscape of compliance technology is composed of many disparate systems that don’t integrate with each other. Compliance officers are often stuck searching for critical data and don’t have a connected approach to the technology that supports their program. They want and need a system that stores data in a single repository with standardized data. How can data governance fix this problem? Automating a compliance program’s many tasks helps to create a unified operations environment. In this paradigm, the compliance function goes beyond its tasks of third-party due diligence and training.
Scaling Observability at Uber
Srivatsan states that "high cardinality has always been the biggest challenge for our alerting platform." As Aaron Sun writes, "cardinality in the context of monitoring systems is defined as the number of unique metric time series stored in your system's time series database." Originally, Uber handled their high cardinality by having alert queries return multiple series and having rules that trigger only if enough series crossed a threshold. This worked well with queries that returned a bounded number of series with well-defined dependencies. However, once teams started writing queries to alert on a per city, per product, and per app version to support their new product lines, the queries no longer fit this constraint. The team began leveraging Origami to help with these more complicated queries. As noted above, Origami is capable of deduplication and rollup of alerts. It is also capable of creating alerts on combinations of city, product, and app version which are then triggered on aggregate policies.
5 steps to getting started with robotic process automation
At the extremes, some businesses go big and “all in” right away, while others are more measured with an individual use case to provide proof points before further deployment. Many others take a hybrid approach that lies somewhere in between. Getting started with RPA may look different from business to business, but designing a proof-of-concept project is often the best way to jumpstart RPA efforts in your organization. Depending on the structure of your organization, change may not always come swiftly. Executives need proof points when making major decisions such as augmenting or flat-out reimagining long-standing processes. When it comes to RPA, using these five steps to assess your organization's processes and determine which would make for a high-impact proof of concept will set you up for both short- and long-term automation success. And remember — it’s not about replacing jobs. It’s more about handling mundane or time-consuming tasks in a more efficient manner to enable your teams to spend more time concentrating on meaningful work.
Hackers Bypass Gmail, Yahoo 2FA at Scale
Amnesty discovered several credential phishing campaigns, likely run by the same attacker, targeting hundreds of individuals across the Middle East and North Africa. One campaign went after Tutanota and ProtonMail accounts; another hit hundreds of Google and Yahoo users. The latter was a targeted phishing campaign designed to steal text-based second-factor codes. Throughout 2017 and 2018, human rights defenders (HRDs) and journalists from the Middle East and North Africa shared suspicious emails with Amnesty, which reports most of this campaign's targets seem to come from the United Arab Emirates, Yemen, Egypt, and Palestine. Most targets initially receive a fake security alert warning them of potential account compromise and instructing them to change their password. It's a simple scheme but effective with HRDs, who have to be on constant high alert for physical and digital security. From there, targets are sent to a convincing but fake Google or Yahoo site to enter their credentials; then they are redirected to a page where they learn they've been sent a two-step verification code.
FBI kicks some of the worst ‘DDoS for hire’ sites off the internet
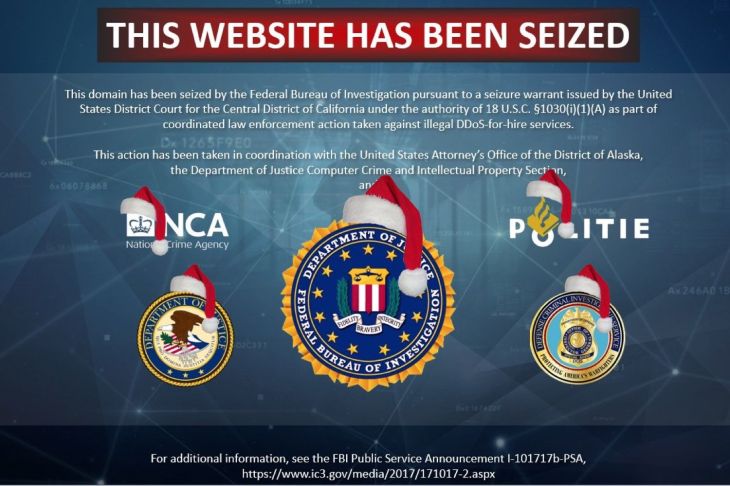
Several seizure warrants granted by a California federal judge went into effect Thursday, removing several of these “booter” or “stresser” sites off the internet “as part of coordinated law enforcement action taken against illegal DDoS-for-hire services.” The orders were granted under federal seizure laws, and the domains were replaced with a federal notice. Prosecutors have charged three men, Matthew Gatrel and Juan Martinez in California and David Bukoski in Alaska, with operating the sites, according to affidavits filed in three U.S. federal courts, which were unsealed Thursday. “DDoS for hire services such as these pose a significant national threat,” U.S. Attorney Bryan Schroder said in a statement. “Coordinated investigations and prosecutions such as these demonstrate the importance of cross-District collaboration and coordination with public sector partners.” The FBI had assistance from the U.K.’s National Crime Agency and the Dutch national police, and the Justice Department named several companies, including Cloudflare, Flashpoint and Google, for providing authorities with additional assistance.
Connecting Business Challenges and Emerging Technologies
Robotic Process Automation (RPA) can be used to automate tasks previously done by human beings, said O’Carroll. It is often applied to repetitive and mundane tasks – the ones often seen as boring. With RPA you can have a robot doing it for you, she said. Solutions based on RPA technology have decisions built in which enable you to do creative work. She explained how you could train a robot to do purchase orders by building rules to extract information from an email, enter the information into the purchase order system, and generate the purchase order. O’Carroll mentioned use cases for RPA: case management (for instance in healthcare), HR for administrating joiners, movers, people leaving, and banks. It can be cheaper to do these activities with robots, and automation can give people more time to spend with customers, she argued. Machine learning (ML) and artificial intelligence (AI) are a different kind of technology as they are based on how our brain works with neural networks, said O’Carroll. It’s about predicting the right answer and getting better at it.
How AI-powered commerce will change shopping
If you think AI is over-hyped from a commerce point of view, think again. Research shows that customers are 9.5X more likely to view AI as revolutionary versus insignificant. Within the next five years, 87 percent of customers believe AI will have transformed their expectations of companies. But how, exactly, is AI changing expectations? While pop culture sometimes paints AI with a scary science-fiction hue, the truth is that many AI-driven experiences are winning customer appreciation, if not affection. A majority of customers say they like or love AI-powered capabilities like credit card fraud detection, personalized recommendations, and voice-activated personal assistants. And today, "personalized recommendations" doesn't mean merely adding an individual's name to an email subject line. We're talking about uber-personalized communications; 59 percent of customers say tailored engagement based on past interactions is very important to winning their business.
Quote for the day:
"Leaders think and talk about the solutions. Followers think and talk about the problems." -- Brian Tracy

No comments:
Post a Comment