How businesses can combat data security and GDPR issues when working remotely

Whether using a business or personal device, having robust Secure Device
Management and effective Mobile Device Management (MDM) is key to implementing
security measures to keep data on mobile devices secure from threats. Adopting
data encryption across software and devices being used remotely also allows data
to be kept safe and secure from unauthorised use, even in the event of a
security breach. In addition, implementing a corporate Virtual Private Network
(VPN) enables an encrypted connection from a device to a network that allows the
safe transmission of data from the office to remote working environments.
Employees should have access only to the data they require to complete their
work to mitigate against unnecessary risk of unauthorised access, with measures
that restrict data on a ‘need-to-know’ basis implemented where possible.
Crucially, companies should provide all employees working from home with a clear
and documented remote working policy that outlines precisely how personal and
company data should be handled to keep it secure.
Digital transformation: 4 excuses to leave behind

Outdated, manual, and siloed processes not only slow your business, but they
boost costs because it is more expensive to maintain broken, outdated processes.
As we emerge from the pandemic, most businesses are realizing that their
existing business processes are not sustainable in the new normal. With remote
and hybrid work becoming standard, organizations have had to think on their feet
to maintain business as usual, and digital transformation makes this possible.
COVID lockdowns made it urgent for enterprises to enable secure remote
operations, which in turn made them realize the importance of migrating their
operations to the cloud. There has been an exponential increase in the adoption
of cloud technology post-pandemic. It has enabled businesses to operate in a
remote environment without impacting the speed and quality of services. If you
haven’t already done so, start by identifying the “low-hanging fruit” – i.e.,
processes that are best for your initial automation roadmaps. Then start scaling
up. Transitioning to the cloud gives you countless possibilities, from reducing
IT infrastructure costs to achieving scalability per business needs.
4 questions that get the answers you need from IT vendors

Enterprises don’t plan on how to adopt abstract technology concepts, they plan
for product adoption and deployment. Network vendors who offer the products
are the usual source of information, which can be delivered through news
stories, vendor websites, or sales engagement. Enterprises expect the seller
to explain why their product or service is the right idea, and sellers largely
agree. It’s just a question of what specific sales process is supposed to
provide that critical information. Technology salespeople, like all
salespeople make their money largely on commissions. They call on prospects,
pitch their products/services, and hopefully get the order. Their goal is a
fast conversion from prospect to customer, and nearly all salespeople will
tell you that they dread above all the “educational sell”. That happens when a
prospect knows so little about the product/service being sold that they can’t
make a decision at all and have to be taught the basics. The salesperson who’s
teaching isn’t making commissions, and their company isn’t hitting their
revenue goals.
3 Things to Consider Before Investing in New Technology for Your Small Business
When you are searching for tech to suit your business's unique needs, it’s
important to keep the happiness of your employees at the forefront. That’s what
authentically attracts new talent to your company and entices people to stay. In
many cases, happiness is derived from productivity. If workers know what they
need to do but just don’t have the tools to do it quickly, they will get
discouraged and customers will complain because they didn’t have a great
experience. So, stop and assess why they’re experiencing each challenge as they
move through tasks. Consider what you genuinely wish could be better or easier
for you, your employees and everyone else involved. Then think about how
technology may be able to solve each problem. If you equip a first-day employee
with a mobile device that helps them get through a full inventory count
comfortably and without making a single mistake, they are going to leave work
feeling empowered. They’ll share their positive experience with friends, family
and (if you’re lucky) social media. Word will spread about how great it is to
work for your company.
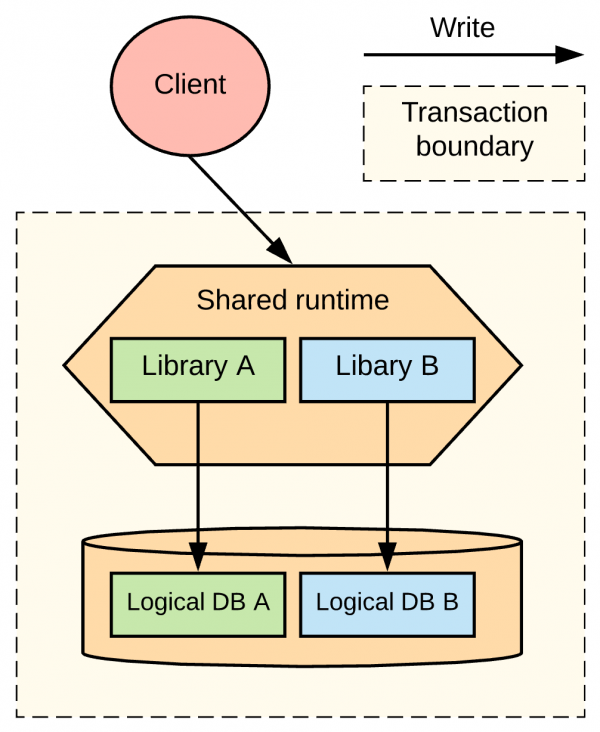
Cloud Cost Optimization: A Pivotal Part of Cloud Strategy

To maintain an optimal state, you need to ensure that sound policies around
budgeting are adhered to. In terms of Governance, the framework should oversee
resource creation permissions as well. ... Once you gain visibility into
spending metrics, you must observe which unused resources can be disposed of and
which resources could be optimized. The journey for any cloud cost optimization
starts with initial analyses of current cloud estate and identifying
optimization opportunities across compute, network, storage, and other
cloud-native features. Any cloud cost optimization framework needs to have a
repository of cost levers with associated architecture and feature trade-offs.
Businesses would need governance — the policies around budget adherence,
resource creation permissions, etc. — to maintain an optimal state. A practical
cost optimization framework requires all three of the above. Achieving initial
savings would entail analyzing the estate and identifying optimization
opportunities across compute, storage, and networking, focusing on the highest
costs first and/or incremental/additional cost, month over month- cloud vendors
provide access to the costs and utilization.
Applying Behavioral Psychology to Strengthen Your Incident Response Team

Orlando says it's natural for relationships to form, and for trust to form, in
an incident response team and within a larger organization. In his experience,
he often encounters what he calls the "rock star problem." "You've got one or a
few people [who are] very, very capable, very knowledgeable, and the team sort
of coalesces around those individuals," he says. "Which is not necessarily a bad
thing, but it can create issues when those individuals inevitably move on, or
maybe they [have] less than optimal work habits, or behaviors, or things we want
to try to account for." Compounding CSIRTs' collaboration issues is a prominent
focus on technical tools and skills, Orlando adds. Incident response teams are
"often inundated" with tools to address technical problems in security and
incident response; however, there is a "definite lack" of tools to address some
of the social and collaboration challenges CSIRTs face in operating within the
context of a multigroup, multiteam system as they need to do.
Netherlands Says Armed Forces May Combat Ransomware Attacks

Countries are being held accountable for their actions and inaction via
diplomatic responses such as actions against cross-border criminal cyber
operations and measures such as sanctions, which are more powerful if they are
designed in a broad coalition context, Knapen says. "Within the EU, the
Netherlands has therefore been a driving force behind the EU Cyber Diplomacy
Toolbox and the adoption of the ninth EU cyber sanctions regime in May 2019, and
the Netherlands is committed to further developing these instruments. This
provides the EU with good tools to respond faster and more vigorously to cyber
incidents. Recent EU statements and sanctions show that these instruments are
delivering concrete results," he notes. Knapen is also pushing for diplomatic
channels for bilateral cooperation between countries in judicial investigations
against ransomware, which he says can be useful if cooperation through
international judicial channels is insufficient. "The Netherlands can then
emphasize the importance attached to cooperation through diplomatic channels,"
he says.
Can India Address the Growing Cybersecurity Challenges in the Nuclear Domain?
India has established several key agencies to counter the growing challenges
on cybersecurity. However, the effectiveness of its cybersecurity policies in
the nuclear domain lies with the ability to effectively incorporate
cybersecurity, cyber infrastructure, and its operating agencies into the
larger nuclear security framework. Efficient and effective cybersecurity
mechanisms require cohesive inter-agency coordination to strengthen said
mechanisms. It is also essential for government authorities to acknowledge,
interact with, and evolve cybersecurity protocols and procedures regularly to
reflect a rapidly changing security environment. An effective cybersecurity
policy also requires clear demarcation of roles, responsibilities, and
contingency plans for short and long-term implementation and altering based on
circumstances and technological advancements. Additionally, and most
importantly, a renewed emphasis on understanding cyber risks and acknowledging
the importance of cyber-nuclear security is essential in the Indian
context.
How technology can drive positive change in insurance post-COVID

From forced closures to operational transformation, the COVID-19 pandemic has
impacted businesses both UK and worldwide. The world of insurance is no
exception to this rule – but the nature of the industry and its interests have
led to a layered set of challenges and opportunities beyond the obvious
disruptions to working practices. These challenges have been laid out in a
recent report from EY, which lists a number
of early pandemic issues for the industry including the tricky transition to
remote working, a “strong push toward digitisation”, and the embrace of
virtual interactions for clients and distribution partners. While these
concerns may feel familiar, EY’s report goes on to draw out the specific
difficulties faced by insurers, where COVID-19 has occasioned “mounting
consumer, political, and legislative pressure to cover pandemic-related
business interruption claims”. Not only has the industry needed to embrace new
technologies and practices to adapt to the pandemic, but it has also needed to
address some of the COVID-driven burdens faced by clients.
Safe and secure disposal of end-of-life IT hardware

First, your business needs to develop a plan of action that brings together
your IT, information security and office management staff, with oversight from
senior executives. To be fully effective, it should establish a
decommissioning strategy that covers the compliant disposal of retired
hardware and the destruction of data. Next, you need to ensure that all the
data on your old hardware has been permanently eradicated and is
non-recoverable. Given the importance of this step, it is likely that you’ll
need assistance from a third-party disposition expert. Third, you need to know
the whereabouts of your assets throughout the disposition process. A secure
chain of custody is vital to prove compliance and so, once again, it is
advisable to employ the services of an outside expert – a company that offers
rigorous security practices, such as asset itemisation, GPS tracking and
protected transportation, all backed up with supporting documentation. Having
a secure chain of custody is critical because it ensures that the IT assets
are tracked during each step of the process from pick-up to final
disposition.
Quote for the day:
"The final test of a leader is that he
leaves behind him in other men, the conviction and the will to carry on." --
Walter Lippmann



.png?width=1500&name=ardoq-content-SecurityMonth(2).png)