The future of IT: Snapshot of a modern multi-cloud data center

The idea of cloud computing remains simplicity itself, which is a key element of its appeal: Move the cost and complexity of procuring, provisioning, operating, and supporting an endless array of hardware, software, and enabling services for your business out to a 3rd party, which does it all it for you, yet more securely and with much greater economies of scale. Writ large across virtually all industries, a comprehensive shift to the cloud thus continues to be a top objective of CIOs in many organizations this year. Even the objective, despite misgivings that we're really just going back to the monolithic IT vendor world again. Not surprisingly, enabling such a strategic move is also the top business goal of the leading commercial cloud vendors, namely Amazon, Microsoft, and Google, who continue to vie vigorously for marketshare, technical leadership, and -- some would say -- the most interesting and valuable part of the market itself ... Hosting companies like Rackspace and others used to be able to provide a hedge that IT departments could use for such purposes, through services like co-location. However, most such providers have not been able to keep up with the overall capacity race or compete in the bruising cost efficiency battles that the top cloud providers can afford to wage.
The Containerization of Artificial Intelligence
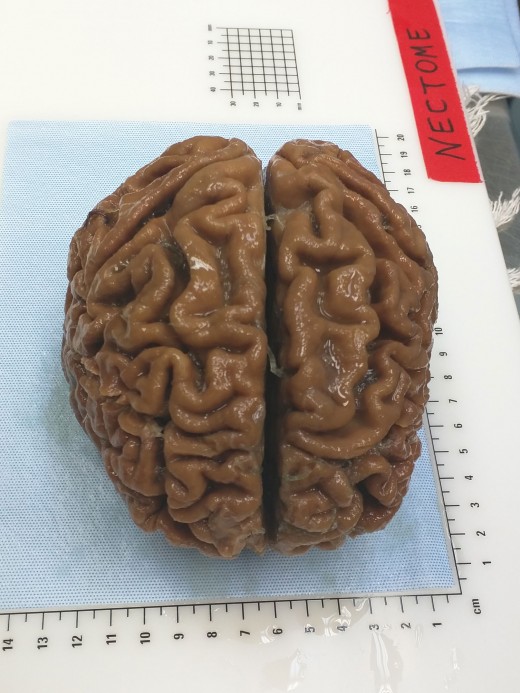
While AI is more hype than reality today, machine intelligence — also referred to as predictive machine learning — driven by a meta-analysis of large data sets that uses correlations and statistics, provides practical measures to reduce the need for human interference in policy decision-making. A typical by-product of such application is the creation of models of behavior that can be shared across policy stores for baselining or policy modifications. ... Adoption of AI can be disruptive to organizational processes and must sometimes be weighed in the context of dismantling analytics and rule-based models. The application of AI must be constructed on the principle of shared security responsibility; based on this model, both technologists and organizational leaders will accept joint responsibility for securing the data and corporate assets because security is no longer strictly the domain of specialists and affects both operational and business fundamentals.
AI & Blockchain: 3 Major Benefits Of Combining These Two Mega-Trends
AI, as the term is most often used today is, simply put, the theory and practice of building machines capable of performing tasks that seem to require intelligence. Currently, cutting-edge technologies striving to make this a reality include machine learning, artificial neural networks and deep learning. Meanwhile, blockchain is essentially a new filing system for digital information, which stores data in an encrypted, distributed ledger format. Because data is encrypted and distributed across many different computers, it enables the creation of tamper-proof, highly robust databases which can be read and updated only by those with permission. Although much has been written from an academic perspective on the potential of combining these ground-breaking technologies, real world applications are sparse at the moment. However, I expect this situation to change in the near future. So here are three ways in which AI and blockchain are made for each other.
Cyber criminals using complex financial system, study shows

The findings on cyber criminal money-laundering and cashing-out methods are part of a study into the macro economics of cyber crime and how the various elements link together which has been led by Michael McGuire, senior lecturer in criminology at Surrey University. “This is the first time the financial flows of cyber criminals have been put together into a composite picture,” said McGuire, who will present the full findings of the nine-month Web of profit study at the RSA Conference in San Francisco from 17-19 in April. “Law enforcement and cyber security professionals can use the study to understand how revenue generation is feeding into laundering, and how laundering is feeding into more traditional methods of money-laundering and the way cyber criminals are spending their money, so that they look at the intersections between the various networks more carefully,” he told Computer Weekly.
To OSPF Or Not? Which Routing Protocol To Use
OSPF with a multipoint MAN is a classic DR/BDR LAN situation, reducing the amount of peer-to-peer flooding. I haven’t run into this at large scale in a design setting yet. Would having such a MAN provide a pretty good reason to run OSPF overall? How would one damp instability in such a network? Large failure domain? What number of peers is “too big” for a full mesh MAN? The other problem I’m still mulling over is the OSPF WAN to dual datacenters design. In one case, a customer was running more than 250 VLANs (one per area) over DWDM, and more recently over OTV between datacenters, with more than 4000 GRE over IPsec tunnels. Dual hub DMVPN and BGP route reflectors looks very attractive compared to that. “Totally stubby EIGRP” — hubs that advertise only 0/0 or corporate default to remote sites — could also work well. By the way, if you are using EIGRP, note Cisco’s clever recent stub-site feature, which was probably built to simplify IWAN.
5 Applications Of Smart Contracts

Due to a lack of automated administration, it can take months for an insurance claim to be processed and paid. This is as problematic for insurance companies as it is for their customers, leading to admin costs, gluts, and inefficiency. Smart contracts can simplify and streamline the process by automatically triggering a claim when certain events occur. For example, if you lived in an area that was hit by a natural disaster and your house sustained damage, the smart contract would recognise this and begin the claim. Specific details (such as the extent of damage) could be recorded on the blockchain in order to determine the exact amount of compensation. ... The terms of a mortgage agreement, for example, are based on an assessment of the mortgagee’s income, outgoings, credit score and other circumstances. The need to carry out these checks, often through third parties, can make the process lengthy and complicated for both the lender and the mortgagee. Cut out the middle men, however, and parties could deal directly with each other (as well as access all the relevant details in one location).
China wants to shape the global future of artificial intelligence
“[The Chinese government] sees standardization not only as a way to provide competitiveness for their companies, but also as a way to go from being a follower to setting the pace,” says Jeffrey Ding, a student at Oxford University’s Future of Humanity Institute who studies China’s nascent AI industry, and who translated the report. The government’s plan cites the way US standards bodies have influenced the development of the internet, expressing a desire to avoid having the same thing happen with AI. China’s booming AI industry and massive government investment in the technology have raised fears in the US and elsewhere that the nation will overtake international rivals in a fundamentally important technology. In truth, it may be possible for both the US and the Chinese economies to benefit from AI. But there may be more rivalry when it comes to influencing the spread of the technology worldwide. “I think this is the first technology area where China has a real chance to set the rules of the game,” says Ding.
Open Source & Smart Mobility In The Transportation Industry

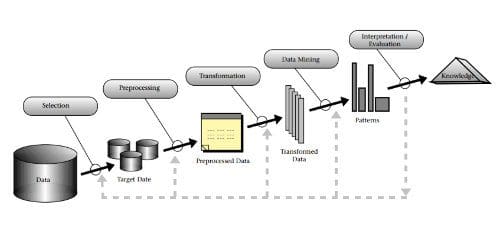
Open source projects in the big data space move their development and feature sets along quickly to harness the latest enhancements in technology, performance, and scalability. New best practices get baked into data platform solutions very quickly, and a huge community of data scientists, scripters, and programmers all works toward the same goal, making best-of-breed technology available to anyone. At the foundational level, innovation occurs so rapidly that it is unrealistic to expect a vendor to encapsulate all these new developments in anything but a proprietary solution layered on top. Selecting an open source platform for data projects removes any risk of vendor lock-in. When it comes to the data space, like most things, putting all your eggs in one basket is inadvisable. Much of the innovation that is occurring in the open source data space is directly attributable to the best and brightest minds’ aversion to being tied down to a single vendor, making a shared effort much more attractive.
Transforming Bank Compliance with Smart Technologies
Digitization, the final stage in the transformation process, has the potential to create a step change in compliance operations. The catalyst is the emergence of smart technologies, which offer significant performance improvements and the ability to mimic human capabilities such as learning, language use, and decision making. Smart technologies have multiple potential applications in the context of compliance, from support for relatively routine tasks in client onboarding to analysis of unstructured data sets—for example, in relation to money laundering. Across the board, these technologies offer a route to significant efficiency gains and can help employees work more effectively. The starting point in building a cutting-edge compliance framework is to establish a taxonomy that describes and classifies key areas of risk. Such a taxonomy is also a prerequisite for defining the scope of a target operating model. The six most relevant types of compliance risks relate to financial crime and conduct.
IBM sets up no-fee Data Science Elite team to speed up AI adoption
Big Blue is calling the latter “Cloud Private for Data”, based on an in-memory database. It adds up to a platform for doing data science, data engineering and app building. IBM said the aim is to “enable users to build and exploit event-driven applications capable of analysing data from things like IoT [internet of things] sensors, online commerce, mobile devices, and more”. ... IBM is also announcing a “Data Science Elite Team”, described as a “no-charge consultancy dedicated to solving clients’ real-world data science problems and assisting them in their journey to AI”. Patricia Maqetuka, chief data officer at South African bank Nedbank, has used the team. She said: “Nedbank has a long tradition of using analytics on internal, structured data. Thanks to IBM Analytics University Live, we were exposed to the guidance and counsel of IBM’s Elite team. This team helped us to unlock new paradigms for how we think about our analytics and change the way we look at use cases to unlock business value.”
Quote for the day:
"Don't waste words on people who deserve your silence. Sometimes the most powerful thing you can say is nothing at all." -- Joubert Botha