Just what the heck does an ‘AI PC’ do?

As the PC market moves to AI PCs, x86 processor dominance will lessen over time, especially in the consumer AI laptop market, as Arm-based AI devices grab more share from Windows x86 AI and non-AI laptops, according to Atwal. “However, in 2025, Windows x86-based AI laptops will lead the business segment,” Atwal said. ... “We see AI-enabled PCs evolving to provide more personalized, adaptive experiences that are tailored to each user’s needs,” Butler said. “The rise of generative AI was a pivotal moment, yet reliance on cloud processing raises concerns around data privacy.” Each component of a PC plays a unique role in making AI tasks efficient, but the NPU is key for accelerating AI computations with minimal power consumption, according to Butler. In general, he said, AI PCs assist in or handle routine tasks to be more efficient and intuitive for users without the need to access an external website or service. ... AI PCs can also boost productivity by handling routine tasks such as scheduling and organizing emails, and by enhancing collaboration with real-time translation and transcription features, according to Butler.
Humanity Protocol: ‘We’re building a full credential ecosystem’

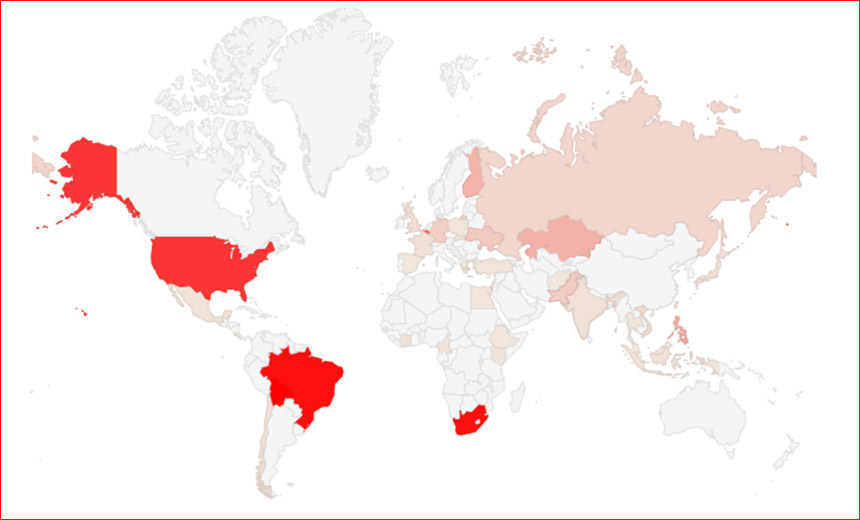
Distinguishing between humans and machines online has become more important than ever. Over the past years, the digital world has seen a proliferation of AI-fueled deepfake impersonations, bots and Sybil attacks, in which a single entity creates many false identities to gain influence. An increasing number of companies are trying to come up with solutions relying on blockchain technology. One of the more well-known projects is World Network, previously known as Worldcoin, which scans irises to confirm their users are human. But the space is seeing more and more competitors relying on biometrics to prove people are real – including Humanity Protocol. “There are definitely a bunch of companies that are trying to solve the whole Proof of Personhood problem,” the company’s founder Terence Kwok told Biometric Update in an interview earlier this month. “We’re lucky to be one of the few that have started launching, building a user base and joined the market.” The company launched a testnet in October, allowing users and developers to get their first taste of the platform and receive some free cryptocurrency. The project has so far signed up over a million people – moving quickly to catch up with World Network which currently has 15 million users, including 7 million verified through its Orb iris-scanning technology.
The way we measure progress in AI is terrible

Benchmark creators often don’t make the questions and answers in their data set
publicly available either. If they did, companies could just train their model
on the benchmark; it would be like letting a student see the questions and
answers on a test before taking it. But that makes them hard to evaluate.
Another issue is that benchmarks are frequently “saturated,” which means all the
problems have been pretty much been solved. For example, let’s say there’s a
test with simple math problems on it. The first generation of an AI model gets a
20% on the test, failing. The second generation of the model gets 90% and the
third generation gets 93%. An outsider may look at these results and determine
that AI progress has slowed down, but another interpretation could just be that
the benchmark got solved and is no longer that great a measure of progress. It
fails to capture the difference in ability between the second and third
generations of a model. One of the goals of the research was to define a list of
criteria that make a good benchmark. “It’s definitely an important problem to
discuss the quality of the benchmarks, what we want from them, what we need from
them,” says Ivanova. “The issue is that there isn’t one good standard to define
benchmarks. This paper is an attempt to provide a set of evaluation criteria.
That’s very useful.”
Governance Considerations and Pitfalls When Implementing GenAI
Many large organizations are still in the process of establishing robust
information governance frameworks for their current environments. Now, they
must also address questions about their readiness to manage the impact of
Copilot1
and similar generative AI tools. These questions include whether they can
uphold appropriate access, use, and management across their IT
infrastructure. Additionally, organizations should assess whether new
artifacts are being created that could introduce unforeseen regulatory risk.
... With Copilot, anything a user has permission to access may surface as
part of a response to a query or prompt. Without Copilot, when users are
over-permissioned and have access to documents that they should not, they
would only uncover the document if actively searching for it. Therefore,
excess permissions and failure to limit access to certain materials can
potentially expose information to far more employees than intended. To
manage this, organizations must be diligent in defining controls and
thoroughly understand the range of materials that Copilot users can access
at different permission levels. Notably, when Copilot is turned on for a
user, every application within Microsoft 365 that has a Copilot element will
have AI activated.
Next-Gen Networking: Exploring the Utility of Smart Routers in Data Centers
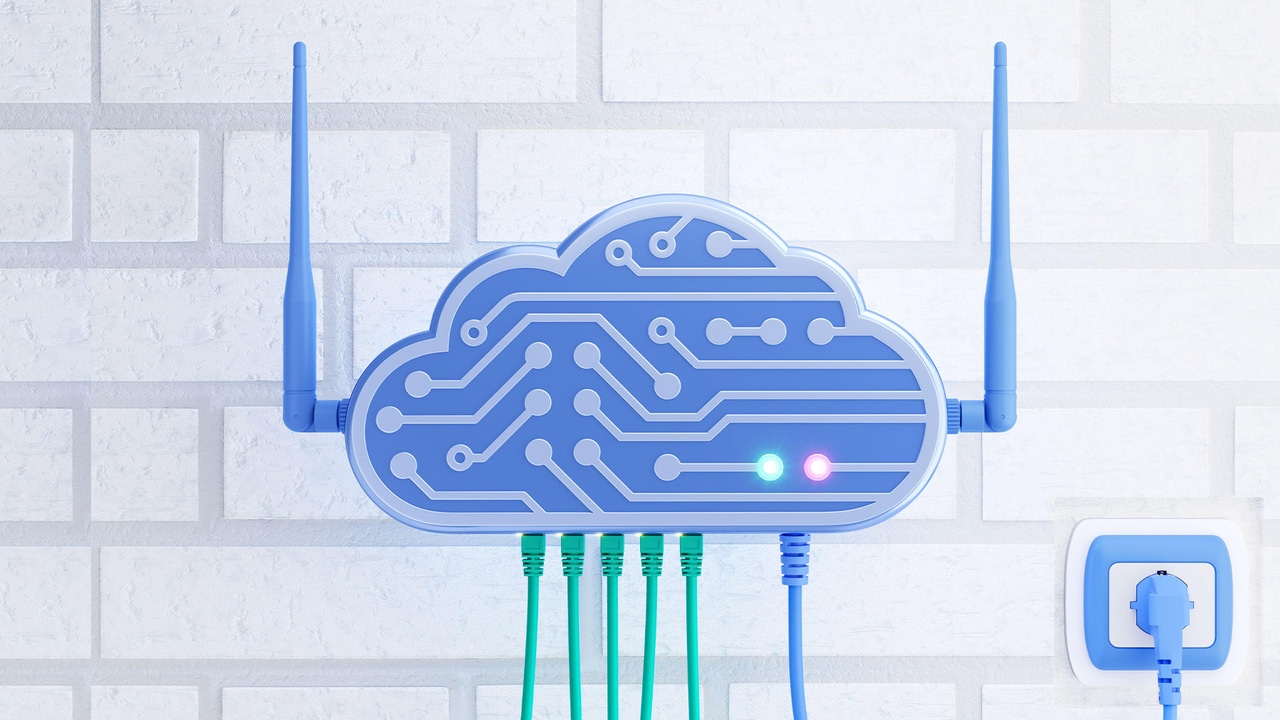
In cases where smart routers offer automated network management capabilities,
they usually do so based on software that provides features like the ability
to reroute packets to help balance network load or discover new devices
automatically when they join the network. In this sense, smart routers don’t
really do anything all that new; the sorts of capabilities just mentioned have
long been a standard part of network management software. The only
differentiator for smart routers, perhaps, is that these devices come bundled
with software that enables them to help manage networks automatically, instead
of requiring additional network management tools for that purpose. In
addition, there seems to be a focus in smart router land on the notion of
hands-off network management. Instead of requiring admins to configure
networking policies and apply them manually, smart routers promise in many
cases to manage your networks for you. It's essentially an example of what you
might categorize as NoOps. It’s worth noting, too, that in more than a few
cases, smart router vendors are slapping the “AI” label on their devices. But
like many vendors who profess to be selling AI-powered solutions today,
they're using the term loosely to refer to any type of software that uses data
analytics in some sort of way.
Digitising India with AI-based photogrammetry software

Photogrammetry is the capturing of measurements from photographs shot by
drones, satellites, or aerial photography and generating maps, and 3D models
even up to including a Geographic Information System (GIS). Traditionally,
photogrammetric processing involved collecting a huge amount of data through
manual efforts with post-processing taken care of by experts over a
considerable period. The introduction of AI and machine learning into
photogrammetry, has smoothened all these processes to make them fast as well
as more automation-friendly. Now with AI photogrammetry software, one can
explore thousands of aerial images automatically to acquire accurate
topographic maps and also in real-time 3D models. ... Errors in land surveys
can be very expensive and lead to many complications, especially in
construction, farming, and city management. Using AI-based photogrammetry
increases accuracy in measurement and reduces human errors in the process. AI
algorithms improve the quality of the resultant maps and models by identifying
and rectifying any anomalies in the data automatically. The system can also
blend images from different sources, such as aerial pictures, LiDAR
departments, as well as satellite images, to provide a better and more
accurate picture of the land.
Will AI Kill Google? Past Predictions of Doom Were Totally Wrong

Sam Altman, the top executive overseeing ChatGPT, has said that AI has a good
shot at shoving aside Google search. Bill Gates predicted that emerging AI
will do tasks like researching your ideal running shoes and automatically
placing an order so you'll "never go to a search site again." ... AI
definitely could draw us away from Google in ways that smartphones and social
media didn't. When you're planning a garden, an AI helper might guide you
through where you want the flowers and fruit trees and hire help for you. No
Googling necessary. "People are increasingly turning to ChatGPT to find
information from the web, including the latest news," Altman's company,
OpenAI, said. Maybe it's right to extrapolate from how people are starting to
use AI today. Or maybe that's the mistake that Jobs made when he said no one
was searching on iPhones. It wasn't wrong in 2010, but it was within a few
years. Or what if AI upends how billions of us find information and we still
keep on Googling? "The notion that we can predict how these new technologies
are going to evolve is silly," said David B. Yoffie, a Harvard Business School
professor who has spent decades studying the technology industry.
Practical strategies to build an inclusive culture in cybersecurity
Despite meaningful progress, the cybersecurity and IT industries continue to
face significant challenges in creating truly inclusive environments.
Unconscious bias remains a pervasive issue, often influencing hiring,
evaluation, and promotion processes, which can disadvantage women and other
underrepresented groups. Retention is another ongoing challenge, as many
organizations struggle to cultivate workplace cultures that are welcoming and
supportive enough to retain diverse talent long-term. Barriers to entry and
advancement persist, highlighting the need for continuous improvement and
active intervention. While the industry has made strides in recognizing the
importance of diversity, achieving full representation and inclusivity
requires sustained commitment and effort. The current focus on diversity is
encouraging, but only through consistent attention and action will the
industry overcome these longstanding challenges and ensure a more equitable
future. ... Work-life balance is another significant issue, particularly in
cultures where traditional gender roles are still prevalent. Women often face
greater expectations regarding balancing work and family, which can impact
their career trajectory, especially in environments that lack flexible work
arrangements.
5 ways to achieve AI transformation that works for your business

"Never work in a silo and prepare to be wrong in terms of how you've set the
technology up." Kollnig and her colleagues have implemented the Freshworks
Customer Service Suite, an omnichannel support software with AI-powered
chatbots and ticketing. She told ZDNET that working closely with the
technology partner has helped her team to deliver a successful AI
transformation. "So, for one of our AI projects, we established our basic
set-up and said, 'Freshworks, come in and audit it. Tell us, are we doing this
right? Would you do it differently?'" she said. ... Moyes said professionals
in all sectors should take some sensible steps, including working with people
who know more about AI. "Within every organization, there are groups of
technology leads who are interested and want to innovate, evolve, and push,"
he said. "Lean on them. Learn from those at the coal face who want to do AI.
There are no guarantees that the technologies you introduce will be the next
best thing, but at least you'll be aware of the potential." Moyes said
SimpsonHaugh is looking at how AI can reduce time-intensive tasks, such as
summarizing text, and help staff find images to create early-stage design
proposals.
What Does Enterprise-Wide Cybersecurity Culture Look Like?

Whoever is championing enterprise-wide security needs to secure buy-in from
everyone within an organization. At the top, that means getting the C-suite
and board to throw their weight behind security. “At the end of the day, if
you don't have the CEO on board and the CEO isn't … voicing the same level of
prioritization, then it will be something that's viewed as a half step back
from … fundamental business priorities,” Cannava warns. Effective
communication is a big part of getting that buy-in from leadership. How can
security leaders explain to their boards and fellow executives that security
is an essential business enabler? “Really [convert] the technology language or
cyber language or jargon into how will … that risk potential impact revenue or
reputation or our compliance?” says Landen. Tabletop exercises can be a
powerful way to not just tell but show executives the value of cybersecurity.
Walking through various cybersecurity incident scenarios can demonstrate the
vital connection security has to operations and business outcomes. Ping
Identity periodically engages multiple members of the C-suite in these
exercises. “Not only do you know learn what the gap is, you also learn by
doing … you're pulled in and engaged as a member of the C-suite, and now
you're invested,” he says.
Quote for the day:
"Great leaders do not desire to lead
but to serve." -- Myles Munroe