Indian IT companies have had to transform every part of their process for faster growth

To get here, Indian IT companies have had to change every part of their process—even becoming less Indian. They have shed jobs, changed how they work, upended part of their business models by focusing on hiring at client locations abroad, invested in training their employees, and chased acquisitions. The goal this time: growing digital revenue, in the hopes that it would offset the contraction in the traditional business, which is still over 60% of their revenues. “The core purpose of IT has changed to helping transform businesses and drive revenues from reducing cost and improving efficiency. This has led to a new wave of growth for IT, helping customers digitally transform their businesses,” said Hexaware CEO R Srikrishna. ... IT companies are looking at building the same campus recruitment engine in client markets as they did in India, and are focusing on current campus hires to become ambassadors for them at their universities. On Wednesday, Infosys announced it would hire 1,200 locals in Australia by 2020, over a third of whom would come from campuses.
With more and more Data Centers being built, and soon after we are done bashing the economy and again ready to make hay as the economy starts turning around, we can alter the shape of our destiny dramatically! As other industries will sag, think of hotels, airlines, etc., which will certainly contribute to a certain reduction of carbon emissions, there is strong reason to believe that the spin-offs from the remote-everything will go into overdrive. Today we are carefully talking about online conferences and soon there will be lots of online activities that will be firing up all over the place. This will lead to huge data crunch operations as more and more information will need more processing power as it will come in audio, video and other formats. This will be extremely demanding for data centers, no matter how centralized they are.
TechUK calls on Matt Hancock to fast-track NHS digitisation
Hancock has said he wants the health tech industry to thrive, which TechUK said is a great idea, but very far from the current status quo where tech companies find health and social care one of the most difficult sectors to “crack”. It called on Hancock to ensure better access to data and improved procurement. “Data, like oil, is worth nothing if it is left in the ground,” the manifesto said. “Far too much data is held in non-digital form or in siloed repositories making it impossible to join up. “Tech companies that need data to build, develop, test and prove their solutions find it difficult to access, while companies that produce valuable data find it difficult to feed back into the System to inform better decision making.”
What machine learning means for software development

Will machine learning eat software, as Pete Warden and Andrej Karpathyhave argued? After all, “software eating the world” has been a process of ever-increasing abstraction and generalization. A laptop, phone, or smart watch can replace radios, televisions, newspapers, pinball machines, locks and keys, light switches, and many more items. All these technologies are possible because we came to see computers as general-purpose machines, not just number crunchers. From this standpoint, it’s easy to imagine machine learning as the next level of abstraction, the most general problem solver that we’ve found yet. Certainly, neural networks have proven they can perform many specific tasks: almost any task for which it’s possible to build a set of training data. Karpathy is optimistic when he says that, for many tasks, it’s easier to collect the data than to explicitly write the program.
Socially Responsible Automation: A Framework for Shaping the Future
We define SRA as the set of technology choices, business strategies, innovation approaches, and management practices that move the affordances of automation beyond cost and performance efficiencies towards profitable and sustainable growth with more and better jobs driving economic development and social cohesion. SRA strives to optimize both business and social goals by adopting “common good” and “shared value” ideals. A minimal approach to SRA would be one where technology decisions are guided by their potential negative impact on jobs and the workforce; where mechanisms such as economic modelling, decision frameworks, and human factors approaches are employed to quantitatively and qualitatively assess technology choices and outcomes, and where appropriate trade-offs are made to balance the economic benefits of automation with the social costs of labor reduction and unemployment.
Chromecast (2018) review: Google's revamped media streamer is what you make of it

The new Chromecast isn’t much different from the second-generation model from 2015. The new design has rounder edges, but it’s still a small puck that hangs behind the TV on a 3-inch HDMI cable, and it still uses the TV’s USB port or a wall outlet for power. (You’ll likely need to choose the latter if you want the Chromecast to turn the TV on when it connects to your phone.) The way you use Chromecast hasn’t really changed, either: In lieu of a remote control and TV-based menus, Chromecast uses the streaming apps on your iOS or Android device as the interface. Apps that support Chromecast will show a cast button that links your device to the television, and whatever video you select will begin playing on the larger screen. You can also use the Chrome browser on a laptop or desktop to launch video from websites that offer that feature. What’s different, then?
How data scientists can help operational analytics succeed
A typical company has an organization that develops and an organization that operates. When I was consulting with PayPal, we had a group of talented professionals that constantly improved the functionality of the PayPal website. There was an equally talented group of professionals responsible for handling the operations of the production site. This operations group had a very different environment within which to succeed. That is why they had the best tools available to analyze what was happening at any point in time, and the best practices for troubleshooting problems in the moment. Data science can help tremendously with monitoring and troubleshooting. A key difference between operations and development is in their perspective of the status quo. For operations, stability is the goal—preserve the status quo; therefore, data science must be used to alert operators when the situation is not normal.
Digital Well-being — Its time to look after ourselves

We always choose such immediate enjoyment of likes, reacts, swipes and claps over long term flourishing, punching a hole in our well-being. But all this is not really good for nothing, your each swipe, click, reaction generates tonnes of revenues for companies in exchange for your sleep. Well, they always say, If You're Not Paying For It, You Are The Product. One must have come across recent announcements by Google and Apple on addressing the issue of digital well-being by monitoring screen time. But if one must need to really achieve/experience the state, one must possess the necessary digital skills. I have explained this using an analogy below. Consider an analogy between two phases of life. At young age when children are exposed to the real world society, certain real world skills like language, manners, values and other resources are taught for them to overcome challenges they might face in life. In similar manner when children are exposed to digital technology, are they prepared or equipped with digital skills to face the challenges they may come across?
Malware Moves: Attackers Retool for Cryptocurrency Theft
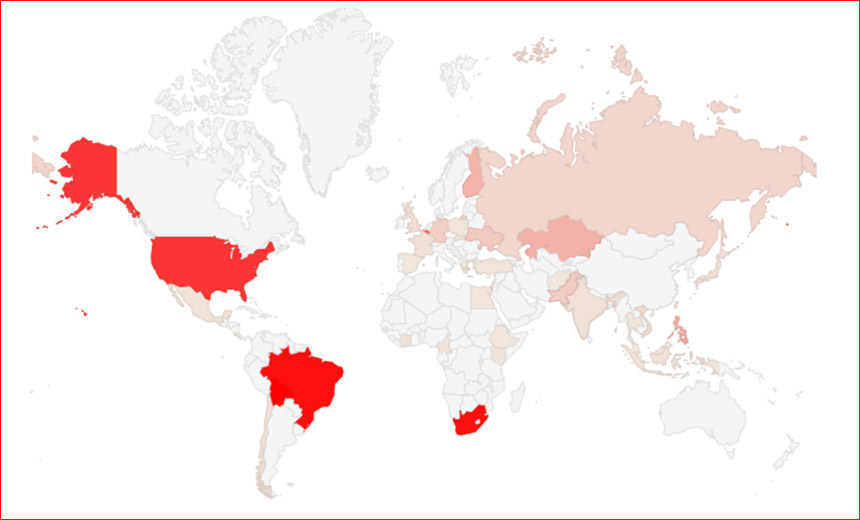
Modular malware called Trickbot, which has also been used to mine for cryptocurrency, is up to new tricks. "TrickBot has traditionally targeted banking customers in multiple geographies to steal login credentials in order to commit identity fraud and facilitate fraudulent transactions," researchers at Digital Shadows say in a research report. But TrickBot's designers have been adding additional capabilities that appear designed to extend the reach of the malware. In February, TrickBot's designers added an open source monero cryptocurrency-mining module. And in March, they added the ability to crypto-lock devices, "potentially helping threat actors to extort victims," the research report says. Last month, Vitali Kremez, director of research at threat intelligence firm Flashpoint, warned the TrickBot had been updated to included a module designed to steal passwords from multiple types of applications and browsers.
Mirai Evolves From IoT Devices to Linux Servers
Netscout researchers say they have observed what appears to be a relatively small number of threat actors attempting to deliver the malware on Linux servers by exploiting a recently disclosed vulnerability in Hadoop YARN. The YARN vulnerability is a command injection flaw that gives attackers a way to remotely execute arbitrary shell commands on a vulnerable server. Many of the servers running Hadoop YARN are x86-based. Netscout has been tracking attempts to exploit the flaw using its global network of honeypots. It says it has observed tens of thousands of exploit attempts daily. In November alone, Netscout observed attackers attempting to deliver some 225 unique malicious payloads via the Hadoop YARN vulnerability. Of that, at least one dozen of the malware samples were Mirai variants.
Quote for the day:
"Adapt what is useful, reject what is useless, and add what is specifically your own." -- Bruce Lee
No comments:
Post a Comment