GitHub Copilot can make inline code suggestions in several ways. Give it a good descriptive function name, and it will generate a working function at least some of the time—less often if it doesn’t have much context to draw on, more often if it has a lot of similar code to use from your open files or from its training corpus. ... Test generation is generally easier to automate than initial code generation. GitHub Copilot will often generate a reasonably good suite of unit tests on the first or second try from a vague comment that includes the word “tests,” especially if you have an existing test suite open elsewhere in the editor. It will usually take your hints about additional unit tests, as well, although you might notice a lot of repetitive code that really should be refactored. Refactoring often works better in Copilot Chat. Copilot can also generate integration tests, but you may have to give it hints about the scope, mocks, specific functions to test, and the verification you need. ... GitHub Copilot Code Reviews can review your code in two ways, and provide feedback. One way is to review your highlighted code selection (Visual Studio Code only, open public preview, any programming language), and the other is to more deeply review all your changes. Deep reviews can use custom coding guidelines.
Closed loop optimisation: Opening a world of advantages for marketers

In marketing, closed loop optimisation refers to the collection and analysis of various data across the marketing lifecycle or customer journey to create a continuous cycle of learning and data-led decision-making. By closing the customer journey loop, starting with the first interaction all the way to “post-sale”, brand marketers can evaluate the effectiveness of advertising campaigns and channels, and deploy their resources in initiatives that deliver the best outcomes. ... With advanced analytics solutions, marketing organisations can process structured and unstructured data from internal and external sources to identify emerging trends, customer needs and behaviours, and other metrics that can inform brand strategies. When a health technology company understood with the help of analytics that user-generated content was a key factor in strengthening interactions with customers, it changed the content strategy to include user feedback, and thereby fostered a sense of community, improved credibility, and elevated the brand experience to substantially increase social media engagement within eighteen months. A top U.S. professional basketball team used predictive analytics to uncover new trends and understand the type of content that would resonate best with fans around the world.
The rise of autonomous enterprises: how robotics, AI, and automation are reshaping the workforce of tomorrow

An autonomous enterprise is an organisation that has successfully implemented
the best application of automation technologies to function with minimal human
intervention in most aspects. From routine administrative tasks to complex
decision-making processes, autonomous enterprises leverage AI, ML, and RPA to
drive efficiency, accuracy, and agility. Companies across sectors such as
manufacturing, healthcare, logistics, and more, are looking towards automation
to streamline operations, reduce costs, and innovate. ... As human-machine
collaboration grows, there is an increasing need for employers and educational
institutions to address reskilling and upskilling to prepare the workforce in
continuously changing labour markets. This does not mean this work will
eliminate human jobs but will definitely require more creativity, critical
thinking, and emotional intelligence among human employees—the very qualities
AI cannot encapsulate. ... As Robotics and AI continue to revolutionise the
world the ethical and governance challenges arising from it have to be
responded, proactively and thoughtfully. Privacy, bias, and accountability
issues have to be strongly addressed so that these technologies are developed
and deployed appropriately.
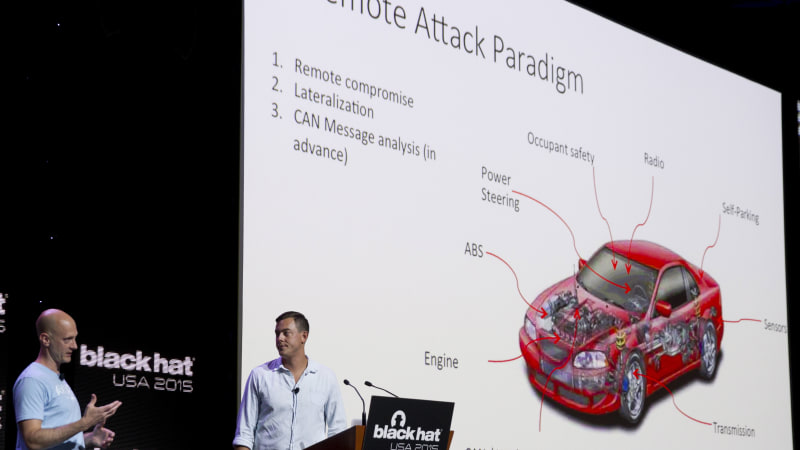
Overcoming legal and organizational challenges in ethical hacking
A professional ethical hacker must have a broad understanding of various IT
systems, networking, and protocols – essentially, a deep “under the hood”
knowledge. This foundational expertise allows them to navigate different
environments effectively. Additionally, target-specific knowledge is crucial,
as the security measures and vulnerabilities can vary significantly based on
the technology stack in use. ... AI and machine learning can significantly
enhance ethical hacking efforts. On the offensive side, automated processes
supported by AI can efficiently identify vulnerabilities and suggest areas for
further manual security testing. This streamlines the initial phases of
penetration testing and helps uncover potential issues more effectively.
Additionally, AI can assist in generating detailed penetration testing
reports, saving time and ensuring accuracy. On the defensive side, AI and
machine learning are invaluable for detecting anomalies and correlating data
to identify potential threats. These technologies enable a proactive approach
to cybersecurity, enhancing both offensive and defensive strategies. By using
AI and machine learning, ethical hackers can improve their
effectiveness.
Why The Gig Economy Is A Key Target For API Attacks

One of the most difficult attacks to prevent is business logic abuse. Strictly
speaking, it isn’t an attack at all. Business logic abuse sees the
functionality of the API used against it, so that a task it is supposed to
execute is then used to carry out an attack. It might be use to subvert access
control, for instance, with attackers manipulating URLs, session tokens,
cookies, or hidden fields to gain advanced privileges and access sensitive
data or functionality. Or bots may attempt to repeatedly sign up, login, or
execute purchases in order to validate credentials, access unauthorised data,
or commit fraud. Perhaps flaws in session tokens or poor handling of session
data allows the attacker to hijack sessions and escalate privileges. Or the
attacker may try to bypass built-in constraints to business logic by reviewing
points of entry such as form fields and coming up with inputs that the
developers may not have planned for. ... Legacy app defences rely on embedding
javascript code into end-user applications and devices, which slows deployment
and leaves platforms vulnerable to reverse engineering. Some of this code,
such as CAPTCHAs, also introduces customer friction.
From Contractors to OAuth: Emerging SDLC Threats for 2025

Outsourcing software development is common practice but opens the door to
significant security risks when not properly managed. These outsourced
operations lack the same stringent security measures applied to internal
teams, creating blind spots that attackers can easily leverage. A common
vulnerability in this scenario is the over-provisioning of access rights. ...
Poorly configured CI/CD pipelines are another critical weakness. When
organizations outsource software development, they often have little
visibility into the security practices of their contractors’ environments.
Attackers can exploit poorly configured pipelines to access source code or
manipulate software delivery processes. ... Preventing OAuth phishing can be
difficult because it exploits user behavior rather than traditional technical
vulnerabilities. While phishing training is essential, the best defense is
limiting the damage attackers can cause if they gain access. By restricting
developer entitlements to only what is necessary for their role, organizations
can reduce the impact of a compromised account and prevent broader system
breaches. ... The most catastrophic SDLC security breaches in 2025 may not
stem from technical vulnerabilities but from poorly managed development
teams.
In a Growing Threat Landscape, Companies Must do Three Things to Get Serious About Cybersecurity

From a practical standpoint, execs and the board make budget decisions about
every domain, including security. Unlike other domains, cybersecurity isn’t a
profit center for most businesses, so it often gets underfunded compared to
business units and projects that generate revenue. That’s a problem. If
executives understand how much is at stake from a fundamental business level,
they will invest in bolstering their cybersecurity posture. Cybersecurity is
essential to protecting profit centers and enabling them to safely grow. And
more and more, customers are looking at a company’s security bonafide when
making their buying decisions. It’s in the execs’ self-interest to take charge
in adopting a cybersecurity posture as they will ultimately be held
accountable in the event of catastrophe. ... It’s also essential to have an
honest, objective CISO at the helm of cybersecurity who has power at the
executive table. The C-suite and board won’t ever know how to effectively
prioritize security unless they have a CISO guiding them accordingly.
Communication is central here. There has to be open discussion between the
CISO and the rest of the C-suite regularly.
Perimeter Security Is at the Forefront of Industry 4.0 Revolution

Perimeter security is crucial for military, government organizations and other
business enterprises alike to detect potential threats, deter the possible
intruders, and delay the illegal attempts which the intruders make while
breaching in a secured area/perimeter. Additionally, perimeter security
maintains the operational continuity within these organizations. To prevent
unauthorized entry to the premises, high-security associations, commercial
centers, government facilities and other organizations can establish a
physical barrier utilizing detection and deterrence techniques.... The
effectiveness of the perimeter security system depends upon several factors
such as design and implementation of the security measures, proper integration
of physical and electronic devices and expertise of a well-trained personnel.
A well-designed perimeter security system should provide a comprehensive
coverage of any building/premise with multiple layers of security which can be
effective against intruders/thieves in creating obstacles. Regular maintenance
and testing of the perimeter security system is necessary to ensure their
continued efficiency. It is critical to continuously assess and expand
perimeter security measures in order to counter different types of threats and
hazards.
5 Trends Reshaping the Data Landscape

Before companies can successfully leverage AI and advanced analytics, it’s
urgent to address the “runaway data movement and data pipeline challenges that
are so common in enterprises,” he pointed out. “When you think about data
movement and data pipelines, most customers have transactional systems or
legacy environments that then feed data to downstream systems. Or they’re
getting a firehose of data from a variety of sources that are coming from the
cloud, and they can be batch or streaming data.” What happens is these
organizations “take that data and transform or consume it by multiple business
units using their own extract, transform, and load (ETL) solutions,” he
illustrated. “They can be completely different types of data. This is
typically the first kind of deviation or loss of a unified source of truth for
the data.” The ETL solutions that each group manages “have their own user
acceptance testing or production environments, which means more copies of
data,” he pointed out. “Then that data is fed to multiple systems, maybe for
dashboarding or for more low-latency analytics. But it’s also fed to their
systems, like OLAP systems or data lakes.” If a data team “can’t get the data
where it needs to go, they’re not going to be able to analyze it in an
efficient, secure way,” he said.
Top challenges holding back CISOs’ agendas

With limited resources and an ever-growing list of threats, CISOs are often
caught managing multiple projects at once. Some of these might move forward
bit by bit, but without clear milestones or measurable progress, it’s
difficult to show their real impact. This makes it harder for CISOs to secure
extra funding or support, especially when stakeholders can’t see solid,
tangible results. “That makes it almost impossible to show meaningful
success,” says John Terrill, CSO at Phosphorus. “A lot of times, this can come
from trying to boil the ocean.” Many CISOs recommend learning to “speak
business” and occasionally scaring the board to get more funding, but these
can only go so far. “The company has a finite amount of resources; you need to
make peace with that,” Avivi says. ... “Aligning both the workforce and the
organization’s leadership around risk appetite helps tremendously to focus
your energy and your dollars in the places that most need them,” says Ken
Deitz, CISO at Secureworks. “If an organization has a stated risk appetite for
security risk, the priorities start to jump off the page.” CISOs should be
open about the risk the organization will take if their priorities are not
addressed.
Quote for the day:
"A leadership disposition guides you
to take the path of most resistance and turn it into the path of least
resistance." -- Dov Seidman