The dangers of voice fraud: We can’t detect what we can’t see

The inherent imperfections in audio offer a veil of anonymity to voice manipulations. A slightly robotic tone or a static-laden voice message can easily be dismissed as a technical glitch rather than an attempt at fraud. This makes voice fraud not only effective but also remarkably insidious. Imagine receiving a phone call from a loved one’s number telling you they are in trouble and asking for help. The voice might sound a bit off, but you attribute this to the wind or a bad line. The emotional urgency of the call might compel you to act before you think to verify its authenticity. Herein lies the danger: Voice fraud preys on our readiness to ignore minor audio discrepancies, which are commonplace in everyday phone use. Video, on the other hand, provides visual cues. There are clear giveaways in small details like hairlines or facial expressions that even the most sophisticated fraudsters have not been able to get past the human eye. On a voice call, those warnings are not available. That’s one reason most mobile operators, including T-Mobile, Verizon and others, make free services available to block — or at least identify and warn of — suspected scam calls.
Provider or partner? IT leaders rethink vendor relationships for value

Vendors achieve partner status in McDaniel’s eyes by consistently demonstrating accountability and integrity; getting ahead of potential issues to ensure there’s no interruptions or problems with the provided products or services; and understanding his operations and objectives. ... McDaniel, other CIOs, and CIO consultants agree that IT leaders don’t need to cultivate partnerships with every vendor; many, if not most, can remain as straight-out suppliers, where the relationship is strictly transactional, fixed-fee, or fee-for-service based. That’s not to suggest those relationships can’t be chummy, but a good personal rapport between the IT team and the supplier’s team is not what partnership is about. A provider-turned-partner is one that gets to know the CIO’s vision and brings to the table ways to get there together, Bouryng says. ... As such, a true partner is also willing to say no to proposed work that could take the pair down an unproductive path. It’s a sign, Bouryng says, that the vendor is more interested in reaching a successful outcome than merely scheduling work to do.
In the AI era, data is gold. And these companies are striking it rich
AI vendors have, sometimes controversially, made deals with organizations like
news publishers, social media companies, and photo banks to license data for
building general-purpose AI models. But businesses can also benefit from using
their own data to train and enhance AI to assist employees and customers.
Examples of source material can include sales email threads, historical
financial reports, geographic data, product images, legal documents, company web
forum posts, and recordings of customer service calls. “The amount of
knowledge—actionable information and content—that those sources contain, and the
applications you can build on top of them, is really just mindboggling,” says
Edo Liberty, founder and CEO of Pinecone, which builds vector database software.
Vector databases store documents or other files as numeric representations that
can be readily mathematically compared to one another. That’s used to quickly
surface relevant material in searches, group together similar files, and feed
recommendations of content or products based on past interests.
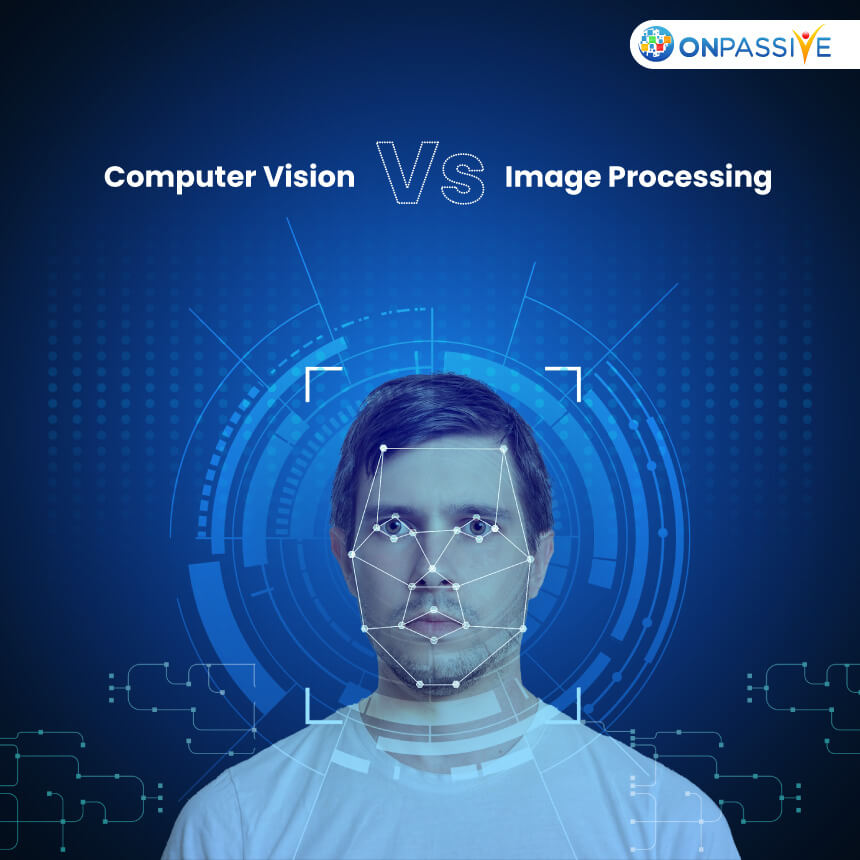
Machine Vision: The Key To Unleashing Automation's Full Potential
Machine vision is a class of technologies that process information from visual
inputs such as images, documents, computer screens, videos and more. Its value
in automation lies in its ability to capture and process large quantities of
documents, images and video quickly and efficiently in quantities and speeds
far in excess of human capability. ... Machine vision based technologies are
even becoming central to the creation of automations themselves. For example,
instead of relying on human workers to describe processes that are being
automated when designing automations, recordings of the process to be
automated are created and then machine vision software, combined with other
technologies, is used to capture the process end-to-end and then provide the
input to automating a lot of the work needed to program the digital workers
(bots). ... Machine vision is integral to maximizing the impact of advanced
automation technologies on business operations and paving the way for
increased capabilities in the automation space.
Put away your credit cards — soon you might be paying with your face

Biometric purchases using facial recognition are beginning to gain some
traction. The restaurant CaliExpress by Flippy, a fully automated fast-food
restaurant, is an early adopter. Whole Food stores offer pay-by-palm, an
alternative biometric to facial recognition. Given that they are already using
biometrics, facial recognition is likely to be available in their stores at
some point in the future. ... Just as credit and debit cards have overtaken
cash as the dominant means to make purchases, biometrics like facial
recognition could eventually become the dominant way to make purchases. There
will however be actual costs during such a transition, which will largely be
absorbed by consumers in higher prices. The technology software and hardware
required to implement such systems will be costly, pushing it out of reach for
many small- and medium-size businesses. However, as facial recognition systems
become more efficient and reliable, and losses from theft are reduced, an
equilibrium will be achieved that will make such additional costs more modest
and manageable to absorb.
Technologists must be ready to seize new opportunities
For technologists, this new dynamic represents a profound (and daunting)
change. They’re being asked to report on application performance in a more
business-focussed, strategic way and to engage in conversations around
experience at a business level. They’re operating outside their comfort zone,
far beyond the technical reporting and discussions they’ve previously
encountered. Of course, technologists are used to rising to a challenge and
pivoting to meet the changing needs of their organisations and their senior
leaders. We saw this during the pandemic, many will (rightly) be excited about
the opportunity to expand their skills and knowledge, and to elevate their
standing within their organisations. The challenge that many technologists
face, however, is that they currently don’t have the tools and insights they
need to operate in a strategic manner. Many don’t have full visibility across
their hybrid environments and they’re struggling to manage and optimise
application availability, performance and security in an effective and
sustainable manner. They can’t easily detect issues, and even when they do, it
is incredibly difficult to quickly understand root causes and dependencies in
order to fix issues before they impact end user experience.
Vulnerability management empowered by AI

Using AI will take vulnerability management to the next level. AI not only
reduces analysis time but also effectively identifies threats. ... AI-driven
systems can identify patterns and anomalies that signify potential
vulnerabilities or attacks. Converting the logs into data and charts will make
analysis simpler and quicker. Incidents should be identified based on the
security risk, and notification should take place for immediate action.
Self-learning is another area where AI can be trained with data. This will
enable AI to be up-to-date on the changing environment and capable of
addressing new and emerging threats. AI will identify high-risk threats and
previously unseen threats. Implementing AI requires iterations to train the
model, which may be time-consuming. But over time, it becomes easier to
identify threats and flaws. AI-driven platforms constantly gather insights
from data, adjusting to shifting landscapes and emerging risks. As they
progress, they enhance their precision and efficacy in pinpointing weaknesses
and offering practical guidance.
Why every company needs a DDoS response plan
Given the rising number of DDoS attacks each year and the reality that DDoS
attacks are frequently used in more sophisticated hacking attempts to apply
maximum pressure on victims, a DDoS response plan should be included in every
company’s cybersecurity tool kit. After all, it’s not just a temporary lack of
access to a website or application that is at risk. A business’s failure to
withstand a DDoS attack and rapidly recover can result in loss of revenue,
compliance failures, and impacts on brand reputation and public perception.
Successful handling of a DDoS attack depends entirely on a company’s
preparedness and execution of existing plans. Like any business continuity
strategy, a DDoS response plan should be a living document that is tested and
refined over the years. It should, at the highest level, consist of five
stages, including preparation, detection, classification, reaction, and
postmortem reflection. Each phase informs the next, and the cycle improves
with each iteration.
Reduce security risk with 3 edge-securing steps

Over the past several years web-based SSL VPNs have been targeted and used to
gain remote access. You may even want to consider evaluating how your firm
allows remote access and how often your VPN solution has been attacked or at
risk. ... “The severity of the vulnerabilities and the repeated exploitation
of this type of vulnerability by actors means that NCSC recommends replacing
solutions for secure remote access that use SSL/TLS with more secure
alternatives,” the authority says. “The NCSC recommends internet protocol
security (IPsec) with internet key exchange (IKEv2). Other countries’
authorities have recommended the same.” ... Pay extra attention to how
credentials that need to be accessed are protected from unauthorized access.
Ensure that you use best practice processes to secure passwords and ensure
that each user has appropriate passwords and access accordingly. ... When
using cloud services, you need to ensure that only those vendors you trust or
that you have thoroughly vetted have access to your cloud services.

The real key to machine learning success is something that is mostly missing
from genAI: the constant tuning of the model. “In ML and AI engineering,”
Shankar writes, “teams often expect too high of accuracy or alignment with
their expectations from an AI application right after it’s launched, and often
don’t build out the infrastructure to continually inspect data, incorporate
new tests, and improve the end-to-end system.” It’s all the work that happens
before and after the prompt, in other words, that delivers success. For genAI
applications, partly because of how fast it is to get started, much of this
discipline is lost. ... As with software development, where the hardest work
isn’t coding but rather figuring out which code to write, the hardest thing in
AI is figuring out how or if to apply AI. When simple rules need to yield to
more complicated rules, Valdarrama suggests switching to a simple model. Note
the continued stress on “simple.” As he says, “simplicity always wins” and
should dictate decisions until more complicated models are absolutely
necessary.
Quote for the day:
“The vision must be followed by the
venture. It is not enough to stare up the steps - we must step up the
stairs.” -- Vance Havner