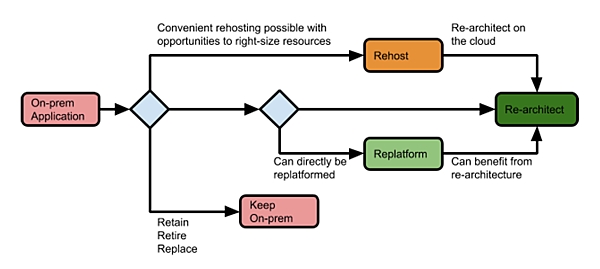
Jump Over the Hidden Barriers to Digital Transformation

A key reason for the failures: a lack of clear, measurable business goals.
Right now, no matter the business, eyes everywhere are on IT. To push through
the transformation, you need to benefit not just yourself but your
organization. You need to be able to speak the language of business, and
here’s how you can do it. If you’re going to ask the company to support your
program, talk about it in a way the C-suite can understand. Think about the
use case they’ll be most interested to hear about. Shortening customer wait
times? They’ll care. Aiding supply chains? They’ll listen. Remember, they’ll
want numbers, too. The C-suite will do a cost-benefit analysis, but you should
preempt this by conducting one beforehand. This shows your commitment to
making the company more successful and inspires trust in the project through
data. Avoid using too much technical jargon; doing so will get glassy-eyed
looks and perhaps inspire them to give some other department a budget increase
or greenlight a different project. Never make the C-suite do your work for
you: Make them understand the value of your plans. Doing so may develop your
soft skills.
6 Insights for Dynamic Leadership
Too often we get caught up in the inequity of having a problem. It’s unfair
that we should suffer this or “that should have never happened in the first
place!” What we need to focus on is how to safely address the problem, how to
move forward, around, over or under it to get where we need to go. ...
Focusing on “being decisive” misses the lesson. Start thinking about the
information — what you have, what you need and whether you can wait for more.
The goal is be able to reflect upon decisions and know that you would make the
same one again tomorrow — even if they were wrong. ... If it’s not someone’s
job, it’s no one’s job. And so, we’re taught to identify a specific person to
carry out a task in order to get the task done. When it can be anyone’s
job to cook dinner, you’ll be hangry by 7:00. But when you split the cooking
every other day, you will go hungry a lot less often. As meetings end, tasks
should be given to people and as specifically as possible with closed-loop
communication built into the responsibility. ... Control yourself — it’s
pretty much the only thing you can control. It’s the doctor whose face says
“Everything’s cool — I got this.” It’s the pilot’s smooth, buttery drawl that
announces the severe turbulence over the PA. It’s the expert in the room
defusing an insane customer or devolving employee.
Management lessons of The True Believer

The True Believer is no less relevant today than when it was first published,
despite its pessimistic view of human nature and skepticism toward mass
movements. Several elements are of particular interest to business leaders.
For example, Hoffer recognizes that “the chief passion” of the frustrated is
to belong, and urges employers to cultivate “a vivid feeling of solidarity” in
employees through collective pay schemes and other means, as teamwork boosts
productivity: “Any policy that disturbs and tears apart the team is bound to
cause severe trouble.” Another important source of belonging is the family.
Dangerous mass movements, in Hoffer’s view, tend to undermine and be jealous
of the family, which is yet another reason firms ought to be friendlier toward
that beleaguered institution. Humans find passionate causes seductive, Hoffer
knows, but he seems not to subscribe to any cultlike conception of a business.
“The practical organization offers opportunities for self-advancement, and its
appeal is mainly to self-interest,” he writes, adding that: “Where
self-advancement cannot, or is not allowed to, serve as a driving force, other
sources of enthusiasm have to be found if momentous changes, such as the
awakening and renovation of a stagnant society or radical reforms in the
character and pattern of life of a community, are to be realized and
perpetuated.”
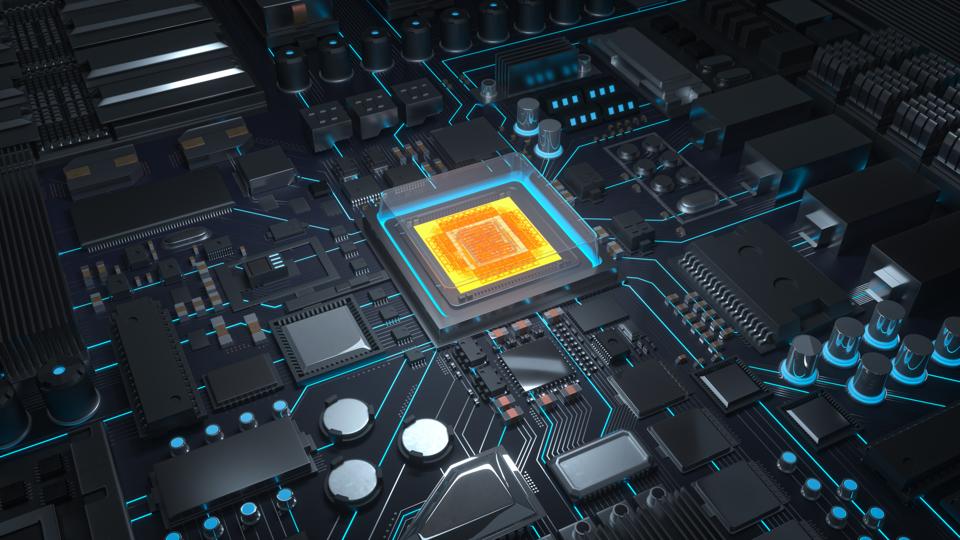
Microsoft Office the most targeted platform to carry out attacks

Researchers said that ... hacking browsers has become more expensive, as
browser security has improved. “Browser developers put much effort into
different kinds of security protections and mitigations,” Liskin said.
“Attackers were looking for a new target, and MS Office has become a star.”
Liskin added that there are plenty of reasons why cybercriminals choose to
attack the popular suite. “Microsoft Office has a huge number of different
file formats," he said. "It is deeply integrated into the Windows operating
system." He also argued that when Microsoft created Office, it made several
decisions that, in hindsight, aren’t optimal security-wise and are currently
difficult to change. Making such alterations would have a significant impact
on all the versions of the products, Liskin said. A new report from SonicWall
released in July 2020 shows this trend is growing. Office files have overtaken
PDF documents as a delivery mechanism for malware. Office documents make up
22.4% of all malicious file types, compared to 10.7% for PDFs. A bit of good
news in the SonicWall report: The number of detected malicious Office files
declined slightly at the end of the first half of 2020.
Intel's 7nm products delayed; first 7nm client CPU expected in late 2022 or 2023

Intel is pushing back its 7nm product roadmap after identifying a defect mode
in its 7nm process that resulted in yield degradation, Swan said. The yield of
Intel's 7nm process is now trending approximately 12 months behind the
company's internal target. "We've root caused the issue, and believe there are
no fundamental roadblocks," Swan said. "But we've also invested in contingency
plans to hedge against further schedule uncertainty. We've mitigated the
impact of the process delay on our product schedule by leveraging improvements
in design methodology, such as die disaggregation and advanced packaging." The
news of the delay caused Intel shares to sink in after-hours trading. The
delay comes in the context of Intel's challenges to transition to 10nm
products, with its product roadmap repeatedly delayed. "We've seen this
movie before," Swan acknowledged Thursday. "We have learned from the
challenges in our 10nm transition, and we have a milestone-driven approach to
ensure our product competitiveness is not impacted by our process technology
roadmap."
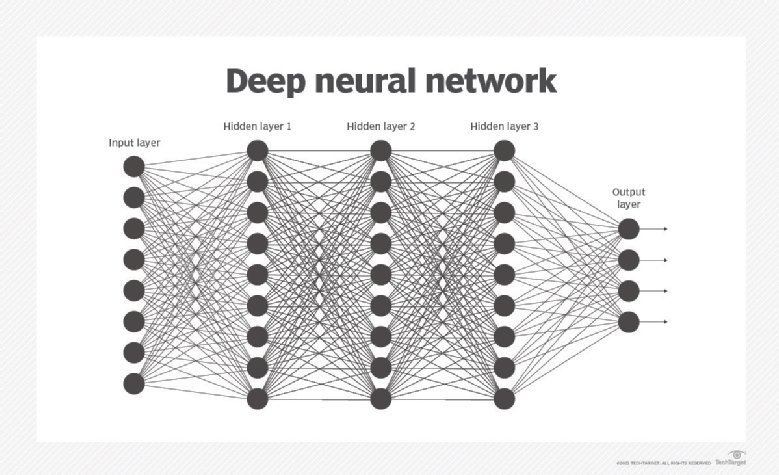
Self-Driving Money Is Coming To Consumer Fintech

The first step to autonomous finance is breaking down the barriers between
these products. Open banking solutions like Plaid, which link fintechs and
banks together, have made it easier to transfer money and data between
platforms. Today, that looks like a hub-and-spoke model: I can move money
from Venmo to my checking account to Vanguard. In the future, it will be
point-to-point: I should be able to take $400 at-rest in Venmo and invest it
directly into my Roth IRA, or split it 50/50 between my student loan
payments and my credit card bill. Self-driving money limited to one app is
like a self-driving car that only works on one road. The second step is
where the ‘autonomous’ part comes in. Connected fintech services will use a
combination of common-language rules set by the user and machine learning to
manage money in the background. This goes a step beyond setting a retirement
goal on a roboadvisor: I should be able to say “whenever I have spare money
laying around, other than what I need for day-to-day expenses, reinvest it
into whatever earns the highest return.” After that, I should never have to
think about what’s happening with my money, other than when I receive
updates from the service on how it is being put to work.
Low-Code Technology Boosts The Growth Of Specialist Bank
During its low-code journey, HTB invested heavily in testing capabilities,
providing value with an improved turnaround time for any defects.
Previously, developers would publish a change, finishing in the evening,
then the test team would arrive the next morning and start the test pack,
which could run for 3-4 hours, ensuring everything worked correctly and
highlighting any regressions. The developers wouldn’t get feedback until
lunchtime, therefore losing half a day of development time. Now, the
developers publish an update and leave for the evening. Liberty Create takes
30 minutes to package the release and push it to the test environment,
waking up the testing platform automatically once complete and running the
series of tests. By 9 am, the test team starts the day with the results and
the developers work on any fixes needed immediately. As a result, an extra
half a day per developer is gained from every push. This acted as the first
step for HTB on its journey to seamless integrated testing and DevOps.
Today, HTB’s confidence in front-end building capabilities now influences
how the bank approaches new potential suppliers with a clear strategy that
needs to work with low-code.
Security Leaders Adapt to Manage Cyber Everywhere
We have placed a significant focus on our early talent development program,
bringing in people who understand the business and can be trained to perform
risk assessments and develop the necessary technical skills. Mentoring young
professionals is one of my passions, and it is essential to develop the
cybersecurity skills we need now and in the future. It’s important to make
the time, however busy our schedules are, to help shape people into more
than they thought they could be. In terms of collaboration across the
profession, we are participating in the recently formed Health Information
Sharing and Analysis Center (H-ISAC) in Japan, which is a community of life
sciences organizations that have come together to share timely, relevant,
actionable information on cybersecurity. Although we are competitors in
business, we share a common goal to prevent, detect, and respond to
cybersecurity concerns. We face many of the same challenges with respect to
resources and professional staffing, so it helps all of us if we can work
collaboratively.
Cloud Computing – Trends that Enterprises Should Watch Out For

The prevalence of mobile phones has majorly affected the business world.
Anyplace, anytime access that these cloud-based apps provide turns to be
perfect for remote working employees. Employees can essentially sign into
any application with web-enabled devices like tablets or mobile phones to
carry out their tasks in the cloud infrastructure. Information breaches,
theft, and data omission are the major threats even for conventional IT
infrastructures. But, as more organizations move to the cloud platforms,
it’s crucial to guarantee that cloud service provider can ensure a secure
framework for the wellbeing of their consumer’s information. Cloud security
isn’t the only trend in cloud computing, but it’s important to be
emphasized enough on by each organization. Consequently, an enormous
demand for cloud security suppliers is emerging that guarantees that
the data practices abide by GDPR and other compliances. With
open-source cloud computing, firms can see various advantages. They can
quickly scale their cloud foundation, including exceptions that are a lot
more direct than the closed source platform, with fewer security
concerns.
Banning TikTok Won't Solve Our Privacy Problems
While all these drivers are legitimate concerns — we should express concern
when a nation-state owns an application that is harvesting huge amounts of
sensitive data — our focus on these factors conveniently bypasses the true
problem. Applications are becoming increasingly more intrusive and we are
surrendering our data ever more willingly without understanding the
potential ramifications that will ripple far into the future. Once our data
has been leaked, it is out there and we can't ask nicely to please have it
back. That means if data we once thought was innocuous suddenly changes into
something dangerous, perhaps because of a new piece of technology or a
change to how we use data, then you are already at a disadvantage. Banning
apps based solely on their country of origin (no matter how hostile) is not
going to solve this problem; it is merely a Band-Aid that won't fully
address all privacy and security concerns. We need to address the
underlying problem, take a hard look at what data our applications are
collecting, and focus on improving privacy controls. We could throw a dart
at a list of apps in most app stores and almost be guaranteed to hit one
with some form of privacy issue.
Quote for the day: