How digital humans can make healthcare technology more patient-centric

Like humans, digital humans have anatomy. Several technologies are used to create digital humans. The Representation: The “face” of the digital entity can be created in likeness to a real or caricature of a human. The quality of this representation is critical to a successfully designed digital human. Natural Language Processing (NLP) or Natural Language Understanding (NLU): NLP/NLU ensures that the digital human can properly interpret information, such as speech detection, speech-to-text translation, and language recognition and detection. Advanced forms of NLP/NLU will include sign language as well. Cognitive Services: Cognitive services are used for creating personalized communication including language translation, speech synthesis, voice customization, speech prosody and pitch, nomenclature and specialized pronunciation. Artificial Intelligence: The AI layer–whether generative, extractive or other forms–provides contextual conversation response, context recognition and for generative AI, content creation.
CISO to BISO – What's your next role?

The role of a BISO has emerged over the past decade, as organisations recognise
the need for dedicated security roles and skills within specific business units
or departments. While it is challenging to pinpoint an exact date when the role
of BISO became established across all industries, it can be traced back to the
increasing emphasis on information security, the evolving nature of
cybersecurity threats and the increasingly complex technical infrastructures in
use. As businesses have become more digital, data-centric, and interconnected,
the complexity and diversity of security risks have grown exponentially with it.
Traditional approaches to information security, where the responsibility solely
resides with the IT department or a centralised security team, have proved
inadequate to address the unique security challenges faced by businesses today.
... When implementing information security in larger organisations, we would
look for security champions within operational or support functions. People who
showed some kind of interest in the world of cybersecurity usually resulted in
them being offered a support role on a voluntary basis.
Top cybersecurity tools aimed at protecting executives

A recent Ponemon report, sponsored by BlackCloak, revealed that 42% of
respondents indicated that key executives and family members have already
experienced at least one cyberattack. While it's likely that cybercriminals will
target executives and the digital assets they have access to, organizations are
not responding with suitable strategies, budgets, and staff, the report found.
Just over half (58%) of respondents reported that the prevention of threats
against executives and their digital assets is not covered in their cyber, IT
and physical security strategies and budget. The lack of attention is
demonstrated with only 38% of respondents reporting a dedicated team to prevent
or respond to cyber or privacy attacks against executives and their families.
The best practice to do this well would be to protect the executive as well as
their family, inner circle, and associates with a broad range of measures,
Agency's Executive Digital Protection report noted. The solutions need to
balance breadth, value, privacy, and specialization, it said.
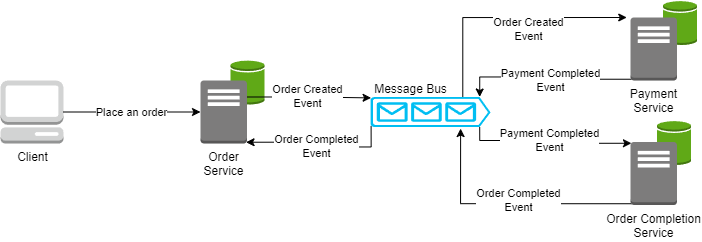
How WebAssembly will transform edge computing

As the next major technical abstraction, Wasm aspires to address the common
complexity inherent in the management of the day-to-day dependencies embedded
into every application. It addresses the cost of operating applications that are
distributed horizontally, across clouds and edges, to meet stringent performance
and reliability requirements. Wasm’s tiny size and secure sandbox mean it can be
safely executed everywhere. With a cold start time in the range of 5 to 50
microseconds, Wasm effectively solves the cold start problem. It is both
compatible with Kubernetes while not being dependent upon it. Its diminutive
size means it can be scaled to a significantly higher density than containers
and, in many cases, it can even be performantly executed on demand with each
invocation. But just how much smaller is a Wasm module compared to a micro-K8s
containerized application? An optimized Wasm module is typically around 20 KB to
30 KB in size. When compared to a Kubernetes container, the Wasm compute units
we want to distribute are several orders of magnitude smaller.
Data Governance Trends and Best Practices for Storage Environments

The more intelligent the data layer is, the more value the data can provide.
More valuable data makes the role of data governance stronger within the
organization. Active archive solutions can serve as a framework for data
governance by including an intelligent data management software layer that
automatically places data where it belongs and optimizes its location based on
cost, performance, and user access needs. “Data governance is the process of
managing the availability, usability, integrity and security of enterprise
data,” said Rich Gadomski, head of tape evangelism at FUJIFILM Recording Media
U.S.A. and co-chair of the Active Archive Alliance. ... Supporting active
archives with optical disk storage technologies can provide long-term data
preservation. These technologies are designed to withstand environmental factors
like temperature, humidity, and magnetic interference, ensuring the integrity
and longevity of archived data. With a typical lifespan of hundreds of years or
more, optical disks are well-suited for archival purposes.
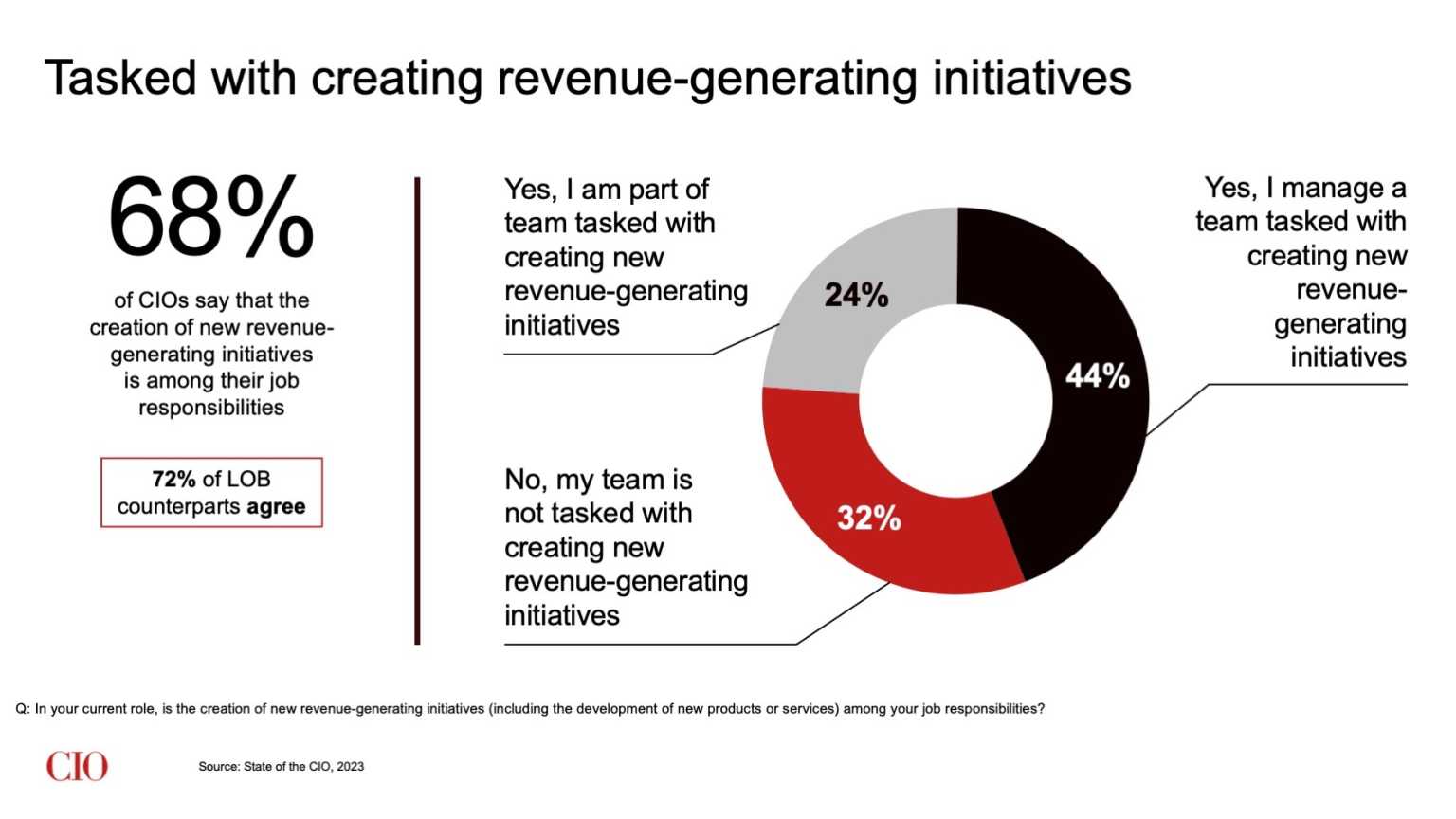
Dr. Pankaj Setia on the challenges that will redefine CIOs’ careers
First, a risk-averse culture may be addressed through a two-pronged approach.
First, CIOs must champion training and engagement of employees, to create a
digital mindset and enhance understanding of the digital transformation being
undertaken. It is imperative that the employees are excited about the
transformation. ... A second step for CIOs is to work toward getting buy-in from
top management. For CIOs to get desired results, the board and top management
team (TMT) must actively champion digital transformation initiatives. Many
examples from the corporate world underline the role of top leadership in
engaging and motivating employee teams. Second, overcoming the barriers due to
siloed strategy is a complex endeavor. It is not always easy to overcome these,
as professional management relies on specialization in a functional domain
(e.g., marketing, finance, human resources, etc.). However, because digital
transformation inherently spans functional domains, siloed strategies — that
emphasize super specialization — are not optimal. Therefore, CIOs should look to
create cross-functional teams.
Risks and Strategies to Use Generative AI in Software Development

Among the risks of using AI in software development is the potential that it
regurgitates bad code that has been making the rounds in the open-source world.
“There’s bad code is being copied and used everywhere,” says Muddu Sudhakar, CEO
and co-founder of Aisera, developer of a generative AI platform for enterprise.
“That’s a big risk.” The risk is not simply poorly written code being repeated
-- the bad code might be put into play by bad actors looking to introduce
vulnerabilities they may exploit at a later date. Sudhakar says organizations
that draw upon generative AI, and other open-source resources, should put
controls in place to spot such risks if they intend to make AI part of the
development equation. “It’s in their interest because all it takes is one bad
code,” he says, pointing to the long-running hacking campaign behind the Solar
Winds data breach. The skyrocketing appeal of AI for development seems to
outweigh concerns about the potential for data to leak or for other issues to
occur. “It’s so useful that it’s worth actually being aware of the risks and
doing it anyway,” says Babak Hodjat, CTO of AI and head of Cognizant AI Labs.
Supply Chain, Open Source Pose Major Challenge to AI Systems
Bengio said one big risk area around AI systems is open-source technology, which
"opens the door" to bad actors. Adversaries can take advantage of open-source
technology without huge amounts of compute or strong expertise in cybersecurity,
according to Bengio. He urged the federal government to establish a definition
of what constitutes open-source technology - even if it changes over time - and
use it to ensure future open-source releases for AI systems are vetted for
potential misuse before being deployed. "Open source is great for scientific
progress," Bengio said. "But if nuclear bombs were software, would you allow
open-source nuclear bombs?" Bengio said the United States must ensure that
spending on AI safety is equivalent to how much the private sector is spending
on new AI capabilities, either through incentives to businesses or direct
investment in nonprofit organizations. The safety investments should address the
hardware used in AI systems as well as cybersecurity controls necessary to
safeguard the software that powers AI systems.
Zero-Day Vulnerabilities Discovered in Global Emergency Services Communications Protocol

In a demonstration video of CVE-2022-24401, researchers showed that an attacker
would be able to capture the encrypted message by targeting a radio to which the
message was being sent. Midnight Blue founding partner Wouter Bokslag says that
in none of the circumstances for this vulnerability do you get your hands on a
key: "The only thing is you're getting is the key stream, which you can use to
decrypt, arbitrary frames, or arbitrary messages that go over the network." A
second demonstration video of CVE-2022-24402 reveals that there is a backdoor in
the TEA1 algorithm that affects networks relying on TEA1 for confidentiality and
integrity. It was also discovered that the TEA1 algorithm uses an 80-bit key
that an attacker could do a brute-force attack on, and listen in to the
communications undetected. Bokslag admits that using the term backdoor is
strong, but it is justified in this instance. "As you feed an 80 bits key to
TEA1, that flows through a reduction step and which leaves it with only 32 bits
of key material, and it will carry on doing the decryption with only those 32
bits," he says.
Enterprises should layer-up security to avoid legal repercussions
There are two competing temptations in the technology landscape that the
seasoned security professional must navigate. The first is the temptation to
totally trust the power of the tool. An overly optimistic reliance on vendor
tools and promises can fail to identify security issues if the tools are not
properly implemented and operationalized in your environment. A shiny SIEM tool,
for example, is useless unless you have clearly documented response actions to
take for each alert, as well as fully trained personnel to handle
investigations. The second temptation, which I believe is more prevalent within
tech and SaaS companies, is to trust no tool except for in-house tech. The
thought process goes as follows: “Since we have a solid development team, and we
want to keep a bench of developers for any eventuality, we need to keep their
skills sharp, so we might as well build our own tools.” It’s a sound argument —
up to a point. However, it may be a bit arrogant to believe your company has the
expertise to develop the best-in-class SIEM solutions, ticketing systems, SAST
tools, and what have you.
Quote for the day:
"If you don't demonstrate leadership
character, your skills and your results will be discounted, if not
dismissed." -- Mark Miller