5G and IoT security: Why cybersecurity experts are sounding an alarm

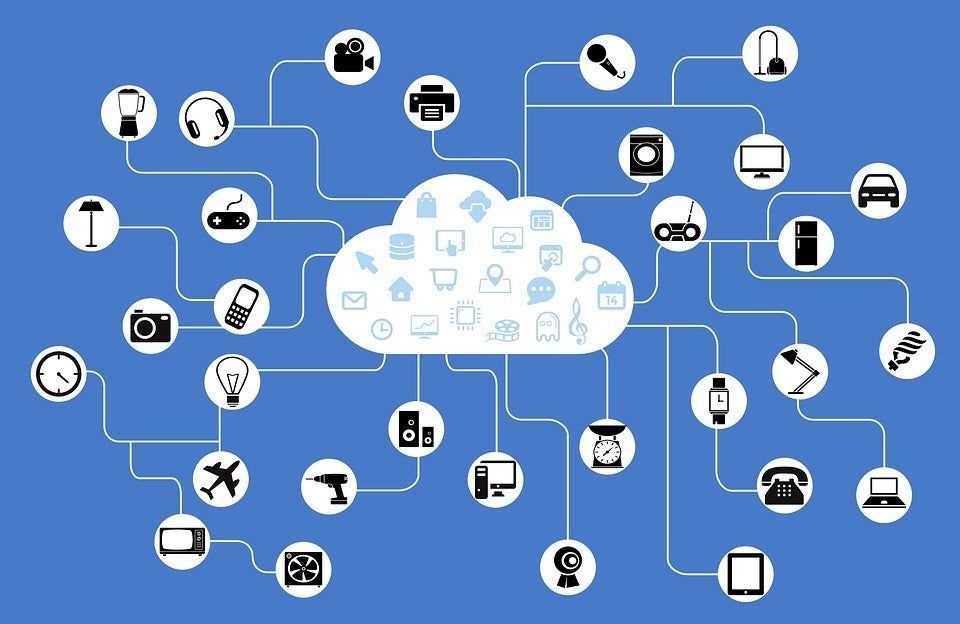
There are five ways in which 5G networks are more susceptible to cyberattacks than their predecessors, according to the 2019 Brookings report, Why 5G requires new approaches to cybersecurity. They are: The network has moved from centralized, hardware-based switching to distributed, software-defined digital routing. Previous networks had "hardware choke points" where cyber hygiene could be implemented. Not so with 5G; Higher-level network functions formerly performed by physical appliances are now being virtualized in software, increasing cyber vulnerability; Even if software vulnerabilities within the network are locked down, the 5G network is now managed by software. That means an attacker that gains control of the software managing the network can also control the network; The dramatic expansion of bandwidth in 5G creates additional avenues of attack; and Increased vulnerability by attaching tens of billions of hackable smart devices to an IoT network. ... The lack of regulations for 5G security, "is why these attacks happen day in and day out" and is also the reason, "2019 was considered the worst year for cybercrime,'' Bencenti said.
More than 40% of privacy compliance technology will rely on AI by 2023
At the forefront of a positive privacy user experience (UX) is the ability of an organization to promptly handle subject rights requests (SRRs). SRRs cover a defined set of rights, where individuals have the power to make requests regarding their data and organizations must respond to them in a defined time frame. According to the survey, many organizations are not capable of delivering swift and precise answers to the SRRs they receive. Two-thirds of respondents indicated it takes them two or more weeks to respond to a single SRR. Often done manually as well, the average costs of these workflows are roughly $1,400 USD, which pile up over time. “The speed and consistency by which AI-powered tools can help address large volumes of SRRs not only saves an organization excessive spend, but also repairs customer trust,” said Mr. Willemsen. “With the loss of customers serving as privacy leaders’ second highest concern, such tools will ensure that their privacy demands are met.”
Cisco security warnings include firewall holes, Nexus software weaknesses

The firewall and UCS vulnerabilities all have a severity level of “high” on the Common Vulnerability Scoring System and include: A vulnerability in the CLI of Cisco FXOS Software and Cisco UCS Manager Software could let an authenticated, local attacker execute arbitrary commands on the underlying operating system (OS). The vulnerability is due to insufficient input validation. A successful exploit could allow the attacker to execute arbitrary commands on the underlying OS with the privileges of the currently logged-in user for all affected platforms excluding Cisco UCS 6400 Series Fabric Interconnects. On Cisco UCS 6400 Series Fabric Interconnects, the injected commands are executed with root privileges, Cisco stated. A second vulnerability in the local management of the same CLI interface in Cisco FXOS Software and Cisco UCS Manager Software could allow similar problems. A weakness in the Cisco Discovery Protocol feature of Cisco FXOS Software and Cisco NX-OS Software could let an unauthenticated, adjacent attacker exploit this vulnerability by sending a crafted Cisco Discovery Protocol packet to a Layer 2-adjacent affected device.
Everything you need to know about the Chief Information Security Officer role

In short, crucial – ensuring that IT systems comply with security and regulatory requirements is the top priority for tech chiefs, according to Grant Thornton LLP and the Technology Business Management Council. They report as many as 83% of IT leaders have increased spending on cybersecurity in the past 12 months. Kind of. While it's good news that CISOs have an increasingly high-profile executive audience for their opinions, the strategic importance of cybersecurity is far from guaranteed. Almost half (43%) of CISOs feel that they are in direct competition with other business and IT initiatives for funding, reports 451 Research and Kaspersky. That battle for cash is at odds with wider business trends: almost every expert recognises businesses need to take security more seriously than ever before. But while 40% of CISOs say their organisation has been subjected to a security attack in the past two years, just 29% of CISOs believe they're very well-positioned to deal with security risks, according to KPMG and Harvey Nash. Consultant EY says organisations can only stay one step ahead of the cyber threat by creating what it refers to as "a culture of security by design". This approach relies on bridging the divide between the security function and the C-suite.
How to find the right zero trust strategy

Where data is anonymised, the security visibility needed for zero trust is reduced. Data anonymisation can mitigate some data protection concerns, but according to the GDPR, only completely anonymous data is not personal in nature. Data is pseudonymised in most cases, meaning it’s possible to re-identify individuals. However, the application of data anonymisation techniques complicates ZT visibility by making it harder to identify the sensitivity or criticality of data in its anonymised form. Colin McMillan, technical director for security at Cisco, says: “Data anonymisation has been used by some European customers to deal with data sovereignty issues. But when implementing ZT, they still want visibility. Customers have implemented technical solutions in non-standard ways to get around this, making maintenance and support challenging for everyone involved.” Non-security executives think that zero trust is just a network security architecture.
Is Artificial Intelligence (AI) A Threat To Humans?

AI will change the workplace and the jobs that humans do. Some jobs will be lost to AI technology, so humans will need to embrace the change and find new activities that will provide them the social and mental benefits their job provided. As Bostrom advises, rather than avoid pursuing AI innovation, "Our focus should be on putting ourselves in the best possible position so that when all the pieces fall into place, we've done our homework. We've developed scalable AI control methods, we've thought hard about the ethics and the governments, etc. And then proceed further and then hopefully have an extremely good outcome from that." If our governments and business institutions don't spend time now formulating rules, regulations, and responsibilities, there could be significant negative ramifications as AI continues to mature. Artificial intelligence will change the way conflicts are fought from autonomous drones, robotic swarms, and remote and nanorobot attacks. In addition to being concerned with a nuclear arms race, we'll need to monitor the global autonomous weapons race.

Although many who follow the hype thought perhaps this shift took place a few years back, this is actually much earlier than I expected, and perhaps faster than most enterprises can manage. Part of this is a bit of “cloud washing,” considering that those with older, on-premises solutions have now rebranded their technology as “private clouds.” Although some of the technology is indeed private cloud technology, many so-called private cloud solutions predate cloud computing and don’t support cloud computing features such as auto- and self-provisioning or supporting automated elastic scalability. You would have to audit all of those technology providers who claim “private cloud” to determine how many of those exist, which is not likely to happen. Putting that issue aside for now, the fact that we’re spending more on cloud computing than traditional on-premises solutions has a few considerations for enterprise IT as we reach the tipping point. ... Most organizations are behind on skills and cultural changes needed to support cloud computing. Indeed, if skills are not updated to meet the needs of cloud-based solutions, they have no chance of succeeding. Most cloud computing failures can be traced to enterprises neglecting human factors.
What Disney+ Can Teach Businesses About Customer Security
Credential stuffing events are pretty straightforward: Hackers gather a massive repository of pre-existing login credentials secured from hundreds, if not thousands, of previous security breaches — leading to nearly 8 billion exposed records — and then attempt to use them to log in to other online services and platforms via automated tools, called bots, trying combinations in rapid succession. Password reuse is the basis for these attacks, given that 65% of Americans admit to using the same password for multiple websites, according to a 2019 Google poll. Aside from password reuse, the failure rate of stuffing attacks is low because launching an attack is easy — plus, subscription services with low price points and massive numbers of users are tempting targets. Once hackers gain access to an account, they also have access to just about any piece of a user's personal information they would need to carry out malicious activities, such as identity theft or credential sales on the Dark Web for as little as $3.
5 Things Google Duplex Means For The Future of Chatbots

Thanks to Duplex, people's expectations of what's possible just changed. Now, whether communicating via voice or text, bots need to be able to act and react in ways that make sense based on human conversational flows. In other words, being mid-flow in customizing your pie with the Pizza Hut bot shouldn't stop you from remembering that you want delivery at the office, not your home. And the bot should be smart enough to accept that input, react naturally, and re-start the tomatoes-or-olives toppings conversation without a hitch. That said, there are different use cases. "Duplex is a better version of a personal assistant," says Julie Blin, former strategy exec at Samsung Mobile. "I think they are complementary." To date, bots have been mostly about text. And that's great when you're in public, or don't want to disturb people, or need privacy. But it'd also be nice to be able to simply speak your requests on occasion ... and maybe even do that in full duplex mode. There are serious speed advantages to speech over texting, at least for those over the age of 15.
Microsoft Teams just added new Outlook integration, chat updates and more

Microsoft has also added the option to assign a tag to members of an organization, so that users can better target their messages. For instance, a store manager could @mention all the cashiers in a given channel and get their message across to all relevant members at once. Calls and meetings got an upgrade in the form of live captions, which can be turned on during Teams meetings to let participants read what people are saying in real time. Salazar wrote that the tool would improve the accessibility and effectiveness of meetings, say, if you are calling from a crowded airport terminal – but it is worth noting that the company recommends speaking clearly, slowly, and to avoid background noise, in order to make the most of the service. The feature supports English language for now, added Salazar, but more languages will be coming soon. And Teams administrators can record meetings to store them in Microsoft Stream cloud storage. Additional security measures also let administrators monitor the content shared on Teams more closely. Microsoft has turned on the option for a legal hold' on private channel chats, which are stored in user mailboxes, should it be necessary to preserve messages related to a specific topic or individual that are relevant to a case.
Quote for the day:
"Stand up for what you believe, let your team see your values and they will trust you more easily." -- Gordon Tredgold