Unpatched Security Flaws Open Connected Vacuum to Takeover

Researchers have discovered several high-severity vulnerabilities in a connected vacuum cleaner. The security holes could give remote attackers the capability to launch an array of attacks — from a denial of service (DoS) attack that renders the vacuum unusable, to viewing private home footage through the vacuum’s embedded camera. The Ironpie M6, which is available for $230 on Amazon, comes equipped with a corresponding mobile app and a security camera. The vacuum cleaner is built by artificial intelligence home robot company Trifo, and was first launched IronPie at CES 2019. Researchers on Wednesday said that they uncovered six flaws, stemming from the vacuum’s mobile app and its connectivity protocol, at RSA Conference 2020, this week in San Francisco. “The most severe vulnerability allows attackers to access any video stream from any Trifo device across the world,” Erez Yalon, director of security research with Checkmarx, told Threatpost. “Through this vulnerability, every single user – whether in a home or office setting as shown in our PoC video – is at risk of a hacker obtaining a live video feed. Needless to say, this represents a total loss of privacy.”
The Amazing Ways Goodyear Uses Artificial Intelligence And IoT For Digital Transformation

Regardless if it's an autonomous, electric, or a traditional vehicle, they all need a solid foundation of the right tire for the specific demands of the vehicle. Goodyear uses internet of things technology in its Eagle 360 Urban tire. The tire is 3D printed with super-elastic polymer and embedded with sensors. These sensors send road and tire data back to the artificial intelligence-enhanced control panel that can then change the tread design to respond to current road conditions on the fly and share info about conditions with the broader network. If the tire tread is damaged, the tire moves the material and begins self-repair. Goodyear’s intelligent tires are in use on a new pilot program with Redspher, a European transportation and logistics company operating in 19 countries. The fleet benefits from the tire's ability to monitor and track tire pressure, vehicle data, and road conditions. This data is then analyzed by Goodyear’s algorithms to gain insights about maintenance needs and ways to improve the safety and performance of the fleet.
Google Teaches AI To Play The Game Of Chip Design

One of the promising frontiers of research right now in chip design is using machine learning techniques to actually help with some of the tasks in the design process. We will be discussing this at our upcoming The Next AI Platform event in San Jose on March 10 with Elias Fallon, engineering director at Cadence Design Systems. The use of machine learning in chip design was also one of the topics that Jeff Dean, a senior fellow in the Research Group at Google who has helped invent many of the hyperscaler’s key technologies, talked about in his keynote address at this week’s 2020 International Solid State Circuits Conference in San Francisco. Google, as it turns out, has more than a passing interest in compute engines, being one of the large consumers of CPUs and GPUs in the world and also the designer of TPUs spanning from the edge to the datacenter for doing both machine learning inference and training. So this is not just an academic exercise for the search engine giant and public cloud contender – particularly if it intends to keep advancing its TPU roadmap and if it decides, like rival Amazon Web Services, to start designing its own custom Arm server chips or decides to do custom Arm chips for its phones and other consumer devices.
JFrog touts DevSecOps edge in CI/CD tools

Most CI/CD tools integrate with package managers for similar purposes. But JFrog could differentiate its Pipelines product based on its experience developing the Artifactory artifact repository manager, as well as its messaging. "Everyone is really doing the same thing -- transforming code into software packages and then shipping those packages to production," said Tom Petrocelli, an analyst at Amalgam Insights. "But there are security advantages as a side effect of the way [JFrog thinks]." This relates to the fact that enterprise DevOps shops in the Linux world increasingly use package managers to centralize corporate governance, explained Charles Betz, an analyst at Forrester Research. "There's a heck of a lot of digital management that revolves around artifacts when you don't own the source code, when that code is written by open source communities and vendors," Betz said.
Hidden cost of cloud puts brakes on migration projects

More than half (58%) of the IT decision-makers surveyed believe the cloud over-promised and under-delivered, while 43% admit that the cloud is more costly than they thought. Only 27% of IT decision-makers surveyed claim they have been able to reduce labour and logistical costs by moving to the cloud. Mark Cook, divisional executive officer at Capita, said: “Every migration journey is unique in both its destination and starting point. While some organisations are either ‘born’ digital or can gather the resources to transform in a relatively short space of time, the majority will have a much slower, more complex path. “Many larger organisations will have heritage technology and processes that can’t simply be lifted and converted, but will need some degree of ‘hybrid by design’,” he added. When asked what unforeseen factors had delayed cloud migration projects, 39% had cost as the main factor, followed by workload and application rearchitecting issues (38%) and security concerns (37%).
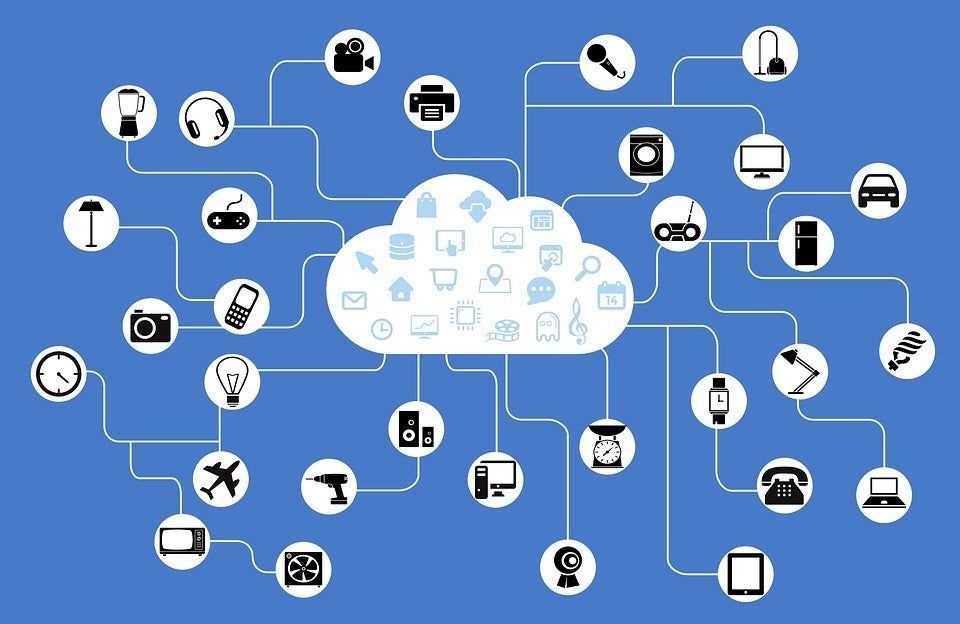
IoT Can Put Your Data at Risk, Here’s How

The data processed by IoT devices is potentially extremely sensitive. With office and home security systems increasingly mediated by IoT (doorbells and surveillance cameras being just a couple of examples), criminal attacks can pose a serious problem. The huge volume of data habitually collected by IoT devices was exposed this year when a database owned by the Chinese firm Orvibo, who offer a smart home appliance platform, was found to have no password protection despite containing logs relating to 2 million worldwide users, including individuals and hotel chains. The data included insufficiently-protected user passwords, reset codes, precise locations, and even a recorded conversation. Botnets are another way for cybercriminals to wreak havoc using IoT devices. Botnets consist of, as their name suggests, networks of bots running on Internet-connected devices. They are primarily known for their role in DDoS (Distributed Denial of Service) attacks, in which a stream of network requests is sent to a network that a malicious entity wishes to bring down.
DesignOps — scaling design to create a productive internal environment for IBMers

DesignOps is a collective term for creating a productive workforce, by addressing challenges such as: growing and evolving design teams, finding and hiring people with the right skills, creating efficient workflows and improving the quality and impact of design outputs. It’s a method of optimising people, processes and workflow, and at IBM, the practice has been deployed to increase efficiency, productivity and general well-being among the the whole organisation, including the thousands-strong IT team. Satisfying this level of individuals and teams is no easy feat, which is why IBM has a specific department dedicated to creating great experiences for IBMers. Kristin Wisnewski — who is on the advisory board for Information Age’s Women in IT Summit in New York on March 25th 2020 at the Grand Hyatt Hotel — leads the CIO Design team at IBM as vice president, whose purpose is to create a productive internal environment at IBM. “We’re here to create, design and improve the experience of employees in their daily jobs. Our team is made up of 140 people, and so it is a big mission to help the hundreds of thousands of employees here at IBM,” she said.
Cloud misconfigurations are a new risk for the enterprise

Cloud misconfigurations are becoming another risk for corporations. At RSA 2020, Steve Grobman, senior vice president and chief technology officer at McAfee, explained how easy it is to take advantage of cloud misconfigurations, an expensive security problem for corporations. He compared cyber security to infectious disease control: an imperfect science. ... In addition to making sure cloud configurations are secure, security teams have to address tomorrow's security risks today, Grobman said. Advances in quantum computing will be a double-edged sword with the downside being the threat to existing encryption systems. "Nation-states will use quantum computing to break our public key encryption systems," he said. "Our adversaries are getting the data today and counting on quantum to unlock in tomorrow." Grubman said that companies need to think about how long data will need to be protected. "Even in 2020, there are documents in the National Archives in relation to the Kennedy assignation that still have redacted information due to national security concerns of today," he said.
Data Science Is A Team Sport: Oracle’s New Cloud Platform Provides The Playing Field

Unlike other data science products that focus on helping individual data scientists, Oracle Cloud Infrastructure Data Science helps improve the effectiveness of data science teams with capabilities like shared projects, model catalogs, team security policies, and reproducibility and auditability features. “Data scientists are experimenters. They want to try stuff and see how it works,” says Pavlik. “They grab sample datasets, they pull in all kinds of open source tools, and they're doing great stuff. What we want to do is let them keep doing that, but improve their productivity by automating their entire workflow and adding strong team support for collaboration to help ensure that data science projects deliver real value to businesses.” The starting point for data science to deliver value is doing more with machine learning, and being more efficient with the data and algorithms involved. “Effective machine learning models are the foundation of successful data science projects,” Pavlik says, but the volume and variety of data facing data science teams “can stall these initiatives before they ever get off the ground.”
Getting closer to no-battery devices
The technique being exploited takes advantage of backscattering. That's a way of parasitically using radio signals inherent in everyday environments. In this case, the chip piggybacks on existing Wi-Fi transmissions to send its data. This method of sending data is power-light, because the carrier needed for the radio transmission is already created—it doesn’t need new energy for the message to be sent. Interestingly, two principal scientists involved in this backscattering project, which was announced by UC San Diego's Jacobs School of Engineering, have also been heavily involved in the development of "wake-up" radios. Wake-up is when a Wi-Fi or other radio comes alive to communicate only when it has something to transmit or receive. The technology uses two radios. One radio is for the wake-up signaling; that radio's only purpose is to listen for a signature. The second is a more heavy-duty radio for the data send. Power is saved because the main radio isn't on all the time. Dinesh Bharadia, now a professor of electrical and computer engineering at UC San Diego, was at Stanford University working on a wake-up radio that I’ve written about.
Quote for the day:
"The greatest good you can do for another is not just share your riches, but reveal to them their own." -- Benjamin Disraeli
No comments:
Post a Comment