As part of any good AI conversation, we have to consider the potential ramifications of an AI-based model. What are the true risks of harnessing AI to help defend ourselves in cyberspace? It is always possible to misuse the information a security system collects. It’s possible to program in unintentional bias. You could break things too much because AI told you to — or you could miss things because you trust your AI system to catch everything. Yet as a business community, we must confront these risks and design to prevent these outcomes. The need for more robust cybersecurity is too great. We simply need to be thoughtful in our approaches, develop and use ethical standards around how we leverage these new and evolving technologies, and, finally, use a trust but-verify-methodology as we look to mature our multilayered cyber-defense strategies. To do this, start by planning ahead and developing a framework for building AI that has preapproved controls in place. Building human review into the decision-making process can go a long way toward preventing major issues. You can also leverage some of the work already being done to manage insider threats and apply that to controlling runaway AI.

Accelerate will enable fintechs to be onboarded to Mastercard in a matter of weeks and provide a guided experience through everything the company can offer. Program participants are connected to relevant parts of the business, to integrate Mastercard’s proprietary technology, leverage its insights and cybersecurity services, engage new customers, and reach new markets and segments. In addition, Mastercard’s commitment to financial inclusion drives focused product development, helping co-create solutions that enable a more inclusive economy. “Mastercard Accelerate is a single doorway to the countless ways Mastercard can help fintechs all over the world grow and scale sustainably,” said Michael Miebach, chief product & innovation officer, Mastercard. “Fintechs are contributing to the rapid digital transformation that makes lives more convenient, simpler, and rewarding. We’re the partner of choice for the top Fintech brands worldwide, and with Accelerate we invite the next generation of global entrepreneurs to join us.” “And for our financial institution partners and customers, Mastercard Accelerate provides access to the next generation of innovators, with a portfolio of start-up partners and fintechs ready to co-create and collaborate on new experiences,” added Miebach.
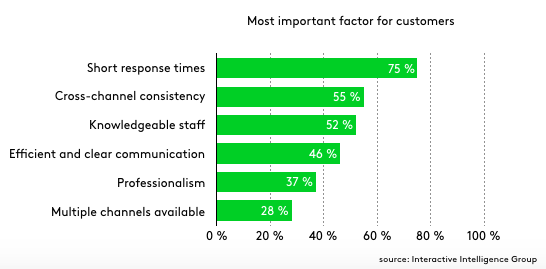
The temptation to use automated support to cut time and costs comes at the risk of further alienating physicians and other clinicians through IT, rather than making their lives easier. Automation via tools like chatbots and self-service surely “roboticizes” interactions, resulting in a loss in human-to-human contact and a degrading of users’ relationships with the IT staff — and perhaps with the institution itself. Despite all the hype around AI and machine learning, perhaps these technologies will be best embraced by support teams as an extension of their personal services, designed first to enhance the customer experience and only secondarily to ease the support staff’s workload and/or cut costs. If we are smart, we should be able to create a balance between digital and human interaction. Even IT-resistant physicians are learning to appreciate digital solutions if they clearly bring ease and convenience.

Microsoft warned us at the beginning of the Win10 onslaught four-plus years ago that it wouldn’t dole out patches one by one. Except for emergency security fixes, patches would be released as part of cumulative updates. Over the years, that promise has evolved into a common pace of two cumulative updates per month: the first on Patch Tuesday, and a second “optional, non-security” cumulative update sometime later in the month. It’s one of the ways “Windows as a service” is a service, doncha know. Last month we were treated to an unholy pileup of Windows security patches as Microsoft released, then re-released, then finally pushed a fix to the Internet Explorer zero-day vulnerability known as CVE-2019-1367. Of course, nobody’s seen any widespread exploits attributable to that security hole, but the bugs — three different sets of them, corresponding to the three botched out-of-band patches — were breathtaking. This month, it looks like we’re headed in a similar direction.
According to Harvard Business School professor Clayton Christensen, each year more than 30,000 new consumer products are launched and 80% of them fail. There is a clear disconnect between product companies and the market. How does it work? The machine learning, natural language processing and visual AI models developed by Commerce.AI analyses unstructured customer feedback or data in the form of text, image, voice and video from reviews, and social media to a lesser extent. “We take unstructured data and synthesise it using AI, NLP and visual AI to create product intelligence for approximately 56,000 product categories,” explained Pandharikar. ... It’s all about improving product development and management; using AI/ML to identify the features that are working and build that into the next product, while taking positive feedback from millions of reviews and using that in the next generation of products. “The old way was to make consumers buy products, now it’s about making products that consumers want,” said Pandharikar.
Speaking at TechCrunch Disrupt SF, Jeanette Manfra, the assistant director for cybersecurity for Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA), said that the agency was making training for new cybersecurity professionals a priority. “It’s a national security risk that we don’t have the talent regardless of whether it’s in the government or the private sector,” said Manfra. “We have a massive shortage that is expected that will grow larger.” Homeland Security is already responding, working on developing curriculum for potential developers as soon as they hit the school system. “We spend a lot of time invested in K-12 curriculum,” she said. The agency is also looking to take a page from the the tech industry’s playbook and developing a new workforce training program that’s modeled after how to recruit and retain individuals. For Manfra, it’s important that the tech community and the government agencies tasked with protecting the nation’s critical assets work more closely together

With the emergence and the implementation of blockchain technology in the Australian financial domain, developers and entrepreneurs can put their creative minds to good use and produce even more innovative games for gambling lovers. This has been brought up due to a well-known relationship between the total revenue and a notable contribution that gambling holds to it. Not only will the peer-to-peer gaming become a reality opening the door for mutual betting, decentralized lotteries and other categories of games, but Aussie high roller casinos will also benefit sizably. One of the main attractions of using Blockchain technology will be the improved degree of trust between players and operators. Every game rule, underlying code, and the outcome will be enabled to verification and thus, enhanced safety and security will be guaranteed. In addition, it will not be too big of a hurdle for Blockchain to gain support rapidly in Australia since many reputable online casinos allow Australian punters to wager, withdraw and deposit in bitcoins.

“Lock your devices up. Make backups. Stay on top of your accounts.” – Ivanti Insider “Be vigilant and be up-to-date. Verify you're typing in the correct web address. Before you click anything in an email, verify the sender is who you think it is and the link/attachment is something they themselves sent. Verify that your antivirus products are up-to-date (and that you have one installed!) and scanning, and that your PC is staying up-to-date with patches. Most issues can be avoided by being careful to always visit legitimate sites, ensuring you aren't opening attachments from unknown individuals, by keeping your PC patched, and your antivirus up-to-date and performing regular scans.” – Kelly Ruston, Technical Support Specialist, William Osler Health System “When you are going to click a link on a webpage or an email, hover over the link first and check the bottom left of your browser to see if it will take you to the page you are expecting.” – Adam Howard, Systems Administrator, Rack Room Shoes

We’re walking in all sorts of different terrains, and the body is naturally adjusting itself, and the way legs move so that you can get around with the least amount of energy possible. The Linx needs to accommodate changes to the environment in a biomechanical way so that users don’t exert so much energy. And that’s a difficult problem because you’re dealing with such a huge variation. If you imagine the activities of daily living — every move that you do — thousands and thousands of steps — how do you detect these changes and accommodate them? The way to do it is to integrate the components of the limb. Rather than looking at products or joints individually, you can leverage all that new information. And what you end up with is a leg which behaves in a much more natural way — able to predict and move in a coordinated way. That’s another important thing. And in our limbs, the movement is very coordinated. Essentially our microprocessor foot would be making its own decisions in complete awareness of what a microprocessor knee would be doing.
A failure to publish an event can mean critical failure to the business process. To explain the problem statement better, let’s consider a Student microservice that helps Enroll the student. After enrollment, the "Course Catalog" service, emails the student all the available courses. Assuming an Event-Driven application, the Student microservice enrolls the student by inserting a record in the database and publishes an event stating that the enrollment for the student is complete. ... This pattern provides an effective solution to publish events reliably. The idea of this approach is to have an “Outbox” table in the service’s database. When receiving a request for enrollment, not only an insert into the Student table is done, but a record representing the event is also inserted into the Outbox table. The two database actions are done as part of the same transaction. An asynchronous process monitors the Outbox table for new entries and if there are any, it publishes the events to the Event Bus. The pattern merely splits the two transactions over different services, increasing reliability.
Quote for the day:
"Leverage is the ability to apply positive pressure on yourself to follow through on your decisions even when it hurts." -- Orrin Woodward